Last Updated on October 29, 2019 by Admin
CCNA CyberOps Chapter 7 Exam Online
CCNA CyberOps 1.1 -- Chapter 7 Exam
Quiz-summary
0 of 25 questions completed
Questions:
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
Information
CCNA CyberOps 1.1 — Chapter 7 Exam
You have already completed the quiz before. Hence you can not start it again.
Quiz is loading...
You must sign in or sign up to start the quiz.
You have to finish following quiz, to start this quiz:
Results
0 of 25 questions answered correctly
Your time:
Time has elapsed
You have reached 0 of 0 points, (0)
| Average score |
|
| Your score |
|
Categories
- Not categorized 0%
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- Answered
- Review
-
Question 1 of 25
1. Question
2 pointsWhat are two monitoring tools that capture network traffic and forward it to network monitoring devices? (Choose two.)
Correct
Incorrect
A network tap is used to capture traffic for monitoring the network. The tap is typically a passive splitting device implemented inline on the network and forwards all traffic including physical layer errors to an analysis device. SPAN is a port mirroring technology supported on Cisco switches that enables the switch to copy frames and forward them to an analysis device.
Hint
A network tap is used to capture traffic for monitoring the network. The tap is typically a passive splitting device implemented inline on the network and forwards all traffic including physical layer errors to an analysis device. SPAN is a port mirroring technology supported on Cisco switches that enables the switch to copy frames and forward them to an analysis device.
-
Question 2 of 25
2. Question
1 pointsWhat network monitoring technology enables a switch to copy and forward traffic sent and received on multiple interfaces out another interface toward a network analysis device?
Correct
Incorrect
When enabled on a switch, port mirroring copies frames sent and recieved by the switch and forwards them to another port, which has a analysis device attached.
Hint
-
When enabled on a switch, port mirroring copies frames sent and recieved by the switch and forwards them to another port, which has a analysis device attached.
-
Question 3 of 25
3. Question
1 pointsWhich network monitoring capability is provided by using SPAN?
Correct
Incorrect
When enabled on a switch, SPAN or port mirroring, copies frames that are sent and received by the switch and forwards them to another port, known as a Switch Port Analyzer port, which has a analysis device attached.
Hint
When enabled on a switch, SPAN or port mirroring, copies frames that are sent and received by the switch and forwards them to another port, known as a Switch Port Analyzer port, which has a analysis device attached.
-
Question 4 of 25
4. Question
1 pointsWhich technology is an open source SIEM system?
Correct
Incorrect
There are many SIEM systems available to network administrators. The ELK suite is an open source option.
Hint
There are many SIEM systems available to network administrators. The ELK suite is an open source option.
-
Question 5 of 25
5. Question
1 pointsWhich network monitoring tool can provide a complete audit trail of basic information of all IP flows on a Cisco router and forward the data to a device?
Correct
Incorrect
NetFlow is a Cisco technology that provides statistics on packets flowing through a Cisco router or multilayer switch.
Hint
NetFlow is a Cisco technology that provides statistics on packets flowing through a Cisco router or multilayer switch.
-
Question 6 of 25
6. Question
1 pointsWhich SIEM function is associated with speeding up detection of security threats by examining logs and events from different systems?
Correct
Incorrect
The correlation function of SIEM speeds the detection and reaction to security threats by examining logs and events from different systems.
Hint
The correlation function of SIEM speeds the detection and reaction to security threats by examining logs and events from different systems.
-
Question 7 of 25
7. Question
1 pointsWhich capability is provided by the aggregation function in SIEM?
Correct
Incorrect
The aggregation function of SIEM reduces the volume of event data by consolidating duplicate event records.
Hint
The aggregation function of SIEM reduces the volume of event data by consolidating duplicate event records.
-
Question 8 of 25
8. Question
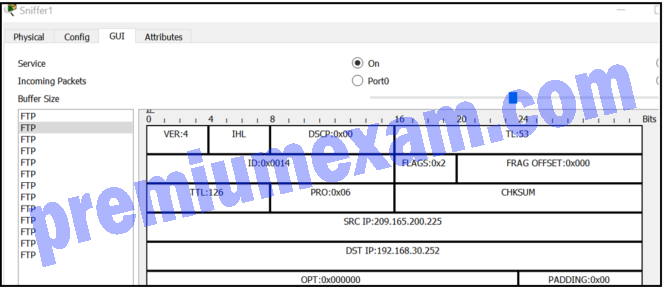
1 pointsRefer to the exhibit. A junior network administrator is inspecting the traffic flow of a particular server in order to make security recommendations to the departmental supervisor. Which recommendation should be made?
Correct
Incorrect
FTP is an unsecure network protocol. Anyone capturing packets can obtain the username and password from the capture. A more secure protocol such as SFTP should be used.
Hint
FTP is an unsecure network protocol. Anyone capturing packets can obtain the username and password from the capture. A more secure protocol such as SFTP should be used.
-
Question 9 of 25
9. Question
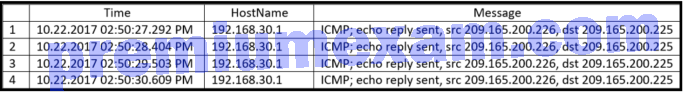
1 pointsRefer to the exhibit. What protocol would be used by the syslog server service to create this type of output for security purposes?
Correct
Incorrect
The Simple Network Management Protocol is used by network devices to send and log messages to a syslog server in order to monitor traffic and network device events.
Hint
The Simple Network Management Protocol is used by network devices to send and log messages to a syslog server in order to monitor traffic and network device events.
-
Question 10 of 25
10. Question
1 pointsWhich network monitoring tool saves captured packets in a PCAP file?
Correct
Incorrect
Wireshark captures are saved as PCAP files, which contain frame, interface, and packet information, and also time stamps.
Hint
Wireshark captures are saved as PCAP files, which contain frame, interface, and packet information, and also time stamps.
-
Question 11 of 25
11. Question
1 pointsHow is optional network layer information carried by IPv6 packets?
Correct
Incorrect
IPv6 uses extension headers to carry optional network layer information. Extension headers are not part of the main IPv6 header but are separate headers placed between the IPv6 header and the payload.
Hint
IPv6 uses extension headers to carry optional network layer information. Extension headers are not part of the main IPv6 header but are separate headers placed between the IPv6 header and the payload.
-
Question 12 of 25
12. Question
1 pointsWhich cyber attack involves a coordinated attack from a botnet of zombie computers?
Correct
Incorrect
DDoS is a distributed denial-of-services attack. A DDoS attack is launched from multiple coordinated sources. The sources of the attack are zombie hosts that the cybercriminal has built into a botnet. When ready, the cybercriminal instructs the botnet of zombies to attack the chosen target.
Hint
DDoS is a distributed denial-of-services attack. A DDoS attack is launched from multiple coordinated sources. The sources of the attack are zombie hosts that the cybercriminal has built into a botnet. When ready, the cybercriminal instructs the botnet of zombies to attack the chosen target.
-
Question 13 of 25
13. Question
1 pointsIn which TCP attack is the cybercriminal attempting to overwhelm a target host with half-open TCP connections?
Correct
Incorrect
In a TCP SYN flood attack, the attacker sends to the target host a continuous flood of TCP SYN session requests with a spoofed source IP address. The target host responds with a TCP-SYN-ACK to each of the SYN session requests and waits for a TCP ACK that will never arrive. Eventually the target is overwhelmed with half-open TCP connections.
Hint
In a TCP SYN flood attack, the attacker sends to the target host a continuous flood of TCP SYN session requests with a spoofed source IP address. The target host responds with a TCP-SYN-ACK to each of the SYN session requests and waits for a TCP ACK that will never arrive. Eventually the target is overwhelmed with half-open TCP connections.
-
Question 14 of 25
14. Question
2 pointsWhat are two methods used by cybercriminals to mask DNS attacks? (Choose two.)
Correct
Incorrect
Fast flux, double IP flux, and domain generation algorithms are used by cybercrimals to attack DNS servers and affect DNS services. Fast flux is a technique used to hide phishing and malware delivery sites behind a quickly-changing network of compromised DNS hosts (bots within botnets). The double IP flux technique rapidly changes the hostname to IP address mappings and the authoritative name server. Domain generation algorithms randomly generate domain names to be used as rendezvous points.
Hint
Fast flux, double IP flux, and domain generation algorithms are used by cybercrimals to attack DNS servers and affect DNS services. Fast flux is a technique used to hide phishing and malware delivery sites behind a quickly-changing network of compromised DNS hosts (bots within botnets). The double IP flux technique rapidly changes the hostname to IP address mappings and the authoritative name server. Domain generation algorithms randomly generate domain names to be used as rendezvous points.
-
Question 15 of 25
15. Question
1 pointsWhat network attack seeks to create a DoS for clients by preventing them from being able to obtain a DHCP lease?
Correct
Incorrect
DCHP starvation attacks are launched by an attacker with the intent to create a DoS for DHCP clients. To accomplish this goal, the attacker uses a tool that sends many DHCPDISCOVER messages in order to lease the entire pool of available IP addresses, thus denying them to legitimate hosts.
Hint
DCHP starvation attacks are launched by an attacker with the intent to create a DoS for DHCP clients. To accomplish this goal, the attacker uses a tool that sends many DHCPDISCOVER messages in order to lease the entire pool of available IP addresses, thus denying them to legitimate hosts.
-
Question 16 of 25
16. Question
1 pointsWhich type of DNS attack involves the cybercriminal compromising a parent domain and creating multiple subdomains to be used during the attacks?
Correct
Incorrect
Two threats to DNS are DNS shadowing and DNS tunneling attacks. DNS shadowing attacks compromise a parent domain and then the cybercriminal creates subdomains to be used in attacks. DNS tunneling attacks build botnets to bypass traditional security solutions. Three threats to DNS open resolvers are cache poisoning, amplification and reflection, and resource utilization attacks.
Hint
Two threats to DNS are DNS shadowing and DNS tunneling attacks. DNS shadowing attacks compromise a parent domain and then the cybercriminal creates subdomains to be used in attacks. DNS tunneling attacks build botnets to bypass traditional security solutions. Three threats to DNS open resolvers are cache poisoning, amplification and reflection, and resource utilization attacks.
-
Question 17 of 25
17. Question
1 pointsWhich protocol is attacked when a cybercriminal provides an invalid gateway in order to create a man-in-the-middle attack?
Correct
Incorrect
A cybercriminal could set up a rogue DHCP server that provides one or more of the following:Wrong default gateway that is used to create a man-in-the-middle attack and allow the attacker to intercept data
Wrong DNS server that results in the user being sent to a malicious website
Invalid default gateway IP address that results in a denial of service attack on the DHCP clientHint
A cybercriminal could set up a rogue DHCP server that provides one or more of the following:Wrong default gateway that is used to create a man-in-the-middle attack and allow the attacker to intercept data
Wrong DNS server that results in the user being sent to a malicious website
Invalid default gateway IP address that results in a denial of service attack on the DHCP client -
Question 18 of 25
18. Question
1 pointsWhat is the result of a passive ARP poisoning attack?
Correct
Incorrect
ARP poisoning attacks can be passive or active. The result of a passive attack is that cybercriminals steal confidential information. With an active attack, cybercriminals modify data in transit or they inject malicious data.
Hint
ARP poisoning attacks can be passive or active. The result of a passive attack is that cybercriminals steal confidential information. With an active attack, cybercriminals modify data in transit or they inject malicious data.
-
Question 19 of 25
19. Question
1 pointsIn which type of attack is falsified information used to redirect users to malicious Internet sites?
Correct
Incorrect
In a DNS cache poisoning attack, falsified information is used to redirect users from legitimate to malicious internet sites.
Hint
In a DNS cache poisoning attack, falsified information is used to redirect users from legitimate to malicious internet sites.
-
Question 20 of 25
20. Question
1 pointsWhat type of attack targets an SQL database using the input field of a user?
Correct
Incorrect
A criminal can insert a malicious SQL statement in an entry field on a website where the system does not filter the user input correctly.
Hint
A criminal can insert a malicious SQL statement in an entry field on a website where the system does not filter the user input correctly.
-
Question 21 of 25
21. Question
1 pointsWhich term is used for bulk advertising emails flooded to as many end users as possible?
Correct
Incorrect
Spam is annoying and unwanted bulk email that is sent to as many end users as possible.
Hint
Spam is annoying and unwanted bulk email that is sent to as many end users as possible.
-
Question 22 of 25
22. Question
1 pointsWhich protocol is exploited by cybercriminals who create malicious iFrames?
Correct
Incorrect
An HTML element known as an inline frame or iFrame allows the browser to load a different web page from another source.
Hint
An HTML element known as an inline frame or iFrame allows the browser to load a different web page from another source.
-
Question 23 of 25
23. Question
1 pointsWhich protocol would be the target of a cushioning attack?
Correct
Incorrect
The HTTP 302 cushioning attack is used by cybercriminals to take advantage of the 302 Found HTTP response status code to redirect the browser of the user to a new location, usually a malicious site.
Hint
The HTTP 302 cushioning attack is used by cybercriminals to take advantage of the 302 Found HTTP response status code to redirect the browser of the user to a new location, usually a malicious site.
-
Question 24 of 25
24. Question
4 pointsMatch the monitoring tool to the description.
Sort elements
- Splunk
- Wireshark
- Gobbler
- StealthWatch
-
SIEM system
-
protocol analyzer
-
DHCP attack tool
-
NetFlow collector
Correct
Incorrect
-
Question 25 of 25
25. Question
3 pointsMatch the attack to the definition. (Not all options are used.)
Sort elements
- resource utilization attack
- ARP cache poisoning
- amplification and reflection
- domain generation
-
attacker sends multiple packets that consume server resources
-
attacker sends falsified information to redirect users to malicious sites
-
attacker uses open resolvers to increase the volume of attacks and mask the true source of the attack
Correct
Incorrect