Last Updated on October 26, 2019 by Admin
ITE 6.0 Pre-Test Online 2019
ITE 6.0 Pre-Test
Quiz-summary
0 of 40 questions completed
Questions:
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
Information
ITE 6.0 Pre-Test
You have already completed the quiz before. Hence you can not start it again.
Quiz is loading...
You must sign in or sign up to start the quiz.
You have to finish following quiz, to start this quiz:
Results
0 of 40 questions answered correctly
Your time:
Time has elapsed
You have reached 0 of 0 points, (0)
| Average score |
|
| Your score |
|
Categories
- Not categorized 0%
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
- Answered
- Review
-
Question 1 of 40
1. Question
1 pointsWhat is an advantage of purchasing a tablet rather than a laptop computer?Correct
Incorrect
-
Question 2 of 40
2. Question
1 pointsWhat is a possible hardware upgrade that can be used to add more storage space to a modern smartphone?Correct
Incorrect
Because of the of cellular phones, a very small storage device is desirable, such as a microSD card. CompactFlash is an older form of storage device; it is is too large for a cellular phone but it is widely used in cameras and video recorders because of its large capacity and fast access speed. Similarly, USB flash drives and hard disk drives are too large for a cellular phone.Hint
Because of the of cellular phones, a very small storage device is desirable, such as a microSD card. CompactFlash is an older form of storage device; it is is too large for a cellular phone but it is widely used in cameras and video recorders because of its large capacity and fast access speed. Similarly, USB flash drives and hard disk drives are too large for a cellular phone. -
Question 3 of 40
3. Question
1 pointsWhich component would be located inside the computer case?Correct
Incorrect
-
Question 4 of 40
4. Question
2 pointsWhich two devices are output devices? (Choose two.)Correct
Incorrect
-
Question 5 of 40
5. Question
1 pointsWhich hardware component must be installed in a PC to provide network connectivity?Correct
Incorrect
-
Question 6 of 40
6. Question
1 pointsCorrect
Incorrect
-
Question 7 of 40
7. Question
1 pointsHow can a section of text in a Notepad document be highlighted to be copied to another location within the document?Correct
Incorrect
-
Question 8 of 40
8. Question
1 pointsRefer to the exhibit. Why is Undo in black, while the other items are in gray?
Correct
Incorrect
-
Question 9 of 40
9. Question
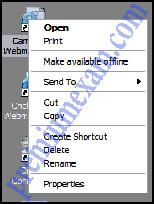
1 pointsRefer to the exhibit. What caused the pictured menu to appear on the user’s screen?
Correct
Incorrect
-
Question 10 of 40
10. Question
2 pointsWhich two operating systems are used in smartphones? (Choose two.)Correct
Incorrect
-
Question 11 of 40
11. Question
1 pointsA student purchased a new WiFi enabled tablet computer. What is required to connect this device to the Internet?Correct
Incorrect
-
Question 12 of 40
12. Question
2 pointsWhich two general precautions should be followed when using hand tools? (Choose two.)Correct
Incorrect
-
Question 13 of 40
13. Question
1 pointsWhich precaution should be taken before any electronic component is removed from a computer system?Correct
Incorrect
-
Question 14 of 40
14. Question
1 pointsWhich problem could occur if a screwdriver is used to pry the top off of a computer case?Correct
Incorrect
-
Question 15 of 40
15. Question
1 pointsWhat would be the most environmentally friendly procedure to consider in the design of a server room?Correct
Incorrect
-
Question 16 of 40
16. Question
2 pointsIn the event that a mobile device is lost or stolen, which two procedures can help protect private information that is stored on the device? (Choose two.)Correct
Incorrect
-
Question 17 of 40
17. Question
1 pointsWhat password would be considered a strong password?Correct
Incorrect
-
Question 18 of 40
18. Question
1 pointsThe failure rate in a certain brand of network interface card has been determined to be 15%. How many cards could be expected to fail in a company that has 80 of the cards installed?Correct
Incorrect
-
Question 19 of 40
19. Question
1 pointsIt is anticipated that a company-wide system upgrade will take approximately 60 person-hours to complete. How long will it take five technicians that each work the same amount of time to perform the refresh?Correct
Incorrect
-
Question 20 of 40
20. Question
1 pointsA classmate is creating an imaginary language. Here are some words the classmate has created:
stalopheah means good day
stalopjink means goodness
drahplunk means light house
flinsjink means happiness
plunkgrecki means house flyWhat would your classmate use to mean “daylight”?
Correct
Incorrect
-
Question 21 of 40
21. Question
1 pointsA user is looking for a wireless headphone for listening to songs stored on a smartphone. What wireless technology would the headphone use?Correct
Incorrect
Bluetooth is a wireless technology for data exchange over a short distance. It is suitable for connecting devices with simple tasks, such as headsets, keyboards, mice, and printers. Wi-Fi is suitable for variety of applications with high speed wireless connectivity required or preferred. Infrared requires a direct line of sight between the transmitter and the receiver. 3G/4G are cellular network technologies to manage voice calls and data transmission between clients and service providers.Hint
Bluetooth is a wireless technology for data exchange over a short distance. It is suitable for connecting devices with simple tasks, such as headsets, keyboards, mice, and printers. Wi-Fi is suitable for variety of applications with high speed wireless connectivity required or preferred. Infrared requires a direct line of sight between the transmitter and the receiver. 3G/4G are cellular network technologies to manage voice calls and data transmission between clients and service providers. -
Question 22 of 40
22. Question
1 pointsA customer connects a smartphone to a cloud service operated by the service provider. What can the cloud service provide to the customer?Correct
Incorrect
A cloud service provided by the service provider would allow customers to upload data from the device to the service and download data from the service to the device. Customers need information to be printed on local printers. Phone calls are handled by the cellular network operated by the service provider. Device troubleshooting should be performed locally.Hint
A cloud service provided by the service provider would allow customers to upload data from the device to the service and download data from the service to the device. Customers need information to be printed on local printers. Phone calls are handled by the cellular network operated by the service provider. Device troubleshooting should be performed locally. -
Question 23 of 40
23. Question
1 pointsWhat is the default subnet mask for the IP address 172.16.4.22?Correct
Incorrect
The first octet of the IP address indicates that this is a Class B address. The default subnet mask for a Class B address is 255.255.0.0.Hint
The first octet of the IP address indicates that this is a Class B address. The default subnet mask for a Class B address is 255.255.0.0. -
Question 24 of 40
24. Question
1 pointsWhich network protocol is used to automatically assign an IP address to a computer on a network?Correct
Incorrect
A Dynamic Host Configuration Protocol (DHCP) server automatically assigns IP addresses, simplifying the addressing process. FTP manages file transfers. SMTP sends email. ICMP is a messaging protocol that is used in troubleshooting. APIPA is Automatic Private IP Addressing, a Windows operating feature that allows DHCP clients to obtain addresses even when a DHCP server is not present.Hint
A Dynamic Host Configuration Protocol (DHCP) server automatically assigns IP addresses, simplifying the addressing process. FTP manages file transfers. SMTP sends email. ICMP is a messaging protocol that is used in troubleshooting. APIPA is Automatic Private IP Addressing, a Windows operating feature that allows DHCP clients to obtain addresses even when a DHCP server is not present. -
Question 25 of 40
25. Question
6 pointsMatch the icon to its likely associated use. (Not all options are used.)
Sort elements
- Explorer
- Word
- IE
- Acrobat Reader
- Safely Remove Hardware
- PowerPoint
-
search for a saved computer hardware exam
-
reaccess a business letter currently being typed
-
access www.cisco.com
-
reaccess a currently opened .pdf document
-
safely remove a flash drive
Correct
Incorrect
-
Question 26 of 40
26. Question
1 pointsWhich type of interface should a customer choose if connecting a single cable from a Microsoft Windows computer to output both audio and video to a high definition television?Correct
Incorrect
The high definition multimedia interface or HDMI connector is used for outputting both audio and video on a single cable. A PS/2 port connects a keyboard or a mouse to a computer. Digital visual interfaces and DB-15 connectors are only used for video output.Hint
The high definition multimedia interface or HDMI connector is used for outputting both audio and video on a single cable. A PS/2 port connects a keyboard or a mouse to a computer. Digital visual interfaces and DB-15 connectors are only used for video output. -
Question 27 of 40
27. Question
1 pointsWhich key or key sequence pressed during the boot process will allow a user to start a Windows PC using the last known good configuration?Correct
Incorrect
-
Question 28 of 40
28. Question
1 pointsA technician has installed a new sound card in a PC but it is not operating correctly. Where should the technician look to investigate driver problems?Correct
Incorrect
Device Manager can be used to view information about a particular piece of hardware, to view the driver version, to update the driver or roll it back, or to disable/enable a particular device.Hint
Device Manager can be used to view information about a particular piece of hardware, to view the driver version, to update the driver or roll it back, or to disable/enable a particular device. -
Question 29 of 40
29. Question
1 pointsA technician notices that an application is not responding to commands and that the computer seems to respond slowly when applications are opened. What is the best administrative tool to force the release of system resources from the unresponsive application?Correct
Incorrect
Use the Task Manager Performance tab to see a visual representation of CPU and RAM utilization. This is helpful in determining if more memory is needed. Use the Applications tab to halt an application that is not responding.Hint
Use the Task Manager Performance tab to see a visual representation of CPU and RAM utilization. This is helpful in determining if more memory is needed. Use the Applications tab to halt an application that is not responding. -
Question 30 of 40
30. Question
1 pointsWhich action can reduce the risk of ESD damage when computer equipment is being worked on?Correct
Incorrect
To help prevent ESD damage, use grounded mats on work benches and grounded floor mats in work areas. You can also use an antistatic wrist strap to prevent ESD strikes except when working inside power supplies or CRT monitors.Hint
To help prevent ESD damage, use grounded mats on work benches and grounded floor mats in work areas. You can also use an antistatic wrist strap to prevent ESD strikes except when working inside power supplies or CRT monitors. -
Question 31 of 40
31. Question
1 pointsWhen should a technician avoid wearing an antistatic wrist strap?Correct
Incorrect
A power supply unit or CRT monitor are both able to retain large amounts of power after being turned off. These types of devices are too dangerous to connect an antistatic wrist strap to. Antistatic wrist straps are commonly worn when upgrading RAM or replacing a hard drive.Hint
A power supply unit or CRT monitor are both able to retain large amounts of power after being turned off. These types of devices are too dangerous to connect an antistatic wrist strap to. Antistatic wrist straps are commonly worn when upgrading RAM or replacing a hard drive. -
Question 32 of 40
32. Question
1 pointsWhat can be tested with a digital multimeter?Correct
Incorrect
A digital multimeter can test the integrity of circuits and the quality of electricity in computer components.Hint
A digital multimeter can test the integrity of circuits and the quality of electricity in computer components. -
Question 33 of 40
33. Question
1 pointsA technician wants to allow users to backup and restore all the files on their computers, but does not want the users to be able to make changes to the system. How should the technician give users this functionality?Correct
Incorrect
It is better to grant permissions at group level than individual permissions. This way any member of a group would have the respective permissions to carry out the permitted tasks and allows for a tighter control of what the group members can do in a given environment. It also makes it easier to administer the environment.Hint
It is better to grant permissions at group level than individual permissions. This way any member of a group would have the respective permissions to carry out the permitted tasks and allows for a tighter control of what the group members can do in a given environment. It also makes it easier to administer the environment. -
Question 34 of 40
34. Question
1 pointsWhat characterizes a DDoS attack?Correct
Incorrect
-
Question 35 of 40
35. Question
1 pointsWhich is the correct procedure to put out a fire with a fire extinguisher after the pin is pulled?Correct
Incorrect
Anyone using a fire extinguisher should remember the basic rules of operation:
P – Pull the pin.
A – Aim at the base of the fire, not at the flames.
S – Squeeze the lever.
S – Sweep the nozzle from side to side.Hint
Anyone using a fire extinguisher should remember the basic rules of operation:
P – Pull the pin.
A – Aim at the base of the fire, not at the flames.
S – Squeeze the lever.
S – Sweep the nozzle from side to side. -
Question 36 of 40
36. Question
1 pointsWhat type of device provides power to a computer and allows it to be safely shut down in the event of a power loss?Correct
Incorrect
An uninterruptible power supply or UPS contains a battery backup that provides consistent power through brownouts and blackouts until the battery power is emptied. Many UPS systems can safely shut down a computer prior to the loss of battery power.Hint
An uninterruptible power supply or UPS contains a battery backup that provides consistent power through brownouts and blackouts until the battery power is emptied. Many UPS systems can safely shut down a computer prior to the loss of battery power. -
Question 37 of 40
37. Question
1 pointsWhich measure can help control RFI effects on wireless networks?Correct
Incorrect
A wireless network (IEEE 802.11) can be affected by radio frequency interference because it shares the same radio frequency range with other devices, such as cordless phones.Hint
A wireless network (IEEE 802.11) can be affected by radio frequency interference because it shares the same radio frequency range with other devices, such as cordless phones. -
Question 38 of 40
38. Question
1 pointsA computer is assigned an IP address of 169.254.33.16. What can be said about the computer, based on the assigned address?Correct
Incorrect
If a computer is configured with DHCP but it cannot communicate with the DHCP server in order to obtain an IP address, the Windows OS automatically assigns a link-local IP, in the range of 169.254.0.0 to 169.254.255.255. The computer can only communicate with other computers connected to the same 169.254.0.0/16 network and cannot communicate with computers in another network.Hint
If a computer is configured with DHCP but it cannot communicate with the DHCP server in order to obtain an IP address, the Windows OS automatically assigns a link-local IP, in the range of 169.254.0.0 to 169.254.255.255. The computer can only communicate with other computers connected to the same 169.254.0.0/16 network and cannot communicate with computers in another network. -
Question 39 of 40
39. Question
1 pointsSeveral messages sent to the network administrator are reporting that access to a secure server using HTTPS is failing. After checking recent updates to the company firewall, the administrator learns that the firewall is blocking HTTPS. Which port should be opened to solve the problem?Correct
Incorrect
-
Question 40 of 40
40. Question
2 pointsA network administrator has finished migrating from a peer-to-peer network to a new client-server network configuration. What are two advantages of the new configuration? (Choose two.)Correct
Incorrect
Centralization in a client-server network configuration provides better monitoring for security, as well as easier access to resources. The total cost may be higher because a network administrator is required, but reliability and scalability are enhanced.Hint
Centralization in a client-server network configuration provides better monitoring for security, as well as easier access to resources. The total cost may be higher because a network administrator is required, but reliability and scalability are enhanced.