Last Updated on October 28, 2019 by Admin
ITN Chapter 11 Quiz Online
ITN -- Chapter 11 Quiz
Quiz-summary
0 of 17 questions completed
Questions:
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
Information
ITN — Chapter 11 Quiz
You have already completed the quiz before. Hence you can not start it again.
Quiz is loading...
You must sign in or sign up to start the quiz.
You have to finish following quiz, to start this quiz:
Results
0 of 17 questions answered correctly
Your time:
Time has elapsed
You have reached 0 of 0 points, (0)
| Average score |
|
| Your score |
|
Categories
- Not categorized 0%
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- Answered
- Review
-
Question 1 of 17
1. Question
1 pointsWhich command will block login attempts on RouterA for a period of 30 seconds if there are 2 failed login attempts within 10 seconds?Correct
Incorrect
The correct syntax is RouterA(config)# login block-for (number of seconds) attempts (number of attempts) within (number of seconds).
Hint
The correct syntax is RouterA(config)# login block-for (number of seconds) attempts (number of attempts) within (number of seconds).
-
Question 2 of 17
2. Question
1 pointsA particular website does not appear to be responding on a Windows 7 computer. What command could the technician use to show any cached DNS entries for this web page?Correct
Incorrect
-
Question 3 of 17
3. Question
5 pointsMatch the type of threat with the cause. (Not all options are used.)Sort elements
- physical damage to servers, routers, switches, cabling plant, and workstations
- temperature extremes (too hot or too cold) or humidity extremes (too wet or too dry)
- voltage spikes, insufficient supply voltage (brownouts), unconditioned power (noise), and total power loss
- poor handling of key electrical components (electrostatic discharge), lack of critical spare parts, poor cabling, and poor labeling
- unauthorized access resulting in loss of data
-
hardware threats
-
environmental threats
-
electrical threats
-
maintenance threats
Correct
Incorrect
Physical threats can be classified into four categories:
- Environmental threats -Temperature extremes (too hot or too cold) or humidity extremes (too wet or too dry)
- Hardware threats – Physical damage to servers, routers, switches, cabling plant, and workstations
- Electrical threats – Voltage spikes, insufficient supply voltage (brownouts), unconditioned power (noise), and total power loss
- Maintenance threats – Poor handling of key electrical components (electrostatic discharge), lack of critical spare parts, poor cabling, and poor labeling
Hint
Physical threats can be classified into four categories:
- Environmental threats -Temperature extremes (too hot or too cold) or humidity extremes (too wet or too dry)
- Hardware threats – Physical damage to servers, routers, switches, cabling plant, and workstations
- Electrical threats – Voltage spikes, insufficient supply voltage (brownouts), unconditioned power (noise), and total power loss
- Maintenance threats – Poor handling of key electrical components (electrostatic discharge), lack of critical spare parts, poor cabling, and poor labeling
-
Question 4 of 17
4. Question
1 pointsWhich statement is true about Cisco IOS ping indicators?Correct
Incorrect
The most common indicators of a ping issued from the Cisco IOS are “!”, “.”, and “U”. The “!” indicates that the ping completed successfully, verifying connectivity at Layer 3. The “.” may indicate that a connectivity problem, routing problem, or device security issue exists along the path and that an ICMP destination unreachable message was not provided. The “U” indicates that a router along the path may not have had a route to the destination address, and that it responded with an ICMP unreachable message.
Hint
The most common indicators of a ping issued from the Cisco IOS are “!”, “.”, and “U”. The “!” indicates that the ping completed successfully, verifying connectivity at Layer 3. The “.” may indicate that a connectivity problem, routing problem, or device security issue exists along the path and that an ICMP destination unreachable message was not provided. The “U” indicates that a router along the path may not have had a route to the destination address, and that it responded with an ICMP unreachable message.
-
Question 5 of 17
5. Question
1 pointsA network technician is investigating network connectivity from a PC to a remote host with the address 10.1.1.5. Which command, when issued on a Windows PC, will display the path to the remote host?Correct
Incorrect
The tracert command is used to initiate a trace from the command prompt on a Windows PC. The traceroute command is used to initiate a trace from a Cisco router or switch. Some other PC operating systems, such as Linux and Mac OS also use the traceroute command. The ping command does not display the network path to the remote host.
Hint
The tracert command is used to initiate a trace from the command prompt on a Windows PC. The traceroute command is used to initiate a trace from a Cisco router or switch. Some other PC operating systems, such as Linux and Mac OS also use the traceroute command. The ping command does not display the network path to the remote host.
-
Question 6 of 17
6. Question
1 pointsWhat is considered the most effective way to mitigate a worm attack?Correct
Incorrect
Because worms take advantage of vulnerabilities in the system itself, the most effective way to mitigate worm attacks is to download security updates from the operating system vendor and patch all vulnerable systems.
Hint
Because worms take advantage of vulnerabilities in the system itself, the most effective way to mitigate worm attacks is to download security updates from the operating system vendor and patch all vulnerable systems.
-
Question 7 of 17
7. Question
1 pointsWhich element of scaling a network involves identifying the physical and logical topologies?Correct
Incorrect
To scale a network, several elements are required:
- Network documentation – physical and logical topology
- Device Inventory – list of devices that use or make up the network
- Budget – Itemized IT budget, including fiscal year equipment purchasing budget
- Traffic analysis – protocols, applications, and services and their respective traffic requirements should be documented
Hint
To scale a network, several elements are required:
- Network documentation – physical and logical topology
- Device Inventory – list of devices that use or make up the network
- Budget – Itemized IT budget, including fiscal year equipment purchasing budget
- Traffic analysis – protocols, applications, and services and their respective traffic requirements should be documented
-
Question 8 of 17
8. Question
1 pointsWhich protocol is used by the traceroute command to send and receive echo-requests and echo-replies?Correct
Incorrect
Traceroute uses the ICMP (Internet Control Message Protocol) to send and receive echo-request and echo-reply messages.
Hint
Traceroute uses the ICMP (Internet Control Message Protocol) to send and receive echo-request and echo-reply messages.
-
Question 9 of 17
9. Question
1 pointsA small company has only one router as the exit point to its ISP. Which solution could be adopted to maintain connectivity if the router itself, or its connection to the ISP, fails?Correct
Incorrect
Small networks generally have only one link to an ISP to establish a connection to the Internet. Problems can occur in the network, which can cause the disruption of this service. In order to keep connectivity, redundancy has to be provided. If the problem is in the router interface that is connected to the ISP, another interface can be activated on the router, so if one interface fails, traffic may be redirected toward the other interface. However, if the router itself fails, a second router that is connected to another ISP can be used as a backup.
Hint
Small networks generally have only one link to an ISP to establish a connection to the Internet. Problems can occur in the network, which can cause the disruption of this service. In order to keep connectivity, redundancy has to be provided. If the problem is in the router interface that is connected to the ISP, another interface can be activated on the router, so if one interface fails, traffic may be redirected toward the other interface. However, if the router itself fails, a second router that is connected to another ISP can be used as a backup.
-
Question 10 of 17
10. Question
2 pointsOn which two interfaces or ports can security be improved by configuring executive timeouts? (Choose two.)Correct
Incorrect
Executive timeouts allow the Cisco device to automatically disconnect users after they have been idle for the specified time. Console, vty, and aux ports can be configured with executive timeouts.
Hint
Executive timeouts allow the Cisco device to automatically disconnect users after they have been idle for the specified time. Console, vty, and aux ports can be configured with executive timeouts.
-
Question 11 of 17
11. Question
1 pointsWhat is one of the most effective security tools available for protecting users from external threats?Correct
Incorrect
A firewall is one of the most effective security tools for protecting internal network users from external threats. A firewall resides between two or more networks, controls the traffic between them, and helps prevent unauthorized access. A host intrusion prevention system can help prevent outside intruders and should be used on all systems.
Hint
A firewall is one of the most effective security tools for protecting internal network users from external threats. A firewall resides between two or more networks, controls the traffic between them, and helps prevent unauthorized access. A host intrusion prevention system can help prevent outside intruders and should be used on all systems.
-
Question 12 of 17
12. Question
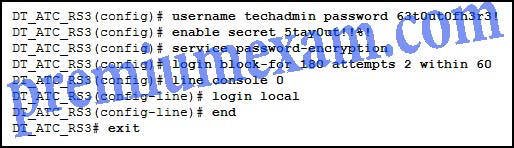
1 pointsRefer to the exhibit. The exhibited configuration is entered by a network administrator into a new router. Sometime later a network technician proceeds to log in to the router via a console connection. The technician enters techadmin as the user name and tries a password of 63t0ut0fh3r3!. What will be the result of this action?
Correct
Incorrect
Whenever an administrator connects to the console port, the configuration applied under the line con 0 interface determines how the user is authenticated. The console port configuration has the login command with local as the keyword. That means the username and password are required before the administrator is even allowed to see the enable mode prompt. Because the correct username and password was typed, the administrator will be presented with the enable mode prompt.
Hint
Whenever an administrator connects to the console port, the configuration applied under the line con 0 interface determines how the user is authenticated. The console port configuration has the login command with local as the keyword. That means the username and password are required before the administrator is even allowed to see the enable mode prompt. Because the correct username and password was typed, the administrator will be presented with the enable mode prompt.
-
Question 13 of 17
13. Question
1 pointsHow should traffic flow be captured in order to best understand traffic patterns in a network?Correct
Incorrect
Capturing traffic during low utilization time will not give a good representation of the different traffic types. Because some traffic could be local to a particular segment, the capture must be done on different network segments.
Hint
Capturing traffic during low utilization time will not give a good representation of the different traffic types. Because some traffic could be local to a particular segment, the capture must be done on different network segments.
-
Question 14 of 17
14. Question
1 pointsWhich process failed if a computer cannot access the Internet and received an IP address of 169.254.142.5?Correct
Incorrect
When a Windows computer cannot communicate with an IPv4 DHCP server, the computer automatically assigns itself an IP address in the169.254.0.0/16 range. Linux and Apple computers do not automatically assign an IP address.
Hint
When a Windows computer cannot communicate with an IPv4 DHCP server, the computer automatically assigns itself an IP address in the169.254.0.0/16 range. Linux and Apple computers do not automatically assign an IP address.
-
Question 15 of 17
15. Question
1 pointsAn administrator wants to back up a router configuration file to a USB drive that is connected to the router. Which command should the administrator use to verify that the USB drive is being recognized by the router?Correct
Incorrect
The show file systems command displays all of the available file systems on the device. If usbflash0: appears then the router recognizes the USB drive as a valid storage device. The pwd command shows the current directory being navigated, and the cd command is used to change the current directory. The dir flash0: command will show the contents of flash memory, not the USB drive.
Hint
The show file systems command displays all of the available file systems on the device. If usbflash0: appears then the router recognizes the USB drive as a valid storage device. The pwd command shows the current directory being navigated, and the cd command is used to change the current directory. The dir flash0: command will show the contents of flash memory, not the USB drive.
-
Question 16 of 17
16. Question
1 pointsFill in the blank.
Network services use ………….. to define a set of rules that govern how devices communicate and the data formats used in a network.Correct
Incorrect
Each application or network service uses protocols, which define the standards and data formats to be used. Without protocols, the data network would not have a common way to format and direct data.
Hint
Each application or network service uses protocols, which define the standards and data formats to be used. Without protocols, the data network would not have a common way to format and direct data.
-
Question 17 of 17
17. Question
1 pointsWhat type of traffic would most likely have the highest priority through the network?Correct
Incorrect
Not all traffic should receive the same treatment or priority through a network. Some types of traffic, such as voice and video, require the highest priority because they are very sensitive to network latency and delay. Other types of traffic, such as FTP, which is not sensitive to latency and delay, should be given the lowest level of priority so that the higher priority traffic can get through.
Hint
Not all traffic should receive the same treatment or priority through a network. Some types of traffic, such as voice and video, require the highest priority because they are very sensitive to network latency and delay. Other types of traffic, such as FTP, which is not sensitive to latency and delay, should be given the lowest level of priority so that the higher priority traffic can get through.