Last Updated on October 24, 2019 by Admin
CCNA 2 RSE 6.0 Pretest Exam Answers 2018 2019 100%
-
Which two components are configured via software in order for a PC to participate in a network environment? (Choose two.)
- MAC address
- IP address
- kernel
- shell
- subnet mask
-
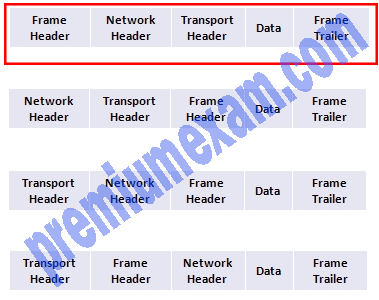
What is the correct order for PDU encapsulation?
-
To revert to a previous configuration, an administrator issues the command copy tftp startup-config on a router and enters the host address and file name when prompted. After the command is completed, why does the current configuration remain unchanged?
- The command should have been copy startup-config tftp.
- The configuration should have been copied to the running configuration instead.
- The configuration changes were copied into RAM and require a reboot to take effect.
- A TFTP server can only be used to restore the Cisco IOS, not the router configuration.
-
A small car dealership has a scanner that is attached to the PC of the sales manager. When salesmen need to scan a document, they place the document in the scanner and use their own PCs to control the scanner through software on the PC of the manager. After the document is scanned, they can attach it to an email or upload it into the sales software. What type of network model does this scenario describe?
- client/server
- packet-switched
- peer-to-peer
- centralized
- hierarchical
Explanation: In a peer-to-peer network, two or more computers are connected via a network and can share resources (in this case a scanner and files) without having a dedicated server. Every connected end device (known as a peer) can function as both a server and a client. Peer-to-peer networks decentralize the resources on a network. Instead of being stored on dedicated servers, data to be shared can be located on any connected device.
-
Which media access method requires that an end device send a notification across the media before sending data?
- CSMA/CA
- CSMA/CD
- deterministic
- token passing
Explanation: Using CSMA/CA as the media access control method, a device will examine the network media. If there is no carrier, the device sends a notification and, if no other device uses the media, it begins to send its data. This method differs from CSMA/CD, where a device will send data once it senses that the media is free, without sending a notification.
-
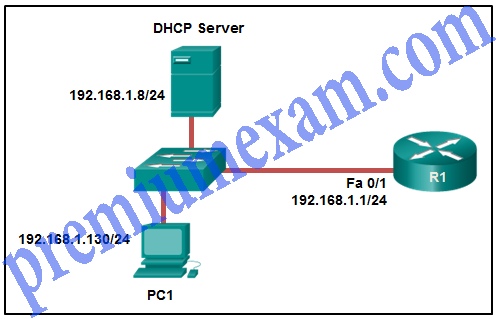
Refer to the exhibit. PC1 is configured to obtain a dynamic IP address from the DHCP server. PC1 has been shut down for two weeks. When PC1 boots and tries to request an available IP address, which destination IP address will PC1 place in the IP header?
- 192.168.1.1
- 192.168.1.8
- 192.168.1.255
- 255.255.255.255
Explanation: When a host boots and has been configured for dynamic IP addressing, the device tries to obtain a valid IP address. It sends a DHCPDISCOVER message. This is a broadcast message because the DHCP server address is unknown (by design). The destination IP address in the IP header is 255.255.255.255 and the destination MAC address is FF:FF:FF:FF:FF:FF.
-
Which statement is true about IPv6 addresses?
- Global unicast addresses are globally unique and can be routed through the Internet.
- Link-local addresses must be unique.
- A loopback address is represented by ::/128.
- Unique local addresses are used to communicate with other devices on the same link.
Explanation: Link-local addresses have relevance only on the local link. Routers will not forward packets that have link-local addresses as either the source or destination address.
The IPv6 loopback address is ::1/128.
Unique local addresses are similar to IPv4 private addresses. There is no broadcast address in the IPv6 protocol.
-
Refer to the exhibit. Which IP addressing scheme should be changed?
- Site 1
- Site 2
- Site 3
- Site 4
Explanation: Site 2 should have designed the 192.168.2.0/25 network for the 70 hosts. Then the 192.168.2.128/26 network could be used for the 40 hosts, and the 192.168.2.192/27 network could be used for the 15 hosts. The other sites are all valid including Site 4 where the bottom of the addressing range was used for the largest number of hosts.
-
What is the most effective way to mitigate worm and virus attacks?
- Secure all Layer 2 devices.
- Ensure that users change their passwords often.
- Deploy packet filtering firewalls at the network edge.
- Install security updates to patch vulnerable systems.
Explanation: Installing the most recent security updates from the operating system vendor on all vulnerable systems is the most effective way to mitigate a worm and virus attacks.
-
A particular website does not appear to be responding on a Windows 7 computer. What command could the technician use to show any cached DNS entries for this web page?
- ipconfig /all
- arp -a
- ipconfig /displaydns
- nslookup
-
Refer to the exhibit. A network administrator is configuring access control to switch SW1. If the administrator uses Telnet to connect to the switch, which password is needed to access user EXEC mode?
- letmein
- secretin
- lineconin
- linevtyin
Explanation: Telnet accesses a network device through the virtual interface configured with the line VTY command. The password configured under this is required to access the user EXEC mode. The password configured under the line console 0 command is required to gain entry through the console port, and the enable and enable secret passwords are used to allow entry into the privileged EXEC mode.
-
In performing a protocol analysis of a network, when should traffic be captured to ensure the most accurate representation of the different traffic types on the network?
- during software upgrades
- during times of moderate network use
- during hours of peak network use
- during weekends and holidays when network use is light
Explanation: To capture traffic that accurately represents all protocols that are running on a network, protocol analysis should take place during times of peak network use.
-
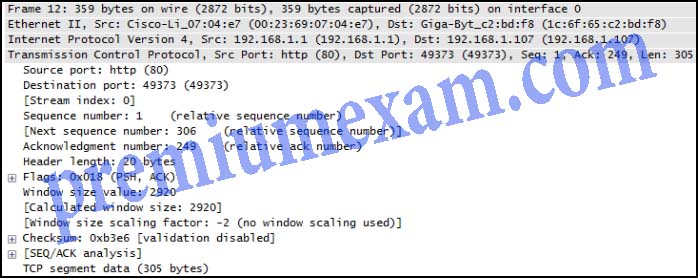
Refer to the exhibit. A TCP segment from a server has been captured by Wireshark, which is running on a host. What acknowledgement number will the host return for the TCP segment that has been received?
- 2
- 21
- 250
- 306
- 2921
Explanation: Because the starting sequence number is 1, and the length of the segment is 305 bytes, the receiving host should return an acknowledgement with an ACK of 306.
-
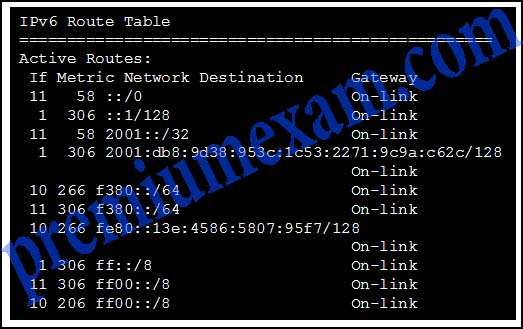
Refer to the exhibit. What is the link-local IPv6 address of the local computer shown based on the output of the netstat -r command?
- ::1/128
- 2001::/32
- 2001:db8:9d38:953c:1c53:2271:9c9a:c62c/128
- fe80::/64
- fe80::13e:4586:5807:95f7/128
Explanation: IPv6 interfaces commonly have two addresses assigned: a link-local address and a global unicast address. Addresses for a link-local address can have hexadecimal numbers in the first hextet ranging from FE80 to FEBF. Global unicast numbers must have the first 3 bits be 001 in the first hextet. The IPv6 addresses that start with 2001 are examples of global unicast addresses.
-
A network administrator is checking the system logs and notices unusual connectivity tests to multiple well-known ports on a server. What kind of potential network attack could this indicate?
- access
- reconnaissance
- denial of service
- information theft
Explanation: A reconnaissance attack is the unauthorized discovery and mapping of systems, services, or vulnerabilities. One of the most common reconnaissance attacks is performed by using utilities that automatically discover hosts on the networks and determine which ports are currently listening for connections.
-
Which technology provides a solution to IPv4 address depletion by allowing multiple devices to share one public IP address?
- ARP
- DNS
- PAT
- SMB
- DHCP
- HTTP
Explanation:
Network Address Translation (NAT) is a technology implemented within IPv4 networks. One application of NAT is to use a few public IP addresses to be shared by many internal network hosts which use private IP addresses. NAT removes the need for public addresses for every internal host. It therefore provides a solution to slow down the IPv4 address depletion.
-
What happens when part of an Internet television transmission is not delivered to the destination?
- A delivery failure message is sent to the source host.
- The part of the television transmission that was lost is re-sent.
- The entire transmission is re-sent.
- The transmission continues without the missing portion.
Explanation: Most streaming services, such as Internet television, use UDP as the transport layer protocol. These transmissions can tolerate some transmission failures, and no failure messages or retransmissions are required. Such control measures would create noticeable disruption to the flow of data.
-
Which three IP addresses are public? (Choose three.)
- 10.1.1.1
- 128.107.0.7
- 192.31.7.10
- 172.16.4.4
- 192.168.5.5
- 64.104.7.7
Explanation: The RFC 1918-compliant private addresses are:
Class A: 10.0.0.0 to 10.255.255.255
Class B: 172.16.0.0 to 172.31.255.255
Class C: 192.168.0.0 to 192.168.255.255
-
A host is accessing an FTP server on a remote network. Which three functions are performed by intermediary network devices during this conversation? (Choose three.)
- regenerating data signals
- acting as a client or a server
- providing a channel over which messages travel
- applying security settings to control the flow of data
- notifying other devices when errors occur
- serving as the source or destination of the messages
Explanation: Intermediary devices provide management of data transmission by keeping track of data pathways, finding alternate pathways when failures occur and notifying other devices, and applying security and priority policies. As they receive data signals, intermediary devices “clean” and retransmit them. Intermediary devices do not create data signals, but rather they utilize network media to interconnect end users.
-
Which IP address is a valid network address?
- 172.16.4.32/27
- 172.16.4.79/28
- 172.16.4.255/22
- 172.16.5.255/23
Explanation: The network address for the device that has the IP address of 172.16.4.255/22 is 172.16.4.0/22. The first valid host address is 172.16.4.1; the last valid host address is 172.16.7.254. The IP address of 172.16.4.32/27 is a network address. Both 172.16.4.79/28 and 172.16.5.255/23 are broadcast addresses.
-
What is the range of host IP addresses for the subnet 172.16.1.32/28?
- 172.16.1.33 – 172.16.1.38
- 172.16.1.33 – 172.16.1.46
- 172.16.1.33 – 172.16.1.62
- 172.16.1.32 – 172.16.1.39
- 172.16.1.32 – 172.16.1.47
Explanation: A /28 subnet has four bits for host addressing. Four bits give sixteen addresses in this subnet, from 172.16.1.32 to 172.16.1.47. However, 172.16.1.32 is the network address and 172.16.1.47 is the broadcast address. Therefore, the valid host range in this subnet is 172.16.1.33 – 172.16.1.46.
-
An organization has received the IPv6 network prefix of 2001:db8:1234::/52 from their ISP. How many subnets can be created from this prefix without borrowing bits from the interface ID?
- 1024
- 4096
- 8192
- 65536
Explanation: The IPv6 address space reserves the last 64 bits for the interface ID. Therefore, a prefix of /52 will have 12 bits remaining for subnetting if needed. 12 bits will yield 4096 subnets.
-
Match the application protocols to the correct transport protocols.
-
Open the PT Activity. Perform the tasks in the activity instructions and then answer the question.
What is the secret keyword that is displayed on the web page?
- router
- switch
- frame
- packet
- cisco
-
Open the PT Activity. Perform the tasks in the activity instructions and then answer the question.
Which IPv6 address is assigned to the Serial0/0/0 interface on RT2?
- 2001:db8:abc:1::1
- 2001:db8:abc:5::1
- 2001:db8:abc:5::2
- 2001:db8:abc:10::15
Explanation: The result of the tracert command is as follows:
1 11 ms 0 ms 0 ms 2001:db8:abc:1::1
2 4 ms 0 ms 1 ms 2001:db8:abc:5::1
3 11 ms 14 ms 2 ms 2001:db8:abc:10::15
It crosses two routers, so the second line is the IP address for the RT2 serial interface0/0/0.
-
Which statement describes a route that has been learned dynamically?
- It is automatically updated and maintained by routing protocols.
- It is unaffected by changes in the topology of the network.
- It has an administrative distance of 1.
- It is identified by the prefix C in the routing table.
-
What is the purpose of a routing protocol?
- It is used to build and maintain ARP tables.
- It provides a method for segmenting and reassembling data packets.
- It allows an administrator to devise an addressing scheme for the network.
- It allows a router to share information about known networks with other routers.
- It provides a procedure for encoding and decoding data into bits for packet forwarding.
-
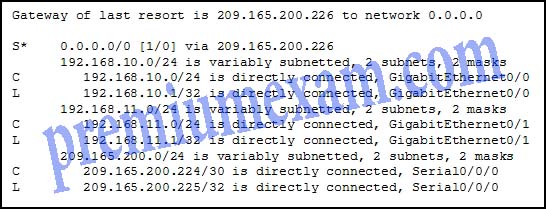
Refer to the exhibit. What will the router do with a packet that has a destination IP address of 192.168.12.227?
- Drop the packet.
- Send the packet out the Serial0/0/0 interface.
- Send the packet out the GigabitEthernet0/0 interface.
- Send the packet out the GigabitEthernet0/1 interface.
Explanation: After a router determines the destination network by ANDing the destination IP address with the subnet mask, the router examines the routing table for the resulting destination network number. When a match is found, the packet is sent to the interface associated with the network number. When no routing table entry is found for the particular network, the default gateway or gateway of last resort (if configured or known) is used. If there is no gateway of last resort, the packet is dropped. In this instance, the 192.168.12.224 network is not found in the routing table and the router uses the gateway of last resort. The gateway of last resort is the IP address of 209.165.200.226. The router knows this is an IP address that is associated with the 209.165.200.224 network. The router then proceeds to transmit the packet out the Serial0/0/0 interface, or the interface that is associated with 209.165.200.224.
-
Which type of static route is configured with a greater administrative distance to provide a backup route to a route learned from a dynamic routing protocol?
- standard static route
- floating static route
- default static route
- summary static route
Explanation: There are four basic types of static routes. Floating static routes are backup routes that are placed into the routing table if a primary route is lost. A summary static route aggregates several routes into one, reducing the of the routing table. Standard static routes are manually entered routes into the routing table. Default static routes create a gateway of last resort.
-
Which two factors are important when deciding which interior gateway routing protocol to use? (Choose two.)
- scalability
- ISP selection
- speed of convergence
- the autonomous system that is used
- campus backbone architecture
Explanation: There are several factors to consider when selecting a routing protocol to implement. Two of them are scalability and speed of convergence. The other options are irrelevant.
-
Which information does a switch use to populate the MAC address table?
- the destination MAC address and the incoming port
- the destination MAC address and the outgoing port
- the source and destination MAC addresses and the incoming port
- the source and destination MAC addresses and the outgoing port
- the source MAC address and the incoming port
- the source MAC address and the outgoing port
Explanation: To maintain the MAC address table, the switch uses the source MAC address of the incoming packets and the port that the packets enter. The destination address is used to select the outgoing port.
-
Employees of a company connect their wireless laptop computers to the enterprise LAN via wireless access points that are cabled to the Ethernet ports of switches. At which layer of the three-layer hierarchical network design model do these switches operate?
- distribution
- data link
- physical
- access
- core
-
Which advantage does the store-and-forward switching method have compared with the cut-through switching method?
- collision detecting
- frame error checking
- faster frame forwarding
- frame forwarding using IPv4 Layer 3 and 4 information
Explanation: A switch using the store-and-forward switching method performs an error check on an incoming frame by comparing the FCS value against its own FCS calculations after the entire frame is received. In comparison, a switch using the cut-through switching method makes quick forwarding decisions and starts the forwarding process without waiting for the entire frame to be received. Thus a switch using cut-through switching may send invalid frames to the network. The performance of store-and-forward switching is slower compared to cut-through switching performance. Collision detection is monitored by the sending device. Store-and-forward switching does not use IPv4 Layer 3 and 4 information for its forwarding decisions.
-
Which type of traffic is designed for a native VLAN?
- user-generated
- tagged
- untagged
- management
Explanation: A native VLAN carries untagged traffic, which is traffic that does not come from a VLAN. A data VLAN carries user-generated traffic. A management VLAN carries management traffic.
-
A network administrator is configuring a new Cisco switch for remote management access. Which three items must be configured on the switch for the task? (Choose three.)
- IP address
- VTP domain
- vty lines
- default VLAN
- default gateway
- loopback address
Explanation: To enable the remote management access, the Cisco switch must be configured with an IP address and a default gateway. In addition, vty lines must configured to enable either Telnet or SSH connections. A loopback address, default VLAN, and VTP domain configurations are not necessary for the purpose of remote switch management.
-
What is the reason why the DHCPREQUEST message is sent as a broadcast during the DHCPv4 process?
- to notify other DHCP servers on the subnet that the IP address was leased
- to notify other hosts not to request the same IP address
- for hosts on other subnets to receive the information
- for routers to fill their routing tables with this new information
Explanation: The DHCPREQUEST message is broadcast to inform other DHCP servers that an IP address has been leased.
-
What is the most likely scenario in which the WAN interface of a router would be configured as a DHCP client to be assigned a dynamic IP address from an ISP?
- There is a web server for public access on the LAN that is attached to the router.
- The router is also the gateway for a LAN.
- It is a SOHO or home broadband router.
- The router is configured as a DHCP server.
Explanation: SOHO and home broadband routers are typically set to acquire an IPv4 address automatically from the ISP. The IP address that is assigned is typically a dynamic address to reduce the cost, but a static IP address is possible with more cost. However, if the router is assigned a dynamic IP address, DNS issues will result in the web server behind the router not being easily accessible to the public. Routers are typically also gateways for LANs, but this has no bearing on whether the router is configured as a DHCP client on its WAN link or not. Likewise, a router can be configured to be a DHCP client in order to obtain an IP address from the ISP, but at the same time, it can be configured as a DHCP server to serve the IP addressing for the devices on its LAN.
-
Which type of traffic would most likely have problems when passing through a NAT device?
- Telnet
- IPsec
- HTTP
- ICMP
- DNS
Explanation: IPsec protocols often perform integrity checks on packets when they are received to ensure that they have not been changed in transit from the source to the destination. Because NAT changes values in the headers as packets pass from inside to outside, these integrity checks can fail, thus causing the packets to be dropped at the destination.
-
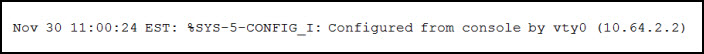
Refer to the exhibit. An administrator is examining the message in a syslog server. What can be determined from the message?
- This is a notification message for a normal but significant condition.
- This is an alert message for which immediate action is needed.
- This is an error message for which warning conditions exist.
- This is an error message that indicates the system is unusable.
Explanation: The number 5 in the message output %SYS-5-CONFIG_I, indicated this is a notification level message that is for normal but significant conditions.
-
Compared with dynamic routes, what are two advantages of using static routes on a router? (Choose two.)
- They improve network security.
- They use fewer router resources.
- They improve the efficiency of discovering neighboring networks.
- They take less time to converge when the network topology changes.
- They automatically switch the path to the destination network when the topology changes.
Explanation: Static routes are manually configured on a router. Static routes are not automatically updated and must be manually reconfigured if the network topology changes. Thus static routing improves network security because it does not make route updates among neighboring routers. Static routes also improve resource efficiency by using less bandwidth, and no CPU cycles are used to calculate and communicate routes.