Last Updated on October 29, 2019 by Admin
CCNA CyberOps Chapter 4 Exam Online
CCNA CyberOps 1.1 -- Chapter 4 Exam
Quiz-summary
0 of 28 questions completed
Questions:
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
Information
CCNA CyberOps 1.1 — Chapter 4 Exam
You have already completed the quiz before. Hence you can not start it again.
Quiz is loading...
You must sign in or sign up to start the quiz.
You have to finish following quiz, to start this quiz:
Results
0 of 28 questions answered correctly
Your time:
Time has elapsed
You have reached 0 of 0 points, (0)
| Average score |
|
| Your score |
|
Categories
- Not categorized 0%
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- Answered
- Review
-
Question 1 of 28
1. Question
1 pointsWhich PDU format is used when bits are received from the network medium by the NIC of a host?
Correct
Incorrect
When received at the physical layer of a host, the bits are formatted into a frame at the data link layer. A packet is the PDU at the network layer. A segment is the PDU at the transport layer. A file is a data structure that may be used at the application layer.
Hint
When received at the physical layer of a host, the bits are formatted into a frame at the data link layer. A packet is the PDU at the network layer. A segment is the PDU at the transport layer. A file is a data structure that may be used at the application layer.
-
Question 2 of 28
2. Question
1 pointsWhich term is used to describe the process of placing one message format inside another message format?
Correct
Incorrect
The encapsulation process is performed at each OSI layer and is the process of placing one message format inside another message format.
Hint
The encapsulation process is performed at each OSI layer and is the process of placing one message format inside another message format.
-
Question 3 of 28
3. Question
1 pointsWhat is the prefix length notation for the subnet mask 255.255.255.224?
Correct
Incorrect
The binary format for 255.255.255.224 is 11111111.11111111.11111111.11100000. The prefix length is the number of consecutive 1s in the subnet mask. Therefore, the prefix length is /27.
Hint
The binary format for 255.255.255.224 is 11111111.11111111.11111111.11100000. The prefix length is the number of consecutive 1s in the subnet mask. Therefore, the prefix length is /27.
-
Question 4 of 28
4. Question
1 pointsWhy does a Layer 3 device perform the ANDing process on a destination IP address and subnet mask?
Correct
Incorrect
ANDing allows us to identify the network address from the IP address and the network mask.
Hint
ANDing allows us to identify the network address from the IP address and the network mask.
-
Question 5 of 28
5. Question
1 pointsA high school in New York (school A) is using videoconferencing technology to establish student interactions with another high school (school B) in Russia. The videoconferencing is conducted between two end devices through the Internet. The network administrator of school A configures the end device with the IP address 209.165.201.10. The administrator sends a request for the IP address for the end device in school B and the response is 192.168.25.10. Neither school is using a VPN. The administrator knows immediately that this IP will not work. Why?
Correct
Incorrect
The IP address 192.168.25.10 is an IPv4 private address. This address will not be routed over the Internet, so school A will not be able to reach school B. Because the address is a private one, it can be used freely on an internal network. As long as no two devices on the internal network are assigned the same private IP, there is no IP conflict issue. Devices that are assigned a private IP will need to use NAT in order to communicate over the Internet.
Hint
The IP address 192.168.25.10 is an IPv4 private address. This address will not be routed over the Internet, so school A will not be able to reach school B. Because the address is a private one, it can be used freely on an internal network. As long as no two devices on the internal network are assigned the same private IP, there is no IP conflict issue. Devices that are assigned a private IP will need to use NAT in order to communicate over the Internet.
-
Question 6 of 28
6. Question
3 pointsWhich three IP addresses are private ? (Choose three.)
Correct
Incorrect
The private IP addresses are within these three ranges:
10.0.0.0 – 10.255.255.255
172.16.0.0 – 172.31.255.255
192.168.0.0 – 192.168.255.255Hint
The private IP addresses are within these three ranges:
10.0.0.0 – 10.255.255.255
172.16.0.0 – 172.31.255.255
192.168.0.0 – 192.168.255.255 -
Question 7 of 28
7. Question
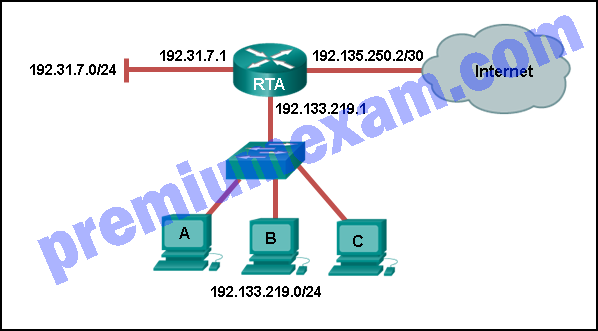
1 pointsRefer to the exhibit. Using the network in the exhibit, what would be the default gateway address for host A in the 192.133.219.0 network?
Correct
Incorrect
-
Question 8 of 28
8. Question
1 pointsWhat is the purpose of the routing process?
Correct
Incorrect
-
Question 9 of 28
9. Question
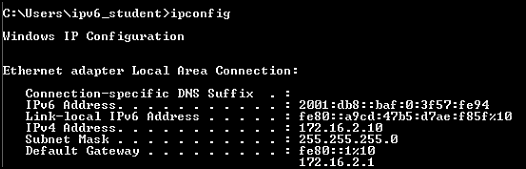
1 pointsRefer to the exhibit. What is the global IPv6 address of the host in uncompressed format?
Correct
Incorrect
In the compressed format, the :: represents two contiguous hextets of all zeros. Leading zeros in the second, fifth, and sixth hextets have also been removed.
Hint
In the compressed format, the :: represents two contiguous hextets of all zeros. Leading zeros in the second, fifth, and sixth hextets have also been removed.
-
Question 10 of 28
10. Question
1 pointsWhat is the purpose of ICMP messages?
Correct
Incorrect
The purpose of ICMP messages is to provide feedback about issues that are related to the processing of IP packets.
Hint
The purpose of ICMP messages is to provide feedback about issues that are related to the processing of IP packets.
-
Question 11 of 28
11. Question
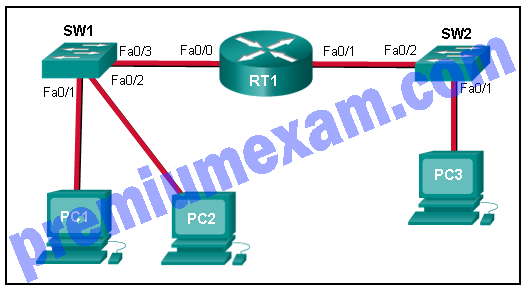
1 pointsRefer to the exhibit. A cybersecurity analyst is viewing captured ICMP echo request packets sent from host A to host B on switch S2. What is the source MAC address of Ethernet frames carrying the ICMP echo request packets?
Correct
Incorrect
When router R1 receives the ICMP echo requests from host A it will forward the packets out interface G0/1 towards host B. However, before forwarding the packets, R1 will encapsulate them in a new Ethernet frame using the MAC address of interface G0/1 as the source and the MAC address of host B as the destination.
Hint
When router R1 receives the ICMP echo requests from host A it will forward the packets out interface G0/1 towards host B. However, before forwarding the packets, R1 will encapsulate them in a new Ethernet frame using the MAC address of interface G0/1 as the source and the MAC address of host B as the destination.
-
Question 12 of 28
12. Question
1 pointsRefer to the exhibit. PC1 issues an ARP request because it needs to send a packet to PC2. In this scenario, what will happen next?
Correct
Incorrect
When a network device wants to communicate with another device on the same network, it sends a broadcast ARP request. In this case, the request will contain the IP address of PC2. The destination device (PC2) sends an ARP reply with its MAC address.
Hint
When a network device wants to communicate with another device on the same network, it sends a broadcast ARP request. In this case, the request will contain the IP address of PC2. The destination device (PC2) sends an ARP reply with its MAC address.
-
Question 13 of 28
13. Question
2 pointsWhat are two features of ARP? (Choose two.)
Correct
Incorrect
When a node encapsulates a data packet into a frame, it needs the destination MAC address. First it determines if the destination device is on the local network or on a remote network. Then it checks the ARP table (not the MAC table) to see if a pair of IP address and MAC address exists for either the destination IP address (if the destination host is on the local network) or the default gateway IP address (if the destination host is on a remote network). If the match does not exist, it generates an ARP broadcast to seek the IP address to MAC address resolution. Because the destination MAC address is unknown, the ARP request is broadcast with the MAC address FFFF.FFFF.FFFF. Either the destination device or the default gateway will respond with its MAC address, which enables the sending node to assemble the frame. If no device responds to the ARP request, then the originating node will discard the packet because a frame cannot be created.
Hint
When a node encapsulates a data packet into a frame, it needs the destination MAC address. First it determines if the destination device is on the local network or on a remote network. Then it checks the ARP table (not the MAC table) to see if a pair of IP address and MAC address exists for either the destination IP address (if the destination host is on the local network) or the default gateway IP address (if the destination host is on a remote network). If the match does not exist, it generates an ARP broadcast to seek the IP address to MAC address resolution. Because the destination MAC address is unknown, the ARP request is broadcast with the MAC address FFFF.FFFF.FFFF. Either the destination device or the default gateway will respond with its MAC address, which enables the sending node to assemble the frame. If no device responds to the ARP request, then the originating node will discard the packet because a frame cannot be created.
-
Question 14 of 28
14. Question
2 pointsWhat are two potential network problems that can result from ARP operation? (Choose two.)
Correct
Incorrect
Large numbers of ARP broadcast messages could cause momentary data communications delays. Network attackers could manipulate MAC address and IP address mappings in ARP messages with the intent to intercept network traffic. ARP requests and replies cause entries to be made into the ARP table, not the MAC address table. ARP table overflows are very unlikely. Manually configuring static ARP associations is a way to prevent, not facilitate, ARP poisoning and MAC address spoofing. Multiple ARP replies resulting in the switch MAC address table containing entries that match the MAC addresses of connected nodes and are associated with the relevant switch port are required for normal switch frame forwarding operations. It is not an ARP caused network problem.
Hint
Large numbers of ARP broadcast messages could cause momentary data communications delays. Network attackers could manipulate MAC address and IP address mappings in ARP messages with the intent to intercept network traffic. ARP requests and replies cause entries to be made into the ARP table, not the MAC address table. ARP table overflows are very unlikely. Manually configuring static ARP associations is a way to prevent, not facilitate, ARP poisoning and MAC address spoofing. Multiple ARP replies resulting in the switch MAC address table containing entries that match the MAC addresses of connected nodes and are associated with the relevant switch port are required for normal switch frame forwarding operations. It is not an ARP caused network problem.
-
Question 15 of 28
15. Question
1 pointsWhat happens if part of an FTP message is not delivered to the destination?
Correct
Incorrect
Because FTP uses TCP as its transport layer protocol, sequence and acknowledgment numbers will identify the missing segments, which will be re-sent to complete the message.
Hint
Because FTP uses TCP as its transport layer protocol, sequence and acknowledgment numbers will identify the missing segments, which will be re-sent to complete the message.
-
Question 16 of 28
16. Question
1 pointsWhat is a socket?
Correct
Incorrect
A socket is a combination of the source IP address and source port or the destination IP address and the destination port number.
Hint
A socket is a combination of the source IP address and source port or the destination IP address and the destination port number.
-
Question 17 of 28
17. Question
2 pointsWhich two characteristics are associated with UDP sessions? (Choose two.)
Correct
Incorrect
TCP:
· Provides tracking of transmitted data segments
· Destination devices will acknowledge received data.
· Source devices will retransmit unacknowledged data.UDP
· Destination devices will not acknowledge received data
· Headers use very little overhead and cause minimal delay.Hint
TCP:
· Provides tracking of transmitted data segments
· Destination devices will acknowledge received data.
· Source devices will retransmit unacknowledged data.UDP
· Destination devices will not acknowledge received data
· Headers use very little overhead and cause minimal delay. -
Question 18 of 28
18. Question
1 pointsWhich TCP mechanism is used to identify missing segments?
Correct
Incorrect
TCP segments are acknowledged by the receiver as they arrive. The receiver keeps track of the sequence number of received segments and uses the sequence number to reorder the segments and to identify any missing segments that need to be retransmitted.
Hint
TCP segments are acknowledged by the receiver as they arrive. The receiver keeps track of the sequence number of received segments and uses the sequence number to reorder the segments and to identify any missing segments that need to be retransmitted.
-
Question 19 of 28
19. Question
1 pointsWhich transport layer feature is used to guarantee session establishment?
Correct
Incorrect
TCP uses the 3-way handshake. UDP does not use this feature. The 3-way handshake ensures there is connectivity between the source and destination devices before transmission occurs.
Hint
TCP uses the 3-way handshake. UDP does not use this feature. The 3-way handshake ensures there is connectivity between the source and destination devices before transmission occurs.
-
Question 20 of 28
20. Question
1 pointsHow is a DHCPDISCOVER transmitted on a network to reach a DHCP server?
Correct
Incorrect
The DHCPDISCOVER message is sent by a DHCPv4 client and targets a broadcast IP along with the destination port 67. The DHCPv4 server or servers respond to the DHCPv4 clients by targeting port 68.
Hint
The DHCPDISCOVER message is sent by a DHCPv4 client and targets a broadcast IP along with the destination port 67. The DHCPv4 server or servers respond to the DHCPv4 clients by targeting port 68.
-
Question 21 of 28
21. Question
1 pointsWhat part of the URL, http://www.cisco.com/index.html, represents the top-level DNS domain?
Correct
Incorrect
The components of the URL http://www.cisco.com/index.htm are as follows:
http = protocol
www = part of the server name
cisco = part of the domain name
index = file name
com = the top-level domainHint
The components of the URL http://www.cisco.com/index.htm are as follows:
http = protocol
www = part of the server name
cisco = part of the domain name
index = file name
com = the top-level domain -
Question 22 of 28
22. Question
1 pointsWhat is the primary purpose of NAT?
Correct
Incorrect
NAT was developed to conserve IPv4 addresses. A side benefit is that NAT adds a small level of security by hiding the internal network addressing scheme. However, there are some drawbacks of using NAT. It does not allow true peer-to-peer communication and it adds latency to outbound connections.
Hint
NAT was developed to conserve IPv4 addresses. A side benefit is that NAT adds a small level of security by hiding the internal network addressing scheme. However, there are some drawbacks of using NAT. It does not allow true peer-to-peer communication and it adds latency to outbound connections.
-
Question 23 of 28
23. Question
1 pointsIn NAT translation for internal hosts, what address would be used by external users to reach internal hosts?
Correct
Incorrect
From the perspective of a NAT device, inside global addresses are used by external users to reach internal hosts. Inside local addresses are the addresses assigned to internal hosts. Outside global addresses are the addresses of destinations on the external network. Outside local addresses are the actual private addresses of destination hosts behind other NAT devices.
Hint
From the perspective of a NAT device, inside global addresses are used by external users to reach internal hosts. Inside local addresses are the addresses assigned to internal hosts. Outside global addresses are the addresses of destinations on the external network. Outside local addresses are the actual private addresses of destination hosts behind other NAT devices.
-
Question 24 of 28
24. Question
1 pointsRefer to the exhibit. A cybersecurity analyst is viewing captured packets forwarded on switch S1. Which device has the MAC address 50:6a:03:96:71:22?
Correct
Incorrect
The Wireshark capture is of a DNS query from PC-A to the DNS server. Because the DNS server is on a remote network, the PC will send the query to the default gateway router, router DG, using the MAC address of the router G0/0 interface on the router.
Hint
The Wireshark capture is of a DNS query from PC-A to the DNS server. Because the DNS server is on a remote network, the PC will send the query to the default gateway router, router DG, using the MAC address of the router G0/0 interface on the router.
-
Question 25 of 28
25. Question
1 pointsWhich application layer protocol uses message types such as GET, PUT, and POST?
Correct
Incorrect
The GET command is a client request for data from a web server. A PUT command uploads resources and content, such as images, to a web server. A POST command uploads data files to a web server.
Hint
The GET command is a client request for data from a web server. A PUT command uploads resources and content, such as images, to a web server. A POST command uploads data files to a web server.
-
Question 26 of 28
26. Question
4 pointsMatch the TCP/IP model layer with the function.
Sort elements
- transport
- application
- network access
- internet
-
supports communication between applications
-
represents data to the user
-
controls the media
-
determines best path
Correct
Incorrect
-
Question 27 of 28
27. Question
4 pointsMatch the compressed IPv6 address representation with the full IPv6 address. (Not all options are used.)
Sort elements
- 2001:0DB8:0010:0000:0000:0000:0011:0101
- 2001:0DB8:0000:0000:0010:0000:0011:0101
- 2001:0DB8:0010:0011:0000:0000:0000:0010
- 2001:0DB8:0000:0000:0000:0010:0011:0101
- 2001:0DB8:0010:0000:0011:0000:0000:0101
-
2001:DB8:10::11:101
-
2001:DB8::10:0:11:101
-
2001:DB8:10:11::10
-
2001:DB8::10:11:101
Correct
Incorrect
-
Question 28 of 28
28. Question
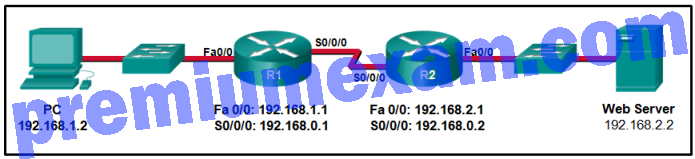
4 pointsRefer to the exhibit. Consider a datagram that originates on the PC and that is destined for the web server. Match the IP addresses and port numbers that are in that datagram to the description. (Not all options are used.)
Sort elements
- 192.168.1.2
- 192.168.2.2
- 2578
- 80
- 192.168.1.1
- 25
-
source IP address
-
destination IP address
-
source port number
-
destination port number
Correct
Incorrect
A TCP/IP segment that originated on the PC has 192.168.1.2 as the IP source address. 2578 is the only possible option for the source port number because the PC port number must be in the range of registered ports 1024 to 49151. The destination is the web server, which has the IP address 192.168.2.2, and the destination port number is 80 according to the HTTP protocol standard.
Hint
A TCP/IP segment that originated on the PC has 192.168.1.2 as the IP source address. 2578 is the only possible option for the source port number because the PC port number must be in the range of registered ports 1024 to 49151. The destination is the web server, which has the IP address 192.168.2.2, and the destination port number is 80 according to the HTTP protocol standard.