Last Updated on October 28, 2019 by Admin
ITN Final Exam Form C Online
ITN -- Final Exam Form C
Quiz-summary
0 of 54 questions completed
Questions:
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
- 41
- 42
- 43
- 44
- 45
- 46
- 47
- 48
- 49
- 50
- 51
- 52
- 53
- 54
Information
ITN — Final Exam Form C
You have already completed the quiz before. Hence you can not start it again.
Quiz is loading...
You must sign in or sign up to start the quiz.
You have to finish following quiz, to start this quiz:
Results
0 of 54 questions answered correctly
Your time:
Time has elapsed
You have reached 0 of 0 points, (0)
| Average score |
|
| Your score |
|
Categories
- Not categorized 0%
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
- 41
- 42
- 43
- 44
- 45
- 46
- 47
- 48
- 49
- 50
- 51
- 52
- 53
- 54
- Answered
- Review
-
Question 1 of 54
1. Question
1 pointsA company is expanding its business to other countries. All branch offices must remain connected to corporate headquarters at all times. Which network technology is required to support this requirement?Correct
Incorrect
A local-area network (LAN) normally connects end users and network resources over a limited geographic area using Ethernet technology. A wireless LAN (WLAN) serves the same purpose as a LAN but uses wireless technologies. A metropolitan-area network (MAN) spans a larger geographic area such as a city, and a wide-area network (WAN) connects networks together over a large geographic area. WANs can span cities, countries, or the globe.
Hint
A local-area network (LAN) normally connects end users and network resources over a limited geographic area using Ethernet technology. A wireless LAN (WLAN) serves the same purpose as a LAN but uses wireless technologies. A metropolitan-area network (MAN) spans a larger geographic area such as a city, and a wide-area network (WAN) connects networks together over a large geographic area. WANs can span cities, countries, or the globe.
-
Question 2 of 54
2. Question
1 pointsA home user is looking for an ISP connection that provides high speed digital transmission over regular phone lines. What ISP connection type should be used?Correct
Incorrect
-
Question 3 of 54
3. Question
1 pointsHow does quality of service help a network support a wide range of applications and services?Correct
Incorrect
Quality of service (QoS), is a vital component of the architecture of a network. With QoS, network administrators can provide applications with predictable and measurable service guarantees through mechanisms that manage congested network traffic.Hint
Quality of service (QoS), is a vital component of the architecture of a network. With QoS, network administrators can provide applications with predictable and measurable service guarantees through mechanisms that manage congested network traffic. -
Question 4 of 54
4. Question
1 pointsOn which switch interface would an administrator configure an IP address so that the switch can be managed remotely?Correct
Incorrect
Interface VLAN 1 is a virtual interface on a switch, called SVI (switch virtual interface). Configuring an IP address on the default SVI, interface VLAN 1, will allow a switch to be accessed remotely. The VTY line must also be configured to allow remote access, but an IP address cannot be configured on this line.Hint
Interface VLAN 1 is a virtual interface on a switch, called SVI (switch virtual interface). Configuring an IP address on the default SVI, interface VLAN 1, will allow a switch to be accessed remotely. The VTY line must also be configured to allow remote access, but an IP address cannot be configured on this line. -
Question 5 of 54
5. Question
1 pointsAfter making configuration changes on a Cisco switch, a network administrator issues a copy running-config startup-config command. What is the result of issuing this command?Correct
Incorrect
With the copy running-config startup-config command, the content of the current operating configuration replaces the startup configuration file stored in NVRAM. The configuration file saved in NVRAM will be loaded when the device is restarted.Hint
With the copy running-config startup-config command, the content of the current operating configuration replaces the startup configuration file stored in NVRAM. The configuration file saved in NVRAM will be loaded when the device is restarted. -
Question 6 of 54
6. Question
1 pointsRefer to the exhibit. A network administrator is configuring access control to switch SW1. If the administrator has already logged into a Telnet session on the switch, which password is needed to access privileged EXEC mode?
Correct
Incorrect
Telnet accesses a network device through the virtual interface configured with the line VTY command. The password configured under this is required to access the user EXEC mode. The password configured under the line console 0 command is required to gain entry through the console port, and the enable and enable secret passwords are used to allow entry into the privileged EXEC mode.Hint
Telnet accesses a network device through the virtual interface configured with the line VTY command. The password configured under this is required to access the user EXEC mode. The password configured under the line console 0 command is required to gain entry through the console port, and the enable and enable secret passwords are used to allow entry into the privileged EXEC mode. -
Question 7 of 54
7. Question
1 pointsWhich connection provides a secure CLI session with encryption to a Cisco switch?Correct
Incorrect
A CLI session using Secure Shell (SSH) provides enhanced security because SSH supports strong passwords and encryption during the transport of session data. The other methods support authentication but not encryption.Hint
A CLI session using Secure Shell (SSH) provides enhanced security because SSH supports strong passwords and encryption during the transport of session data. The other methods support authentication but not encryption. -
Question 8 of 54
8. Question
1 pointsA network technician is attempting to configure an interface by entering the following command: SanJose(config)# ip address 192.168.2.1 255.255.255.0. The command is rejected by the device. What is the reason for this?Correct
Incorrect
The wrong mode of operation is being used. The CLI prompt indicates that the mode of operation is global configuration. IP addresses must be configured from interface configuration mode, as indicated by the SanJose(config-if)# prompt.Hint
The wrong mode of operation is being used. The CLI prompt indicates that the mode of operation is global configuration. IP addresses must be configured from interface configuration mode, as indicated by the SanJose(config-if)# prompt. -
Question 9 of 54
9. Question
1 pointsWhat function does pressing the Tab key have when entering a command in IOS?Correct
Incorrect
Pressing the Tab key after a command has been partially typed will cause the IOS to complete the rest of the command.Hint
Pressing the Tab key after a command has been partially typed will cause the IOS to complete the rest of the command. -
Question 10 of 54
10. Question
1 pointsWhat is a characteristic of multicast messages?Correct
Incorrect
Multicast is a one-to-many type of communication. Multicast messages are addressed to a specific multicast group.Hint
Multicast is a one-to-many type of communication. Multicast messages are addressed to a specific multicast group. -
Question 11 of 54
11. Question
1 pointsWhat protocol is responsible for controlling the size of segments and the rate at which segments are exchanged between a web client and a web server?Correct
Incorrect
TCP is a Layer 4 protocol of the OSI model. TCP has several responsibilities in the network communication process. It divides large messages into smaller segments which are more efficient to send across the network. It also controls the size and rate of segments exchanged between clients and servers.Hint
TCP is a Layer 4 protocol of the OSI model. TCP has several responsibilities in the network communication process. It divides large messages into smaller segments which are more efficient to send across the network. It also controls the size and rate of segments exchanged between clients and servers. -
Question 12 of 54
12. Question
1 pointsWhat layer is responsible for routing messages through an internetwork in the TCP/IP model?Correct
Incorrect
The TCP/IP model consists of four layers: application, transport, internet, and network access. Of these four layers, it is the internet layer that is responsible for routing messages. The session layer is not part of the TCP/IP model but is rather part of the OSI model.Hint
The TCP/IP model consists of four layers: application, transport, internet, and network access. Of these four layers, it is the internet layer that is responsible for routing messages. The session layer is not part of the TCP/IP model but is rather part of the OSI model. -
Question 13 of 54
13. Question
1 pointsWhich statement accurately describes a TCP/IP encapsulation process when a PC is sending data to the network?Correct
Incorrect
When the data is traveling from the PC to the network, the transport layer sends segments to the internet layer. The internet layer sends packets to the network access layer, which creates frames and then converts the frames to bits. The bits are released to the network media.Hint
When the data is traveling from the PC to the network, the transport layer sends segments to the internet layer. The internet layer sends packets to the network access layer, which creates frames and then converts the frames to bits. The bits are released to the network media. -
Question 14 of 54
14. Question
1 pointsWhat unique address is embedded in an Ethernet NIC and used for communication on an Ethernet network?Correct
Incorrect
The MAC address is a 48-bit address that is burned into every Ethernet NIC. Each MAC address is unique throughout the world.Hint
The MAC address is a 48-bit address that is burned into every Ethernet NIC. Each MAC address is unique throughout the world. -
Question 15 of 54
15. Question
1 pointsA network administrator is troubleshooting connectivity issues on a server. Using a tester, the administrator notices that the signals generated by the server NIC are distorted and not usable. In which layer of the OSI model is the error categorized?Correct
Incorrect
The NIC has responsibilities in both Layer 1 and Layer 2. The NIC encodes the frame as a series of signals that are transmitted onto the local media. This is the responsibility of the physical layer of the OSI model. The signal could be in the form of electrical, optical, or radio waves.Hint
The NIC has responsibilities in both Layer 1 and Layer 2. The NIC encodes the frame as a series of signals that are transmitted onto the local media. This is the responsibility of the physical layer of the OSI model. The signal could be in the form of electrical, optical, or radio waves. -
Question 16 of 54
16. Question
3 pointsA network administrator is measuring the transfer of bits across the company backbone for a mission critical financial application. The administrator notices that the network throughput appears lower than the bandwidth expected. Which three factors could influence the differences in throughput? (Choose three.)Correct
Incorrect
Throughput usually does not match the specified bandwidth of physical links due to multiple factors. These factors include, the amount of traffic, type of traffic, and latency created by the network devices the data has to cross.Hint
Throughput usually does not match the specified bandwidth of physical links due to multiple factors. These factors include, the amount of traffic, type of traffic, and latency created by the network devices the data has to cross. -
Question 17 of 54
17. Question
1 pointsWhich procedure is used to reduce the effect of crosstalk in copper cables?Correct
Incorrect
In copper cables, crosstalk is a disturbance caused by the electric or magnetic fields of a signal on one wire interfering with the signal in an adjacent wire. Twisting opposing circuit wire pairs together can effectively cancel the crosstalk. The other options are effective measures to counter the negative effects of EMI and RFI, but not crosstalk.Hint
In copper cables, crosstalk is a disturbance caused by the electric or magnetic fields of a signal on one wire interfering with the signal in an adjacent wire. Twisting opposing circuit wire pairs together can effectively cancel the crosstalk. The other options are effective measures to counter the negative effects of EMI and RFI, but not crosstalk. -
Question 18 of 54
18. Question
1 pointsWhat is a characteristic of the LLC sublayer?Correct
Incorrect
The Logical Link Control (LLC) defines the software processes that provide services to the network layer protocols. The information is placed by LLC in the frame and identifies which network layer protocol is being used for the frame. This information allows multiple Layer 3 protocols, such as IPv4 and IPv6, to utilize the same network interface and media.Hint
The Logical Link Control (LLC) defines the software processes that provide services to the network layer protocols. The information is placed by LLC in the frame and identifies which network layer protocol is being used for the frame. This information allows multiple Layer 3 protocols, such as IPv4 and IPv6, to utilize the same network interface and media. -
Question 19 of 54
19. Question
1 pointsWhat method is used to manage contention-based access on a wireless network?Correct
Incorrect
Carrier sense multiple access with collision avoidance (CSMA/CA) is used with wireless networking technology to mediate media contention. Carrier sense multiple access with collision detection (CSMA/CD) is used with wired Ethernet technology to mediate media contention. Priority ordering and token passing are not used (or not a method) for media access control.Hint
Carrier sense multiple access with collision avoidance (CSMA/CA) is used with wireless networking technology to mediate media contention. Carrier sense multiple access with collision detection (CSMA/CD) is used with wired Ethernet technology to mediate media contention. Priority ordering and token passing are not used (or not a method) for media access control. -
Question 20 of 54
20. Question
1 pointsDuring the encapsulation process, what occurs at the data link layer for a PC connected to an Ethernet network?Correct
Incorrect
The Ethernet frame includes the source and destination physical address. The trailer includes a CRC value in the Frame Check Sequence field to allow the receiving device to determine if the frame has been changed (has errors) during the transmission.Hint
The Ethernet frame includes the source and destination physical address. The trailer includes a CRC value in the Frame Check Sequence field to allow the receiving device to determine if the frame has been changed (has errors) during the transmission. -
Question 21 of 54
21. Question
3 pointsWhat are the three primary functions provided by Layer 2 data encapsulation? (Choose three.)Correct
Incorrect
Through the framing process, delimiters are used to identify the start and end of the sequence of bits that make up a frame. Data link layer addressing is added to enable a frame to be delivered to a destination node. A cyclic redundancy check (CRC) field is calculated on every bit and added to the frame. If the CRC value contained in the arriving frame is the same as the one the receiving node creates, the frame will be processed.Hint
Through the framing process, delimiters are used to identify the start and end of the sequence of bits that make up a frame. Data link layer addressing is added to enable a frame to be delivered to a destination node. A cyclic redundancy check (CRC) field is calculated on every bit and added to the frame. If the CRC value contained in the arriving frame is the same as the one the receiving node creates, the frame will be processed. -
Question 22 of 54
22. Question
2 pointsWhat are two characteristics of Ethernet MAC addresses? (Choose two.)Correct
Incorrect
An Ethernet MAC address is a 48-bit binary value expressed as 12 hexadecimal digits. MAC addresses must be globally unique by design. MAC addresses are in flat structure and thus they are not routable on the Internet. Serial interfaces do not use MAC addresses.Hint
An Ethernet MAC address is a 48-bit binary value expressed as 12 hexadecimal digits. MAC addresses must be globally unique by design. MAC addresses are in flat structure and thus they are not routable on the Internet. Serial interfaces do not use MAC addresses. -
Question 23 of 54
23. Question
1 pointsIf a device receives an Ethernet frame of 60 bytes, what will it do?Correct
Incorrect
Ethernet standards define the minimum frame size as 64 bytes. A frame less than 64 bytes is considered a “collision fragment” or “runt frame” and is automatically discarded by receiving devices.Hint
Ethernet standards define the minimum frame size as 64 bytes. A frame less than 64 bytes is considered a “collision fragment” or “runt frame” and is automatically discarded by receiving devices. -
Question 24 of 54
24. Question
1 pointsWhat will a host on an Ethernet network do if it receives a frame with a destination MAC address that does not match its own MAC address?Correct
Incorrect
In an Ethernet network, each NIC in the network checks every arriving frame to see if the destination MAC address in the frame matches its own MAC address. If there is no match, the device discards the frame. If there is a match, the NIC passes the frame up to the next OSI layer.Hint
In an Ethernet network, each NIC in the network checks every arriving frame to see if the destination MAC address in the frame matches its own MAC address. If there is no match, the device discards the frame. If there is a match, the NIC passes the frame up to the next OSI layer. -
Question 25 of 54
25. Question
2 pointsUnder which two circumstances will a switch flood a frame out of every port except the port that the frame was received on? (Choose two.)Correct
Incorrect
A switch will flood a frame out of every port, except the one that the frame was received from, under two circumstances. Either the frame has the broadcast address as the destination address, or the destination address is unknown to the switch.Hint
A switch will flood a frame out of every port, except the one that the frame was received from, under two circumstances. Either the frame has the broadcast address as the destination address, or the destination address is unknown to the switch. -
Question 26 of 54
26. Question
1 pointsWhich switching method has the lowest level of latency?Correct
Incorrect
Fast-forward switching begins to forward a frame after reading the destination MAC address, resulting in the lowest latency. Fragment-free reads the first 64 bytes before forwarding. Store-and-forward has the highest latency because it reads the entire frame before beginning to forward it. Both fragment-free and fast-forward are types of cut-through switching.Hint
Fast-forward switching begins to forward a frame after reading the destination MAC address, resulting in the lowest latency. Fragment-free reads the first 64 bytes before forwarding. Store-and-forward has the highest latency because it reads the entire frame before beginning to forward it. Both fragment-free and fast-forward are types of cut-through switching. -
Question 27 of 54
27. Question
2 pointsWhich two commands can be used on a Windows host to display the routing table? (Choose two.)Correct
Incorrect
On a Windows host, the route print or netstat -r commands can be used to display the host routing table. Both commands generate the same output. On a router, the show ip route command is used to display the routing table. The netstat –s command is used to display per-protocol statistics. The tracert command is used to display the path that a packet travels to its destination.Hint
On a Windows host, the route print or netstat -r commands can be used to display the host routing table. Both commands generate the same output. On a router, the show ip route command is used to display the routing table. The netstat –s command is used to display per-protocol statistics. The tracert command is used to display the path that a packet travels to its destination. -
Question 28 of 54
28. Question
2 pointsWhich two functions are primary functions of a router? (Choose two.)Correct
Incorrect
-
Question 29 of 54
29. Question
3 pointsWhat are the three ranges of IP addresses that are reserved for internal private use? (Choose three.)Correct
Incorrect
The private IP address blocks that are used inside companies are as follows:
- 10.0.0.0 /8 (any address that starts with 10 in the first octet)
- 172.16.0.0 /12 (any address that starts with 172.16 in the first two octets through 172.31.255.255)
- 192.168.0.0 /16 (any address that starts with 192.168 in the first two octets)
Hint
The private IP address blocks that are used inside companies are as follows:
- 10.0.0.0 /8 (any address that starts with 10 in the first octet)
- 172.16.0.0 /12 (any address that starts with 172.16 in the first two octets through 172.31.255.255)
- 192.168.0.0 /16 (any address that starts with 192.168 in the first two octets)
-
Question 30 of 54
30. Question
1 pointsWhat purpose does NAT64 serve in IPv6?Correct
Incorrect
NAT64 is typically used in IPv6 when networks are being transitioned from IPv4 to IPv6. It allows the IPv6 networks to connect to IPv4 networks (such as the Internet), and works by translating the IPv6 packets into IPv4 packets.Hint
NAT64 is typically used in IPv6 when networks are being transitioned from IPv4 to IPv6. It allows the IPv6 networks to connect to IPv4 networks (such as the Internet), and works by translating the IPv6 packets into IPv4 packets. -
Question 31 of 54
31. Question
1 pointsWhat is the binary representation of 0xCA?Correct
Incorrect
When converted, CA in hex is equivalent to 11011010 in binary. One way to do the conversion is one nibble at a time, C = 1100 and A = 1010. Combine the two nibbles gives 11001010.Hint
When converted, CA in hex is equivalent to 11011010 in binary. One way to do the conversion is one nibble at a time, C = 1100 and A = 1010. Combine the two nibbles gives 11001010. -
Question 32 of 54
32. Question
1 pointsAt a minimum, which address is required on IPv6-enabled interfaces?Correct
Incorrect
All IPv6 enabled interfaces must at minimum have a link-local address. Other IPv6 addresses can be assigned to the interface as required.Hint
All IPv6 enabled interfaces must at minimum have a link-local address. Other IPv6 addresses can be assigned to the interface as required. -
Question 33 of 54
33. Question
1 pointsWhich service provides dynamic global IPv6 addressing to end devices without using a server that keeps a record of available IPv6 addresses?Correct
Incorrect
Using stateless address autoconfiguration (SLAAC), a PC can solicit a router and receive the prefix length of the network. From this information the PC can then create its own IPv6 global unicast address.Hint
Using stateless address autoconfiguration (SLAAC), a PC can solicit a router and receive the prefix length of the network. From this information the PC can then create its own IPv6 global unicast address. -
Question 34 of 54
34. Question
1 pointsWhat is the purpose of the command ping ::1?Correct
Incorrect
The address ::1 is an IPv6 loopback address. Using the command ping ::1 tests the internal IP stack to ensure that it is configured and functioning correctly. It does not test reachability to any external device, nor does it confirm that IPv6 addresses are properly configured on the host.
Hint
The address ::1 is an IPv6 loopback address. Using the command ping ::1 tests the internal IP stack to ensure that it is configured and functioning correctly. It does not test reachability to any external device, nor does it confirm that IPv6 addresses are properly configured on the host.
-
Question 35 of 54
35. Question
1 pointsHow many usable IP addresses are available on the 192.168.1.0/27 network?
Correct
Incorrect
A /27 mask is the same as 255.255.255.224. This leaves 5 host bits. With 5 host bits, 32 IP addresses are possible, but one address represents the subnet number and one address represents the broadcast address. Thus, 30 addresses can then be used to assign to network devices.Hint
A /27 mask is the same as 255.255.255.224. This leaves 5 host bits. With 5 host bits, 32 IP addresses are possible, but one address represents the subnet number and one address represents the broadcast address. Thus, 30 addresses can then be used to assign to network devices. -
Question 36 of 54
36. Question
1 pointsWhich subnet would include the address 192.168.1.96 as a usable host address?Correct
Incorrect
For the subnet of 192.168.1.64/26, there are 6 bits for host addresses, yielding 64 possible addresses. However, the first and last subnets are the network and broadcast addresses for this subnet. Therefore, the range of host addresses for this subnet is 192.168.1.65 to 192.168.1.126. The other subnets do not contain the address 192.168.1.96 as a valid host address.Hint
For the subnet of 192.168.1.64/26, there are 6 bits for host addresses, yielding 64 possible addresses. However, the first and last subnets are the network and broadcast addresses for this subnet. Therefore, the range of host addresses for this subnet is 192.168.1.65 to 192.168.1.126. The other subnets do not contain the address 192.168.1.96 as a valid host address. -
Question 37 of 54
37. Question
1 pointsA network administrator wants to have the same subnet mask for three subnetworks at a small site. The site has the following networks and numbers of devices:
Subnetwork A: IP phones – 10 addresses
Subnetwork B: PCs – 8 addresses
Subnetwork C: Printers – 2 addressesWhat single subnet mask would be appropriate to use for the three subnetworks?
Correct
Incorrect
If the same mask is to be used, then the network with the most hosts must be examined for number of hosts. Because this is 10 hosts, 4 host bits are needed. The /28 or 255.255.255.240 subnet mask would be appropriate to use for these networks. Hint
If the same mask is to be used, then the network with the most hosts must be examined for number of hosts. Because this is 10 hosts, 4 host bits are needed. The /28 or 255.255.255.240 subnet mask would be appropriate to use for these networks. -
Question 38 of 54
38. Question
1 pointsWhich statement is true about variable-length subnet masking?Correct
Incorrect
In variable-length subnet masking, bits are borrowed to create subnets. Additional bits may be borrowed to create additional subnets within the original subnets. This may continue until there are no bits available to borrow.Hint
In variable-length subnet masking, bits are borrowed to create subnets. Additional bits may be borrowed to create additional subnets within the original subnets. This may continue until there are no bits available to borrow. -
Question 39 of 54
39. Question
1 pointsWhat subnet mask is needed if an IPv4 network has 40 devices that need IP addresses and address space is not to be wasted?Correct
Incorrect
In order to accommodate 40 devices, 6 host bits are needed. With 6 bits, 64 addresses are possible, but one address is for the subnet number and one address is for a broadcast. This leaves 62 addresses that can be assigned to network devices. The mask associated with leaving 6 host bits for addressing is 255.255.255.192.Hint
In order to accommodate 40 devices, 6 host bits are needed. With 6 bits, 64 addresses are possible, but one address is for the subnet number and one address is for a broadcast. This leaves 62 addresses that can be assigned to network devices. The mask associated with leaving 6 host bits for addressing is 255.255.255.192. -
Question 40 of 54
40. Question
2 pointsWhat are two characteristics shared by TCP and UDP? (Choose two.)Correct
Incorrect
Both TCP and UDP use source and destination port numbers to distinguish different data streams and to forward the right data segments to the right applications. Error checking the header and data is done by both protocols by using a checksum calculation to determine the integrity of the data that is received. TCP is connection-oriented and uses a 3-way handshake to establish an initial connection. TCP also uses window to regulate the amount of traffic sent before receiving an acknowledgment. UDP is connectionless and is the best protocol for carry digitized VoIP signals.Hint
Both TCP and UDP use source and destination port numbers to distinguish different data streams and to forward the right data segments to the right applications. Error checking the header and data is done by both protocols by using a checksum calculation to determine the integrity of the data that is received. TCP is connection-oriented and uses a 3-way handshake to establish an initial connection. TCP also uses window to regulate the amount of traffic sent before receiving an acknowledgment. UDP is connectionless and is the best protocol for carry digitized VoIP signals. -
Question 41 of 54
41. Question
1 pointsWhy are port numbers included in the TCP header of a segment?Correct
Incorrect
-
Question 42 of 54
42. Question
2 pointsWhat are two ways that TCP uses the sequence numbers in a segment? (Choose two.)Correct
Incorrect
-
Question 43 of 54
43. Question
2 pointsWhich two protocols operate at the highest layer of the TCP/IP protocol stack? (Choose two.)Correct
Incorrect
The application layer is the top layer of the TCP/IP protocol stack. Application layer protocols include HTTP, DNS, HTML, TFTP, POP, IMAP, FTP, and SMTP.Hint
The application layer is the top layer of the TCP/IP protocol stack. Application layer protocols include HTTP, DNS, HTML, TFTP, POP, IMAP, FTP, and SMTP. -
Question 44 of 54
44. Question
1 pointsWhat is an example of a top-level domain?Correct
Incorrect
Top-level domains represent a country or type of organization, such as .com or .edu.Hint
Top-level domains represent a country or type of organization, such as .com or .edu. -
Question 45 of 54
45. Question
1 pointsWhat is one difference between the client-server and peer-to-peer network models?Correct
Incorrect
Data transfer speeds depend on a number of factors including the amount of traffic, the quality of service imposed, and the network media. Transfer speeds are not dependent on the network model type. File transfers can occur using the client-server model or the peer-to-peer model. A data transfer between a device acting in the client role and a device acting in the server role can occur in both peer-to-peer and client-server networks.Hint
Data transfer speeds depend on a number of factors including the amount of traffic, the quality of service imposed, and the network media. Transfer speeds are not dependent on the network model type. File transfers can occur using the client-server model or the peer-to-peer model. A data transfer between a device acting in the client role and a device acting in the server role can occur in both peer-to-peer and client-server networks.
-
Question 46 of 54
46. Question
1 pointsWhich networking model is being used when an author uploads one chapter document to a file server of a book publisher?Correct
Incorrect
In the client/server network model, a network device assumes the role of server in order to provide a particular service such as file transfer and storage. In the client/server network model, a dedicated server does not have to be used, but if one is present, the network model being used is the client/server model. In contrast, a peer-to-peer network does not have a dedicated server.Hint
In the client/server network model, a network device assumes the role of server in order to provide a particular service such as file transfer and storage. In the client/server network model, a dedicated server does not have to be used, but if one is present, the network model being used is the client/server model. In contrast, a peer-to-peer network does not have a dedicated server. -
Question 47 of 54
47. Question
1 pointsA wireless host needs to request an IP address. What protocol would be used to process the request?Correct
Incorrect
The DHCP protocol is used to request, issue, and manage IP addressing information. CSMA/CD is the access method used with wired Ethernet. ICMP is used to test connectivity. SNMP is used with network management and FTP is used for file transfer.Hint
The DHCP protocol is used to request, issue, and manage IP addressing information. CSMA/CD is the access method used with wired Ethernet. ICMP is used to test connectivity. SNMP is used with network management and FTP is used for file transfer. -
Question 48 of 54
48. Question
1 pointsWhat network service resolves the URL entered on a PC to the IP address of the destination server?Correct
Incorrect
When a client attempts to connect to a website, the destination URL must be resolved to an IP address. To do this the client queries a Domain Name System (DNS) server.Hint
When a client attempts to connect to a website, the destination URL must be resolved to an IP address. To do this the client queries a Domain Name System (DNS) server. -
Question 49 of 54
49. Question
1 pointsA network engineer is analyzing reports from a recently performed network baseline. Which situation would depict a possible latency issue?Correct
Incorrect
While analyzing historical reports an administrator can compare host-to-host timers from the ping command and depict possible latency issues.Hint
While analyzing historical reports an administrator can compare host-to-host timers from the ping command and depict possible latency issues. -
Question 50 of 54
50. Question
1 pointsWhich firewall feature is used to ensure that packets coming into a network are legitimate responses to requests initiated from internal hosts?Correct
Incorrect
Stateful packet inspection on a firewall checks that incoming packets are actually legitimate responses to requests originating from hosts inside the network. Packet filtering can be used to permit or deny access to resources based on IP or MAC address. Application filtering can permit or deny access based on port number. URL filtering is used to permit or deny access based on URL or on keywords.Hint
Stateful packet inspection on a firewall checks that incoming packets are actually legitimate responses to requests originating from hosts inside the network. Packet filtering can be used to permit or deny access to resources based on IP or MAC address. Application filtering can permit or deny access based on port number. URL filtering is used to permit or deny access based on URL or on keywords. -
Question 51 of 54
51. Question
1 pointsWhat is one indication that a Windows computer did not receive an IPv4 address from a DHCP server?Correct
Incorrect
When a Windows PC cannot communicate with an IPv4 DHCP server, the computer automatically assigns an IP address in the 169.254.0.0/16 range. Any other device on the same network that receives an address in the same range is reachable.Hint
When a Windows PC cannot communicate with an IPv4 DHCP server, the computer automatically assigns an IP address in the 169.254.0.0/16 range. Any other device on the same network that receives an address in the same range is reachable. -
Question 52 of 54
52. Question
1 pointsWhich command can an administrator issue on a Cisco router to send debug messages to the vty lines?Correct
Incorrect
Debug messages, like other IOS log messages, are sent to the console line by default. Sending these messages to the terminal lines requires the terminal monitor command.Hint
Debug messages, like other IOS log messages, are sent to the console line by default. Sending these messages to the terminal lines requires the terminal monitor command. -
Question 53 of 54
53. Question
6 pointsMatch the description with the associated IOS mode. (Not all options are used.)
Sort elements
- limited number of basic monitoring commands
- the first entrance into the CLI of an IOS device
- accessed by entering the enable command
- identified by a prompt ending with the # character
- changes made affect the operation of the device as a whole
- accessed by entering the configure terminal command
- used to enable the password for vty lines
-
user EXEC mode
-
user EXEC mode
-
privileged EXEC mode
-
privileged EXEC mode
-
global configuration mode
-
global configuration mode
Correct
Incorrect
-
Question 54 of 54
54. Question
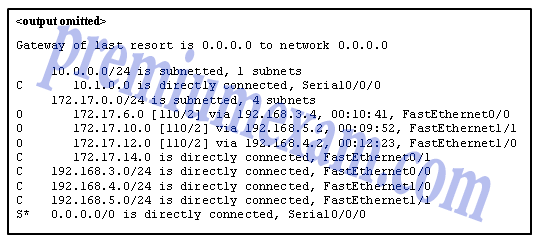
5 pointsRefer to the exhibit. Match the packets with their destination IP address to the exiting interfaces on the router. (Not all targets are used.)
Sort elements
- FastEthernet0/0
- FastEthernet0/1
- FastEthernet1/0
- FastEthernet1/1
- Serial0/0/0
- The packet is dropped.
-
packets with destination of 172.17.6.15
-
packets with destination of 172.17.14.8
-
packets with destination of 172.17.12.10
-
packets with destination of 172.17.10.5
-
packets with destination of 172.17.8.20
Correct
Incorrect