Last Updated on October 23, 2019 by Admin
IT Essentials – ITE Chapter 8 Exam Answers v6.0 2018 2019
Cisco ITE v6.0 latest or IT Essentials v6.0 Chapter 8 Exam Answers PC hardware and software (ITE Version 6.00) collection year 2017, 2018 and 2019 Full 100%. IT Essentials has been know as ITE v6. The following are the questions exam answers. Guarantee Passed. ITE v6.0 Chapter 8 exam answers has some new update from the old version 5. You can review all Chapter 8 Exam Answers. You will get passed scored 100% with this version 6.0. Good Luck for ITE v6.0 Exam!
CCNA7.COM is helping you to collect Cisco IT Essentials Chapter 8 Exam Answers v6 2018 & 2019 or ITE Chapter 8 Exam to show you on this page. ITE Chapter 8 Exam are almost 25 questions. While you take exam online with Cisco, you will meet 25 questions with duration 1 hours to 2 hours depend on your instructor activate. To pass ITE v6 Chapter 8 Exam, you should review all these question. We provide you accurate answer 100%.
Click here go to ITE Chapter 8 Exam – Online Test
-
A user notices that the data transfer rate for the gigabit NIC in the user computer is much slower than expected. What is a possible cause for the problem?
- The switch connection speed was set to 10/100 Mb/s.
- The NIC wake-on-LAN setting is misconfigured.
- Hibernation mode is causing the NIC to shutdown unexpectedly.
- The NIC is configured to use both IPv4 and IPv6 at the same time.
Explanation: For optimum performance, both ends of the conection must be set to the fastest possible speed. If the switch end was set to 10/100 Mb/s the top speed of the connection would be 100 Mb/s.
-
A user notices that the data transfer rate for the gigabit NIC in the user computer is much slower than expected. What is a possible cause for the problem?
- The NIC duplex settings have somehow been set to half-duplex.
- The NIC wake-on-LAN setting is misconfigured.
- Hibernation mode is causing the NIC to shutdown unexpectedly.
- The NIC is configured to use both IPv4 and IPv6 at the same time.
-
Two LEDs are usually present on a NIC. What are the two primary uses for these LEDs? (Choose two.)
- to indicate the presence of a connection
- to indicate interference from another nearby wireless or electronic device
- to indicate that the NIC has connected to a DHCP server
- to indicate that the NIC is connected to a homegroup or workgroup
- to indicate that data transfer activity is present
Explanation: An Ethernet NIC usually has two LEDs, sometimes both are green, and sometimes one is green and one is amber. One light indicates that a connection with an active network device, such as a router or network switch, is present. The second LED flashes to indicate that data activity is present.
-
What is the purpose of the network profiles that are used to establish a new network connection on a Windows PC?
- to configure NIC settings for the fastest network available
- to remove the need for IP addresses when connecting to a network
- to provide a list of ISPs that may be used for Internet access
- to provide an easy way to configure or apply network functions based on the type of network to be joined
Explanation: A choice of a Windows Network Location is required when configuring a new network connection. Network Location Profiles are a collection of network settings and defaults created for each type of location to help the user to easily join a network.
-
A wireless router is displaying the IP address of 192.168.0.1. What could this mean?
- The NAT function is not working on the wireless router.
- The wireless router still has the factory default IP address.
- Dynamic IP address allocation has been configured on the router and is functioning correctly.
- The wireless router has been configured to use the frequencies on channel 1.
Explanation: Wireless routers usually come with factory default settings. The IP address is often set to 192.168.0.1. The default username and password are often admin. The IP address, username, and password should all be modified to help secure the router.
-
A technician is configuring the channel on a wireless router to either 1, 6, or 11. What is the purpose of adjusting the channel?
- to disable broadcasting of the SSID
- to enable different 802.11 standards
- to provide stronger security modes
- to avoid interference from nearby wireless devices
Explanation: Channels 1, 6, and 11 are selected because they are 5 channels apart. thus minimizing the interference with adjacent channels. A channel frequency can interfere with channels on either side of the main frequency. All wireless devices need to be used on nonadjacent channels.
-
Which combination of user account and network location profile allows a user to become a member of a homegroup?
- an admin account with a network location profile of Work
- a guest account with a network location profile of Home
- an admin user account with a network location of Public
- a standard user account with a network location profile of Home
Explanation: Every user account, except the Guest account, can become a member of a homegroup. A homegroup cannot be joined if the network location profile is set to Work or Public.
-
A business traveler connects to a wireless network with open authentication. What should the traveler do to secure confidential data when connecting to the business services?
- Connect with a VPN.
- Change the network location profile to public.
- Change the Windows firewall settings.
- Manually configure an IP address, subnet mask, and default gateway.
Explanation: A VPN is used to form a secure tunnel across a public network. This technology allows users to communicate over an insecure network and yet keep data confidential. Changing the network location profile will modify firewall settings on a computer but not increase the confidentiality of data crossing a network. Modifying the IP address, subnet mask, and default gateway will not change the confidentiality of data transmitting on a network.
-
A technician has been asked to configure a broadband connection for a teleworker. The technician has been instructed that all uploads and downloads for the connection must use existing phone lines. Which broadband technology should be used?
- cable
- DSL
- ISDN
- POTS
-
Which type of connection to the Internet is capable of the fastest transfer rates?
- ISDN
- POTS
- satellite
- cable
- fiber
Explanation: Refer to the chapter graphics to see the various connectivity types and speeds.
-
Which technology would be recommended for a business that requires workers to access the Internet while visiting customers at many different locations?
- ADSL
- cellular
- ISDN
- VPN
Explanation: Cellular access can provide voice connectivity as well as Internet connectivity for video and data transfers.
-
A small company is considering moving many of its data center functions to the cloud. What are three advantages of this plan? (Choose three.)
- The company only needs to pay for the amount of processing and storage capacity that it uses.
- Cloud services are billed at a fixed fee no matter how much processing and storage are used by the company.
- Cloud services enable the company to own and administer its own servers and storage devices.
- The company can increase processing and storage capacity as needed and then decrease capacity when it is no longer needed.
- Single-tenant data centers can easily grow to accommodate increasing data storage requirements.
- As the amount of data that the company uses increases, it becomes impractical for the data to be stored and processed in a single-tenant data center.
Explanation: Cloud computing offers many advantages to the company. Since the cloud data storage and processing facilities are owned by third-parties, the company doesn’t need to be concerned about how it will handle increasing data storage and processing demands with its own data center equipment. The company can easily increase or decrease processing power and storage capacity based on need. Also, cloud services are billed by usage, so the company doesn’t have the costs of supporting its own expensive data center that is not always used to maximum capacity.
-
Which Cloud computing service would be best for an organization that does not have the technical knowledge to host and maintain applications at their local site?
- SaaS
- IaaS
- PaaS
- ITaaS
Explanation: Software as a Service (SaaS) allows a business to host an application through a Cloud provider. The Cloud provider manages access to the application and maintains the application. The application can be utilized by any authorized device with an Internet connection.
-
A network client in a corporate environment reboots. Which type of server would most likely be used first?
- DNS
- DHCP
- FTP
- Telnet
- web
-
What is a common function of a proxy server?
- to store frequently accessed web pages on the internal network
- to control who is permitted to access the internal network
- to detect malicious signatures by monitoring traffic that is entering the internal network
- to provide access to a shared pool of configurable computing resources
Explanation: A proxy server is often responsible for caching web pages frequently accessed by internal users. If another internal user requests any of the stored pages, the proxy server can quickly provide the stored web pages to the internal user instead of sending the request over the Internet to the original web server.
-
ABC Company requires preventive maintenance for all local network cabling once a year. Which task should be included in the preventive maintenance program?
- Disconnect and reconnect all patch cables.
- Inspect all patch cables for breaks.
- Replace all labeling on the cables.
- Replace all cable supports to prevent loose attachment points.
Explanation: Network preventive procedures include checking the condition of cables, network devices, servers, and computers to make sure that they are kept clean and are in good working order.
-
What is a benefit of performing preventative maintenance at regular intervals?
- reduction in network downtime
- reduction in connectivity
- reduction in security threats
- reduction in EMI and RFI
Explanation: Performing preventative maintenance for a network at regular intervals prevents network downtime and network equipment failures. This will maintain good network performance, prevent the loss of bandwidth, and increase connectivity.
-
A user cannot access the network. While the technician is checking the computer, the other users on the same network report that they are having the same problem. Further investigation shows that the LED lights on each NIC are not lit. What should the technician do next?
- Check each computer to verify that they all have the same settings.
- Report the problem to the network administrator.
- Attempt to ping devices on other networks.
- Use nslookup to check network connectivity.
Explanation: Unlit LED indicators on multiple computers in the same network is a possible symptom of a network problem. If the NIC is not attached to the network, pings and commands like nslookup will fail. It is best to escalate the problem to the network administrator for further investigation.
-
A user can print to a printer that is on the same network, but the traffic of the user cannot reach the Internet. What is a possible cause of the problem?
- The PC default gateway address is missing or incorrect.
- The PC has an incorrect IP address.
- The network cable connected to the user PC is faulty.
- The NIC on the PC is faulty.
Explanation: The default gateway IP address is used to reach other networks, including the Internet.
-
A technician is investigating a report that a computer is unable to access network resources. The technician discovers that the computer has an IP address of 169.254.27.168. What is a logical first step in diagnosing this problem?
- Attempt to ping the default gateway.
- Check the NIC LED lights.
- Test that DNS is operating correctly.
- Activate Network Discovery and File Sharing.
Explanation: An IP address of 169.254.x.x indicates that the computer has not been able to receive an IP address from DHCP. There are many possible causes for this, but it is important to first check to see if the computer has any connection to the network at all. The LED lights on the NIC will indicate this. If the device does not have a valid network address from DHCP, pinging the default gateway or testing DNS will fail. This should already be apparent from the IP address, so this test offers no additional information. Similarly, DNS will also fail. This problem is not related to the Network Discovery and File Sharing settings.
A logical next step would be to inspect the cable if no LED lights are lit.
-
A Windows 7 computer is unable to reach a mapped drive on a file server that is on another network within the organization. Further investigation shows that the user is able to use a printer that is connected to the same network as the computer. Which action should the technician perform next?
- Verify that DNS name resolution is operating properly.
- Inspect the network patch cable for wear or breaks.
- Check Network Connection Details in the Windows GUI for the appropriate network connection.
- Check the link LED on the NIC.
Explanation: Network Connection Details in the Windows GUI allows the technician to check the IP addressing information of the computer. From the symptoms described, a good theory is that the default gateway setting is incorrect. Because the computer can access the printer, it is not necessary to check the cable or link lights to gather information to solve this problem. Finally, DNS is not implicated, because drive mappings on file servers within the organization are not assigned URLs.
-
A user has taken a personal laptop to work. The laptop is unable to discover the name of the office wireless network. What are two potential causes of this problem? (Choose two.)
- The wireless router is not broadcasting the SSID.
- The laptop has not received an IP address from the wireless router.
- The wireless router is set to mixed mode.
- The network does not support the wireless protocol in use by the laptop.
- The laptop must be configured with the office workgroup name.
Explanation: The laptop could be using an older NIC that uses a protocol not supported by the network. This would be especially likely if the wireless router was not configured in mixed mode. In addition, the wireless router could have SSID broadcasting deactivated. In either case, the computer would not be able to discover the network name. An IP address or workgroup configuration is not required to see the network name.
-
A network technician attempts to ping www.example.net from a customer computer, but the ping fails. Access to mapped network drives and a shared printer are working correctly. What are two potential causes for this problem? (Choose two.)
- The Windows domain or workgroup name that is configured on the computer is incorrect.
- The target web server is down.
- The computer has been assigned a static IP address.
- DNS service is unavailable on the customer network.
- The HTTP protocol is not working properly on the target server.
Explanation: A ping would fail if the destination device was not operational. It would also fail if the DNS server was unavailable to convert the URL to an IP address. The fact that a computer had a static IP address is not a factor. Even if the target protocol (HTTP) is not functioning, the server would still respond to a ping.
-
A technician uses the nbtstat -A 192.168.0.3 command. What does the technician expect to view in the command output?
- current connections and statistics
- network adapter configuration information
- a list of routers within the traffic path
- computer accounts and domain specific information
Explanation: The nbtstat command is used to display current connections, services, and statistics on local and remote computers.
-
Fill in the blank.
What is the acronym for the protocol that is used when securely communicating with a web server?
- HTTPS
-
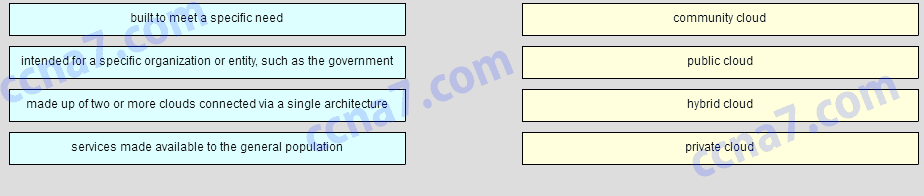
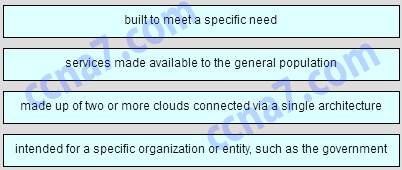
Match the definition to the of cloud.
- Question
- Answer
Explanation: Public cloud services are made available to the general population. Private cloud services are intended for a specific organization or entity. A custom cloud is built to meet the needs of a specific industry. A hybrid cloud is made up of two or more clouds that are connected via a single architecture.