Last Updated on October 29, 2019 by Admin
CCNA CyberOps SECOPS (210-255) Cert Practice Exam Online
CCNA CyberOps 1.1 -- SECOPS (210-255) Cert Practice Exam
Quiz-summary
0 of 55 questions completed
Questions:
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
- 41
- 42
- 43
- 44
- 45
- 46
- 47
- 48
- 49
- 50
- 51
- 52
- 53
- 54
- 55
Information
CCNA CyberOps 1.1 — SECOPS (210-255) Cert Practice Exam
You have already completed the quiz before. Hence you can not start it again.
Quiz is loading...
You must sign in or sign up to start the quiz.
You have to finish following quiz, to start this quiz:
Results
0 of 55 questions answered correctly
Your time:
Time has elapsed
You have reached 0 of 0 points, (0)
| Average score |
|
| Your score |
|
Categories
- Not categorized 0%
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
- 41
- 42
- 43
- 44
- 45
- 46
- 47
- 48
- 49
- 50
- 51
- 52
- 53
- 54
- 55
- Answered
- Review
-
Question 1 of 55
1. Question
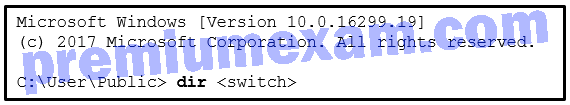
1 pointsRefer to the exhibit. A security specialist is checking if files in the directory contain ADS data. Which switch should be used to show that a file has ADS attached?
Correct
Incorrect
By using NTFS, Alternate Data Streams (ADSs) can be connected to a file as an attribute called $DATA. The command dir /r can be used to see if a file contains ADS data.
Hint
By using NTFS, Alternate Data Streams (ADSs) can be connected to a file as an attribute called $DATA. The command dir /r can be used to see if a file contains ADS data.
-
Question 2 of 55
2. Question
1 pointsWhen attempting to improve system performance for Linux computers with a limited amount of memory, why is increasing the size of the swap file system not considered the best solution?
Correct
Incorrect
The swap file system is used by Linux when it runs out of physical memory. When needed, the kernel moves inactive RAM content to the swap partition on the hard disk. Storing and retrieving content in the swap partition is much slower than RAM is, and therefore using the swap partition should not be considered the best solution to improving system performance.
Hint
The swap file system is used by Linux when it runs out of physical memory. When needed, the kernel moves inactive RAM content to the swap partition on the hard disk. Storing and retrieving content in the swap partition is much slower than RAM is, and therefore using the swap partition should not be considered the best solution to improving system performance.
-
Question 3 of 55
3. Question
1 pointsHow much overhead does the TCP header add to data from the application layer?
Correct
Incorrect
The Layer 4 header in a TCP segment is the TCP header, which is 20 bytes in length. This adds 20 bytes of overhead to the data from the application layer in the composition of a TCP segment.
Hint
The Layer 4 header in a TCP segment is the TCP header, which is 20 bytes in length. This adds 20 bytes of overhead to the data from the application layer in the composition of a TCP segment.
-
Question 4 of 55
4. Question
3 pointsWhich three fields are found in both the TCP and UDP headers? (Choose three.)
Correct
Incorrect
The UPD header has four fields. Three of these fields are in common with the TCP header. These three fields are the source port, destination port, and checksum.
Hint
The UPD header has four fields. Three of these fields are in common with the TCP header. These three fields are the source port, destination port, and checksum.
-
Question 5 of 55
5. Question
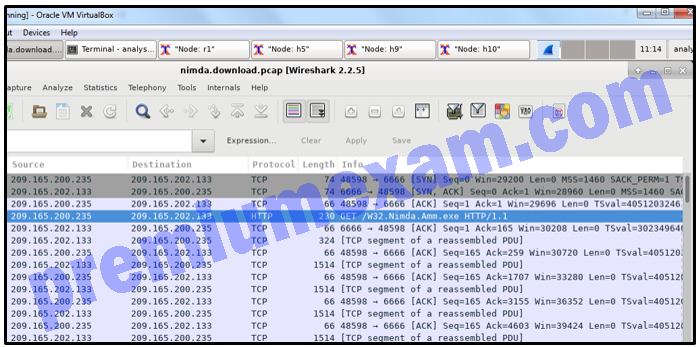
1 pointsRefer to the exhibit. A security specialist is using Wireshark to review a PCAP file generated by tcpdump. When the client initiated a file download request, which source socket pair was used?
Correct
Incorrect
The combination of the source IP address and source port number, or the destination IP address and destination port number, is known as a socket. A socket is shown as the IP address and associated port number with a colon in between the two (IP_address:port_number).
Hint
The combination of the source IP address and source port number, or the destination IP address and destination port number, is known as a socket. A socket is shown as the IP address and associated port number with a colon in between the two (IP_address:port_number).
-
Question 6 of 55
6. Question
1 pointsWhich field in the IPv6 header points to optional network layer information that is carried in the IPv6 packet?
Correct
Incorrect
Optional Layer 3 information about fragmentation, security, and mobility is carried inside of extension headers in an IPv6 packet. The next header field of the IPv6 header acts as a pointer to these optional extension headers if they are present.
Hint
Optional Layer 3 information about fragmentation, security, and mobility is carried inside of extension headers in an IPv6 packet. The next header field of the IPv6 header acts as a pointer to these optional extension headers if they are present.
-
Question 7 of 55
7. Question
3 pointsWhich three IPv4 header fields have no equivalent in an IPv6 header? (Choose three.)
Correct
Incorrect
Unlike IPv4, IPv6 routers do not perform fragmentation. Therefore, all three fields supporting fragmentation in the IPv4 header are removed and have no equivalent in the IPv6 header. These three fields are fragment offset, flag, and identification. IPv6 does support host packet fragmentation through the use of extension headers, which are not part of the IPv6 header.
Hint
Unlike IPv4, IPv6 routers do not perform fragmentation. Therefore, all three fields supporting fragmentation in the IPv4 header are removed and have no equivalent in the IPv6 header. These three fields are fragment offset, flag, and identification. IPv6 does support host packet fragmentation through the use of extension headers, which are not part of the IPv6 header.
-
Question 8 of 55
8. Question
1 pointsWhich technology is used by Cisco Advanced Malware Protection (AMP) in defending and protecting against known and emerging threats?
Correct
Incorrect
Cisco AMP uses threat intelligence along with known file signatures to identify and block policy-violating file types and exploitations.
Hint
Cisco AMP uses threat intelligence along with known file signatures to identify and block policy-violating file types and exploitations.
-
Question 9 of 55
9. Question
1 pointsWhen establishing a network profile for an organization, which element describes the time between the establishment of a data flow and its termination?
Correct
Incorrect
A network profile should include some important elements, such as the following:
- Total throughput – the amount of data passing from a given source to a given destination in a given period of time
- Session duration – the time between the establishment of a data flow and its termination
- Ports used – a list of TCP or UDP processes that are available to accept data
- Critical asset address space – the IP addresses or the logical location of essential systems or data
Hint
A network profile should include some important elements, such as the following:
- Total throughput – the amount of data passing from a given source to a given destination in a given period of time
- Session duration – the time between the establishment of a data flow and its termination
- Ports used – a list of TCP or UDP processes that are available to accept data
- Critical asset address space – the IP addresses or the logical location of essential systems or data
-
Question 10 of 55
10. Question
1 pointsA network administrator is creating a network profile to generate a network baseline. What is included in the critical asset address space element?
Correct
Incorrect
A network profile should include some important elements, such as the following:
- Total throughput – the amount of data passing from a given source to a given destination in a given period of time
- Session duration – the time between the establishment of a data flow and its termination
- Ports used – a list of TCP or UDP processes that are available to accept data
- Critical asset address space – the IP addresses or the logical location of essential systems or data
Hint
A network profile should include some important elements, such as the following:
- Total throughput – the amount of data passing from a given source to a given destination in a given period of time
- Session duration – the time between the establishment of a data flow and its termination
- Ports used – a list of TCP or UDP processes that are available to accept data
- Critical asset address space – the IP addresses or the logical location of essential systems or data
-
Question 11 of 55
11. Question
1 pointsWhen a server profile for an organization is being established, which element describes the TCP and UDP daemons and ports that are allowed to be open on the server?
Correct
Incorrect
A server profile will often contain the following:
- Listening ports – the TCP and UDP daemons and ports that are allowed to be open on the server
- User accounts – the parameters defining user access and behavior
- Service accounts – the definitions of the type of service that an application is allowed to run on a server
- Software environment – the tasks, processes, and applications that are permitted to run on the server
Hint
A server profile will often contain the following:
- Listening ports – the TCP and UDP daemons and ports that are allowed to be open on the server
- User accounts – the parameters defining user access and behavior
- Service accounts – the definitions of the type of service that an application is allowed to run on a server
- Software environment – the tasks, processes, and applications that are permitted to run on the server
-
Question 12 of 55
12. Question
1 pointsWhen establishing a server profile for an organization, which element describes the type of service that an application is allowed to run on the server?
Correct
Incorrect
A server profile should contain some important elements including these:
- Listening ports – the TCP and UDP daemons and ports that are allowed to be open on the server
- User accounts – the parameters defining user access and behavior
- Service accounts – the definitions of the type of service that an application is allowed to run on a server
- Software environment – the tasks, processes, and applications that are permitted to run on the server
Hint
A server profile should contain some important elements including these:
- Listening ports – the TCP and UDP daemons and ports that are allowed to be open on the server
- User accounts – the parameters defining user access and behavior
- Service accounts – the definitions of the type of service that an application is allowed to run on a server
- Software environment – the tasks, processes, and applications that are permitted to run on the server
-
Question 13 of 55
13. Question
3 pointsWhat are the three impact metrics contained in the CVSS 3.0 Base Metric Group? (Choose three.)
Correct
Incorrect
The Common Vulnerability Scoring System (CVSS) is a vendor-neutral, industry standard, open framework for weighing the risks of a vulnerability using a variety of metrics. CVSS uses three groups of metrics to assess vulnerability, the Base Metric Group, Temporal Metric Group, and Environmental Metric Group. The Base Metric Group has two classes of metrics (exploitability and impact). The impact metrics are rooted in the following areas: confidentiality, integrity, and availability.
Hint
The Common Vulnerability Scoring System (CVSS) is a vendor-neutral, industry standard, open framework for weighing the risks of a vulnerability using a variety of metrics. CVSS uses three groups of metrics to assess vulnerability, the Base Metric Group, Temporal Metric Group, and Environmental Metric Group. The Base Metric Group has two classes of metrics (exploitability and impact). The impact metrics are rooted in the following areas: confidentiality, integrity, and availability.
-
Question 14 of 55
14. Question
1 pointsWhich metric in the CVSS Base Metric Group is used with an attack vector?
Correct
Incorrect
The attack vector is one of several metrics defined in the Common Vulnerability Scoring System (CVSS) Base Metric Group Exploitability metrics. The attack vector is how close the threat actor is to the vulnerable component. The farther away the threat actor is to the component, the higher the severity because threat actors close to the network are easier to detect and mitigate.
Hint
The attack vector is one of several metrics defined in the Common Vulnerability Scoring System (CVSS) Base Metric Group Exploitability metrics. The attack vector is how close the threat actor is to the vulnerable component. The farther away the threat actor is to the component, the higher the severity because threat actors close to the network are easier to detect and mitigate.
-
Question 15 of 55
15. Question
1 pointsA cybersecurity analyst is performing a CVSS assessment on an attack where a web link was sent to several employees. Once clicked, an internal attack was launched. Which CVSS Base Metric Group Exploitability metric is used to document that the user had to click on the link in order for the attack to occur?
Correct
Incorrect
The CVSS Base Metric Group has the following metrics: attack vector, attack complexity, privileges required, user interaction, and scope. The user interaction metric expresses the presence or absence of the requirement for user interaction in order for an exploit to be successful.
Hint
The CVSS Base Metric Group has the following metrics: attack vector, attack complexity, privileges required, user interaction, and scope. The user interaction metric expresses the presence or absence of the requirement for user interaction in order for an exploit to be successful.
-
Question 16 of 55
16. Question
1 pointsWhich statement describes the card verification value (CVV) for a credit card?
Correct
Incorrect
The card verification value (CVV), or card verification code (CVC), or card security code (CSC) is a security feature of a credit card, usually 3 or 4 digits printed on the back of the card.
Hint
The card verification value (CVV), or card verification code (CVC), or card security code (CSC) is a security feature of a credit card, usually 3 or 4 digits printed on the back of the card.
-
Question 17 of 55
17. Question
1 pointsAfter a security monitoring tool identifies a malware attachment entering the network, what is the benefit of performing a retrospective analysis?
Correct
Incorrect
General security monitoring can identify when a malware attachment enters a network and which host is first infected. Retrospective analysis takes the next step and is the tracking of the behavior of the malware from that point forward.
Hint
General security monitoring can identify when a malware attachment enters a network and which host is first infected. Retrospective analysis takes the next step and is the tracking of the behavior of the malware from that point forward.
-
Question 18 of 55
18. Question
2 pointsWhat are two of the 5-tuples? (Choose two.)
Correct
Incorrect
The components of a 5-tuple include a source IP address and port number, destination IP address and port number, and the protocol in use.
Hint
The components of a 5-tuple include a source IP address and port number, destination IP address and port number, and the protocol in use.
-
Question 19 of 55
19. Question
1 pointsWhat are security event logs commonly based on when sourced by traditional firewalls?
Correct
Incorrect
Traditional firewalls commonly provide security event logs based on the 5-tuples of source IP address and port number, destination IP address and port number, and the protocol in use.
Hint
Traditional firewalls commonly provide security event logs based on the 5-tuples of source IP address and port number, destination IP address and port number, and the protocol in use.
-
Question 20 of 55
20. Question
1 pointsWhen real-time reporting of security events from multiple sources is being received, which function in SIEM provides capturing and processing of data in a common format?
Correct
Incorrect
SIEM combines SEM and SIM tools to provide some useful functions, one of which is data normalization. Data normalization is the process of mapping log messages from different systems into a common data model in order to analyze related security events, even if they are initially logged in different source formats.
Hint
SIEM combines SEM and SIM tools to provide some useful functions, one of which is data normalization. Data normalization is the process of mapping log messages from different systems into a common data model in order to analyze related security events, even if they are initially logged in different source formats.
-
Question 21 of 55
21. Question
1 pointsWhat is a goal of deploying an in-line security device that can analyze data as a normalized stream?
Correct
Incorrect
An IPS is an in-line security device that can analyze data as a normalized stream to reduce or eliminate the possibility of security evasions.
Hint
An IPS is an in-line security device that can analyze data as a normalized stream to reduce or eliminate the possibility of security evasions.
-
Question 22 of 55
22. Question
2 pointsWhat are two sources of data in the operation of a security information and event management (SIEM) system? (Choose two.)
Correct
Incorrect
Security information and event management (SIEM) systems receive data from IPS devices, firewalls, NetFlow devices, servers, endpoints, and syslog infrastructure devices.
Hint
Security information and event management (SIEM) systems receive data from IPS devices, firewalls, NetFlow devices, servers, endpoints, and syslog infrastructure devices.
-
Question 23 of 55
23. Question
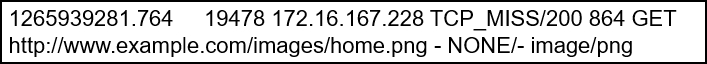
1 pointsRefer to the exhibit. Which techology generated the event log?
Correct
Incorrect
The output shown is from a web proxy.
Hint
The output shown is from a web proxy.
-
Question 24 of 55
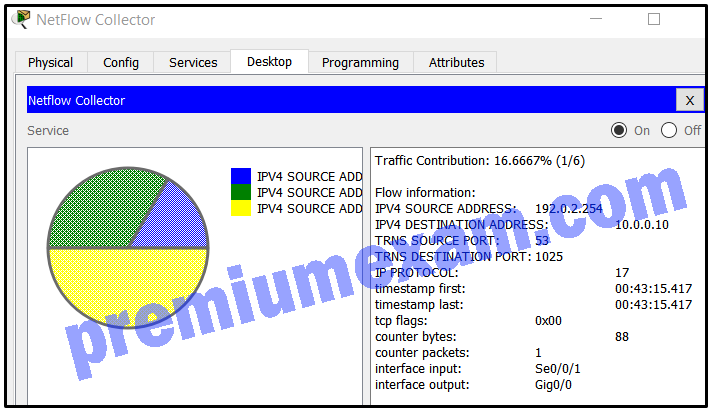
24. Question
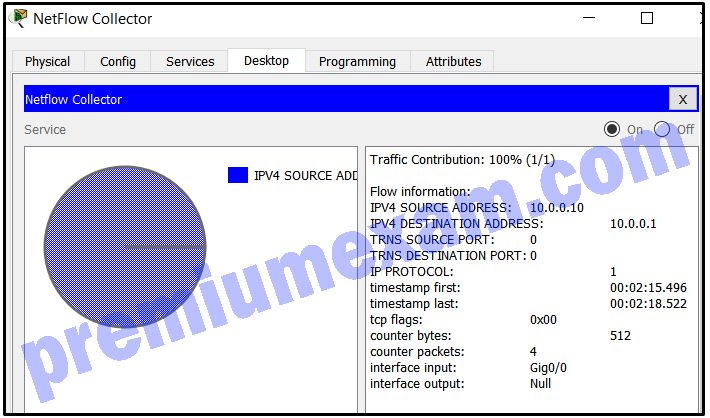
1 pointsRefer to the exhibit. A network administrator is examining a NetFlow record. Why would the record indicate that both TRNS SOURCE PORT and TRNS DESTINATION PORT are 0?
Correct
Incorrect
The data flow recorded is ICMP traffic, indicated by the number 1 for IP PROTOCOL. Because ICMP is a Layer 3 protocol and has no need for a Layer 4 protocol such as TCP or UDP, the port numbers show a 0 within the NetFlow output.
Hint
The data flow recorded is ICMP traffic, indicated by the number 1 for IP PROTOCOL. Because ICMP is a Layer 3 protocol and has no need for a Layer 4 protocol such as TCP or UDP, the port numbers show a 0 within the NetFlow output.
-
Question 25 of 55
25. Question
1 pointsRefer to the exhibit. A network administrator is examining a NetFlow record. Which protocol is in use in the flow shown?
Correct
Incorrect
The data flow shown is captured UDP traffic of a DNS response, indicated by the number 17 in the IP PROTOCOL output.
Hint
The data flow shown is captured UDP traffic of a DNS response, indicated by the number 17 in the IP PROTOCOL output.
-
Question 26 of 55
26. Question
1 pointsAt the request of investors, a company is proceeding with cyber attribution with a particular attack that was conducted from an external source. Which security term is used to describe the person or device responsible for the attack?
Correct
Incorrect
Some people may use the common word of “hacker” to describe a threat actor. A threat actor is an entity that is involved with an incident that impacts or has the potential to impact an organization in such a way that it is considered a security risk or threat.
Hint
Some people may use the common word of “hacker” to describe a threat actor. A threat actor is an entity that is involved with an incident that impacts or has the potential to impact an organization in such a way that it is considered a security risk or threat.
-
Question 27 of 55
27. Question
1 pointsWhat classification is used for an alert that correctly identifies that an exploit has occurred?
Correct
Incorrect
A true positive occurs when an IDS and IPS signature is correctly fired and an alarm is generated when offending traffic is detected.
Hint
A true positive occurs when an IDS and IPS signature is correctly fired and an alarm is generated when offending traffic is detected.
-
Question 28 of 55
28. Question
1 pointsWhich type of analysis relies on predefined conditions and can analyze applications that only use well-known fixed ports?
Correct
Incorrect
Deterministic analysis uses predefined conditions to analyze applications that conform to specification standards, such as performing a port-based analysis.
Hint
Deterministic analysis uses predefined conditions to analyze applications that conform to specification standards, such as performing a port-based analysis.
-
Question 29 of 55
29. Question
1 pointsWhich type of analysis relies on different methods to establish the likelihood that a security event has happened or will happen?
Correct
Incorrect
Probabilistic methods use powerful tools to create a probabilistic answer as a result of analyzing applications.
Hint
Probabilistic methods use powerful tools to create a probabilistic answer as a result of analyzing applications.
-
Question 30 of 55
30. Question
1 pointsWhat is the benefit of converting log file data into a common schema?
Correct
Incorrect
When data is converted into a universal format, it can be effectively structured for performing fast queries and event analysis.
Hint
When data is converted into a universal format, it can be effectively structured for performing fast queries and event analysis.
-
Question 31 of 55
31. Question
1 pointsWhat will match the regular expression ^83?
Correct
Incorrect
The expression ^83 indicates any string that begins with 83 will be matched.
Hint
The expression ^83 indicates any string that begins with 83 will be matched.
-
Question 32 of 55
32. Question
1 pointsUsing Tcpdump and Wireshark, a security analyst extracts a downloaded file from a pcap file. The analyst suspects that the file is a virus and wants to know the file type for further examination. Which Linux command can be used to determine the file type?
Correct
Incorrect
The Linux file command can be used to determine a file type, such as whether it is executable, ASCII text, or zip.
Hint
The Linux file command can be used to determine a file type, such as whether it is executable, ASCII text, or zip.
-
Question 33 of 55
33. Question
1 pointsWhich type of evidence cannot prove an IT security fact on its own?
Correct
Incorrect
Indirect evidence cannot prove a fact on its own, but direct evidence can. Corroborative evidence is supporting information. Best evidence is most reliable because it is something concrete such as a signed contract.
Hint
Indirect evidence cannot prove a fact on its own, but direct evidence can. Corroborative evidence is supporting information. Best evidence is most reliable because it is something concrete such as a signed contract.
-
Question 34 of 55
34. Question
1 pointsA cybersecurity analyst has been called to a crime scene that contains several technology items including a computer. Which technique will be used so that the information found on the computer can be used in court?
Correct
Incorrect
A normal file copy does not recover all data on a storage device so an unaltered disk image is commonly made. An unaltered disk image preserves the original evidence, thus preventing inadvertent alteration during the discovery phase. It also allows recreation of the original evidence.
Hint
A normal file copy does not recover all data on a storage device so an unaltered disk image is commonly made. An unaltered disk image preserves the original evidence, thus preventing inadvertent alteration during the discovery phase. It also allows recreation of the original evidence.
-
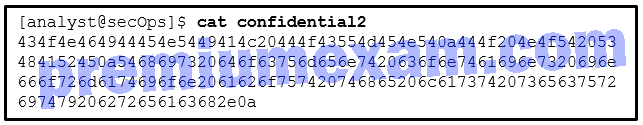
Question 35 of 55
35. Question
1 pointsRefer to the exhibit. A security analyst issues the cat command to review the content of the file confidential2. Which encoding method was used to encode the file?
Correct
Incorrect
Hex encodes binary data in hexidecimal string format. Base64 encodes binary data in an ASCII string format. In this case, the characters are 0-9 and a-f, typical hexidecimal numbers.
Hint
Hex encodes binary data in hexidecimal string format. Base64 encodes binary data in an ASCII string format. In this case, the characters are 0-9 and a-f, typical hexidecimal numbers.
-
Question 36 of 55
36. Question
1 pointsAccording to the Cyber Kill Chain model, after a weapon is delivered to a targeted system, what is the next step that a threat actor would take?
Correct
Incorrect
The Cyber Kill Chain specifies seven steps (or phases) and sequences that a threat actor must complete to accomplish an attack:
- Reconnaissance – The threat actor performs research, gathers intelligence, and selects targets.
- Weaponization – The threat actor uses the information from the reconnaissance phase to develop a weapon against specific targeted systems.
- Delivery – The weapon is transmitted to the target using a delivery vector.
- Exploitation – The threat actor uses the weapon delivered to break the vulnerability and gain control of the target.
- Installation – The threat actor establishes a back door into the system to allow for continued access to the target.
- Command and Control (CnC) – The threat actor establishes command and control (CnC) with the target system.
- Action on Objectives – The threat actor is able to take action on the target system, thus achieving the original objective.
Hint
The Cyber Kill Chain specifies seven steps (or phases) and sequences that a threat actor must complete to accomplish an attack:
- Reconnaissance – The threat actor performs research, gathers intelligence, and selects targets.
- Weaponization – The threat actor uses the information from the reconnaissance phase to develop a weapon against specific targeted systems.
- Delivery – The weapon is transmitted to the target using a delivery vector.
- Exploitation – The threat actor uses the weapon delivered to break the vulnerability and gain control of the target.
- Installation – The threat actor establishes a back door into the system to allow for continued access to the target.
- Command and Control (CnC) – The threat actor establishes command and control (CnC) with the target system.
- Action on Objectives – The threat actor is able to take action on the target system, thus achieving the original objective.
-
Question 37 of 55
37. Question
1 pointsWhat will a threat actor do to create a back door on a compromised target according to the Cyber Kill Chain model?
Correct
Incorrect
Once a target system is compromised, the threat actor will establish a back door into the system to allow for continued access to the target. Adding services and autorun keys is a way to create a point of persistent access.
Hint
Once a target system is compromised, the threat actor will establish a back door into the system to allow for continued access to the target. Adding services and autorun keys is a way to create a point of persistent access.
-
Question 38 of 55
38. Question
3 pointsWhich three things will a threat actor do to prepare a DDoS attack against a target system on the Internet? (Choose three.)
Correct
Incorrect
To prepare for launching a DDoS attack, a threat actor will compromise many hosts on the Internet, called zombies. The threat actor will then install attack software on zombies and establish a two-way communications channel to CnC infrastructure with zombies. The threat actor will issue the command to zombies through the CnC to launch a DDoS attack against a target system.
Hint
To prepare for launching a DDoS attack, a threat actor will compromise many hosts on the Internet, called zombies. The threat actor will then install attack software on zombies and establish a two-way communications channel to CnC infrastructure with zombies. The threat actor will issue the command to zombies through the CnC to launch a DDoS attack against a target system.
-
Question 39 of 55
39. Question
1 pointsIn which top-level element of the VERIS schema does VERIS use the A4 threat model to describe an incident?
Correct
Incorrect
In the top-level element incident description of the VERIS schema, VERIS uses the A4 threat model that was developed by the RISK team at Verizon to describe an incident completely.
Hint
In the top-level element incident description of the VERIS schema, VERIS uses the A4 threat model that was developed by the RISK team at Verizon to describe an incident completely.
-
Question 40 of 55
40. Question
3 pointsWhat are three of the four interactive landscapes that VERIS schema use to define risk?
Correct
Incorrect
In the VERIS schema, risk is defined as the intersection of four landscapes of threat, asset, impact, and control. Information from each landscape helps to understand the level of risk to the organization.
Hint
In the VERIS schema, risk is defined as the intersection of four landscapes of threat, asset, impact, and control. Information from each landscape helps to understand the level of risk to the organization.
-
Question 41 of 55
41. Question
1 pointsWhich specification provides a common language for describing security incidents in a structured and repeatable way?
Correct
Incorrect
Vocabulary for Event Recording and Incident Sharing (VERIS) was created to provide a common language for describing security incidents. VERIS addresses the problems of dealing with different security tools and the tendency of humans to refer to incidents and events inconsistently.
Hint
Vocabulary for Event Recording and Incident Sharing (VERIS) was created to provide a common language for describing security incidents. VERIS addresses the problems of dealing with different security tools and the tendency of humans to refer to incidents and events inconsistently.
-
Question 42 of 55
42. Question
1 pointsWhat is the VERIS Community Database (VCDB)?
Correct
Incorrect
The VERIS Community Database (VCDB) is an open and free collection of publicly-reported security incidents in VERIS format. The VCDB is in a universal format that allows for manipulation and transformation.
Hint
The VERIS Community Database (VCDB) is an open and free collection of publicly-reported security incidents in VERIS format. The VCDB is in a universal format that allows for manipulation and transformation.
-
Question 43 of 55
43. Question
1 pointsWhich type of computer security incident response team is responsible for determining trends to help predict and provide warning of future security incidents?
Correct
Incorrect
There are many different types of computer security incident response teams (CSIRTs) and related information security organizations. Analysis centers use data from many sources to determine security incident trends that can help predict future incidents and provide early warning.
Hint
There are many different types of computer security incident response teams (CSIRTs) and related information security organizations. Analysis centers use data from many sources to determine security incident trends that can help predict future incidents and provide early warning.
-
Question 44 of 55
44. Question
1 pointsWhat is the role of vendor teams as they relate to a computer security incident response team?
Correct
Incorrect
There are many different types of computer security incident response teams (CSIRTs) and related information security organizations. Vendor CSIRT teams provide remediation for vulnerabilities in the software or hardware of an organization and often handle customer reports concerning security vulnerabilities.
Hint
There are many different types of computer security incident response teams (CSIRTs) and related information security organizations. Vendor CSIRT teams provide remediation for vulnerabilities in the software or hardware of an organization and often handle customer reports concerning security vulnerabilities.
-
Question 45 of 55
45. Question
2 pointsWhich two actions should be taken during the preparation phase of the incident response life cycle defined by NIST? (Choose two.)
Correct
Incorrect
According to the guideline defined in the NIST Incident Response Life Cycle, several actions should be taken during the preparation phase including (1) creating and training the CSIRT and (2) acquiring and deploying the tools needed by the team to investigate incidents.
Hint
According to the guideline defined in the NIST Incident Response Life Cycle, several actions should be taken during the preparation phase including (1) creating and training the CSIRT and (2) acquiring and deploying the tools needed by the team to investigate incidents.
-
Question 46 of 55
46. Question
1 pointsDuring the detection and analysis phase of the NIST incident response process life cycle, which sign category is used to describe that an incident might occur in the future?
Correct
Incorrect
There are two categories for the signs of an incident:
- Precursor – a sign that an incident might occur in the future
- Indicator – a sign that an incident might already have occurred or is currently occurring
Hint
There are two categories for the signs of an incident:
- Precursor – a sign that an incident might occur in the future
- Indicator – a sign that an incident might already have occurred or is currently occurring
-
Question 47 of 55
47. Question
2 pointsA company is applying the NIST.SP800-61 r2 incident handling process to security events. What are two examples of incidents that are in the category of precursor? (Choose two.)
Correct
Incorrect
As an incident category, the precursor is a sign that an incident might occur in the future. Examples of precursors are log entries that show a response to a port scan or a newly-discovered vulnerability in web servers using Apache.
Hint
As an incident category, the precursor is a sign that an incident might occur in the future. Examples of precursors are log entries that show a response to a port scan or a newly-discovered vulnerability in web servers using Apache.
-
Question 48 of 55
48. Question
2 pointsWhich two actions can help identify an attacking host during a security incident? (Choose two.)
Correct
Incorrect
The following actions can help identify an attacking host during a security incident:Use incident databases to research related activity.
Validate the IP address of the threat actor to determine if it is a viable one.
Use an Internet search engine to gain additional information about the attack.
Monitor the communication channels that some threat actors use, such as IRC.Hint
The following actions can help identify an attacking host during a security incident:Use incident databases to research related activity.
Validate the IP address of the threat actor to determine if it is a viable one.
Use an Internet search engine to gain additional information about the attack.
Monitor the communication channels that some threat actors use, such as IRC. -
Question 49 of 55
49. Question
1 pointsWhat is defined in the policy element of the NIST incident response plan?
Correct
Incorrect
The policy element of the NIST incident response plan details how incidents should be handled based on the mission and function of the organization.
Hint
The policy element of the NIST incident response plan details how incidents should be handled based on the mission and function of the organization.
-
Question 50 of 55
50. Question
1 pointsWhat is specified in the plan element of the NIST incident response plan?
Correct
Incorrect
NIST recommends creating policies, plans, and procedures for establishing and maintaining a CSIRC. One component of the plan element is to develop metrics for measuring the incident response capability and its effectiveness.
Hint
NIST recommends creating policies, plans, and procedures for establishing and maintaining a CSIRC. One component of the plan element is to develop metrics for measuring the incident response capability and its effectiveness.
-
Question 51 of 55
51. Question
1 pointsWhich NIST-defined incident response stakeholder is responsible for coordinating incident response with other stakeholders and minimizing the damage of an incident?
Correct
Incorrect
The management team creates the policies, designs the budget, and is in charge of staffing all departments. Management is also responsible for coordinating the incident response with other stakeholders and minimizing the damage of an incident.
Hint
The management team creates the policies, designs the budget, and is in charge of staffing all departments. Management is also responsible for coordinating the incident response with other stakeholders and minimizing the damage of an incident.
-
Question 52 of 55
52. Question
1 pointsWhat is the responsibility of the IT support group when handing an incident as defined by NIST?
Correct
Incorrect
IT support best understands the technology used in the organization and can perform the correct actions to minimize the effectiveness of the attack and preserve evidence.
Hint
IT support best understands the technology used in the organization and can perform the correct actions to minimize the effectiveness of the attack and preserve evidence.
-
Question 53 of 55
53. Question
1 pointsWhat is the responsibility of the human resources department when handing a security incident as defined by NIST?
Correct
Incorrect
The human resources department may be called upon to perform disciplinary measures if an incident is caused by an employee.
Hint
The human resources department may be called upon to perform disciplinary measures if an incident is caused by an employee.
-
Question 54 of 55
54. Question
3 pointsAfter containing an incident that infected user workstations with malware, what are three effective remediation procedures that an organization can take for eradication? (Choose three.)
Correct
Incorrect
To recover infected user workstations, use clean and recent backups or rebuild the PCs with installation media if no backups are available or they have been compromised. Also, fully update and patch the operating system and installed software of all hosts. All users are encouraged to change their passwords for the workstation or workstations they use. Rebuilding DHCP servers is needed only if they are affected by the incident.Also not all devices need to change the name and password configuration setting unless they are affected by the incident.
Hint
To recover infected user workstations, use clean and recent backups or rebuild the PCs with installation media if no backups are available or they have been compromised. Also, fully update and patch the operating system and installed software of all hosts. All users are encouraged to change their passwords for the workstation or workstations they use. Rebuilding DHCP servers is needed only if they are affected by the incident.Also not all devices need to change the name and password configuration setting unless they are affected by the incident.
-
Question 55 of 55
55. Question
1 pointsIn which step of the NIST incident response process does the CSIRT perform an analysis to determine which networks, systems, or applications are affected; who or what originated the incident; and how the incident is occurring?
Correct
Incorrect
In the detection and analysis phase of the NIST incident response process life cycle, the CSIRT should immediately perform an initial analysis to determine the scope of the incident, such as which networks, systems, or applications are affected; who or what originated the incident; and how the incident is occurring.
Hint
In the detection and analysis phase of the NIST incident response process life cycle, the CSIRT should immediately perform an initial analysis to determine the scope of the incident, such as which networks, systems, or applications are affected; who or what originated the incident; and how the incident is occurring.