Last Updated on October 28, 2019 by Admin
ITN Final Exam Form A Online
ITN -- Final Exam Form A
Quiz-summary
0 of 54 questions completed
Questions:
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
- 41
- 42
- 43
- 44
- 45
- 46
- 47
- 48
- 49
- 50
- 51
- 52
- 53
- 54
Information
ITN — Final Exam Form A
You have already completed the quiz before. Hence you can not start it again.
Quiz is loading...
You must sign in or sign up to start the quiz.
You have to finish following quiz, to start this quiz:
Results
0 of 54 questions answered correctly
Your time:
Time has elapsed
You have reached 0 of 0 points, (0)
| Average score |
|
| Your score |
|
Categories
- Not categorized 0%
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
- 41
- 42
- 43
- 44
- 45
- 46
- 47
- 48
- 49
- 50
- 51
- 52
- 53
- 54
- Answered
- Review
-
Question 1 of 54
1. Question
1 pointsWhat is a characteristic of a fault tolerant network?Correct
Incorrect
Fault tolerant networks limit the impact of a failure because the networks are built in a way that allows for quick recovery when such a failure occurs. These networks depend on multiple or redundant paths between the source and destination of a message.
A scalable network can expand quickly to support new users and applications without impacting the performance of the service being delivered to existing users.
Quality of service (QoS) is a mechanism for managing congestion and ensuring reliable delivery of content to all users.Hint
Fault tolerant networks limit the impact of a failure because the networks are built in a way that allows for quick recovery when such a failure occurs. These networks depend on multiple or redundant paths between the source and destination of a message.
A scalable network can expand quickly to support new users and applications without impacting the performance of the service being delivered to existing users.
Quality of service (QoS) is a mechanism for managing congestion and ensuring reliable delivery of content to all users. -
Question 2 of 54
2. Question
1 pointsThree bank employees are using the corporate network. The first employee uses a web browser to view a company web page in order to read some announcements. The second employee accesses the corporate database to perform some financial transactions. The third employee participates in an important live audio conference with other corporate managers in branch offices. If QoS is implemented on this network, what will be the priorities from highest to lowest of the different data types?Correct
Incorrect
QoS mechanisms enable the establishment of queue management strategies that enforce priorities for different categories of application data. Thus, this queuing enables voice data to have priority over transaction data, which has priority over web data.Hint
QoS mechanisms enable the establishment of queue management strategies that enforce priorities for different categories of application data. Thus, this queuing enables voice data to have priority over transaction data, which has priority over web data. -
Question 3 of 54
3. Question
1 pointsWhat is a benefit of using cloud computing in networking?Correct
Incorrect
Cloud computing extends IT’s capabilities without requiring investment in new infrastructure, training new personnel, or licensing new software. These services are available on-demand and delivered economically to any device anywhere in the world without compromising security or function. BYOD is about end users having the freedom to use personal tools to access information and communicate across a business or campus network. Smart home technology is integrated into every-day appliances allowing them to interconnect with other devices, making them more ‘smart’ or automated. Powerline networking is a trend for home networking that uses existing electrical wiring to connect devices to the network wherever there is an electrical outlet, saving the cost of installing data cables.Hint
Cloud computing extends IT’s capabilities without requiring investment in new infrastructure, training new personnel, or licensing new software. These services are available on-demand and delivered economically to any device anywhere in the world without compromising security or function. BYOD is about end users having the freedom to use personal tools to access information and communicate across a business or campus network. Smart home technology is integrated into every-day appliances allowing them to interconnect with other devices, making them more ‘smart’ or automated. Powerline networking is a trend for home networking that uses existing electrical wiring to connect devices to the network wherever there is an electrical outlet, saving the cost of installing data cables. -
Question 4 of 54
4. Question
1 pointsWhat is the function of the shell in an OS?Correct
Incorrect
Most operating systems contain a shell and a kernel. The kernel interacts with the hardware and the shell interfaces between the kernel and the users.Hint
Most operating systems contain a shell and a kernel. The kernel interacts with the hardware and the shell interfaces between the kernel and the users. -
Question 5 of 54
5. Question
1 pointsWhich connection provides a secure CLI session with encryption to a Cisco switch?Correct
Incorrect
A CLI session using Secure Shell (SSH) provides enhanced security because SSH supports strong passwords and encryption during the transport of session data. The other methods support authentication but not encryption.Hint
A CLI session using Secure Shell (SSH) provides enhanced security because SSH supports strong passwords and encryption during the transport of session data. The other methods support authentication but not encryption. -
Question 6 of 54
6. Question
1 pointsA network technician is attempting to configure an interface by entering the following command: SanJose(config)# ip address 192.168.2.1 255.255.255.0. The command is rejected by the device. What is the reason for this?Correct
Incorrect
The wrong mode of operation is being used. The CLI prompt indicates that the mode of operation is global configuration. IP addresses must be configured from interface configuration mode, as indicated by the SanJose(config-if)# prompt.Hint
The wrong mode of operation is being used. The CLI prompt indicates that the mode of operation is global configuration. IP addresses must be configured from interface configuration mode, as indicated by the SanJose(config-if)# prompt. -
Question 7 of 54
7. Question
1 pointsAn administrator uses the Ctrl-Shift-6 key combination on a switch after issuing the ping command. What is the purpose of using these keystrokes?Correct
Incorrect
To interrupt an IOS process such as ping or traceroute, a user enters the Ctrl-Shift-6 key combination. Tab completes the remainder of parameters or arguments within a command. To exit from configuration mode to privileged mode use the Ctrl-Z keystroke. CTRL-R will redisplay the line just typed, thus making it easier for the user to press Enter and reissue the ping command.Hint
To interrupt an IOS process such as ping or traceroute, a user enters the Ctrl-Shift-6 key combination. Tab completes the remainder of parameters or arguments within a command. To exit from configuration mode to privileged mode use the Ctrl-Z keystroke. CTRL-R will redisplay the line just typed, thus making it easier for the user to press Enter and reissue the ping command. -
Question 8 of 54
8. Question
1 pointsRefer to the exhibit. A network administrator is configuring access control to switch SW1. If the administrator uses a console connection to connect to the switch, which password is needed to access user EXEC mode?
Correct
Incorrect
Telnet accesses a network device through the virtual interface configured with the line VTY command. The password configured under this is required to access the user EXEC mode. The password configured under the line console 0 command is required to gain entry through the console port, and the enable and enable secret passwords are used to allow entry into the privileged EXEC mode.Hint
Telnet accesses a network device through the virtual interface configured with the line VTY command. The password configured under this is required to access the user EXEC mode. The password configured under the line console 0 command is required to gain entry through the console port, and the enable and enable secret passwords are used to allow entry into the privileged EXEC mode. -
Question 9 of 54
9. Question
1 pointsOn which switch interface would an administrator configure an IP address so that the switch can be managed remotely?Correct
Incorrect
Interface VLAN 1 is a virtual interface on a switch, called SVI (switch virtual interface). Configuring an IP address on the default SVI, interface VLAN 1, will allow a switch to be accessed remotely. The VTY line must also be configured to allow remote access, but an IP address cannot be configured on this line.Hint
Interface VLAN 1 is a virtual interface on a switch, called SVI (switch virtual interface). Configuring an IP address on the default SVI, interface VLAN 1, will allow a switch to be accessed remotely. The VTY line must also be configured to allow remote access, but an IP address cannot be configured on this line. -
Question 10 of 54
10. Question
1 pointsWhat protocol is responsible for controlling the size of segments and the rate at which segments are exchanged between a web client and a web server?Correct
Incorrect
TCP is a Layer 4 protocol of the OSI model. TCP has several responsibilities in the network communication process. It divides large messages into smaller segments which are more efficient to send across the network. It also controls the size and rate of segments exchanged between clients and servers.Hint
TCP is a Layer 4 protocol of the OSI model. TCP has several responsibilities in the network communication process. It divides large messages into smaller segments which are more efficient to send across the network. It also controls the size and rate of segments exchanged between clients and servers. -
Question 11 of 54
11. Question
1 pointsWhat is an advantage to using a protocol that is defined by an open standard?Correct
Incorrect
A monopoly by one company is not a good idea from a user point of view. If a protocol can only be run on one brand, it makes it difficult to have mixed equipment in a network. A proprietary protocol is not free to use. An open standard protocol will in general be implemented by a wide range of vendors.Hint
A monopoly by one company is not a good idea from a user point of view. If a protocol can only be run on one brand, it makes it difficult to have mixed equipment in a network. A proprietary protocol is not free to use. An open standard protocol will in general be implemented by a wide range of vendors. -
Question 12 of 54
12. Question
2 pointsWhat are two benefits of using a layered network model? (Choose two.)Correct
Incorrect
Some vendors have developed their own reference models and protocols. Today, if a device is to communicate on the Internet, the device must use the TCP/IP model. The benefits of using a layered model are as follows:
- assists in protocol design
- fosters competition between vendors
- prevents a technology that functions at one layer from affecting any other layer
- provides a common language for describing network functionality
- helps in visualizing the interaction between each layer and protocols between each layer
Hint
Some vendors have developed their own reference models and protocols. Today, if a device is to communicate on the Internet, the device must use the TCP/IP model. The benefits of using a layered model are as follows:
- assists in protocol design
- fosters competition between vendors
- prevents a technology that functions at one layer from affecting any other layer
- provides a common language for describing network functionality
- helps in visualizing the interaction between each layer and protocols between each layer
-
Question 13 of 54
13. Question
2 pointsWhich two OSI model layers have the same functionality as two layers of the TCP/IP model? (Choose two.)Correct
Incorrect
The OSI transport layer is functionally equivalent to the TCP/IP transport layer, and the OSI network layer is equivalent to the TCP/IP internet layer. The OSI data link and physical layers together are equivalent to the TCP/IP network access layer. The OSI session layer (with the presentation layer) is included within the TCP/IP application layer.Hint
The OSI transport layer is functionally equivalent to the TCP/IP transport layer, and the OSI network layer is equivalent to the TCP/IP internet layer. The OSI data link and physical layers together are equivalent to the TCP/IP network access layer. The OSI session layer (with the presentation layer) is included within the TCP/IP application layer. -
Question 14 of 54
14. Question
1 pointsWhich name is assigned to the transport layer PDU?Correct
Incorrect
Application data is passed down the protocol stack on its way to be transmitted across the network media. During the process, various protocols add information to it at each level. At each stage of the process, a PDU (protocol data unit) has a different name to reflect its new functions. The PDUs are named according to the protocols of the TCP/IP suite:
- Data – The general term for the PDU used at the application layer.
- Segment – transport layer PDU
- Packet – network layer PDU
- Frame – data link layer PDU
- Bits – A physical layer PDU used when physically transmitting data over the medium
Hint
Application data is passed down the protocol stack on its way to be transmitted across the network media. During the process, various protocols add information to it at each level. At each stage of the process, a PDU (protocol data unit) has a different name to reflect its new functions. The PDUs are named according to the protocols of the TCP/IP suite:
- Data – The general term for the PDU used at the application layer.
- Segment – transport layer PDU
- Packet – network layer PDU
- Frame – data link layer PDU
- Bits – A physical layer PDU used when physically transmitting data over the medium
-
Question 15 of 54
15. Question
1 pointsA network administrator is troubleshooting connectivity issues on a server. Using a tester, the administrator notices that the signals generated by the server NIC are distorted and not usable. In which layer of the OSI model is the error categorized?Correct
Incorrect
The NIC has responsibilities in both Layer 1 and Layer 2. The NIC encodes the frame as a series of signals that are transmitted onto the local media. This is the responsibility of the physical layer of the OSI model. The signal could be in the form of electrical, optical, or radio waves.Hint
The NIC has responsibilities in both Layer 1 and Layer 2. The NIC encodes the frame as a series of signals that are transmitted onto the local media. This is the responsibility of the physical layer of the OSI model. The signal could be in the form of electrical, optical, or radio waves. -
Question 16 of 54
16. Question
3 pointsA network administrator is measuring the transfer of bits across the company backbone for a mission critical financial application. The administrator notices that the network throughput appears lower than the bandwidth expected. Which three factors could influence the differences in throughput? (Choose three.)Correct
Incorrect
Throughput usually does not match the specified bandwidth of physical links due to multiple factors. These factors include, the amount of traffic, type of traffic, and latency created by the network devices the data has to cross.Hint
Throughput usually does not match the specified bandwidth of physical links due to multiple factors. These factors include, the amount of traffic, type of traffic, and latency created by the network devices the data has to cross. -
Question 17 of 54
17. Question
1 pointsWhat is a characteristic of UTP cabling?Correct
Incorrect
Cladding and immunization from electrical hazards are characteristics for fiber-optic cabling. A woven copper braid or metallic foil is used as a shield for the inner coaxial cable conductor. Cancellation is a property of UTP cabling where two wires are located adjacent to one another so each magnetic field cancels out the adjacent magnetic field.Hint
Cladding and immunization from electrical hazards are characteristics for fiber-optic cabling. A woven copper braid or metallic foil is used as a shield for the inner coaxial cable conductor. Cancellation is a property of UTP cabling where two wires are located adjacent to one another so each magnetic field cancels out the adjacent magnetic field. -
Question 18 of 54
18. Question
2 pointsWhat are two characteristics of fiber-optic cable? (Choose two.)Correct
Incorrect
Fiber-optic cabling supports higher bandwidth than UTP for longer distances. Fiber is immune to EMI and RFI, but costs more, requires more skill to install, and requires more safety precautions.Hint
Fiber-optic cabling supports higher bandwidth than UTP for longer distances. Fiber is immune to EMI and RFI, but costs more, requires more skill to install, and requires more safety precautions. -
Question 19 of 54
19. Question
1 pointsWhat is a characteristic of the LLC sublayer?Correct
Incorrect
The Logical Link Control (LLC) defines the software processes that provide services to the network layer protocols. The information is placed by LLC in the frame and identifies which network layer protocol is being used for the frame. This information allows multiple Layer 3 protocols, such as IPv4 and IPv6, to utilize the same network interface and media.Hint
The Logical Link Control (LLC) defines the software processes that provide services to the network layer protocols. The information is placed by LLC in the frame and identifies which network layer protocol is being used for the frame. This information allows multiple Layer 3 protocols, such as IPv4 and IPv6, to utilize the same network interface and media. -
Question 20 of 54
20. Question
1 pointsA network team is comparing physical WAN topologies for connecting remote sites to a headquarters building. Which topology provides high availability and connects some, but not all, remote sites?Correct
Incorrect
Partial mesh topologies provide high availability by interconnecting multiple remote sites, but do not require a connection between all remote sites. A mesh topology requires point-to-point links with every system being connected to every other system. A point-to-point topology is where each device is connected to one other device. A hub and spoke uses a central device in a star topology that connects to other point-to-point devices.Hint
Partial mesh topologies provide high availability by interconnecting multiple remote sites, but do not require a connection between all remote sites. A mesh topology requires point-to-point links with every system being connected to every other system. A point-to-point topology is where each device is connected to one other device. A hub and spoke uses a central device in a star topology that connects to other point-to-point devices. -
Question 21 of 54
21. Question
1 pointsWhat method is used to manage contention-based access on a wireless network?Correct
Incorrect
Carrier sense multiple access with collision avoidance (CSMA/CA) is used with wireless networking technology to mediate media contention. Carrier sense multiple access with collision detection (CSMA/CD) is used with wired Ethernet technology to mediate media contention. Priority ordering and token passing are not used (or not a method) for media access control.Hint
Carrier sense multiple access with collision avoidance (CSMA/CA) is used with wireless networking technology to mediate media contention. Carrier sense multiple access with collision detection (CSMA/CD) is used with wired Ethernet technology to mediate media contention. Priority ordering and token passing are not used (or not a method) for media access control. -
Question 22 of 54
22. Question
3 pointsWhat are the three primary functions provided by Layer 2 data encapsulation? (Choose three.)Correct
Incorrect
Through the framing process, delimiters are used to identify the start and end of the sequence of bits that make up a frame. Data link layer addressing is added to enable a frame to be delivered to a destination node. A cyclic redundancy check (CRC) field is calculated on every bit and added to the frame. If the CRC value contained in the arriving frame is the same as the one the receiving node creates, the frame will be processed.Hint
Through the framing process, delimiters are used to identify the start and end of the sequence of bits that make up a frame. Data link layer addressing is added to enable a frame to be delivered to a destination node. A cyclic redundancy check (CRC) field is calculated on every bit and added to the frame. If the CRC value contained in the arriving frame is the same as the one the receiving node creates, the frame will be processed. -
Question 23 of 54
23. Question
1 pointsWhat will a host on an Ethernet network do if it receives a frame with a destination MAC address that does not match its own MAC address?Correct
Incorrect
In an Ethernet network, each NIC in the network checks every arriving frame to see if the destination MAC address in the frame matches its own MAC address. If there is no match, the device discards the frame. If there is a match, the NIC passes the frame up to the next OSI layer.Hint
In an Ethernet network, each NIC in the network checks every arriving frame to see if the destination MAC address in the frame matches its own MAC address. If there is no match, the device discards the frame. If there is a match, the NIC passes the frame up to the next OSI layer. -
Question 24 of 54
24. Question
1 pointsWhich frame forwarding method receives the entire frame and performs a CRC check to detect errors before forwarding the frame?Correct
Incorrect
Fast-forward and fragment-free switching are variations of cut-through switching, which begins to forward the frame before the entire frame is received.Hint
Fast-forward and fragment-free switching are variations of cut-through switching, which begins to forward the frame before the entire frame is received. -
Question 25 of 54
25. Question
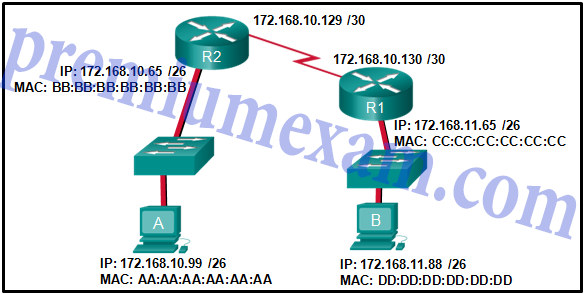
1 pointsRefer to the exhibit. If host A sends an IP packet to host B, what will the destination address be in the frame when it leaves host A?
Correct
Incorrect
When a host sends information to a distant network, the Layer 2 frame header will contain a source and destination MAC address. The source address will be the originating host device. The destination address will be the router interface that connects to the same network. In the case of host A sending information to host B, the source address is AA:AA:AA:AA:AA:AA and the destination address is the MAC address assigned to the R2 Ethernet interface, BB:BB:BB:BB:BB:BB.Hint
When a host sends information to a distant network, the Layer 2 frame header will contain a source and destination MAC address. The source address will be the originating host device. The destination address will be the router interface that connects to the same network. In the case of host A sending information to host B, the source address is AA:AA:AA:AA:AA:AA and the destination address is the MAC address assigned to the R2 Ethernet interface, BB:BB:BB:BB:BB:BB. -
Question 26 of 54
26. Question
1 pointsWhat addresses are mapped by ARP?Correct
Incorrect
ARP, or the Address Resolution Protocol, works by mapping a destination MAC address to a destination IPv4 address. The host knows the destination IPv4 address and uses ARP to resolve the corresponding destination MAC address.Hint
ARP, or the Address Resolution Protocol, works by mapping a destination MAC address to a destination IPv4 address. The host knows the destination IPv4 address and uses ARP to resolve the corresponding destination MAC address. -
Question 27 of 54
27. Question
2 pointsWhat are two services provided by the OSI network layer? (Choose two.)Correct
Incorrect
The OSI network layer provides several services to allow communication between devices:
- addressing
- encapsulation
- routing
- de-encapsulation
Error detection, placing frames on the media, and collision detection are all functions of the data ink layer.
Hint
The OSI network layer provides several services to allow communication between devices:
- addressing
- encapsulation
- routing
- de-encapsulation
Error detection, placing frames on the media, and collision detection are all functions of the data ink layer.
-
Question 28 of 54
28. Question
2 pointsWhat are two functions of NVRAM? (Choose two.)Correct
Incorrect
NVRAM is permanent memory storage, so the startup configuration file is preserved even if the router loses power.Hint
NVRAM is permanent memory storage, so the startup configuration file is preserved even if the router loses power. -
Question 29 of 54
29. Question
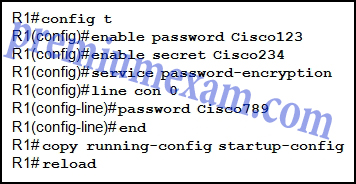
1 pointsRefer to the exhibit. What will be the result of entering this configuration the next time a network administrator connects a console cable to the router and no additional commands have been entered?
Correct
Incorrect
Until both the password password and the login commands are entered in console line configuration mode, no password is required to gain access to enable mode.Hint
Until both the password password and the login commands are entered in console line configuration mode, no password is required to gain access to enable mode. -
Question 30 of 54
30. Question
1 pointsWhat is the dotted decimal representation of the IPv4 address 11001011.00000000.01110001.11010011?Correct
Incorrect
Each section (octet) contains eight binary digits. Each digit represents a specific value (128, 64, 32, 16, 8, 4, 2, and 1). Everywhere there is a 1, the specific value is relevant. Add all relevant values in a particular octet to obtain the decimal value. For example binary 11001011 equals 203 in decimal.Hint
Each section (octet) contains eight binary digits. Each digit represents a specific value (128, 64, 32, 16, 8, 4, 2, and 1). Everywhere there is a 1, the specific value is relevant. Add all relevant values in a particular octet to obtain the decimal value. For example binary 11001011 equals 203 in decimal. -
Question 31 of 54
31. Question
3 pointsWhat are three characteristics of multicast transmission? (Choose three.)Correct
Incorrect
Broadcast messages consist of single packets that are sent to all hosts on a network segment. These types of messages are used to request IPv4 addresses, and map upper layer addresses to lower layer addresses. A multicast transmission is a single packet sent to a group of hosts and is used by routing protocols, such as OSPF and RIPv2, to exchange routes. The address range 224.0.0.0 to 224.0.0.255 is reserved for link-local addresses to reach multicast groups on a local network. -
Question 32 of 54
32. Question
3 pointsWhat are the three ranges of IP addresses that are reserved for internal private use? (Choose three.)Correct
Incorrect
The private IP address blocks that are used inside companies are as follows:
- 10.0.0.0 /8 (any address that starts with 10 in the first octet)
- 172.16.0.0 /12 (any address that starts with 172.16 in the first two octets through 172.31.255.255)
- 192.168.0.0 /16 (any address that starts with 192.168 in the first two octets)
-
Question 33 of 54
33. Question
1 pointsWhat purpose does NAT64 serve in IPv6?Correct
Incorrect
NAT64 is typically used in IPv6 when networks are being transitioned from IPv4 to IPv6. It allows the IPv6 networks to connect to IPv4 networks (such as the Internet), and works by translating the IPv6 packets into IPv4 packets. -
Question 34 of 54
34. Question
1 pointsWhat is the most compressed representation of the IPv6 address 2001:0000:0000:abcd:0000:0000:0000:0001?Correct
Incorrect
The IPv6 address 2001:0000:0000:abcd:0000:0000:0000:0001 in its most compressed format would be 2001:0:0:abcd::1. The first two hextets of zeros would each compress to a single zero. The three consecutive hextets of zeros can be compressed to a double colon ::. The three leading zeros in the last hextet can be removed. The double colon :: can only be used once in an address. -
Question 35 of 54
35. Question
1 pointsWhich range of link-local addresses can be assigned to an IPv6-enabled interface?Correct
Incorrect
Link-local addresses are in the range of FE80::/10 to FEBF::/10. The original IPv6 specification defined site-local addresses and used the prefix range FEC0::/10, but these addresses were deprecated by the IETF in favor of unique local addresses. FDEE::/7 is a unique local address because it is in the range of FC00::/7 to FDFF::/7. IPv6 multicast addresses have the prefix FF00::/8. -
Question 36 of 54
36. Question
1 pointsHow many valid host addresses are available on an IPv4 subnet that is configured with a /26 mask?Correct
Incorrect
When a /26 mask is used, 6 bits are used as host bits. With 6 bits, 64 addresses are possible, but one address is for the subnet number and one address is for a broadcast. This leaves 62 addresses that can be assigned to network devices. -
Question 37 of 54
37. Question
1 pointsA site administrator has been told that a particular network at the site must accommodate 126 hosts. Which subnet mask would be used that contains the required number of host bits?
Correct
Incorrect
The subnet mask of 255.255.255.0 has 8 host bits. The mask of 255.255.255.128 results in 7 host bits. The mask of 255.255.255.224 has 5 host bits. Finally, 255.255.255.240 represents 4 host bits. -
Question 38 of 54
38. Question
1 pointsWhich subnet would include the address 192.168.1.96 as a usable host address?Correct
Incorrect
For the subnet of 192.168.1.64/26, there are 6 bits for host addresses, yielding 64 possible addresses. However, the first and last subnets are the network and broadcast addresses for this subnet. Therefore, the range of host addresses for this subnet is 192.168.1.65 to 192.168.1.126. The other subnets do not contain the address 192.168.1.96 as a valid host address. -
Question 39 of 54
39. Question
1 pointsWhich statement is true about variable-length subnet masking?Correct
Incorrect
In variable-length subnet masking, bits are borrowed to create subnets. Additional bits may be borrowed to create additional subnets within the original subnets. This may continue until there are no bits available to borrow. -
Question 40 of 54
40. Question
1 pointsWhich scenario describes a function provided by the transport layer?Correct
Incorrect
The source and destination port numbers are used to identify the correct application and window within that application. -
Question 41 of 54
41. Question
1 pointsA user opens three browsers on the same PC to access http://www.cisco.com to search for certification course information. The Cisco web server sends a datagram as a reply to the request from one of the web browsers. Which information is used by the TCP/IP protocol stack in the PC to identify which of the three web browsers should receive the reply?Correct
Incorrect
Each web browser client application opens a randomly generated port number in the range of the registered ports and uses this number as the source port number in the datagram that it sends to a server. The server then uses this port number as the destination port number in the reply datagram that it sends to the web browser. The PC that is running the web browser application receives the datagram and uses the destination port number that is contained in this datagram to identify the client application.Hint
Each web browser client application opens a randomly generated port number in the range of the registered ports and uses this number as the source port number in the datagram that it sends to a server. The server then uses this port number as the destination port number in the reply datagram that it sends to the web browser. The PC that is running the web browser application receives the datagram and uses the destination port number that is contained in this datagram to identify the client application. -
Question 42 of 54
42. Question
2 pointsWhat are two ways that TCP uses the sequence numbers in a segment? (Choose two.)Correct
Incorrect
-
Question 43 of 54
43. Question
2 pointsWhich two tasks are functions of the presentation layer? (Choose two.)Correct
Incorrect
The presentation layer deals with common data format. Encryption, formatting, and compression are some of the functions of the layer. Addressing occurs in the network layer, session control occurs in the session layer, and authentication takes place in the application or session layer.Hint
The presentation layer deals with common data format. Encryption, formatting, and compression are some of the functions of the layer. Addressing occurs in the network layer, session control occurs in the session layer, and authentication takes place in the application or session layer. -
Question 44 of 54
44. Question
1 pointsWhat is a key characteristic of the peer-to-peer networking model?Correct
Incorrect
The peer-to-peer (P2P) networking model allows data, printer, and resource sharing without a dedicated server.Hint
The peer-to-peer (P2P) networking model allows data, printer, and resource sharing without a dedicated server. -
Question 45 of 54
45. Question
1 pointsA technician can ping the IP address of the web server of a remote company but cannot successfully ping the URL address of the same web server. Which software utility can the technician use to diagnose the problem?Correct
Incorrect
Traceroute (tracert) is a utility that generates a list of hops that were successfully reached along the path from source to destination.This list can provide important verification and troubleshooting information. The ipconfig utility is used to display the IP configuration settings on a Windows PC. The Netstat utility is used to identify which active TCP connections are open and running on a networked host. Nslookup is a utility that allows the user to manually query the name servers to resolve a given host name. This utility can also be used to troubleshoot name resolution issues and to verify the current status of the name servers.Hint
Traceroute (tracert) is a utility that generates a list of hops that were successfully reached along the path from source to destination.This list can provide important verification and troubleshooting information. The ipconfig utility is used to display the IP configuration settings on a Windows PC. The Netstat utility is used to identify which active TCP connections are open and running on a networked host. Nslookup is a utility that allows the user to manually query the name servers to resolve a given host name. This utility can also be used to troubleshoot name resolution issues and to verify the current status of the name servers. -
Question 46 of 54
46. Question
1 pointsWhich domain name would be an example of a top-level domain?Correct
Incorrect
Top-level domains represent a country or type of organization, such as .com or .edu.Hint
Top-level domains represent a country or type of organization, such as .com or .edu. -
Question 47 of 54
47. Question
1 pointsA PC obtains its IP address from a DHCP server. If the PC is taken off the network for repair, what happens to the IP address configuration?Correct
Incorrect
When a DCHP address is issued to a host, it is for a specific lease time. Once the lease expires, the address is returned to the DHCP pool.Hint
When a DCHP address is issued to a host, it is for a specific lease time. Once the lease expires, the address is returned to the DHCP pool. -
Question 48 of 54
48. Question
1 pointsA wireless host needs to request an IP address. What protocol would be used to process the request?Correct
Incorrect
The DHCP protocol is used to request, issue, and manage IP addressing information. CSMA/CD is the access method used with wired Ethernet. ICMP is used to test connectivity. SNMP is used with network management and FTP is used for file transfer.Hint
The DHCP protocol is used to request, issue, and manage IP addressing information. CSMA/CD is the access method used with wired Ethernet. ICMP is used to test connectivity. SNMP is used with network management and FTP is used for file transfer. -
Question 49 of 54
49. Question
1 pointsWhich example of malicious code would be classified as a Trojan horse?Correct
Incorrect
A Trojan horse is malicious code that has been written specifically to look like a legitimate program. This is in contrast to a virus, which simply attaches itself to an actual legitimate program. Viruses require manual intervention from a user to spread from one system to another, while a worm is able to spread automatically between systems by exploiting vulnerabilities on those devices.Hint
A Trojan horse is malicious code that has been written specifically to look like a legitimate program. This is in contrast to a virus, which simply attaches itself to an actual legitimate program. Viruses require manual intervention from a user to spread from one system to another, while a worm is able to spread automatically between systems by exploiting vulnerabilities on those devices. -
Question 50 of 54
50. Question
1 pointsWhen applied to a router, which command would help mitigate brute-force password attacks against the router?Correct
Incorrect
The login block-for command sets a limit on the maximum number of failed login attempts allowed within a defined period of time. If this limit is exceeded, no further logins are allowed for the specified period of time. This helps to mitigate brute-force password cracking since it will significantly increase the amount of time required to crack a password. The exec-timeout command specifies how long the session can be idle before the user is disconnected. The service password-encryption command encrypts the passwords in the running configuration. The banner motd command displays a message to users who are logging in to the device.Hint
The login block-for command sets a limit on the maximum number of failed login attempts allowed within a defined period of time. If this limit is exceeded, no further logins are allowed for the specified period of time. This helps to mitigate brute-force password cracking since it will significantly increase the amount of time required to crack a password. The exec-timeout command specifies how long the session can be idle before the user is disconnected. The service password-encryption command encrypts the passwords in the running configuration. The banner motd command displays a message to users who are logging in to the device. -
Question 51 of 54
51. Question
1 pointsA network technician suspects that a particular network connection between two Cisco switches is having a duplex mismatch. Which command would the technician use to see the Layer 1 and Layer 2 details of a switch port?Correct
Incorrect
The show interfaces command can be used on both routers and switches to see speed, duplex, media type, MAC address, port type, and other Layer 1/Layer 2-related information.Hint
The show interfaces command can be used on both routers and switches to see speed, duplex, media type, MAC address, port type, and other Layer 1/Layer 2-related information. -
Question 52 of 54
52. Question
1 pointsWhere are Cisco IOS debug output messages sent by default?Correct
Incorrect
Debug messages, like other IOS log messages, are sent to the console line by default. Sending these messages to the terminal lines requires the terminal monitor command.Hint
Debug messages, like other IOS log messages, are sent to the console line by default. Sending these messages to the terminal lines requires the terminal monitor command. -
Question 53 of 54
53. Question
6 pointsMatch the description with the associated IOS mode. (Not all options are used.)
Sort elements
- limited number of basic monitoring commands
- the first entrance into the CLI of an IOS device
- accessed by entering the enable command
- identified by a prompt ending with the # character
- changes made affect the operation of the device as a whole
- accessed by entering the configure terminal command
- used to enable the password for vty lines
-
user EXEC mode
-
user EXEC mode
-
privileged EXEC mode
-
privileged EXEC mode
-
global configuration mode
-
global configuration mode
Correct
Incorrect
-
Question 54 of 54
54. Question
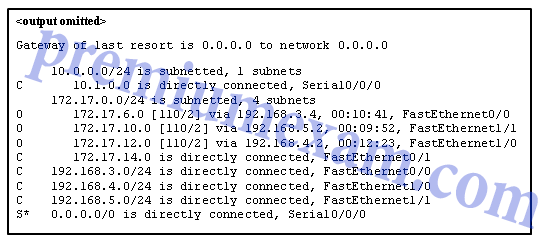
5 pointsRefer to the exhibit. Match the packets with their destination IP address to the exiting interfaces on the router. (Not all targets are used.)
Sort elements
- FastEthernet0/0
- FastEthernet0/1
- FastEthernet1/0
- FastEthernet1/1
- Serial0/0/0
- The packet is dropped.
-
packets with destinations of 172.17.6.15
-
packets with destinations of 172.17.14.8
-
packets with destinations of 172.17.12.10
-
packets with destinations of 172.17.10.5
-
packets with destinations of 172.17.8.20
Correct
Incorrect