Last Updated on October 26, 2019 by Admin
Networking Essentials Chapter 1-5 Checkpoint Exam Online Full 100% 2019
NE -- Chapter 1-5 Checkpoint Exam
Quiz-summary
0 of 26 questions completed
Questions:
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
Information
NE — Chapter 1-5 Checkpoint Exam
You have already completed the quiz before. Hence you can not start it again.
Quiz is loading...
You must sign in or sign up to start the quiz.
You have to finish following quiz, to start this quiz:
Results
0 of 26 questions answered correctly
Your time:
Time has elapsed
You have reached 0 of 0 points, (0)
| Average score |
|
| Your score |
|
Categories
- Not categorized 0%
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- Answered
- Review
-
Question 1 of 26
1. Question
1 pointsWhat is an example of a binary value from everyday life?
Correct
Incorrect
A binary digit (or bit) has two possible values, 0 or 1. The on and off state of a simple switch is an example of the two states represented by a bit.
Hint
A binary digit (or bit) has two possible values, 0 or 1. The on and off state of a simple switch is an example of the two states represented by a bit.
-
Question 2 of 26
2. Question
1 pointsWhich wireless technology is used on smart phones to transmit data to another device within only very close proximity?
Correct
Incorrect
Near Field Communications (NFC) is a wireless technology that enables data to be exchanged by devices that are in very close proximity to each other.
Hint
Near Field Communications (NFC) is a wireless technology that enables data to be exchanged by devices that are in very close proximity to each other.
-
Question 3 of 26
3. Question
2 pointsWhich two devices are shared peripherals? (Choose two.)
Correct
Incorrect
A shared peripheral device does not connect directly to a network. This device is attached to a host (such as a PC) and the host connects to the network to share the peripheral device.
Hint
A shared peripheral device does not connect directly to a network. This device is attached to a host (such as a PC) and the host connects to the network to share the peripheral device.
-
Question 4 of 26
4. Question
3 pointsWhich three configuration components are required to allow a host to communicate with other hosts on remote networks? (Choose three.)
Correct
Incorrect
An IP address, a subnet mask, and a default gateway are required on a host that must communicate with another host in a remote network. DNS server information is needed if mapping a domain name to an associated IP address. DHCP server information is dynamically learned and is not a required configuration for remote network reachability.
Hint
An IP address, a subnet mask, and a default gateway are required on a host that must communicate with another host in a remote network. DNS server information is needed if mapping a domain name to an associated IP address. DHCP server information is dynamically learned and is not a required configuration for remote network reachability.
-
Question 5 of 26
5. Question
3 pointsWhich three factors should be considered when choosing the appropriate network media? (Choose three.)
Correct
Incorrect
Several criteria should be considered when selecting network media:The cost of the media and installation
The environment in which the media is installed
The amount of data and the data transfer rate desired
The distance between hosts that the media will connectHint
Several criteria should be considered when selecting network media:The cost of the media and installation
The environment in which the media is installed
The amount of data and the data transfer rate desired
The distance between hosts that the media will connect -
Question 6 of 26
6. Question
1 pointsWhich factor classifies a host as a server?
Correct
Incorrect
A server is a host with server software installed. Although CPU, memory, and the network connection will determine the performance of a server, it is the server software that provides desired server services.
Hint
A server is a host with server software installed. Although CPU, memory, and the network connection will determine the performance of a server, it is the server software that provides desired server services.
-
Question 7 of 26
7. Question
2 pointsWhich two types of interference may affect the data throughput on UTP cables? (Choose two.)
Correct
Incorrect
Unshielded twisted-pair (UTP) cabling is sensitive to the interference introduced by electromagnetic interference (EMI) and crosstalk.
Hint
Unshielded twisted-pair (UTP) cabling is sensitive to the interference introduced by electromagnetic interference (EMI) and crosstalk.
-
Question 8 of 26
8. Question
1 pointsWhich statement defines a data communications protocol?
Correct
Incorrect
A data communication protocol is a set of rules that govern the communication process.
Hint
A data communication protocol is a set of rules that govern the communication process.
-
Question 9 of 26
9. Question
1 pointsWhich statement describes a MAC address?
Correct
Incorrect
The Media Access Control (MAC) address is a physical address assigned to each Ethernet NIC by manufacturers. It is 48-bits in length. The MAC address is used to identify the source and destination on a local Ethernet network. It cannot be routed to remote networks.
Hint
The Media Access Control (MAC) address is a physical address assigned to each Ethernet NIC by manufacturers. It is 48-bits in length. The MAC address is used to identify the source and destination on a local Ethernet network. It cannot be routed to remote networks.
-
Question 10 of 26
10. Question
1 pointsWhat information does an Ethernet switch examine and use to build its address table?
Correct
Incorrect
An Ethernet switch examines the source MAC address of an incoming frame. If the source MAC address is not in the MAC address table, the switch will add it to the table with the associated ingress Ethernet port.
Hint
An Ethernet switch examines the source MAC address of an incoming frame. If the source MAC address is not in the MAC address table, the switch will add it to the table with the associated ingress Ethernet port.
-
Question 11 of 26
11. Question
1 pointsWhat is the equivalent decimal value given a binary number of 11001010?
Correct
Incorrect
The equivalent decimal value for a binary number of 11001010 can be determined by 1*2^7+1*2^6+1*2^3+1*2^1.
Hint
The equivalent decimal value for a binary number of 11001010 can be determined by 1*2^7+1*2^6+1*2^3+1*2^1.
-
Question 12 of 26
12. Question
1 pointsWhat is the difference between the terms bandwidth and throughput?
Correct
Incorrect
Both bandwidth and throughput are the measurement of data transfer over a period of time. They use the same measurement units. However, bandwidth is used to indicate the theoretical capacity of a network connection whereas throughput is used to indicate the actual data transfer rate between two hosts at the time of measurement.
Hint
Both bandwidth and throughput are the measurement of data transfer over a period of time. They use the same measurement units. However, bandwidth is used to indicate the theoretical capacity of a network connection whereas throughput is used to indicate the actual data transfer rate between two hosts at the time of measurement.
-
Question 13 of 26
13. Question
3 pointsWhich three IP addresses are considered private addresses? (Choose three.)
Correct
Incorrect
The designated private IP addresses are within the three IP address ranges:10.0.0.0 – 10.255.255.255
172.16.0.0 – 172.31.255.255
192.168.0.0 – 192.168.255.255Hint
The designated private IP addresses are within the three IP address ranges:10.0.0.0 – 10.255.255.255
172.16.0.0 – 172.31.255.255
192.168.0.0 – 192.168.255.255 -
Question 14 of 26
14. Question
1 pointsWhich IP address is a unicast address if a default subnet mask is used?
Correct
Incorrect
The IP addresses 201.34.45.0, 192.16.43.67, and 195.124.45.255 are Class C addresses. With the default subnet mask of 255.255.255.0, 192.16.43.67 is a unicast address or host address, 195.124.45.255 is a broadcast address, and 201.34.45.0 is a network address. IP address 226.34.15.78 is a Class D multicast address.
Hint
The IP addresses 201.34.45.0, 192.16.43.67, and 195.124.45.255 are Class C addresses. With the default subnet mask of 255.255.255.0, 192.16.43.67 is a unicast address or host address, 195.124.45.255 is a broadcast address, and 201.34.45.0 is a network address. IP address 226.34.15.78 is a Class D multicast address.
-
Question 15 of 26
15. Question
1 pointsWhat is the full uncompressed representation of the IPv6 address 2001:DB8:0:0:AA::200?
Correct
Incorrect
An IPv6 address is made up of 128 bits represented in hexadecimal numbers.There are two rules that help reduce the number of digits needed to represent an IPv6 address.Rule 1 – Omit leading zeros in any 16-bit section.
Rule 2 – Replace any single group of consecutive zeros with a double colon (::). This can only be used once within an IPv6 address.Hint
An IPv6 address is made up of 128 bits represented in hexadecimal numbers.There are two rules that help reduce the number of digits needed to represent an IPv6 address.Rule 1 – Omit leading zeros in any 16-bit section.
Rule 2 – Replace any single group of consecutive zeros with a double colon (::). This can only be used once within an IPv6 address. -
Question 16 of 26
16. Question
1 pointsA user types http://www.cisco.com into a web browser to visit the corporate website. Which service will resolve the domain name to an associated IP address?
Correct
Incorrect
When a user types a domain name to visit a website, the DNS service is called to resolve the domain name to its associated IP address before the user packet is sent to the website.
Hint
When a user types a domain name to visit a website, the DNS service is called to resolve the domain name to its associated IP address before the user packet is sent to the website.
-
Question 17 of 26
17. Question
1 pointsA user opens multiple windows on the desktop with several tasks including web surfing, emailing, and Skype calling. What is used by the TCP/IP protocol stack to track the specific sessions for each application?
Correct
Incorrect
A user may request different services from the same server or different servers. TCP and UDP port numbers are used to keep track of specific sessions between a client and server.
Hint
A user may request different services from the same server or different servers. TCP and UDP port numbers are used to keep track of specific sessions between a client and server.
-
Question 18 of 26
18. Question
2 pointsWhich two application layer protocols manage the exchange of messages between a client with a web browser and a remote web server? (Choose two.)
Correct
Incorrect
Hypertext Transfer Protocol (HTTP) and HTTP Secure (HTTPS) are two application layer protocols that manage the content requests from clients and the responses from the web server. HTML (Hypertext Mark-up Language) is the encoding language that describes the content and display features of a web page. DNS is for domain name to IP address resolution. DHCP manages and provides dynamic IP configurations to clients.
Hint
Hypertext Transfer Protocol (HTTP) and HTTP Secure (HTTPS) are two application layer protocols that manage the content requests from clients and the responses from the web server. HTML (Hypertext Mark-up Language) is the encoding language that describes the content and display features of a web page. DNS is for domain name to IP address resolution. DHCP manages and provides dynamic IP configurations to clients.
-
Question 19 of 26
19. Question
1 pointsA client is sending a message to request information from a web server on the Internet. Which parameter is used in the message to indicate the specific service requested?
Correct
Incorrect
When clients send requests for a service from a server, the destination port number is used to indicate the specific service requested.
Hint
When clients send requests for a service from a server, the destination port number is used to indicate the specific service requested.
-
Question 20 of 26
20. Question
1 pointsHow much data can be encapsulated into a normal sized Ethernet frame before it is sent over the network?
Correct
Incorrect
According to the Ethernet standards, each Ethernet frame can carry 46 to 1500 bytes of user data. During the encapsulation process, other fields are added, such as destination MAC address, source MAC address, and FCS. The size of Ethernet frames is normally limited to a maximum of 1518 bytes and a minimum of 64 bytes.
Hint
According to the Ethernet standards, each Ethernet frame can carry 46 to 1500 bytes of user data. During the encapsulation process, other fields are added, such as destination MAC address, source MAC address, and FCS. The size of Ethernet frames is normally limited to a maximum of 1518 bytes and a minimum of 64 bytes.
-
Question 21 of 26
21. Question
1 pointsWhich transport layer protocol provides best effort delivery without guaranteeing that packets arrive at the destination?
Correct
Incorrect
User Datagram Protocol (UDP) is a best effort transport layer protocol. Unlike TCP, it does not use an acknowledgment protocol to ensure reliable packet delivery. TCP provides reliable delivery service. HTTP and SSH are application layer protocols in the TCP/IP model.
Hint
User Datagram Protocol (UDP) is a best effort transport layer protocol. Unlike TCP, it does not use an acknowledgment protocol to ensure reliable packet delivery. TCP provides reliable delivery service. HTTP and SSH are application layer protocols in the TCP/IP model.
-
Question 22 of 26
22. Question
1 pointsWhich scenario describes a peer-to-peer network?
Correct
Incorrect
In a peer-to-peer network there is no centralized or dedicated server. A user computer can be a client to request service from another user computer and a server to share a network resource (such as a printer) to other users.
Hint
In a peer-to-peer network there is no centralized or dedicated server. A user computer can be a client to request service from another user computer and a server to share a network resource (such as a printer) to other users.
-
Question 23 of 26
23. Question
3 pointsWhich three devices are considered intermediate devices in a network? (Choose three.)
Correct
Incorrect
Intermediate devices in a network provide network connectivity to end devices and transfer user data packets during data communications.
Hint
Intermediate devices in a network provide network connectivity to end devices and transfer user data packets during data communications.
-
Question 24 of 26
24. Question
1 pointsWhen a host sends a packet, how does it determine if the destination of the packet is on the same local network or on a remote network?
Correct
Incorrect
When a host sends a packet, it uses the subnet mask to compare the source IPv4 address and the destination IPv4 address. If the network bits match, both the source and destination host are on the same local network. Otherwise, the destination host is on a remote network.
Hint
When a host sends a packet, it uses the subnet mask to compare the source IPv4 address and the destination IPv4 address. If the network bits match, both the source and destination host are on the same local network. Otherwise, the destination host is on a remote network.
-
Question 25 of 26
25. Question
4 pointsMatch the TCP/IP model layer to the function.
Sort elements
- internet
- application
- network access
- transport
-
determines the best path to forward data through the network.
-
represents data to the user, encoding, and dialog control.
-
controls hardware devices and media that make up the network.
-
supports communication between diverse devices across networks
Correct
Incorrect
-
Question 26 of 26
26. Question
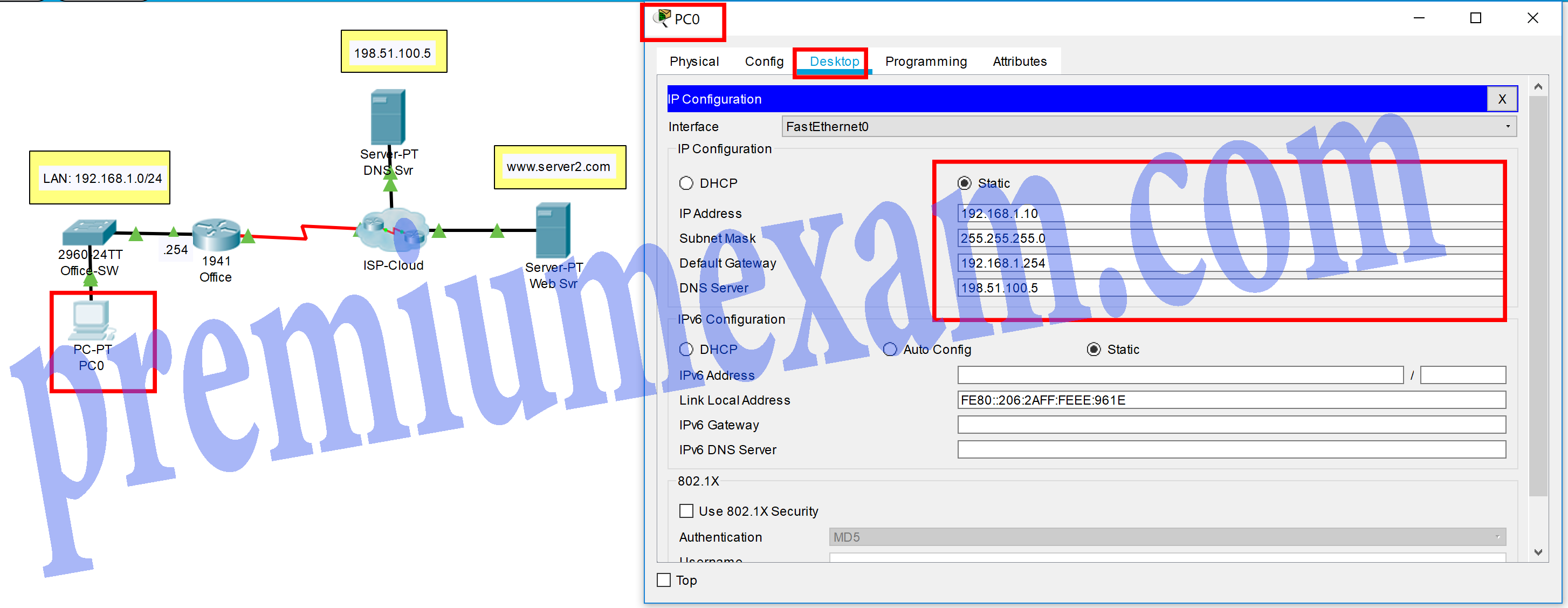
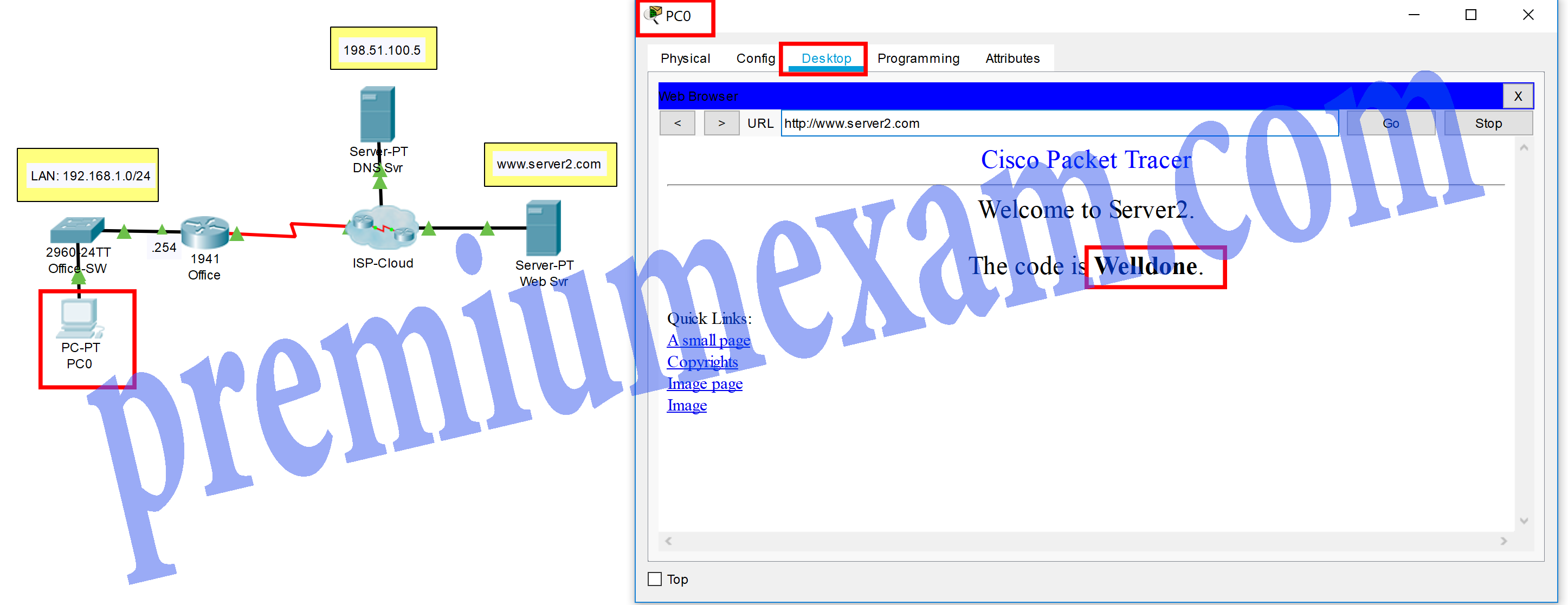
1 pointsOpen the PT Activity. Perform the tasks in the activity instructions and then answer the question.
What is the code displayed on the web page?Correct
Incorrect
The IP address configuration on PC0 requires the following:IP address – any valid host address on the LAN, except for .254
Subnet mask – default value for the network
Gateway – the nearest router interface
DNS – the DNS server on the ISP networkHint
The IP address configuration on PC0 requires the following:IP address – any valid host address on the LAN, except for .254
Subnet mask – default value for the network
Gateway – the nearest router interface
DNS – the DNS server on the ISP network