Last Updated on November 1, 2019 by Admin
Implementing Network Security (Version 2.0) – CCNA Security 2.0 Pretest Exam Online
CCNAS – Pretest Exam
Quiz-summary
0 of 40 questions completed
Questions:
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
Information
CCNAS – Pretest Exam
You have already completed the quiz before. Hence you can not start it again.
Quiz is loading...
You must sign in or sign up to start the quiz.
You have to finish following quiz, to start this quiz:
Results
0 of 40 questions answered correctly
Your time:
Time has elapsed
You have reached 0 of 0 points, (0)
| Average score |
|
| Your score |
|
Categories
- Not categorized 0%
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
- Answered
- Review
-
Question 1 of 40
1. Question
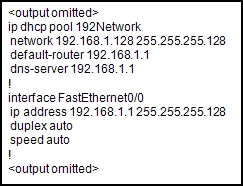
1 pointsRefer to the exhibit. A host connected to Fa0/0 is unable to acquire an IP address from this DHCP server. The output of the debug ip dhcp server command shows “DHCPD: there is no address pool for 192.168.1.1”. What is the problem?
Correct
Incorrect
-
Question 2 of 40
2. Question
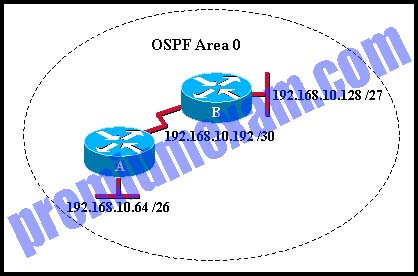
1 pointsRefer to the exhibit. Which sequence of commands will configure router A for OSPF?
Correct
Incorrect
-
Question 3 of 40
3. Question
1 pointsSwitch port Fa0/24 was previously configured as a trunk, but now it is to be used to connect a host to the network. How should the network administrator reconfigure switch port Fa0/24?
Correct
Incorrect
-
Question 4 of 40
4. Question
1 pointsWhich device performs the function of determining the path that messages should take through internetworks?
Correct
Incorrect
A router is used to determine the path that the messages should take through the network. A firewall is used to filter incoming and outgoing traffic. A DSL modem is used to provide Internet connection for a home or an organization.
Hint
A router is used to determine the path that the messages should take through the network. A firewall is used to filter incoming and outgoing traffic. A DSL modem is used to provide Internet connection for a home or an organization.
-
Question 5 of 40
5. Question
1 pointsThe ARP table in a switch maps which two types of address together?
Correct
Incorrect
The switch ARP table keeps a mapping of Layer 2 MAC addresses to Layer 3 IP addresses. These mappings can be learned by the switch dynamically through ARP or statically through manual configuration.
Hint
The switch ARP table keeps a mapping of Layer 2 MAC addresses to Layer 3 IP addresses. These mappings can be learned by the switch dynamically through ARP or statically through manual configuration.
-
Question 6 of 40
6. Question
1 pointsWhen applied to a router, which command would help mitigate brute-force password attacks against the router?
Correct
Incorrect
The login block-for command sets a limit on the maximum number of failed login attempts allowed within a defined period of time. If this limit is exceeded, no further logins are allowed for the specified period of time. This helps to mitigate brute-force password cracking since it will significantly increase the amount of time required to crack a password. The exec-timeout command specifies how long the session can be idle before the user is disconnected. The service password-encryption command encrypts the passwords in the running configuration. The banner motd command displays a message to users who are logging in to the device.Hint
The login block-for command sets a limit on the maximum number of failed login attempts allowed within a defined period of time. If this limit is exceeded, no further logins are allowed for the specified period of time. This helps to mitigate brute-force password cracking since it will significantly increase the amount of time required to crack a password. The exec-timeout command specifies how long the session can be idle before the user is disconnected. The service password-encryption command encrypts the passwords in the running configuration. The banner motd command displays a message to users who are logging in to the device. -
Question 7 of 40
7. Question
1 pointsWhich statement describes a characteristic of the traceroute utility?
Correct
Incorrect
Traceroute is a utility that generates a list of hops (or routers) along the path from a source host to the destination host.
Hint
Traceroute is a utility that generates a list of hops (or routers) along the path from a source host to the destination host.
-
Question 8 of 40
8. Question
1 pointsRefer to the exhibit. A network administrator has configured R1 as shown. When the administrator checks the status of the serial interface, the interface is shown as being administratively down. What additional command must be entered on the serial interface of R1 to bring the interface up?
Correct
Incorrect
By default all router interfaces are shut down. To bring the interfaces up, an administrator must issue the no shutdown command in interface mode.
Hint
By default all router interfaces are shut down. To bring the interfaces up, an administrator must issue the no shutdown command in interface mode.
-
Question 9 of 40
9. Question
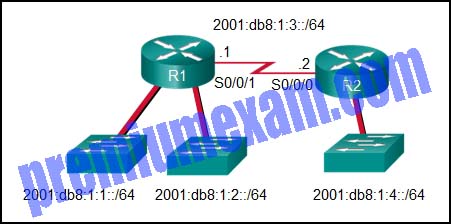
1 pointsRefer to the exhibit. What command would be used to configure a static route on R1 so that traffic from both LANs can reach the 2001:db8:1:4::/64 remote network?
Correct
Incorrect
To configure an IPv6 static route, use the ipv6 route command followed by the destination network. Then add either the IP address of the adjacent router or the interface R1 will use to transmit a packet to the 2001:db8:1:4::/64 network.Hint
To configure an IPv6 static route, use the ipv6 route command followed by the destination network. Then add either the IP address of the adjacent router or the interface R1 will use to transmit a packet to the 2001:db8:1:4::/64 network. -
Question 10 of 40
10. Question
2 pointsA network administrator needs to configure a standard ACL so that only the workstation of the administrator with the IP address 192.168.15.23 can access the virtual terminal of the main router. Which two configuration commands can achieve the task? (Choose two.)
Correct
Incorrect
To permit or deny one specific IP address, either the wildcard mask 0.0.0.0 (used after the IP address) or the wildcard mask keyword host (used before the IP address) can be used.Hint
To permit or deny one specific IP address, either the wildcard mask 0.0.0.0 (used after the IP address) or the wildcard mask keyword host (used before the IP address) can be used. -
Question 11 of 40
11. Question
1 pointsHow many classful networks are summarized by the static summary route ip route 192.168.32.0 255.255.248.0 S0/0/0?
Correct
Incorrect
A summary route of 192.168.32.0 with a network prefix of /21 will summarize 8 routes. The network prefix has moved from the classful boundary of 24 to the left by 3 bits. These 3 bits identify that 8 networks are summarized. The networks that are summarized would be 192.168.32.0/24 through 192.168.39.0/24.
Hint
A summary route of 192.168.32.0 with a network prefix of /21 will summarize 8 routes. The network prefix has moved from the classful boundary of 24 to the left by 3 bits. These 3 bits identify that 8 networks are summarized. The networks that are summarized would be 192.168.32.0/24 through 192.168.39.0/24.
-
Question 12 of 40
12. Question
2 pointsWhich two Layer 2 security best practices would help prevent VLAN hopping attacks? (Choose two.)
Correct
Incorrect
Allowing end-user devices to negotiate trunk settings via DTP can lead to a VLAN hopping attack, so DTP autonegotiation should be disabled on access ports. Configuring a trunk link with a native VLAN that is also used for end-users can lead to VLAN hopping attacks as well. The native VLAN should be set to a VLAN that is not used anywhere else.
Hint
Allowing end-user devices to negotiate trunk settings via DTP can lead to a VLAN hopping attack, so DTP autonegotiation should be disabled on access ports. Configuring a trunk link with a native VLAN that is also used for end-users can lead to VLAN hopping attacks as well. The native VLAN should be set to a VLAN that is not used anywhere else.
-
Question 13 of 40
13. Question
1 pointsA destination route in the routing table is indicated with a code D. Which kind of route entry is this?
Correct
Incorrect
Routes in a routing table are manually created or dynamically learned. Letter D indicates that the route was learned dynamically through the EIGRP routing protocol.
Hint
Routes in a routing table are manually created or dynamically learned. Letter D indicates that the route was learned dynamically through the EIGRP routing protocol.
-
Question 14 of 40
14. Question
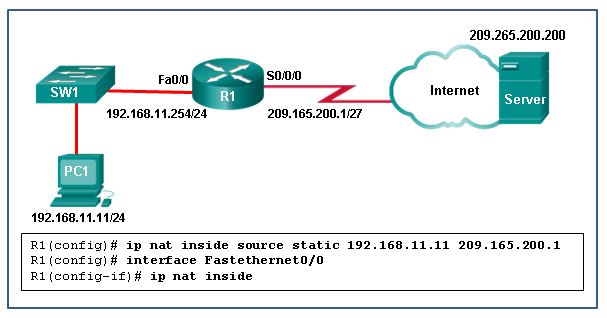
1 pointsRefer to the exhibit. What has to be done in order to complete the static NAT configuration on R1?
Correct
Incorrect
In order for NAT translations to work properly, both an inside and outside interface must be configured for NAT translation on the router.
Hint
In order for NAT translations to work properly, both an inside and outside interface must be configured for NAT translation on the router.
-
Question 15 of 40
15. Question
1 pointsWhich statement accurately describes dynamic NAT?
Correct
Incorrect
Dynamic NAT provides a dynamic mapping of inside local to inside global IP addresses. NAT is merely the one-to-one mapping of one address to another address without taking into account whether the address is public or private. DHCP is automatic assignment of IP addresses to hosts. DNS is mapping host names to IP addresses.
Hint
Dynamic NAT provides a dynamic mapping of inside local to inside global IP addresses. NAT is merely the one-to-one mapping of one address to another address without taking into account whether the address is public or private. DHCP is automatic assignment of IP addresses to hosts. DNS is mapping host names to IP addresses.
-
Question 16 of 40
16. Question
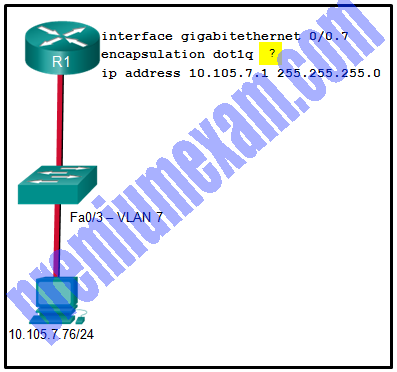
1 pointsRefer to the exhibit. A network administrator is configuring inter-VLAN routing on a network. For now, only one VLAN is being used, but more will be added soon. What is the missing parameter that is shown as the highlighted question mark in the graphic?
Correct
Incorrect
The completed command would be encapsulation dot1q 7. The encapsulation dot1q part of the command enables trunking and identifies the type of trunking to use. The 7 identifies the VLAN number.Hint
The completed command would be encapsulation dot1q 7. The encapsulation dot1q part of the command enables trunking and identifies the type of trunking to use. The 7 identifies the VLAN number. -
Question 17 of 40
17. Question
1 pointsWhich command would be best to use on an unused switch port if a company adheres to the best practices as recommended by Cisco?
Correct
Incorrect
Unlike router Ethernet ports, switch ports are enabled by default. Cisco recommends disabling any port that is not used. The ip dhcp snooping command globally enables DHCP snooping on a switch. Further configuration allows defining ports that can respond to DHCP requests. The switchport port-security command is used to protect the network from unidentified or unauthorized attachment of network devices.Hint
Unlike router Ethernet ports, switch ports are enabled by default. Cisco recommends disabling any port that is not used. The ip dhcp snooping command globally enables DHCP snooping on a switch. Further configuration allows defining ports that can respond to DHCP requests. The switchport port-security command is used to protect the network from unidentified or unauthorized attachment of network devices. -
Question 18 of 40
18. Question
1 pointsA small company has a web server in the office that is accessible from the Internet. The IP address 192.168.10.15 is assigned to the web server. The network administrator is configuring the router so that external clients can access the web server over the Internet. Which item is required in the NAT configuration?
Correct
Incorrect
A static NAT configuration is necessary for a web server that is accessible from the Internet. The configuration is achieved via an ip nat inside source static <inside local> <inside global> command under the global configuration mode. An IP address pool and an ACL are necessary when configuring dynamic NAT and PAT. The keyword overload is used to configure PAT.
Hint
A static NAT configuration is necessary for a web server that is accessible from the Internet. The configuration is achieved via an ip nat inside source static <inside local> <inside global> command under the global configuration mode. An IP address pool and an ACL are necessary when configuring dynamic NAT and PAT. The keyword overload is used to configure PAT.
-
Question 19 of 40
19. Question
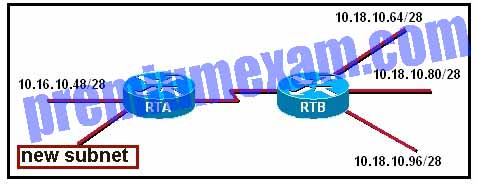
1 pointsRefer to the exhibit. What would be a valid network address for the new subnet on RTA?
Correct
Incorrect
-
Question 20 of 40
20. Question
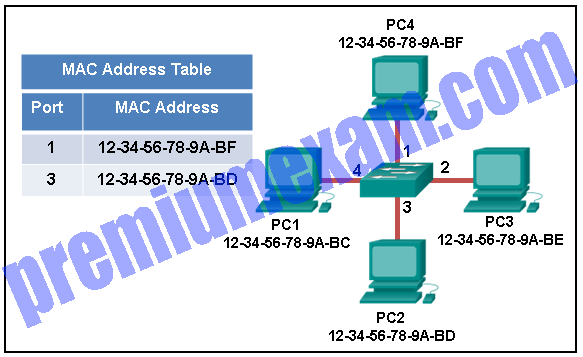
1 pointsRefer to the exhibit. The exhibit shows a small switched network and the contents of the MAC address table of the switch. PC1 has sent a frame addressed to PC3. What will the switch do with the frame?
Correct
Incorrect
The MAC address of PC3 is not present in the MAC table of the switch. Because the switch does not know where to send the frame that is addressed to PC3, it will forward the frame to all the switch ports, except for port 4, which is the incoming port.
Hint
The MAC address of PC3 is not present in the MAC table of the switch. Because the switch does not know where to send the frame that is addressed to PC3, it will forward the frame to all the switch ports, except for port 4, which is the incoming port.
-
Question 21 of 40
21. Question
2 pointsWhich two wildcard masks are required in an extended access list entry that blocks the traffic from network 192.168.20.0/26 to network 172.16.32.0/28? (Choose two.)
Correct
Incorrect
-
Question 22 of 40
22. Question
2 pointsWhich two statements describe static routes? (Choose two.)
Correct
Incorrect
-
Question 23 of 40
23. Question
1 pointsWhen is UDP preferred to TCP?
Correct
Incorrect
UDP can be used when an application can tolerate some data loss. UDP is the preferred protocol for applications that provide voice or video that cannot tolerate delay.
Hint
UDP can be used when an application can tolerate some data loss. UDP is the preferred protocol for applications that provide voice or video that cannot tolerate delay.
-
Question 24 of 40
24. Question
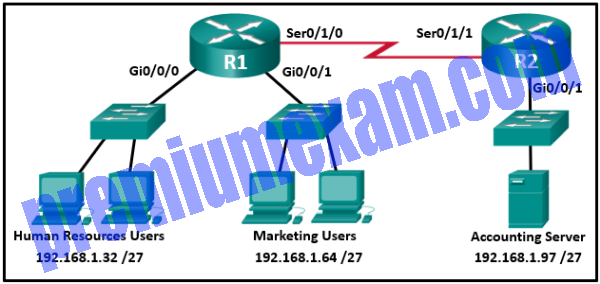
1 pointsRefer to the exhibit. An extended access list has been created to prevent human resource users from gaining access to the accounting server. All other network traffic is to be permitted. When following the ACL configuration guidelines, on which router, interface, and direction should the access list be applied?
Correct
Incorrect
The ACL configuration guidelines recommend placing extended access control lists as close to the source of network traffic as possible and placing standard access control lists as close to the destination of network traffic as possible.
Hint
The ACL configuration guidelines recommend placing extended access control lists as close to the source of network traffic as possible and placing standard access control lists as close to the destination of network traffic as possible.
-
Question 25 of 40
25. Question
1 pointsRefer to the exhibit. R1 was configured with the static route command ip route 209.165.200.224 255.255.255.224 S0/0/0 and consequently users on network 172.16.0.0/16 are unable to reach resources on the Internet. How should this static route be changed to allow user traffic from the LAN to reach the Internet?
Correct
Incorrect
The static route on R1 has been incorrectly configured with the wrong destination network and mask. The correct destination network and mask is 0.0.0.0 0.0.0.0.
Hint
The static route on R1 has been incorrectly configured with the wrong destination network and mask. The correct destination network and mask is 0.0.0.0 0.0.0.0.
-
Question 26 of 40
26. Question
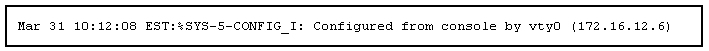
2 pointsRefer to the exhibit. What two pieces of information can be gathered from the generated message? (Choose two.)
Correct
Incorrect
A Cisco router log message consists for three parts:
1) the timestamp
2) the log message and severity level
3) the message textHint
A Cisco router log message consists for three parts:
1) the timestamp
2) the log message and severity level
3) the message text -
Question 27 of 40
27. Question
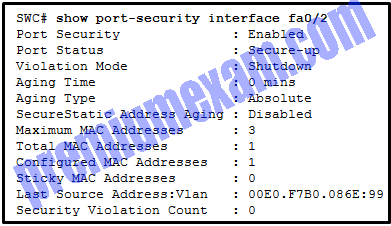
3 pointsRefer to the exhibit. The network administrator is configuring the port security feature on switch SWC. The administrator issued the command show port-security interface fa 0/2 to verify the configuration. What can be concluded from the output that is shown? (Choose three.)
Correct
Incorrect
Because the security violation count is at 0, no violation has occurred. The system shows that 3 MAC addresses are allowed on port fa0/2, but only one has been configured and no sticky MAC addresses have been learned. The port is up because of the port status of secure-up. The violation mode is what happens when an unauthorized device is attached to the port. A port must be in access mode in order to activate and use port security.
Hint
Because the security violation count is at 0, no violation has occurred. The system shows that 3 MAC addresses are allowed on port fa0/2, but only one has been configured and no sticky MAC addresses have been learned. The port is up because of the port status of secure-up. The violation mode is what happens when an unauthorized device is attached to the port. A port must be in access mode in order to activate and use port security.
-
Question 28 of 40
28. Question
3 pointsWhich three statements describe limitations in using privilege levels for assigning command authorization? (Choose three.)
Correct
Incorrect
An administrator can create customized privilege levels and assign different commands to each level. However, this method of controlling he level of access to the router has limitations. Using privilege levels access to specific interfaces or ports cannot be controlled and availability of commands cannot be customized across levels.
Hint
An administrator can create customized privilege levels and assign different commands to each level. However, this method of controlling he level of access to the router has limitations. Using privilege levels access to specific interfaces or ports cannot be controlled and availability of commands cannot be customized across levels.
-
Question 29 of 40
29. Question
2 pointsWhat are two protocols that are used by AAA to authenticate users against a central database of usernames and password? (Choose two.)
Correct
Incorrect
By using TACACS+ or RADIUS, AAA can authenticate users from a database of usernames and passwords stored centrally on a server such as a Cisco ACS server.
Hint
By using TACACS+ or RADIUS, AAA can authenticate users from a database of usernames and passwords stored centrally on a server such as a Cisco ACS server.
-
Question 30 of 40
30. Question
1 pointsWhat is the main difference between the implementation of IDS and IPS devices?
Correct
Incorrect
An IPS is deployed in inline mode and will not allow malicious traffic to enter the internal network without first analyzing it. An advantage of this is that it can stop an attack immediately. An IDS is deployed in promiscuous mode. It copies the traffic patterns and analyzes them offline, thus it cannot stop the attack immediately and it relies on another device to take further actions once it detects an attack. Being deployed in inline mode, an IPS can negatively impact the traffic flow. Both IDS and IPS can use signature-based technology to detect malicious packets. An IPS cannot replace other security devices, such as firewalls, because they perform different tasks.
Hint
An IPS is deployed in inline mode and will not allow malicious traffic to enter the internal network without first analyzing it. An advantage of this is that it can stop an attack immediately. An IDS is deployed in promiscuous mode. It copies the traffic patterns and analyzes them offline, thus it cannot stop the attack immediately and it relies on another device to take further actions once it detects an attack. Being deployed in inline mode, an IPS can negatively impact the traffic flow. Both IDS and IPS can use signature-based technology to detect malicious packets. An IPS cannot replace other security devices, such as firewalls, because they perform different tasks.
-
Question 31 of 40
31. Question
1 pointsA network technician has been asked to design a virtual private network between two branch routers. Which type of cryptographic key should be used in this scenario?
Correct
Incorrect
A symmetric key requires that both routers have access to the secret key that is used to encrypt and decrypt exchanged data.
Hint
A symmetric key requires that both routers have access to the secret key that is used to encrypt and decrypt exchanged data.
-
Question 32 of 40
32. Question
1 pointsWhat is a difference between ASA IPv4 ACLs and IOS IPv4 ACLs?
Correct
Incorrect
There are many similarities between ASA ACLs and IOS ACLs, including:
- In both, there is an implicit deny any
- Only one ACL per interface, per protocol, per direction still applies.
- Both use deny and permit ACEs.
- ACLs can be either named or numbered.
ASA ACLs differ from IOS ACLs in that they use a network mask (e.g., 255.255.255.0) instead of a wildcard mask (e.g. 0.0.0.255). Although most ASA ACLs are named, they can also be numbered.
Hint
There are many similarities between ASA ACLs and IOS ACLs, including:
- In both, there is an implicit deny any
- Only one ACL per interface, per protocol, per direction still applies.
- Both use deny and permit ACEs.
- ACLs can be either named or numbered.
ASA ACLs differ from IOS ACLs in that they use a network mask (e.g., 255.255.255.0) instead of a wildcard mask (e.g. 0.0.0.255). Although most ASA ACLs are named, they can also be numbered.
-
Question 33 of 40
33. Question
1 pointsWhat type of algorithms require sender and receiver to exchange a secret key that is used to ensure the confidentiality of messages?
Correct
Incorrect
Symmetric algorithms use the same key, a secret key, to encrypt and decrypt data. This key must be pre-shared before communication can occur. Asymmetric algorithms require more processing power and overhead on the communicating devices because these keys can be long in order to avoid being hacked.
Hint
Symmetric algorithms use the same key, a secret key, to encrypt and decrypt data. This key must be pre-shared before communication can occur. Asymmetric algorithms require more processing power and overhead on the communicating devices because these keys can be long in order to avoid being hacked.
-
Question 34 of 40
34. Question
1 pointsWhat is the one major difference between local AAA authentication and using the login local command when configuring device access authentication?
Correct
Incorrect
Local AAA authentication works very similar to the login local command, except that it allows you to specify backup authentication methods as well. Both methods require that local usernames and passwords be manually configured on the router.Hint
Local AAA authentication works very similar to the login local command, except that it allows you to specify backup authentication methods as well. Both methods require that local usernames and passwords be manually configured on the router. -
Question 35 of 40
35. Question
1 pointsWhat is a result of securing the Cisco IOS image using the Cisco IOS Resilient Configuration feature?
Correct
Incorrect
When using the Cisco IOS Resilient Configuration feature, a secure copy of the IOS image is stored in flash and is hidden from view and and not included in any directory listings.
Hint
When using the Cisco IOS Resilient Configuration feature, a secure copy of the IOS image is stored in flash and is hidden from view and and not included in any directory listings.
-
Question 36 of 40
36. Question
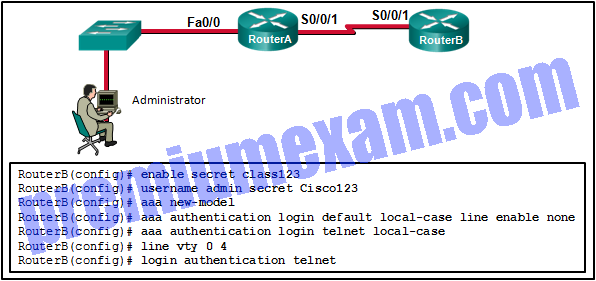
1 pointsRefer to the exhibit. The administrator can ping the S0/0/1 interface of RouterB but is unable to gain Telnet access to the router by using the password cisco123. What is a possible cause of the problem?
Correct
Incorrect
To authenticate and log in using a Telnet vty line, the network administrator is required to use the local username and password that has been configured on the local router. This is evidenced by the application of the aaa authentication login telnet local-case command. The administrator must use a capital C in Cisco123 to match the applied configuration.
Hint
To authenticate and log in using a Telnet vty line, the network administrator is required to use the local username and password that has been configured on the local router. This is evidenced by the application of the aaa authentication login telnet local-case command. The administrator must use a capital C in Cisco123 to match the applied configuration.
-
Question 37 of 40
37. Question
1 pointsWhich IDS/IPS signature alarm will look for packets that are destined to or from a particular port?
Correct
Incorrect
Cisco IDS and IPS sensors can use four types of signature alarms or triggers:
- Pattern-based detection – also known as signature-based detection, searches for a specific and pre-defined pattern. In most cases, the pattern is matched to the signature only if the suspect packet is associated with a particular service or destined to or from particular ports.
- Anomaly-based detection – also known as profile-based detection, involves first defining a profile of what is considered normal for the network or host. After defining normal activity, the signature triggers an action if excessive activity occurs beyond a specified threshold that is not included in the normal profile.
- Policy-based detection – also known as behavior-based detection, is similar to pattern-based detection, but instead of trying to define specific patterns, the administrator defines behaviors that are suspicious based on historical analysis.
- Honey pot-based detection – uses a dummy server to attract attacks.
Hint
Cisco IDS and IPS sensors can use four types of signature alarms or triggers:
- Pattern-based detection – also known as signature-based detection, searches for a specific and pre-defined pattern. In most cases, the pattern is matched to the signature only if the suspect packet is associated with a particular service or destined to or from particular ports.
- Anomaly-based detection – also known as profile-based detection, involves first defining a profile of what is considered normal for the network or host. After defining normal activity, the signature triggers an action if excessive activity occurs beyond a specified threshold that is not included in the normal profile.
- Policy-based detection – also known as behavior-based detection, is similar to pattern-based detection, but instead of trying to define specific patterns, the administrator defines behaviors that are suspicious based on historical analysis.
- Honey pot-based detection – uses a dummy server to attract attacks.
-
Question 38 of 40
38. Question
3 pointsWhich three actions can the Cisco IOS Firewall IPS feature be configured to take when an intrusion activity is detected? (Choose three.)
Correct
Incorrect
In IPS implementation, when a signature detects a matching activity, the signature triggers one or more of these actions:
- Generates an alert
- Logs the activity
- Drops or prevent the activity
- Resets a TCP connection
- Blocks future activity
- Allows the activity
Hint
In IPS implementation, when a signature detects a matching activity, the signature triggers one or more of these actions:
- Generates an alert
- Logs the activity
- Drops or prevent the activity
- Resets a TCP connection
- Blocks future activity
- Allows the activity
-
Question 39 of 40
39. Question
1 pointsWhat Layer 2 attack is mitigated by disabling Dynamic Trunking Protocol?
Correct
Incorrect
Mitigating a VLAN hopping attack can be done by disabling Dynamic Trunking Protocol (DTP) and by setting the native VLAN of trunk links to VLANs not in use.
Hint
Mitigating a VLAN hopping attack can be done by disabling Dynamic Trunking Protocol (DTP) and by setting the native VLAN of trunk links to VLANs not in use.
-
Question 40 of 40
40. Question
3 pointsMatch the network security testing technique with how it is used to test network security. (Not all options are used.)
Sort elements
- used to determine the possible consequences of successful attacks on the network
- used to discover available resources on the network
- used to find weaknesses and misconfigurations on network systems
- used to detect and report changes made to systems
-
penetration testing
-
network scanning
-
vulnerability scanning
Correct
Incorrect
Network scanning tools are used to probe network devices, servers and hosts for open TCP or UDP ports. Vulnerability scanning tools are used to discover security weaknesses in a network or computer system. Penetration testing tools are used to determine the possible outcome of a successful attack on a network or computer system.
Hint
Network scanning tools are used to probe network devices, servers and hosts for open TCP or UDP ports. Vulnerability scanning tools are used to discover security weaknesses in a network or computer system. Penetration testing tools are used to determine the possible outcome of a successful attack on a network or computer system.