Last Updated on October 29, 2019 by Admin
CCNA CyberOps Chapter 12 Exam Online
CCNA CyberOps 1.1 -- Chapter 12 Exam
Quiz-summary
0 of 32 questions completed
Questions:
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
Information
CCNA CyberOps 1.1 — Chapter 12 Exam
You have already completed the quiz before. Hence you can not start it again.
Quiz is loading...
You must sign in or sign up to start the quiz.
You have to finish following quiz, to start this quiz:
Results
0 of 32 questions answered correctly
Your time:
Time has elapsed
You have reached 0 of 0 points, (0)
| Average score |
|
| Your score |
|
Categories
- Not categorized 0%
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- Answered
- Review
-
Question 1 of 32
1. Question
1 pointsWhich statement describes the status after the Security Onion VM is started?
Correct
Incorrect
Security Onion is a Linux distro for intrusion detection, network security monitoring, and log management. It contains many security tools like Snort, Suricata, Bro, and ELSA.
Hint
Security Onion is a Linux distro for intrusion detection, network security monitoring, and log management. It contains many security tools like Snort, Suricata, Bro, and ELSA.
-
Question 2 of 32
2. Question
1 pointsWhich tool is included with Security Onion that is used by Snort to automatically download new rules?
Correct
Incorrect
PulledPork is a rule management utility included with Security Onion to automatically download rules for Snort.
Hint
PulledPork is a rule management utility included with Security Onion to automatically download rules for Snort.
-
Question 3 of 32
3. Question
1 pointsWhat is indicated by a Snort signature ID that is below 3464?
Correct
Incorrect
Snort is an open source network intrusion prevention system (NIPS) and network intrusion detection system (NIDS) developed by Sourcefire. It has the ability to perform real time traffic analysis and packet logging on Internet Protocol (IP) networks and can also be used to detect probes or attacks.
Hint
Snort is an open source network intrusion prevention system (NIPS) and network intrusion detection system (NIDS) developed by Sourcefire. It has the ability to perform real time traffic analysis and packet logging on Internet Protocol (IP) networks and can also be used to detect probes or attacks.
-
Question 4 of 32
4. Question
1 pointsWhich tool is a Security Onion integrated host-based intrusion detection system?
Correct
Incorrect
OSSEC is a host-based intrusion detection system (HIDS) that is integrated into Security Onion and actively monitors host system operation.
Hint
OSSEC is a host-based intrusion detection system (HIDS) that is integrated into Security Onion and actively monitors host system operation.
-
Question 5 of 32
5. Question
1 pointsWhat is the tool that has alert records linked directly to the search functionality of the Enterprise Log Search and Archive (ELSA)?
Correct
Incorrect
The Enterprise Log Search and Archive (ELSA) is an enterprise-level tool for allowing searching and archiving of NSM data. Searches can be executed by pivoting from Sguil to ELSA as its search functionality is directly linked to Sguil alert records.
Hint
The Enterprise Log Search and Archive (ELSA) is an enterprise-level tool for allowing searching and archiving of NSM data. Searches can be executed by pivoting from Sguil to ELSA as its search functionality is directly linked to Sguil alert records.
-
Question 6 of 32
6. Question
3 pointsWhat are the three core functions provided by the Security Onion? (Choose three.)
Correct
Incorrect
Security Onion is an open source suite of Network Security Monitoring (NSM) tools for evaluating cybersecurity alerts. For cybersecurity analysts the Security Onion provides full packet capture, network-based and host-based intrusion detection systems, and alert analysis tools.
Hint
Security Onion is an open source suite of Network Security Monitoring (NSM) tools for evaluating cybersecurity alerts. For cybersecurity analysts the Security Onion provides full packet capture, network-based and host-based intrusion detection systems, and alert analysis tools.
-
Question 7 of 32
7. Question
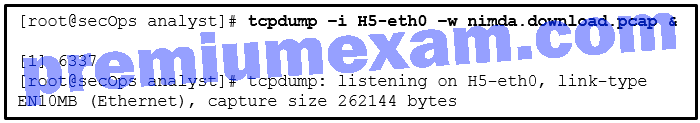
1 pointsRefer to the exhibit. A network security specialist issues the command tcpdump to capture events. What is the function provided by the ampersand symbol used in the command?
Correct
Incorrect
The ampersand symbol tells the Linux shell to execute tcpdump in the background.
Hint
The ampersand symbol tells the Linux shell to execute tcpdump in the background.
-
Question 8 of 32
8. Question
1 pointsA law office uses a Linux host as the firewall device for the network. The IT administrator is adding a rule to the firewall iptables to block internal hosts from connecting to a remote device that has the IP address 209.165.202.133. Which command should the administrator use?
Correct
Incorrect
The firewall iptables uses the concepts of chains and rules to filter traffic:
- INPUT chain – handles traffic entering the firewall and destined to the firewall device itself
- OUTPUT chain – handles traffic originating within the firewall device itself and destined to somewhere else
- FORWARD chain – handles traffic originated somewhere else and passing through the firewall device
Hint
The firewall iptables uses the concepts of chains and rules to filter traffic:
- INPUT chain – handles traffic entering the firewall and destined to the firewall device itself
- OUTPUT chain – handles traffic originating within the firewall device itself and destined to somewhere else
- FORWARD chain – handles traffic originated somewhere else and passing through the firewall device
-
Question 9 of 32
9. Question
1 pointsA threat actor has successfully breached the network firewall without being detected by the IDS system. What condition describes the lack of alert?
Correct
Incorrect
A false negative is where no alert exists and exploits are not being detected by the security systems that are in place.
Hint
A false negative is where no alert exists and exploits are not being detected by the security systems that are in place.
-
Question 10 of 32
10. Question
1 pointsWhat procedure should be avoided in a digital forensics investigation?
Correct
Incorrect
Digital forensic investigation is the science of collecting and examining electronic evidence that can evaluate damage to a computer as a result of an electronic attack or that can recover lost information from a system in order to prosecute a criminal. To prevent tampering and alteration of the suspect data, a data forensic analysis should be conducted on a copy of the suspect computer. Furthermore, restarting a computer may change or overwrite files and inadvertently destroy evidence.
Hint
Digital forensic investigation is the science of collecting and examining electronic evidence that can evaluate damage to a computer as a result of an electronic attack or that can recover lost information from a system in order to prosecute a criminal. To prevent tampering and alteration of the suspect data, a data forensic analysis should be conducted on a copy of the suspect computer. Furthermore, restarting a computer may change or overwrite files and inadvertently destroy evidence.
-
Question 11 of 32
11. Question
1 pointsWhich tool would an analyst use to start a workflow investigation?
Correct
Incorrect
Sguil is a GUI-based application used by security analysts to analyze network security events.
Hint
Sguil is a GUI-based application used by security analysts to analyze network security events.
-
Question 12 of 32
12. Question
2 pointsWhich two types of unreadable network traffic could be eliminated from data collected by NSM? (Choose two.)
Correct
Incorrect
To reduce the huge amount of data collected so that cybersecurity analysts can focus on critical threats, some less important or unusable data could be eliminated from the datasets. For example, encrypted data, such as IPsec and SSL traffic, could be eliminated because it is unreadable in a reasonable time frame.
Hint
To reduce the huge amount of data collected so that cybersecurity analysts can focus on critical threats, some less important or unusable data could be eliminated from the datasets. For example, encrypted data, such as IPsec and SSL traffic, could be eliminated because it is unreadable in a reasonable time frame.
-
Question 13 of 32
13. Question
1 pointsWhich term is used to describe the process of converting log entries into a common format?
Correct
Incorrect
For processing log entries, data normalization can organize and convert data values in datasets from difference sources into common format. The normalization makes it easy for further data analysis and reporting.
Hint
For processing log entries, data normalization can organize and convert data values in datasets from difference sources into common format. The normalization makes it easy for further data analysis and reporting.
-
Question 14 of 32
14. Question
1 pointsWhich statement describes a feature of timestamps in Linux?
Correct
Incorrect
-
Question 15 of 32
15. Question
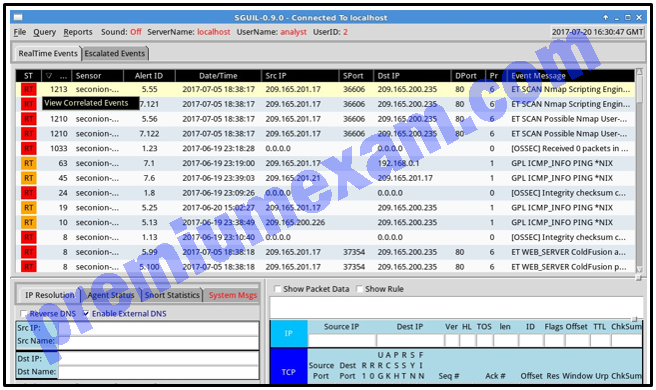
1 pointsRefer to the exhibit. A cybersecurity analyst is using Sguil to verify security alerts. How is the current view sorted?
Correct
Incorrect
The CNT column, between the ST and Sensor columns, displays the frequency of alerts. By sorting with frequency, the analyst will get a better sense of what has happened on the network.
Hint
The CNT column, between the ST and Sensor columns, displays the frequency of alerts. By sorting with frequency, the analyst will get a better sense of what has happened on the network.
-
Question 16 of 32
16. Question
2 pointsWhich two strings will be matched by the regular expression? (Choose two.)
Level[^12]
Correct
Incorrect
Regular expressions allow forensics analysts to search through large quantities of text information for patterns of data. Some common operators used in regular expressions are as follows:
$ End of a line.
[] Any single value within the square brackets.
* Preceding sub-expression zero or more times.
[^1] Any character except those bound by the [^ and the].Hint
Regular expressions allow forensics analysts to search through large quantities of text information for patterns of data. Some common operators used in regular expressions are as follows:
$ End of a line.
[] Any single value within the square brackets.
* Preceding sub-expression zero or more times.
[^1] Any character except those bound by the [^ and the]. -
Question 17 of 32
17. Question
1 pointsHow is the hash value of files useful in network security investigations?
Correct
Incorrect
When ELSA is used to investigate downloaded files, the hash value of each file is created and stored with other information about the file. If a cybersecurity analyst is suspicious of the file, the hash value can be submitted to an online malware repository site to determine if the file is known malware.
Hint
When ELSA is used to investigate downloaded files, the hash value of each file is created and stored with other information about the file. If a cybersecurity analyst is suspicious of the file, the hash value can be submitted to an online malware repository site to determine if the file is known malware.
-
Question 18 of 32
18. Question
1 pointsHow does an application program interact with the operating system?
Correct
Incorrect
Application programs interact with an operating system through system calls to the OS application programming interface (API). These system calls allow access to many aspects of system operation such as software process control, file management, device management, and network access.
Hint
Application programs interact with an operating system through system calls to the OS application programming interface (API). These system calls allow access to many aspects of system operation such as software process control, file management, device management, and network access.
-
Question 19 of 32
19. Question
3 pointsWhich three procedures in Sguil are provided to security analysts to address alerts? (Choose three.)
Correct
Incorrect
Sguil is a tool for addressing alerts. Three tasks can be completed in Sguil to manage alerts:Alerts that have been found to be false positives can be expired.
An alert can be escalated if the cybersecurity analyst is uncertain how to handle it.
Events that have been identified as true positives can be categorized.Hint
Sguil is a tool for addressing alerts. Three tasks can be completed in Sguil to manage alerts:Alerts that have been found to be false positives can be expired.
An alert can be escalated if the cybersecurity analyst is uncertain how to handle it.
Events that have been identified as true positives can be categorized. -
Question 20 of 32
20. Question
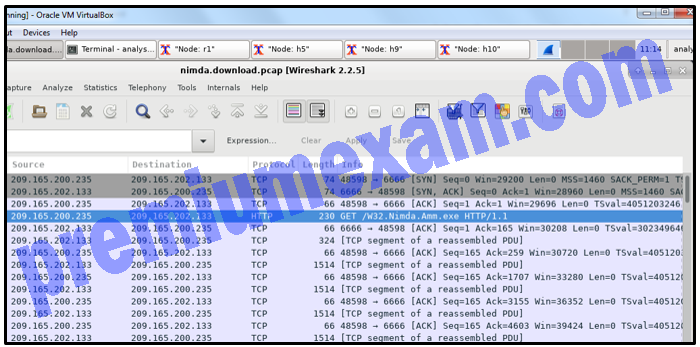
1 pointsRefer to the exhibit. A network security analyst is examining captured data using Wireshark. The captured frames indicate that a host is downloading malware from a server. Which source port is used by the host to request the download?
Correct
Incorrect
During the TCP three-way handshake process, the output shows that the host uses source port 48598 to initiate the connection and request the download.
Hint
During the TCP three-way handshake process, the output shows that the host uses source port 48598 to initiate the connection and request the download.
-
Question 21 of 32
21. Question
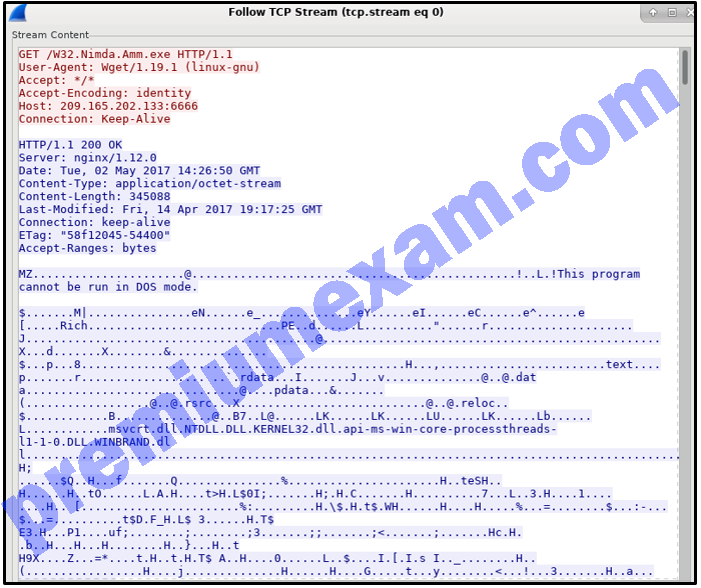
1 pointsRefer to the exhibit. A network security analyst is using the Follow TCP Stream feature in Wireshark to rebuild the TCP transaction. However, the transaction data seems indecipherable. What is the explanation for this?
Correct
Incorrect
The host is downloading W32.Nimda.Amm.exe, a binary file. Wireshark does not know how to represent it. The displayed symbols are the best guess at making sense of the binary data while decoding it as text.
Hint
The host is downloading W32.Nimda.Amm.exe, a binary file. Wireshark does not know how to represent it. The displayed symbols are the best guess at making sense of the binary data while decoding it as text.
-
Question 22 of 32
22. Question
1 pointsWhich tool is developed by Cisco and provides an interactive dashboard that allows investigation of the threat landscape?
Correct
Incorrect
Cisco Talos provides an interactive dashboard that allows investigation of the threat landscape.
Hint
Cisco Talos provides an interactive dashboard that allows investigation of the threat landscape.
-
Question 23 of 32
23. Question
1 pointsWhich type of evidence supports an assertion based on previously obtained evidence?
Correct
Incorrect
Corroborating evidence is evidence that supports a proposition already supported by initial evidence, therefore confirming the original proposition. Circumstantial evidence is evidence other than first-hand accounts of events provided by witnesses.
Hint
Corroborating evidence is evidence that supports a proposition already supported by initial evidence, therefore confirming the original proposition. Circumstantial evidence is evidence other than first-hand accounts of events provided by witnesses.
-
Question 24 of 32
24. Question
1 pointsAccording to NIST, which step in the digital forensics process involves extracting relevant information from data?
Correct
Incorrect
NIST describes the digital forensics process as involving the following four steps:
- Collection – the identification of potential sources of forensic data and acquisition, handling, and storage of that data.
- Examination – assessing and extracting relevant information from the collected data. This may involve decompression or decryption of the data.
- Analysis – drawing conclusions from the data. Salient features such as people, places, times, events, and so on should be documented.
- Reporting – preparing and presenting information that resulted from the analysis. Reporting should be impartial and alternative explanations should be offered if appropriate.
Hint
NIST describes the digital forensics process as involving the following four steps:
- Collection – the identification of potential sources of forensic data and acquisition, handling, and storage of that data.
- Examination – assessing and extracting relevant information from the collected data. This may involve decompression or decryption of the data.
- Analysis – drawing conclusions from the data. Salient features such as people, places, times, events, and so on should be documented.
- Reporting – preparing and presenting information that resulted from the analysis. Reporting should be impartial and alternative explanations should be offered if appropriate.
-
Question 25 of 32
25. Question
5 pointsMatch the characteristic to the method of security analysis.
Sort elements
- each event is the inevitable result of antecedent causes
- precise method that yields the same result every time by relying on predefined conditions
- analysis of applications that conform to application/networking standards
- random variables create difficulty in knowing the outcome of any given event with certainty
- preferred method for analyzing applications designed to circumvent firewalls
-
Deterministic Target
-
Deterministic Target
-
Deterministic Target
-
Probabilistic Target
-
Probabilistic Target
Correct
Incorrect
-
Question 26 of 32
26. Question
6 pointsMatch the field in the Event table of Sguil to the description.
Sort elements
- sid
- ip_proto
- signature
- cid
- timestamp
- status
-
the unique ID of the sensor
-
IP protocol type of the packet
-
the human readable name of the event
-
the unique event number from the sensor
-
the time the event occurred on the sensor
-
the Sguil classification assigned to this event
Correct
Incorrect
-
Question 27 of 32
27. Question
7 pointsPlace the evidence collection priority from most volatile to least volatile as defined by the IETF guidelines.
Sort elements
- memory registers, caches
- routing table, ARP cache, process table, kernel statistics, RAM
- temporary file systems
- non-volatile media, fixed and removable
- remote logging and monitoring data
- physical interconnections and topologies
- physical interconnections and topologies
-
1. (most volatile)
-
2.
-
3.
-
4.
-
5.
-
6.
-
7. (least volatile)
Correct
Incorrect
-
Question 28 of 32
28. Question
1 pointsCorrect
Incorrect
Amateur or script kiddies use common existing tools found on the internet to launch attacks. Hacktivists disrupt services in protest against organizations or governments for a particular political or social idea. State-sponsored threat actors use cyberspace for industrial espionage or interfering with another country in some way. Terrorist groups attack for a specific cause.
Hint
Amateur or script kiddies use common existing tools found on the internet to launch attacks. Hacktivists disrupt services in protest against organizations or governments for a particular political or social idea. State-sponsored threat actors use cyberspace for industrial espionage or interfering with another country in some way. Terrorist groups attack for a specific cause.
-
Question 29 of 32
29. Question
1 pointsCorrect
Incorrect
Evidence is classified as direct or indirect. Direct evidence is that the accused was caught in the act, there is an eyewitness, or the evidence is indisputable. Three other types of evidence are best, corroborating, and indirect. Best is evidence in its original state. Corroborating evidence supports an assertion developed from best evidence. Indirect evidence provides support for a hypothesis.
Hint
Evidence is classified as direct or indirect. Direct evidence is that the accused was caught in the act, there is an eyewitness, or the evidence is indisputable. Three other types of evidence are best, corroborating, and indirect. Best is evidence in its original state. Corroborating evidence supports an assertion developed from best evidence. Indirect evidence provides support for a hypothesis.
-
Question 30 of 32
30. Question
1 pointsCorrect
Incorrect
A denial-of-service attack results in an interruption of service to users, devices, or applications or all three. A direct DoS attack uses zombies and bots in order to have a coordinated attack from a multitude of sources. An access attack exploit known vulnerabilities in servers. Social engineering is a specific type of access attack toward an individual in an effort to get that individual to divulge information.
Hint
A denial-of-service attack results in an interruption of service to users, devices, or applications or all three. A direct DoS attack uses zombies and bots in order to have a coordinated attack from a multitude of sources. An access attack exploit known vulnerabilities in servers. Social engineering is a specific type of access attack toward an individual in an effort to get that individual to divulge information.
-
Question 31 of 32
31. Question
1 pointsCorrect
Incorrect
Threat attribution refers to determining the individual, organization, or nation responsible for a successful intrusion or attack incident. The security investigation team correlates all the evidence in order to identify commonalities between tactics, techniques, and procedures (TPPs) for known and unknown threat actors.
Hint
Threat attribution refers to determining the individual, organization, or nation responsible for a successful intrusion or attack incident. The security investigation team correlates all the evidence in order to identify commonalities between tactics, techniques, and procedures (TPPs) for known and unknown threat actors.
-
Question 32 of 32
32. Question
3 pointsCorrect
Incorrect
Three tools used to carry out this type of attack are TCP SYN flood, buffer overflow, and smurf attack. All three attacks send data in order to overwhelm another network device. A ping sweep is used in reconnaissance. Man-in-the middle occurs when the threat actor collects data in order to read, modify, or redirect that data. IP, MAC, and DHCP spoofing attacks are used to falsify address data.
Hint
Three tools used to carry out this type of attack are TCP SYN flood, buffer overflow, and smurf attack. All three attacks send data in order to overwhelm another network device. A ping sweep is used in reconnaissance. Man-in-the middle occurs when the threat actor collects data in order to read, modify, or redirect that data. IP, MAC, and DHCP spoofing attacks are used to falsify address data.