Last Updated on January 28, 2021 by Admin
IT Essentials – ITE Chapter 10 Exam Answers v6.0 2018 2019
Cisco ITE v6.0 latest or IT Essentials v6.0 Chapter 10 Exam Answers PC hardware and software (ITE Version 6.00) collection year 2017, 2018 and 2019 Full 100%. IT Essentials has been know as ITE v6. The following are the questions exam answers. Guarantee Passed. ITE v6.0 Chapter 10 exam answers has some new update from the old version 5. You can review all Chapter 10 Exam Answers. You will get passed scored 100% with this version 6.0. Good Luck for ITE v6.0 Exam!
CCNA7.COM is helping you to collect Cisco IT Essentials Chapter 10 Exam Answers v6 2018 & 2019 or ITE Chapter 10 Exam to show you on this page. ITE Chapter 10 Exam is almost 28 questions. While you take exam online with Cisco, you will meet 28 questions with duration 1 hours to 2 hours depend on your instructor activate. To pass ITE v6 Chapter 10 Exam, you should review all these question. We provide you accurate answer 100%.
Click here go to ITE Chapter 10 Exam – Online Test
-
What are two ways that iOS differs from Android? (Choose two.)
- iOS uses an All Apps button whereas Android uses a Home button.
- iOS has a physical Home button, but Android uses navigation icons.
- In iOS, the icon for an app represents the app itself. Deleting the icon in iOS deletes the app. In Android, the icon on the Home screen is a shortcut to the app.
- In iOS, apps can only appear on screens, whereas in Android, apps can appear on screens and in folders.
- In iOS, folders are created by dragging one app on top of another app, but in Android folders must be created from the home screen menu.
Explanation: Apple iOS devices have a physical Home button that has many uses. One of the uses of the Home button is navigation between screens. Android uses navigation icons instead of a physical Home button. In addition, much like a Windows OS, apps in Android are represented by icons that are shortcuts to the actual app. In iOS, the icons are the apps. Deleting an icon in Android deletes only the shortcut. However, the entire app is deleted from an iOS device when its icon is deleted.
-
What is a good source for safely downloading Android apps?
- iTunes
- Google Play
- freeware sites
- the Apple App Store
Explanation: Google Play ensures that the app is compatible with the mobile device and is a trusted source for apps.
-
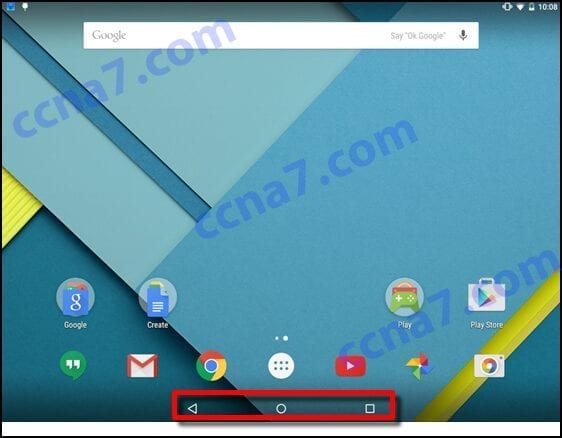
Refer to the exhibit. What two statements are true about the operating system screen shown? (Choose two.)
- The area that is highlighted contains navigation icons.
- The area that is highlighted displays background processes and indicators.
- The area that is highlighted contains the system icons.
- This is an Android screen.
- This is an iOS screen.
Explanation: The highlighted area shows the Android operating system navigation icons. From left to right they are Back, Home, and Recent Apps.
-
A small number has appeared on one of the apps on a user’s iOS home screen. What does this mean?
- It is an alert badge that indicates the number of items requiring attention for that app.
- It indicates the number of instances of the app that are running on the device.
- It indicates how frequently the app has been used within a period of time.
- It indicates the number of items in the app folder.
Explanation: Many of the apps on iOS devices are able to show an alert badge. An alert badge is displayed as a small icon over an app that contains a number that indicates the number of alerts from the app.
-
What represents apps in the Windows Phone interface?
- buttons
- icons
- tiles
- widgets
Explanation: The Windows Phone OS uses tiles to represent apps. Tiles are rectangles that can display active content. When tapped, they open the associated app. Tiles can be resized to unclutter screens and to reflect the relative importance of the app.
-
What is the name of the Windows Phone 8.1 digital, or virtual, assistant?
- Bing
- Cortana
- Nova Launcher
- Spotlight
Explanation: Siri is the well-known digital, or virtual, assistant that is available in iOS. Windows Phone also has a digitial assistant. It is called Cortana.
-
What is Wi-Fi calling?
- a method used to push apps to smartphones
- a convenient way to securely and digitally make payments with mobile devices
- a government emergency alert service for smartphones
- a way to make mobile phone calls over a wireless data network
- a method for sharing data between two mobile devices
Explanation: Wi-Fi calling is a way that a mobile phone can use a wireless data network to make phone calls as if it were connected to a cellular network. In cases where cell phone coverage is inadequate, calls can be placed from places that have open Wi-Fi networks.
-
What is a benefit of the WEA system?
- It can save lives by sending emergency text messages to mobile phones.
- It can simplify commerce by allowing payments to be made from a mobile phone.
- It is a method of securing a mobile device that has been lost or stolen.
- It allows a user to search for resources that are located near the current location.
Explanation: The Wireless Emergency Alerts (WEA) system is a way that government agencies can send emergency alerts in the form of text messages to wireless device users. The WEA system can save lives by rapidly spreading alerts about man-made and natural disasters to many people in a short period of time. WEA can also be used to spread AMBER alerts regarding abducted children.
-
What are two purposes of the passcode lock feature on mobile devices? (Choose two.)
- to help prevent theft of private information
- to prevent unauthorized use of the device
- to erase all personal data from the device
- to return the device to the default factory state
- to restore and re-synchronize the device
- to remotely lock the device if it is stolen
Explanation: The passcode lock feature on mobile devices helps prevent theft of private information and places the device into a power saving state. Personal data will not usually be erased from some mobile devices unless the number of failed passcode login attempts exceeds a threshold. Remote lock allows the device to be locked from a remote location. A factory reset returns the device to the original operation state when the device was first purchased. Various applications such as email or cloud storage can provide synchronization capabilities to be able to restore and re-synchronize information such as user data, contacts, and email on a mobile device.y other device features and actions.
-
Which two conditions must be met for mobile device security measures such as remote lock and remote wipe to function? (Choose two.)
- The device must be powered on.
- The device must be connected to a network.
- The passcode must be disabled.
- The GPS locator must be enabled.
- Sandboxing must be enabled.
Explanation: Successful mobile device remote security measures require the device to be powered on and connected to a network. The device passcode and GPS status do not affect the operation of remote security measures. Mobile devices run apps within a sandbox by default.
-
Which two location data sources can locator apps use to determine the position of a mobile device? (Choose two.)
- cellular towers
- WiFi hotspots
- the sandbox
- remote lock
- an app source
Explanation: In addition to GPS, mobile device locator apps can use cellular towers and WiFi hotspots to determine the position of a mobile device. The device sandbox, remote lock, or an app source (Play Store or iTunes) are other features and functions related to security and app downloading.
-
What are two potential user benefits of rooting or jailbreaking a mobile device? (Choose two.)
- The user interface can be extensively customized.
- The operating system can be fine-tuned to improve the speed of the device.
- The root directory of the device is blocked.
- The operation of the carrier cellular network may be affected.
- A custom OS may reduce sandboxing features.
Explanation: Rooting or jailbreaking a mobile device usually enables extensive customization of the user interface and can enable performance enhancement. The three incorrect options are all considered potential risks to the user, the device, and the network that may result from rooting or jailbreaking a mobile device.
-
Which statement is true about wireless connectivity on an Android mobile device?
- If the network SSID is not being broadcast, the device will not be able to connect to the network.
- When the device roams out of the range of any Wi-Fi networks, it can connect to the cellular data network if this feature is enabled.
- If a Wi-Fi network is secured with a password, the network must be manually configured on the device.
- The Android OS does not support wireless connectivity that uses WPA2 security.
Explanation: When joining a mobile device to a Wi-Fi network, it is always a good idea to ensure the network is secure using a protocol like WPA2. The user does not have to manually configure all of the settings to connect to a password-secured Wi-Fi network. The user will simply be prompted for the password the first time a connection is established. However, if the Wi-Fi network is not broadcasting an SSID, the device will need to be manually configured to connect to the network. If the device moves out of range of any known Wi-Fi networks, it will automatically switch over to use the cellular data network provided that the device has been pre-configured for this situation.
-
In the context of mobile devices, what does the term tethering involve?
- connecting a mobile device to another mobile device or computer to share a network connection
- connecting a mobile device to a hands-free headset
- connecting a mobile device to a 4G cellular network
- connecting a mobile device to a USB port on a computer in order to charge the mobile device
Explanation: Tethering allows a laptop or PC to use the Internet connection of a mobile device such as a cell phone, usually through a cellular data connection. This allows devices to connect to the Internet in locations where there is no Wi-Fi or cabled connection, but where there is still a cellular data connection.
-
Which statement is true about industry standards for cellular networks?
- Cell phones that use a single standard can often only be used in specific geographic areas.
- Cellular standards have made it more difficult and expensive to make calls to people that are on a different network.
- First generation cellular standards are mostly digital standards.
- Third generation cellular standards require a maximum of 1 Gb/s for devices moving slowly, such as when a user has a mobile device and is walking.
Explanation: Cellular standards are not uniformly adopted around the world, so different geographic areas may use different cellular standards. Although some devices have the ability to work using multiple cellular standards, most devices are designed to work with a single standard, such as CDMA. These device will only work in areas where the cellular network has been deployed using that particular standard.
-
What will allow someone to use a cell phone for entertainment without connecting to any networks?
- a hotspot
- Bluetooth
- Airplane Mode
- 4G
- WiMax
Explanation: Airplane mode turns off all cellular, Wi-Fi, and Bluetooth radios.
-
What technology enables a cell phone to be used as a hands-free device?
- Wi-Fi
- Bluetooth
- 4G
- Yosemite
Explanation: Bluetooth provides a way to connect wireless devices, such as headsets, to a nearby mobile device. Wi-Fi and 4G provide WAN access to voice and data. Yosemite is the code name applied to a recent version of Apple OS X.
-
A technician is configuring email on a mobile device. The user wants to be able to keep the original email on the server, organize it into folders, and synchronize the folders between the mobile device and the server. Which email protocol should the technician use?
- POP3
- IMAP
- MIME
- SMTP
Explanation: The IMAP protocol allows email data to be synchronized between a client and server. Changes made in one location, such as marking an email as read, are automatically applied to the other location. POP3 is also an email protocol. However, the data is not synchronized between the client and the server. SMTP is used for sending email, and is typically used in conjunction with the POP3 protocol. MIME is an email standard that is used to define attachment types, and allows extra content like pictures and documents to be attached to email messages.
-
What is the code name used for the OS X 10.10 operating system?
- Ubuntu
- Lollipop
- Aqua
- Yosemite
- Unity
Explanation: Many operating systems have a user-friendly code name for reference. The code names for recent releases of OS X are as follows:10.8 is Mountain Lion, 10.9 is Mavericks, and 10.10 is Yosemite.
-
What is a purpose of the boot manager program?
- It manages antivirus signature files, encryption keys, and certificates when a device boots.
- It automates the POST and checks the disk for bad sectors during a boot.
- It checks the validity of hardware and software on the device after a factory reset.
- It allows the user to select the OS to use to boot the device.
- It allows the user to determine which apps are automatically opened during the boot process.
Explanation: Many devices have multiple operating systems installed in different partitions. When a device boots, the boot manager asks the user to select the OS to use. The boot manager then directs the BIOS to the correct partition so that the device can continue to boot by using the selected OS.
-
What is the purpose of signature files used to secure mobile devices and operating systems?
- They contain a record of historical and pending firmware and software updates.
- They contain a list of all user passwords.
- They contain a log of digital certificates and encryption keys associated with the user.
- They contain sample code from known viruses and malware that is used by security software to identify malicious software.
Explanation: Antivirus and antimalware software compare the contents of a disk with sample virus and malware code included in signature files. If a comparison is found, the user can be notified and the virus can be isolated or removed.
-
A file called new_resume has the following file permissions: rw-r-x–x What two facts can be determined from these permissions? (Choose two.)
- The user has full access to the file.
- Members of the group have read and execute access to the file.
- Other people have read and execute access to the file.
- Group members are able to modify the file.
- The user is able to read and modify the file.
- Other people have no access to the file.
Explanation: Read, write, and execute permissions are assigned to each file. The permissions are listed in groups of three. The first group of three permissions references users, the second references group members, and the third references others. The first position of each of the three permissions is the R or read permission, the second is the W or write permission, and the third is the X or execute permission. If any position has a dash, the associated group does not have permission for that category. In this case, the user hasread and write access (rw-). Group members haveread and execute access (r-x). Other people haveexecute only access (–x).
-
What is the result of doing a factory reset on a mobile device?
- The operating system will be updated with the most recent updates and patches.
- All user data and settings will be deleted.
- The operating system will be deleted and all user data is transferred to the Cloud.
- A complete backup of the device is done and all viruses and malware are removed.
Explanation: After a factor reset, a mobile device is left in the same state that it was when it left the factory. The operating system software would not be altered but all user data, settings, and third party applications would be deleted. Backups should be done prior to a factory reset. Updates or patches to the operating system could be done before or after the factory reset.
-
What tool can be used on a mobile device to display available cellular networks, location of networks, and signal strength?
- Wi-Fi analyzer
- loopback adapter
- cell tower analyzer
- toner generator and probe
Explanation: A cell tower analyzer can be used on cellular networks to display available cellular networks, location of networks, and signal strength. A WiFi analyzer can be used to display information about WLAN networks.
-
An administrator is re-imaging a large number of Mac OS X machines. What built-in tool or command can be used to remotely boot the computers?
- mstsc
- Netboot
- Time Machine
- Finder
Explanation: Netboot is a built-in tool on the Mac OS that allows for remotely booting the computers. Finder is similar to the Windows File Explorer tool and is used to navigate the Mac OS file system. MSTSC is used to open the Windows Remote Desktop utility. Time Machine is an automatic backup utility built into the Mac OS.
-
What tool or command is used in the Mac OS X to navigate the file system?
- File Explorer
- Task Manager
- Finder
- mstsc
Explanation: Finder is similar to the Windows File Explorer tool and is used to navigate the Mac OS file system. The mstsc command is used to open the Windows Remote Desktop utility. The Task Manager tool on Windows allows a user to view all running applications.
-
What command is used to open a text editor in Unix-like systems?
- grep
- ifconfig
- ls
- vi
Explanation: The vi command is used to open the text editor; ls displays files within a directory; grep searches for strings of characters within a file; and ifconfig displays information about the network interface card.
-
Fill in the blank.
Both Linux and OS X devices have a service called cron that runs in the background and is responsible for executing scheduled tasks.