Last Updated on October 29, 2019 by Admin
CCNA CyberOps Chapter 11 Exam Online
CCNA CyberOps 1.1 -- Chapter 11 Exam
Quiz-summary
0 of 29 questions completed
Questions:
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
Information
CCNA CyberOps 1.1 — Chapter 11 Exam
You have already completed the quiz before. Hence you can not start it again.
Quiz is loading...
You must sign in or sign up to start the quiz.
You have to finish following quiz, to start this quiz:
Results
0 of 29 questions answered correctly
Your time:
Time has elapsed
You have reached 0 of 0 points, (0)
| Average score |
|
| Your score |
|
Categories
- Not categorized 0%
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- Answered
- Review
-
Question 1 of 29
1. Question
2 pointsWhich two application layer protocols manage the exchange of messages between a client with a web browser and a remote web server? (Choose two.)
Correct
Incorrect
Hypertext Transfer Protocol (HTTP) and HTTP Secure (HTTPS) are two application layer protocols that manage the content requests from clients and the responses from the web server. HTML (Hypertext Mark-up Language) is the encoding language that describes the content and display features of a web page. DNS is for domain name to IP address resolution. DHCP manages and provides dynamic IP configurations to clients.
Hint
Hypertext Transfer Protocol (HTTP) and HTTP Secure (HTTPS) are two application layer protocols that manage the content requests from clients and the responses from the web server. HTML (Hypertext Mark-up Language) is the encoding language that describes the content and display features of a web page. DNS is for domain name to IP address resolution. DHCP manages and provides dynamic IP configurations to clients.
-
Question 2 of 29
2. Question
1 pointsWhat port number would be used if a threat actor was using NTP to direct DDoS attacks?
Correct
Incorrect
NTP uses UDP port number 123. Threat actors could use port 123 on NTP systems in order to direct DDoS attacks through vulnerabilities in client or server software.
Hint
NTP uses UDP port number 123. Threat actors could use port 123 on NTP systems in order to direct DDoS attacks through vulnerabilities in client or server software.
-
Question 3 of 29
3. Question
1 pointsWhich protocol is a name resolution protocol often used by malware to communicate with command-and-control (CnC) servers?
Correct
Incorrect
Domain Name Service (DNS) is used to convert domain names into IP addresses. Some organizations have less stringent policies in place to protect against DNS-based threats than they have in place for other exploits.
Hint
Domain Name Service (DNS) is used to convert domain names into IP addresses. Some organizations have less stringent policies in place to protect against DNS-based threats than they have in place for other exploits.
-
Question 4 of 29
4. Question
2 pointsWhat are two ways that ICMP can be a security threat to a company? (Choose two.)
Correct
Incorrect
ICMP can be used as a conduit for DoS attacks. It can be used to collect information about a network such as the identification of hosts and network structure, and by determining the operating systems being used on the network.
Hint
ICMP can be used as a conduit for DoS attacks. It can be used to collect information about a network such as the identification of hosts and network structure, and by determining the operating systems being used on the network.
-
Question 5 of 29
5. Question
1 pointsHow might corporate IT professionals deal with DNS-based cyber threats?
Correct
Incorrect
DNS queries for randomly generated domain names or extremely long random-appearing DNS subdomains should be considered suspicious. Cyberanalysts could do the following for DNS-based attacks:Analyze DNS logs.
Use a passive DNS service to block requests to suspected CnC and exploit domains.Hint
DNS queries for randomly generated domain names or extremely long random-appearing DNS subdomains should be considered suspicious. Cyberanalysts could do the following for DNS-based attacks:Analyze DNS logs.
Use a passive DNS service to block requests to suspected CnC and exploit domains. -
Question 6 of 29
6. Question
1 pointsWhich protocol is used to send e-mail messages between two servers that are in different e-mail domains?
Correct
Incorrect
SMTP is used to send data between mail servers and to send data from a host to a mail server. The other two protocols that can be used for email are IMAP and POP3. IMAP and POP3 are used to download email messages from a mail server.
Hint
SMTP is used to send data between mail servers and to send data from a host to a mail server. The other two protocols that can be used for email are IMAP and POP3. IMAP and POP3 are used to download email messages from a mail server.
-
Question 7 of 29
7. Question
1 pointsHow can IMAP be a security threat to a company?
Correct
Incorrect
IMAP, SMTP, and POP3 are email protocols. SMTP is used to send data from a host to a server or to send data between servers. IMAP and POP3 are used to download email messages and can be responsible for bringing malware to the receiving host.
Hint
IMAP, SMTP, and POP3 are email protocols. SMTP is used to send data from a host to a server or to send data between servers. IMAP and POP3 are used to download email messages and can be responsible for bringing malware to the receiving host.
-
Question 8 of 29
8. Question
1 pointsHow does using HTTPS complicate network security monitoring?
Correct
Incorrect
HTTPS adds extra overhead to the HTTP-formed packet. HTTPS encrypts using secure socket layer (SSL). Even though some devices can perform SSL decryption and inspection, this can present processing and privacy issues. HTTPS adds complexity to packet captures due to the additional message involved in establishing an encrypted data connection.
Hint
HTTPS adds extra overhead to the HTTP-formed packet. HTTPS encrypts using secure socket layer (SSL). Even though some devices can perform SSL decryption and inspection, this can present processing and privacy issues. HTTPS adds complexity to packet captures due to the additional message involved in establishing an encrypted data connection.
-
Question 9 of 29
9. Question
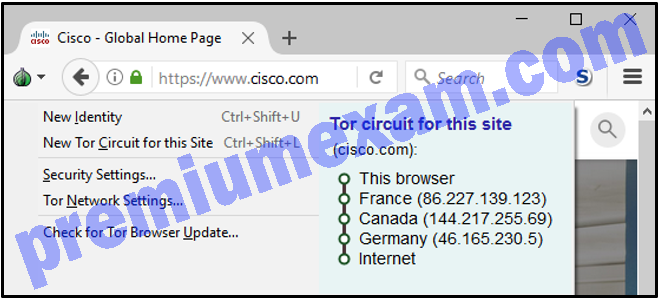
1 pointsRefer to the exhibit. How is the traffic from the client web browser being altered when connected to the destination website of http://www.cisco.com?
Correct
Incorrect
When data is being sent into the TOR network, the data is only encrypted by the sending client itself. The next-hop information is encrypted and decrypted between the TOR relays on a hop-by-hop basis. In this way, no single device knows the entire path to the destination, and routing information is readable only by the device that requires it. Finally, at the end of the Tor path, the traffic reaches its Internet destination. The client data is not encrypted by the TOR network; that encryption is the responsibility of the user.
Hint
When data is being sent into the TOR network, the data is only encrypted by the sending client itself. The next-hop information is encrypted and decrypted between the TOR relays on a hop-by-hop basis. In this way, no single device knows the entire path to the destination, and routing information is readable only by the device that requires it. Finally, at the end of the Tor path, the traffic reaches its Internet destination. The client data is not encrypted by the TOR network; that encryption is the responsibility of the user.
-
Question 10 of 29
10. Question
1 pointsWhat is Tor?
Correct
Incorrect
A special browser is used to access the Tor network. This browser allows a user to browse the Internet anonymously.
Hint
A special browser is used to access the Tor network. This browser allows a user to browse the Internet anonymously.
-
Question 11 of 29
11. Question
1 pointsWhich function is provided by the Sguil application?
Correct
Incorrect
Applications such as Snorby and Sguil can be used to read and search alert messages generated by NIDS/NIPS.
Hint
Applications such as Snorby and Sguil can be used to read and search alert messages generated by NIDS/NIPS.
-
Question 12 of 29
12. Question
1 pointsWhich statement describes session data in security logs?
Correct
Incorrect
Session data is a record of a conversation between two network endpoints.
Hint
Session data is a record of a conversation between two network endpoints.
-
Question 13 of 29
13. Question
1 pointsWhich statement describes statistical data in network security monitoring processes?
Correct
Incorrect
Like session data, statistical data is about network traffic. Statistical data is created through the analysis of other forms of network data.
Hint
Like session data, statistical data is about network traffic. Statistical data is created through the analysis of other forms of network data.
-
Question 14 of 29
14. Question
2 pointsWhich two options are network security monitoring approaches that use advanced analytic techniques to analyze network telemetry data? (Choose two.)
Correct
Incorrect
Network behavior analysis (NBA) and network behavior anomaly detection (NBAD) are approaches to network security monitoring that use advanced analytical techniques to analyze NetFlow or IPFIX network telemetry data.
Hint
Network behavior analysis (NBA) and network behavior anomaly detection (NBAD) are approaches to network security monitoring that use advanced analytical techniques to analyze NetFlow or IPFIX network telemetry data.
-
Question 15 of 29
15. Question
1 pointsA system administrator runs a file scan utility on a Windows PC and notices a file lsass.exe in the Program Files directory. What should the administrator do?
Correct
Incorrect
On Windows computers, security logging and security policies enforcement are carried out by the Local Security Authority Subsystem Service (LSASS), running as lsass.exe. It should be running from the Windows\System32 directory. If a file with this name, or a camouflaged name, such as 1sass.exe, is running or running from another directory, it could be malware.
Hint
On Windows computers, security logging and security policies enforcement are carried out by the Local Security Authority Subsystem Service (LSASS), running as lsass.exe. It should be running from the Windows\System32 directory. If a file with this name, or a camouflaged name, such as 1sass.exe, is running or running from another directory, it could be malware.
-
Question 16 of 29
16. Question
1 pointsA system analyst is reviewing syslog messages and notices that the PRI value of a message is 26. What is the severity value of the message?
Correct
Incorrect
The priority (PRI) value consists of two elements, the facility and severity of the message. It is calculated by multiplying the facility value by 8, and then adding the severity value, that is, priority = (facility * 8) + severity. To find the severity value from a given PRI, divide the PRI by 8 and the remainder is the severity value.
Hint
The priority (PRI) value consists of two elements, the facility and severity of the message. It is calculated by multiplying the facility value by 8, and then adding the severity value, that is, priority = (facility * 8) + severity. To find the severity value from a given PRI, divide the PRI by 8 and the remainder is the severity value.
-
Question 17 of 29
17. Question
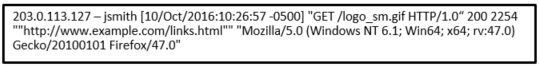
1 pointsRefer to the exhibit. A network administrator is reviewing an Apache access log message. What is the status of the access request by the client?
Correct
Incorrect
The sixth field of the Apache access log message is the three-digital numeric status code. Codes that begin with a 2 represent success. Codes that begin with a 3 represent redirection. Codes that begin with a 4 represent client errors. Codes that begin with a 5 represent server errors.
Hint
The sixth field of the Apache access log message is the three-digital numeric status code. Codes that begin with a 2 represent success. Codes that begin with a 3 represent redirection. Codes that begin with a 4 represent client errors. Codes that begin with a 5 represent server errors.
-
Question 18 of 29
18. Question
1 pointsWhat does it indicate if the timestamp in the HEADER section of a syslog message is preceded by a period or asterisk symbol?
Correct
Incorrect
The HEADER section of the message contains the timestamp. If the timestamp is preceded by the period (.) or asterisk (*) symbols, a problem is indicated with NTP.
Hint
The HEADER section of the message contains the timestamp. If the timestamp is preceded by the period (.) or asterisk (*) symbols, a problem is indicated with NTP.
-
Question 19 of 29
19. Question
1 pointsWhich Windows log records events related to login attempts and operations related to file or object access?
Correct
Incorrect
On a Windows host, security logs record events related to security, such as login attempts and operations related to file or object management and access.
Hint
On a Windows host, security logs record events related to security, such as login attempts and operations related to file or object management and access.
-
Question 20 of 29
20. Question
1 pointsWhich Windows log contains information about installations of software, including Windows updates?
Correct
Incorrect
On a Windows host, setup logs record information about the installation of software, including Windows updates.
Hint
On a Windows host, setup logs record information about the installation of software, including Windows updates.
-
Question 21 of 29
21. Question
1 pointsWhich information can be provided by the Cisco NetFlow utility?
Correct
Incorrect
NetFlow efficiently provides an important set of services for IP applications including network traffic accounting, usage-based network billing, network planning, security, denial of service monitoring capabilities, and network monitoring. NetFlow provides valuable information about network users and applications, peak usage times, and traffic routing.
Hint
NetFlow efficiently provides an important set of services for IP applications including network traffic accounting, usage-based network billing, network planning, security, denial of service monitoring capabilities, and network monitoring. NetFlow provides valuable information about network users and applications, peak usage times, and traffic routing.
-
Question 22 of 29
22. Question
1 pointsIn a Cisco AVC system, in which module is NetFlow deployed?
Correct
Incorrect
NetFlow technology is deployed in the Metrics Collection module of a Cisco AVC system to collect network flow metrics and to export to management tools.
Hint
NetFlow technology is deployed in the Metrics Collection module of a Cisco AVC system to collect network flow metrics and to export to management tools.
-
Question 23 of 29
23. Question
1 pointsHow does a web proxy device provide data loss prevention (DLP) for an enterprise?
Correct
Incorrect
A web proxy device can inspect outgoing traffic as means of data loss prevention (DLP). DLP involves scanning outgoing traffic to detect whether the data that is leaving the enterprise network contains sensitive, confidential, or secret information.
Hint
A web proxy device can inspect outgoing traffic as means of data loss prevention (DLP). DLP involves scanning outgoing traffic to detect whether the data that is leaving the enterprise network contains sensitive, confidential, or secret information.
-
Question 24 of 29
24. Question
1 pointsWhich technology is used in Cisco Next-Generation IPS devices to consolidate multiple security layers into a single platform?
Correct
Incorrect
Cisco Next-Generation IPS devices (NGIPS) use FirePOWER Services to consolidate multiple security layers into a single platform, which helps to contain costs and simplify management. Apache Traffic Server, Squid, and WinGate are examples of web proxies.
Hint
Cisco Next-Generation IPS devices (NGIPS) use FirePOWER Services to consolidate multiple security layers into a single platform, which helps to contain costs and simplify management. Apache Traffic Server, Squid, and WinGate are examples of web proxies.
-
Question 25 of 29
25. Question
1 pointsRefer to the exhibit. A junior network engineer is handed a print-out of the network information shown. Which protocol or service originated the information shown in the graphic?
Correct
Incorrect
Syslog clients send log entries to a syslog server. The syslog server concentrates and stores log entries. Log entries are categorized by seven severity levels:
emergencies (0), alerts (1), critical (2), errors (3), warnings (4), notifications (5), informational (6), and debugging (7).Hint
Syslog clients send log entries to a syslog server. The syslog server concentrates and stores log entries. Log entries are categorized by seven severity levels:
emergencies (0), alerts (1), critical (2), errors (3), warnings (4), notifications (5), informational (6), and debugging (7). -
Question 26 of 29
26. Question
2 pointsCorrect
Incorrect
The syslog standard is used for logging event messages from network devices. Syslog messages are sent from the device to a logging server. Apache web server access logs are an important source of information for a cybersecurity analyst in order to see who accessed the server, the IP address used, date/time of access, and URL used.
Hint
The syslog standard is used for logging event messages from network devices. Syslog messages are sent from the device to a logging server. Apache web server access logs are an important source of information for a cybersecurity analyst in order to see who accessed the server, the IP address used, date/time of access, and URL used.
-
Question 27 of 29
27. Question
1 pointsCorrect
Incorrect
A daemon in Linux is a background process that runs without the need for user interaction. A network administrator can view log files in order to see information about daemons running on the Linux server.
Hint
A daemon in Linux is a background process that runs without the need for user interaction. A network administrator can view log files in order to see information about daemons running on the Linux server.
-
Question 28 of 29
28. Question
1 pointsCorrect
Incorrect
Discretionary access control allows users to control access to their data as owners of that data. ACLs may also be used in order to specify which users or groups have access to the data.
Hint
Discretionary access control allows users to control access to their data as owners of that data. ACLs may also be used in order to specify which users or groups have access to the data.
-
Question 29 of 29
29. Question
2 pointsCorrect
Incorrect
Based on the ex3 file system, an ext4 partition includes extensions that improve performance and an increase in the of supported files. An ext4 partition also supports journaling, a file system feature that minimizes the risk of file system corruption if power is suddenly lost to the system.
Hint
Based on the ex3 file system, an ext4 partition includes extensions that improve performance and an increase in the of supported files. An ext4 partition also supports journaling, a file system feature that minimizes the risk of file system corruption if power is suddenly lost to the system.