Last Updated on October 29, 2019 by Admin
CCNA CyberOps SECFND (210-250) Cert Practice Exam Online
CCNA CyberOps 1.1 -- SECFND (210-250) Cert Practice Exam
Quiz-summary
0 of 55 questions completed
Questions:
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
- 41
- 42
- 43
- 44
- 45
- 46
- 47
- 48
- 49
- 50
- 51
- 52
- 53
- 54
- 55
Information
CCNA CyberOps 1.1 — SECFND (210-250) Cert Practice Exam
You have already completed the quiz before. Hence you can not start it again.
Quiz is loading...
You must sign in or sign up to start the quiz.
You have to finish following quiz, to start this quiz:
Results
0 of 55 questions answered correctly
Your time:
Time has elapsed
You have reached 0 of 0 points, (0)
| Average score |
|
| Your score |
|
Categories
- Not categorized 0%
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
- 41
- 42
- 43
- 44
- 45
- 46
- 47
- 48
- 49
- 50
- 51
- 52
- 53
- 54
- 55
- Answered
- Review
-
Question 1 of 55
1. Question
1 pointsRefer to the exhibit. Approximately what percentage of the physical memory is still available on this Windows system?
Correct
Incorrect
The graphic shows that there is 5.1 GB (187 MB) of memory in use with 10.6 GB still available. Together this adds up to 16 GB of total physical memory. 5 GB is approximately 32% of 16 GB leaving 68% still available.
Hint
The graphic shows that there is 5.1 GB (187 MB) of memory in use with 10.6 GB still available. Together this adds up to 16 GB of total physical memory. 5 GB is approximately 32% of 16 GB leaving 68% still available.
-
Question 2 of 55
2. Question
1 pointsWhich Windows tool can be used by a cybersecurity administrator to secure stand-alone computers that are not part of an active directory domain?
Correct
Incorrect
Windows systems that are not part of an Active Directory Domain can use the Windows Local Security Policy to enforce security settings on each stand-alone system.
Hint
Windows systems that are not part of an Active Directory Domain can use the Windows Local Security Policy to enforce security settings on each stand-alone system.
-
Question 3 of 55
3. Question
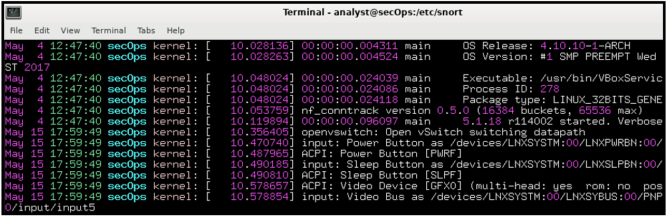
1 pointsRefer to the exhibit. Which technology would contain information similar to the data shown for infrastructure devices within a company?
Correct
Incorrect
A syslog server consolidates and maintains messages from infrastructure devices that have been configured to send logging information. Data from the syslog server can be analyzed to detect anomalies..
Hint
A syslog server consolidates and maintains messages from infrastructure devices that have been configured to send logging information. Data from the syslog server can be analyzed to detect anomalies..
-
Question 4 of 55
4. Question
3 pointsWhat are three benefits of using symbolic links over hard links in Linux? (Choose three.)
Correct
Incorrect
In Linux, a hard link is another file that points to the same location as the original file. A soft link (also called a symbolic link or a symlink) is a link to another file system name. Hard links are limited to the file system in which they are created and they cannot link to a directory; soft links are not limited to the same file system and they can link to a directory. To see the location of the original file for a symbolic link use the ls –l command.
Hint
In Linux, a hard link is another file that points to the same location as the original file. A soft link (also called a symbolic link or a symlink) is a link to another file system name. Hard links are limited to the file system in which they are created and they cannot link to a directory; soft links are not limited to the same file system and they can link to a directory. To see the location of the original file for a symbolic link use the ls –l command.
-
Question 5 of 55
5. Question
2 pointsWhich two protocols are associated with the transport layer? (Choose two.)
Correct
Incorrect
TCP and UDP reside at the transport layer in both the OSI and TCP/IP models.
Hint
TCP and UDP reside at the transport layer in both the OSI and TCP/IP models.
-
Question 6 of 55
6. Question
1 pointsRefer to the exhibit. A user reports that resources can no longer be reached on the local 192.168.1.0/24 network nor on the internet. A cybersecurity analyst investigates the issue by reviewing the routing table of the PC in question. What is the reason for the problem reported by the user?
Correct
Incorrect
In the routing table of the PC, the default gateway is 192.168.1.1 and the host IP address is 192.168.2.2. These addresses are on different networks. The host should have an IP address on the 192.168.1.0/24 network. To correct this problem the host IP must be changed to an address on the 192.168.1.0/24 local network.
Hint
In the routing table of the PC, the default gateway is 192.168.1.1 and the host IP address is 192.168.2.2. These addresses are on different networks. The host should have an IP address on the 192.168.1.0/24 network. To correct this problem the host IP must be changed to an address on the 192.168.1.0/24 local network.
-
Question 7 of 55
7. Question
1 pointsWhat is the function of ARP?
Correct
Incorrect
ARP, or Address Resolution Protocol, is used by hosts to resolve a destination MAC address from a given destination IP address.
Hint
ARP, or Address Resolution Protocol, is used by hosts to resolve a destination MAC address from a given destination IP address.
-
Question 8 of 55
8. Question
1 pointsA cybersecurity analyst believes an attacker is spoofing the MAC address of the default gateway to perform a man-in-the-middle attack. Which command should the analyst use to view the MAC address a host is using to reach the default gateway?
Correct
Incorrect
ARP is a protocol used with IPv4 to map a MAC address to an associated specific IP address. The command arp -a will display the MAC address table on a Windows PC.
Hint
ARP is a protocol used with IPv4 to map a MAC address to an associated specific IP address. The command arp -a will display the MAC address table on a Windows PC.
-
Question 9 of 55
9. Question
1 pointsWhich network service is used by clients to resolve the IP address of a domain name?
Correct
Incorrect
The Domain Name System (DNS) is used by clients to resolve the IP address of a domain name. For example, a host may need to connect to http://www.cisco.com. The host would contact a DNS server to discover the IP address associated with the domain http://www.cisco.com.
Hint
The Domain Name System (DNS) is used by clients to resolve the IP address of a domain name. For example, a host may need to connect to http://www.cisco.com. The host would contact a DNS server to discover the IP address associated with the domain http://www.cisco.com.
-
Question 10 of 55
10. Question
1 pointsRefer to the exhibit. A cybersecurity analyst is viewing captured packets forwarded on switch S1. Which device is the source of the captured packet?
Correct
Incorrect
The Wireshark output is displaying a DNS query that was sent from PC-A to switch S1. DNS queries are sourced from DNS clients, which in this case would be PC-A.
Hint
The Wireshark output is displaying a DNS query that was sent from PC-A to switch S1. DNS queries are sourced from DNS clients, which in this case would be PC-A.
-
Question 11 of 55
11. Question
1 pointsWhat is a purpose of implementing VLANs on a network?
Correct
Incorrect
VLANs are used on a network to separate user traffic based on factors such as function, project team, or application, without regard for the physical location of the user or device.
Hint
VLANs are used on a network to separate user traffic based on factors such as function, project team, or application, without regard for the physical location of the user or device.
-
Question 12 of 55
12. Question
1 pointsWhich type of firewall is a combination of various firewall types?
Correct
Incorrect
A hybrid firewall is a combination of different firewall types such as combining a stateful firewall with an application gateway firewall.
Hint
A hybrid firewall is a combination of different firewall types such as combining a stateful firewall with an application gateway firewall.
-
Question 13 of 55
13. Question
1 pointsWhat is a feature of an IPS?
Correct
Incorrect
An advantage of an intrusion prevention systems (IPS) is that it can identify and stop malicious packets. However, because an IPS is deployed inline, it can add latency to the network.
Hint
An advantage of an intrusion prevention systems (IPS) is that it can identify and stop malicious packets. However, because an IPS is deployed inline, it can add latency to the network.
-
Question 14 of 55
14. Question
1 pointsRefer to the exhibit. A network administrator has written a standard access control list to prevent packets from the 192.168.2.0 LAN from reaching the restricted LAN 192.168.3.0 while permiting traffic from any other LAN. On what interface and in which direction should the access list be implemented on router R1?
Correct
Incorrect
The access list requires that the source network 192.168.2.0 is denied while other networks are permitted to reach the restricted LAN. The access list must be applied on interface G0/2 in the outbound direction.
Hint
The access list requires that the source network 192.168.2.0 is denied while other networks are permitted to reach the restricted LAN. The access list must be applied on interface G0/2 in the outbound direction.
-
Question 15 of 55
15. Question
1 pointsWhat is an example of a local exploit?
Correct
Incorrect
Vulnerability exploits may be remote or local. In a local exploit, the threat actor has some type of user access to the end system, either physically or through remote access. The exploitation activity is within the local network.
Hint
Vulnerability exploits may be remote or local. In a local exploit, the threat actor has some type of user access to the end system, either physically or through remote access. The exploitation activity is within the local network.
-
Question 16 of 55
16. Question
1 pointsAfter complaints from users, a technician identifies that the college web server is running very slowly. A check of the server reveals that there are an unusually large number of TCP requests coming from multiple locations on the Internet. What is the source of the problem?
Correct
Incorrect
The source of the problem cannot be a virus because in this situation the server is passive and at the receiving end of the attack. A replay attack uses intercepted and recorded data in an attempt to gain access to an unauthorized server. This type of attack does not involve multiple computers. The issue is not the bandwidth available, but the number of TCP connections taking place. Receiving a large number of connections from multiple locations is the main symptom of a distributed denial of service attack which use botnets or zombie computers.
Hint
The source of the problem cannot be a virus because in this situation the server is passive and at the receiving end of the attack. A replay attack uses intercepted and recorded data in an attempt to gain access to an unauthorized server. This type of attack does not involve multiple computers. The issue is not the bandwidth available, but the number of TCP connections taking place. Receiving a large number of connections from multiple locations is the main symptom of a distributed denial of service attack which use botnets or zombie computers.
-
Question 17 of 55
17. Question
1 pointsA user receives an email requesting verification of the password that is used to access bank files. What type of security threat is this?
Correct
Incorrect
Phishing is a form of attack that starts with the attacker pretending to be a legitimate entity and then tries to gather information that can be used to conduct the exploit.
Hint
Phishing is a form of attack that starts with the attacker pretending to be a legitimate entity and then tries to gather information that can be used to conduct the exploit.
-
Question 18 of 55
18. Question
1 pointsTo which category of security attacks does man-in-the-middle belong?
Correct
Incorrect
With a man-in-the-middle attack, a threat actor is positioned in between two legitimate entities in order to read, modify, or redirect the data that passes between the two parties.
Hint
With a man-in-the-middle attack, a threat actor is positioned in between two legitimate entities in order to read, modify, or redirect the data that passes between the two parties.
-
Question 19 of 55
19. Question
1 pointsWhat is the main goal of using different evasion techniques by threat actors?
Correct
Incorrect
Many threat actors use stealthy evasion techniques to disguise an attack payload because the malware and attack methods are most effective if they are undetected. The goal is to prevent detection by network and host defenses.
Hint
Many threat actors use stealthy evasion techniques to disguise an attack payload because the malware and attack methods are most effective if they are undetected. The goal is to prevent detection by network and host defenses.
-
Question 20 of 55
20. Question
2 pointsWhat are two examples of DoS attacks? (Choose two.)
Correct
Incorrect
The buffer overflow and ping of death DoS attacks exploit system memory-related flaws on a server by sending an unexpected amount of data or malformed data to the server.
Hint
The buffer overflow and ping of death DoS attacks exploit system memory-related flaws on a server by sending an unexpected amount of data or malformed data to the server.
-
Question 21 of 55
21. Question
1 pointsWhich attack is integrated with the lowest levels of the operating system of a host and attempts to completely hide the activities of the threat actor on the local system?
Correct
Incorrect
A rootkit is a complex attack tool and it integrates with the lowest levels of the operating system. The goal of the rootkit is to completely hide the activities of the threat actor on the local system.
Hint
A rootkit is a complex attack tool and it integrates with the lowest levels of the operating system. The goal of the rootkit is to completely hide the activities of the threat actor on the local system.
-
Question 22 of 55
22. Question
1 pointsWhich evasion method describes the situation that after gaining access to the administrator password on a compromised host, a threat actor is attempting to login to another host using the same credentials?
Correct
Incorrect
Pivoting is an evasion method that assumes the threat actor has compromised an inside host and the actor wants to expand the access further into the compromised network.
Hint
Pivoting is an evasion method that assumes the threat actor has compromised an inside host and the actor wants to expand the access further into the compromised network.
-
Question 23 of 55
23. Question
2 pointsWhich two attacks target web servers through exploiting possible vulnerabilities of input functions used by an application? (Choose two.)
Correct
Incorrect
When a web application uses input fields to collect data from clients, threat actors may exploit possible vulnerabilities for entering malicious commands. The malicious commands that are executed through the web application might affect the OS on the web server. SQL injection and cross-site scripting are two different types of command injection attacks.
Hint
When a web application uses input fields to collect data from clients, threat actors may exploit possible vulnerabilities for entering malicious commands. The malicious commands that are executed through the web application might affect the OS on the web server. SQL injection and cross-site scripting are two different types of command injection attacks.
-
Question 24 of 55
24. Question
1 pointsWhat is the first line of defense when an organization is using a defense-in-depth approach to network security?
Correct
Incorrect
A defense-in-depth approach uses layers of security measures starting at the network edge, working through the network, and finally ending at the network endpoints. Routers at the network edge are the first line of defense and forward traffic intended for the internal network to the firewall.
Hint
A defense-in-depth approach uses layers of security measures starting at the network edge, working through the network, and finally ending at the network endpoints. Routers at the network edge are the first line of defense and forward traffic intended for the internal network to the firewall.
-
Question 25 of 55
25. Question
1 pointsWhat is the benefit of a defense-in-depth approach?
Correct
Incorrect
The benefit of the defense-in-depth approach is that network defenses are implemented in layers so that failure of any single security mechanism does not impact other secuirty measures.
Hint
The benefit of the defense-in-depth approach is that network defenses are implemented in layers so that failure of any single security mechanism does not impact other secuirty measures.
-
Question 26 of 55
26. Question
1 pointsWhich access control model allows users to control access to data as an owner of that data?
Correct
Incorrect
In the discretionary access control (DAC) model, users can control access to data as owners of the data.
Hint
In the discretionary access control (DAC) model, users can control access to data as owners of the data.
-
Question 27 of 55
27. Question
1 pointsWhat is the principle behind the nondiscretionary access control model?
Correct
Incorrect
The nondiscretionary access control model used the roles and responsibilities of the user as the basis for access decisions.
Hint
The nondiscretionary access control model used the roles and responsibilities of the user as the basis for access decisions.
-
Question 28 of 55
28. Question
1 pointsWhat is an example of privilege escalation attack?
Correct
Incorrect
With the privilege escalation exploit, vulnerabilities in servers or access control systems are exploited to grant an unauthorized user, or software process, higher levels of privilege than either should have. After the higher privilege is granted, the threat actor can access sensitive information or take control of a system.
Hint
With the privilege escalation exploit, vulnerabilities in servers or access control systems are exploited to grant an unauthorized user, or software process, higher levels of privilege than either should have. After the higher privilege is granted, the threat actor can access sensitive information or take control of a system.
-
Question 29 of 55
29. Question
1 pointsWhich access control model applies the strictest access control and is often used in military and mission critical applications?
Correct
Incorrect
Military and mission critical applications typically use mandatory access control which applies the strictest access control to protect network resources.
Hint
Military and mission critical applications typically use mandatory access control which applies the strictest access control to protect network resources.
-
Question 30 of 55
30. Question
1 pointsWhich data security component is provided by hashing algorithms?
Correct
Incorrect
Hashing algorithms are used to provide message integrity, which ensures that data in transit has not changed or been altered.
Hint
Hashing algorithms are used to provide message integrity, which ensures that data in transit has not changed or been altered.
-
Question 31 of 55
31. Question
2 pointsWhich two algorithms use a hashing function to ensure message integrity? (Choose two.)
Correct
Incorrect
Hashing algorithms are used to provide data integrity, which ensures that the data has not changed during transmission. MD5 and SHA are commonly used hashing algorithms.
Hint
Hashing algorithms are used to provide data integrity, which ensures that the data has not changed during transmission. MD5 and SHA are commonly used hashing algorithms.
-
Question 32 of 55
32. Question
1 pointsWhat is a feature of asymmetrical encryption?
Correct
Incorrect
Asymmetric encryption algorithms use different keys for encryption and decryption. These are known as private and public keys. The longer key lengths used by asymmetric algorithms make them slower than symmetrical encryption and inefficient for bulk data.
Hint
Asymmetric encryption algorithms use different keys for encryption and decryption. These are known as private and public keys. The longer key lengths used by asymmetric algorithms make them slower than symmetrical encryption and inefficient for bulk data.
-
Question 33 of 55
33. Question
1 pointsWhat technology supports asymmetric key encryption used in IPsec VPNs?
Correct
Incorrect
IKE, or Internet Key Exchange, is a protocol to support asymmetric encryption algorithms. It is used to securely exchange encryption keys in the setup of IPsec VPNs.
Hint
IKE, or Internet Key Exchange, is a protocol to support asymmetric encryption algorithms. It is used to securely exchange encryption keys in the setup of IPsec VPNs.
-
Question 34 of 55
34. Question
1 pointsWhich security function is provided by encryption algorithms?
Correct
Incorrect
Encryption algorithms are used to provide data confidentiality, which ensures that if data is intercepted in transit, it cannot be read.
Hint
Encryption algorithms are used to provide data confidentiality, which ensures that if data is intercepted in transit, it cannot be read.
-
Question 35 of 55
35. Question
1 pointsA security professional is making recommendations to a company for enhancing endpoint security. Which security endpoint technology would be recommended as an agent-based system to protect hosts against malware?
Correct
Incorrect
A host-based intrusion detection systems (HIDS) is a comprehensive security application that provides antimalware applications, a firewall, and monitoring and reporting.
Hint
A host-based intrusion detection systems (HIDS) is a comprehensive security application that provides antimalware applications, a firewall, and monitoring and reporting.
-
Question 36 of 55
36. Question
1 pointsWhich firewall application runs on a Linux host and allows an administrator to configure network access rules as part of the Linux kernel?
Correct
Incorrect
The iptables is an application that allows Linux system administrators to configure network access rules that are part of the Linux kernel Netfilter modules.
Hint
The iptables is an application that allows Linux system administrators to configure network access rules that are part of the Linux kernel Netfilter modules.
-
Question 37 of 55
37. Question
1 pointsWhich security endpoint setting would be used by a security analyst to determine if a computer has been configured to prevent a particular application from running?
Correct
Incorrect
Blacklisting can be used on a local system or updated on security devices such as a firewall. Blacklists can be manually entered or obtained from a centralized security system. Blacklists are applications that are prevented from executing because they pose a security risk to the individual system and potentially the company.
Hint
Blacklisting can be used on a local system or updated on security devices such as a firewall. Blacklists can be manually entered or obtained from a centralized security system. Blacklists are applications that are prevented from executing because they pose a security risk to the individual system and potentially the company.
-
Question 38 of 55
38. Question
1 pointsWhich technique could be used by security personnel to analyze a suspicious file in a safe environment?
Correct
Incorrect
Sandboxing allows suspicious files to be executed and analyzed in a safe environment. There are free public sandboxes that allow for malware samples to be uploaded or submitted and analyzed.
Hint
Sandboxing allows suspicious files to be executed and analyzed in a safe environment. There are free public sandboxes that allow for malware samples to be uploaded or submitted and analyzed.
-
Question 39 of 55
39. Question
1 pointsWhich attack surface, defined by the SANS Institute, is delivered through the exploitation of vulnerabilities in web, cloud, or host-based applications?
Correct
Incorrect
The SANS Institute describes three components of the attack surface:
- Network Attack Surface – exploits vulnerabilities in networks
- Software Attack Surface – delivered through the exploitation of vulnerabilities in web, cloud, or host-based software applications
- Human Attack Surface – exploits weaknesses in user behavior
Hint
The SANS Institute describes three components of the attack surface:
- Network Attack Surface – exploits vulnerabilities in networks
- Software Attack Surface – delivered through the exploitation of vulnerabilities in web, cloud, or host-based software applications
- Human Attack Surface – exploits weaknesses in user behavior
-
Question 40 of 55
40. Question
1 pointsWhat is an action that should be taken in the discovery step of the vulnerability management life cycle?
Correct
Incorrect
During the discovery step of the vulnerability management life cycle, an inventory of all network assets is made. A network baseline is developed, and security vulnerabilities are identified.
Hint
During the discovery step of the vulnerability management life cycle, an inventory of all network assets is made. A network baseline is developed, and security vulnerabilities are identified.
-
Question 41 of 55
41. Question
1 pointsWhich security management plan specifies a component that involves tracking the location and configuration of networked devices and software across an enterprise?
Correct
Incorrect
Asset management involves tracking the location and configuration of networked devices and software across an enterprise.
Hint
Asset management involves tracking the location and configuration of networked devices and software across an enterprise.
-
Question 42 of 55
42. Question
1 pointsWhich risk management plan involves discontinuing an activity that creates a risk?
Correct
Incorrect
During a risk assessment it may be determined that an activity involves more risk than benefit. In such a situation an organization may decide to avoid the risk altogether by discontinuing the activity. This is known as risk avoidance.
Hint
During a risk assessment it may be determined that an activity involves more risk than benefit. In such a situation an organization may decide to avoid the risk altogether by discontinuing the activity. This is known as risk avoidance.
-
Question 43 of 55
43. Question
1 pointsA piece of malware has gained access to a workstation and issued a DNS lookup query to a CnC server. What is the purpose of this attack?
Correct
Incorrect
A piece of malware, after accessing a host, may exploit the DNS service by communicating with command-and-control (CnC) servers and then exfiltrate data in traffic disguised as normal DNS lookup queries. Various types of encoding, such as base64, 8-bit binary, and hex can be used to camouflage the data and evade basic data loss prevention (DLP) measures.
Hint
A piece of malware, after accessing a host, may exploit the DNS service by communicating with command-and-control (CnC) servers and then exfiltrate data in traffic disguised as normal DNS lookup queries. Various types of encoding, such as base64, 8-bit binary, and hex can be used to camouflage the data and evade basic data loss prevention (DLP) measures.
-
Question 44 of 55
44. Question
1 pointsWhy does HTTPS technology add complexity to network security monitoring?
Correct
Incorrect
With HTTPS, a symmetric key is generated by the client after the client verifies the trustworthiness of the web server. The symmetric key is encrypted with the public key of the web server and then sent to the web server. The web server uses its public key to decrypt the key. The key is then used to encrypt the data requested by the client and the data is sent to the client. This end-to-end encryption complicates inline network security monitoring. The HTTPS port number, typically 443, is configured statically on the web server.
Hint
With HTTPS, a symmetric key is generated by the client after the client verifies the trustworthiness of the web server. The symmetric key is encrypted with the public key of the web server and then sent to the web server. The web server uses its public key to decrypt the key. The key is then used to encrypt the data requested by the client and the data is sent to the client. This end-to-end encryption complicates inline network security monitoring. The HTTPS port number, typically 443, is configured statically on the web server.
-
Question 45 of 55
45. Question
1 pointsWhich type of attack is carried out by threat actors against a network to determine which IP addresses, protocols, and ports are allowed by ACLs?
Correct
Incorrect
Packet filtering ACLs use rules to filter incoming and outgoing traffic. These rules are defined by specifying IP addresses, port numbers, and protocols to be matched. Threat actors can use a reconnaissance attack involving port scanning or penetration testing to determine which IP addresses, protocols, and ports are allowed by ACLs.
Hint
Packet filtering ACLs use rules to filter incoming and outgoing traffic. These rules are defined by specifying IP addresses, port numbers, and protocols to be matched. Threat actors can use a reconnaissance attack involving port scanning or penetration testing to determine which IP addresses, protocols, and ports are allowed by ACLs.
-
Question 46 of 55
46. Question
1 pointsHow can NAT/PAT complicate network security monitoring if NetFlow is being used?
Correct
Incorrect
NAT/PAT maps multiple internal IP addresses with only a single or a few outside IP addresses breaking end-to-end flows. The result makes it difficult to log the inside device that is requesting and receiving the traffic. This is especially a problem with a NetFlow application because NetFlow flows are unidirectional and are defined by the addresses and ports that they share.
Hint
NAT/PAT maps multiple internal IP addresses with only a single or a few outside IP addresses breaking end-to-end flows. The result makes it difficult to log the inside device that is requesting and receiving the traffic. This is especially a problem with a NetFlow application because NetFlow flows are unidirectional and are defined by the addresses and ports that they share.
-
Question 47 of 55
47. Question
1 pointsWhich statement describes the function provided by the Tor network?
Correct
Incorrect
Tor is a software platform and network of P2P hosts that function as Internet routers on the Tor network. The Tor network allows users to browse the Internet anonymously.
Hint
Tor is a software platform and network of P2P hosts that function as Internet routers on the Tor network. The Tor network allows users to browse the Internet anonymously.
-
Question 48 of 55
48. Question
1 pointsRefer to the exhibit. A security analyst is reviewing an alert message generated by Snort. What does the number 2100498 in the message indicate?
Correct
Incorrect
The sid field in a Snort alert message indicates the Snort security rule that is triggered.
Hint
The sid field in a Snort alert message indicates the Snort security rule that is triggered.
-
Question 49 of 55
49. Question
1 pointsWhich type of data is used by Cisco Cognitive Threat Analytics to find malicious activity that has bypassed security controls, or entered through unmonitored channels, and is operating inside an enterprise network?
Correct
Incorrect
Cisco Cognitive Threat Analytics utilizes statistical data for statistical analysis in order to find malicious activity that has bypassed security controls, or entered through unmonitored channels (including removable media), and is operating inside the network of an organization.
Hint
Cisco Cognitive Threat Analytics utilizes statistical data for statistical analysis in order to find malicious activity that has bypassed security controls, or entered through unmonitored channels (including removable media), and is operating inside the network of an organization.
-
Question 50 of 55
50. Question
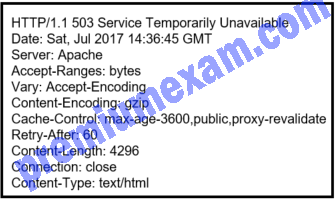
1 pointsRefer to the exhibit. A security analyst is reviewing the logs of an Apache web server. Which action should the analyst take based on the output shown?
Correct
Incorrect
An Apache web server is an open source server that delivers web pages. Security access logs for an Apache web server include a 3-digit HTTP code that represents the status of the web request. A code that begins with 2 indicates access success. A code that begins with 3 represents redirection. A code that begins with 4 represents a client error and a code that begins with 5 represents a server error. The server administrator should be alerted if a server error such as the 503 code occurs.
Hint
An Apache web server is an open source server that delivers web pages. Security access logs for an Apache web server include a 3-digit HTTP code that represents the status of the web request. A code that begins with 2 indicates access success. A code that begins with 3 represents redirection. A code that begins with 4 represents a client error and a code that begins with 5 represents a server error. The server administrator should be alerted if a server error such as the 503 code occurs.
-
Question 51 of 55
51. Question
1 pointsWhich Windows application is commonly used by a cybersecurity analyst to view Microsoft IIS access logs?
Correct
Incorrect
Event Viewer is an application on a Windows-based device used to view event logs including IIS access logs.
Hint
Event Viewer is an application on a Windows-based device used to view event logs including IIS access logs.
-
Question 52 of 55
52. Question
1 pointsWhich tool captures full data packets with a command-line interface only?
Correct
Incorrect
The command-line tool tcpdump is a packet analyzer. Wireshark is a packet analyzer with a GUI interface.
Hint
The command-line tool tcpdump is a packet analyzer. Wireshark is a packet analyzer with a GUI interface.
-
Question 53 of 55
53. Question
1 pointsWhat is a key difference between the data captured by NetFlow and data captured by Wireshark?
Correct
Incorrect
Wireshark captures the entire contents of a packet. NetFlow does not. Instead, NetFlow collects metadata, or data about the flow.
Hint
Wireshark captures the entire contents of a packet. NetFlow does not. Instead, NetFlow collects metadata, or data about the flow.
-
Question 54 of 55
54. Question
1 pointsWhich Cisco appliance can be used to filter network traffic contents to report and deny traffic based on the web server reputation?
Correct
Incorrect
The Cisco Web Security Appliance (WSA) acts as a web proxy for an enterprise network. WSA can provide many types of logs related to web traffic security including ACL decision logs, malware scan logs, and web reputation filtering logs. The Cisco Email Security Appliance (ESA) is a tool to monitor most aspects of email delivery, system functioning, antivirus, antispam operations, and blacklist and whitelist decisions. The Cisco ASA is a firewall appliance. The Cisco Application Visibility and Control (AVC) system combines multiple technologies to recognize, analyze, and control over 1000 applications.
Hint
The Cisco Web Security Appliance (WSA) acts as a web proxy for an enterprise network. WSA can provide many types of logs related to web traffic security including ACL decision logs, malware scan logs, and web reputation filtering logs. The Cisco Email Security Appliance (ESA) is a tool to monitor most aspects of email delivery, system functioning, antivirus, antispam operations, and blacklist and whitelist decisions. The Cisco ASA is a firewall appliance. The Cisco Application Visibility and Control (AVC) system combines multiple technologies to recognize, analyze, and control over 1000 applications.
-
Question 55 of 55
55. Question
1 pointsWhich type of event is logged in Cisco Next-Generation IPS devices (NGIPS) using FirePOWER Services when changes have been detected in the monitored network?
Correct
Incorrect
Network discovery events in Cisco NGIPS represent changes that have been detected in the monitored network.
Hint
Network discovery events in Cisco NGIPS represent changes that have been detected in the monitored network.