Last Updated on November 1, 2019 by Admin
Implementing Network Security (Version 2.0) – CCNAS Final Exam Online
CCNAS -- Final Exam
Quiz-summary
0 of 60 questions completed
Questions:
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
- 41
- 42
- 43
- 44
- 45
- 46
- 47
- 48
- 49
- 50
- 51
- 52
- 53
- 54
- 55
- 56
- 57
- 58
- 59
- 60
Information
CCNAS — Final Exam
You have already completed the quiz before. Hence you can not start it again.
Quiz is loading...
You must sign in or sign up to start the quiz.
You have to finish following quiz, to start this quiz:
Results
0 of 60 questions answered correctly
Your time:
Time has elapsed
You have reached 0 of 0 points, (0)
| Average score |
|
| Your score |
|
Categories
- Not categorized 0%
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
- 41
- 42
- 43
- 44
- 45
- 46
- 47
- 48
- 49
- 50
- 51
- 52
- 53
- 54
- 55
- 56
- 57
- 58
- 59
- 60
- Answered
- Review
-
Question 1 of 60
1. Question
1 pointsWhich security measure is best used to limit the success of a reconnaissance attack from within a campus area network?
Correct
Incorrect
The implementation of an access list may provide extra security by permitting denying a flow of traffic, but it will not provide a direct response to limit the success of the attack. The implementation of a firewall on the network edge may prevent reconnaissance attacks from the Internet, but attacks within the local network are not prevented. By implementing restrictions on the sending of ICMP echo-reply messages within a local network, devices may not respond to ping messages, but port scans are not prevented and clear-text data sent on the network are still vulnerable. The best security measure is to encrypt as much network traffic as possible, both user data and network management traffic.
Hint
The implementation of an access list may provide extra security by permitting denying a flow of traffic, but it will not provide a direct response to limit the success of the attack. The implementation of a firewall on the network edge may prevent reconnaissance attacks from the Internet, but attacks within the local network are not prevented. By implementing restrictions on the sending of ICMP echo-reply messages within a local network, devices may not respond to ping messages, but port scans are not prevented and clear-text data sent on the network are still vulnerable. The best security measure is to encrypt as much network traffic as possible, both user data and network management traffic.
-
Question 2 of 60
2. Question
1 pointsWhich security implementation will provide control plane protection for a network device?
Correct
Incorrect
Control plane traffic such as ARP messages or routing protocol advertisements are generated by a network device in order to support network operations. Routing protocol authentication provides an extra measure of security to authenticate the source of routing updates. Encrypting remote access connections, utilizing the NTP protocol, and using AAA, are all measures implemented to secure management plane traffic.
Hint
Control plane traffic such as ARP messages or routing protocol advertisements are generated by a network device in order to support network operations. Routing protocol authentication provides an extra measure of security to authenticate the source of routing updates. Encrypting remote access connections, utilizing the NTP protocol, and using AAA, are all measures implemented to secure management plane traffic.
-
Question 3 of 60
3. Question
2 pointsWhich two practices are associated with securing the features and performance of router operating systems? (Choose two.)
Correct
Incorrect
Configuring a router with maximum available memory allows support for the widest range of security services and can help to protect against certain DoS attacks. Secure copies of router operating system images and configuration files provide backups needed for device recovery. Installing a UPS device provides physical security for networking devices but does not affect the security of their operating systems. Disabling unnecessary ports and services is part of the process of router hardening, and does not specifically involve the router operating system.
Hint
Configuring a router with maximum available memory allows support for the widest range of security services and can help to protect against certain DoS attacks. Secure copies of router operating system images and configuration files provide backups needed for device recovery. Installing a UPS device provides physical security for networking devices but does not affect the security of their operating systems. Disabling unnecessary ports and services is part of the process of router hardening, and does not specifically involve the router operating system.
-
Question 4 of 60
4. Question
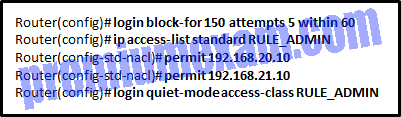
1 pointsRefer to the exhibit. An administrator issues these IOS login enhancement commands to increase the security for login connections. What can be concluded about them?
Correct
Incorrect
When the login block-for command is implemented, it automatically invokes a one-second delay between login attempts. The login block-for command that is presented means that login will be disabled for 150 seconds, if more than 5 login failures occur within 60 seconds. These enhancements do not apply to console connections. When quiet mode is enabled, all login attempts are denied except for the hosts permitted in the ACL.Hint
When the login block-for command is implemented, it automatically invokes a one-second delay between login attempts. The login block-for command that is presented means that login will be disabled for 150 seconds, if more than 5 login failures occur within 60 seconds. These enhancements do not apply to console connections. When quiet mode is enabled, all login attempts are denied except for the hosts permitted in the ACL. -
Question 5 of 60
5. Question
1 pointsWhat is a characteristic of a role-based CLI view of router configuration?
Correct
Incorrect
A CLI view has no command hierarchy, and therefore, no higher or lower views. Deleting a superview does not delete the associated CLI views. Only a root view user can configure a new view and add or remove commands from the existing views.
Hint
A CLI view has no command hierarchy, and therefore, no higher or lower views. Deleting a superview does not delete the associated CLI views. Only a root view user can configure a new view and add or remove commands from the existing views.
-
Question 6 of 60
6. Question
1 pointsWhat is a result of securing the Cisco IOS image using the Cisco IOS Resilient Configuration feature?
Correct
Incorrect
When using the Cisco IOS Resilient Configuration feature, a secure copy of the IOS image is stored in flash and is hidden from view and and not included in any directory listings.
Hint
When using the Cisco IOS Resilient Configuration feature, a secure copy of the IOS image is stored in flash and is hidden from view and and not included in any directory listings.
-
Question 7 of 60
7. Question
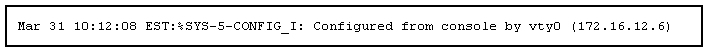
2 pointsRefer to the exhibit. What two pieces of information can be gathered from the generated message? (Choose two.)
Correct
Incorrect
A Cisco router log message consists for three parts:
1) the timestamp
2) the log message and severity level
3) the message textHint
A Cisco router log message consists for three parts:
1) the timestamp
2) the log message and severity level
3) the message text -
Question 8 of 60
8. Question
1 pointsWhat represents a best practice concerning discovery protocols such as CDP and LLDP on network devices?
Correct
Incorrect
Both discovery protocols can provide hackers with sensitive network information. They should not be enabled on edge devices, and should be disabled globally or on a per-interface basis if not required. CDP is enabled by default.Hint
Both discovery protocols can provide hackers with sensitive network information. They should not be enabled on edge devices, and should be disabled globally or on a per-interface basis if not required. CDP is enabled by default. -
Question 9 of 60
9. Question
1 pointsWhat is the one major difference between local AAA authentication and using the login local command when configuring device access authentication?
Correct
Incorrect
Local AAA authentication works very similar to the login local command, except that it allows you to specify backup authentication methods as well. Both methods require that local usernames and passwords be manually configured on the router.
Hint
Local AAA authentication works very similar to the login local command, except that it allows you to specify backup authentication methods as well. Both methods require that local usernames and passwords be manually configured on the router.
-
Question 10 of 60
10. Question
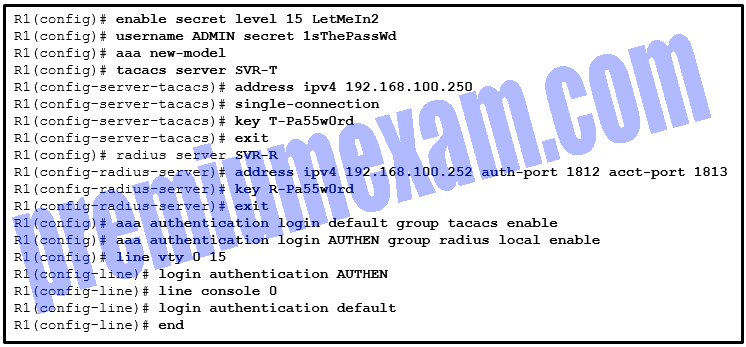
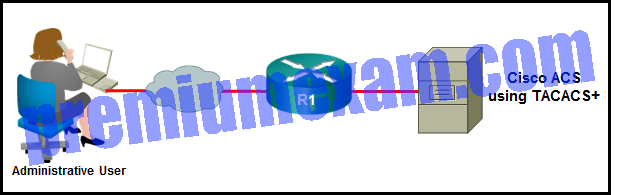
1 pointsRefer to the exhibit. A network administrator configures AAA authentication on router R1. The ACS servers are configured and running. The administrator tests the configuration by telneting to R1. What will happen if the administrator attempts to authenticate through the RADIUS server using incorrect credentials?
Correct
Incorrect
The authentication for Telnet connections is defined by AAA method list AUTHEN. The AUTHEN list defines that the first authentication method is through an ACS server using the RADIUS protocol (or RADIUS server), the second authentication method is to use the local user database, and the third method is to use the enable password. In this scenario, however, because the administrator fails to pass the authentication by the first method, the authentication process stops and no other authentication methods are allowed.
Hint
The authentication for Telnet connections is defined by AAA method list AUTHEN. The AUTHEN list defines that the first authentication method is through an ACS server using the RADIUS protocol (or RADIUS server), the second authentication method is to use the local user database, and the third method is to use the enable password. In this scenario, however, because the administrator fails to pass the authentication by the first method, the authentication process stops and no other authentication methods are allowed.
-
Question 11 of 60
11. Question
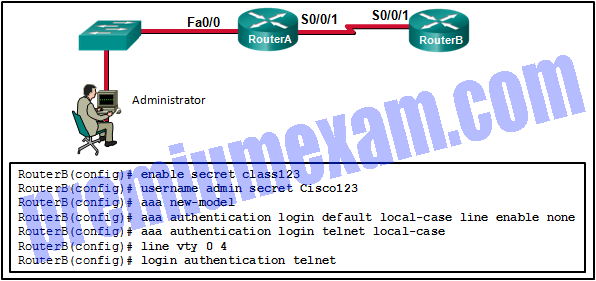
1 pointsRefer to the exhibit. The administrator can ping the S0/0/1 interface of RouterB but is unable to gain Telnet access to the router by using the password cisco123. What is a possible cause of the problem?
Correct
Incorrect
To authenticate and log in using a Telnet vty line, the network administrator is required to use the local username and password that has been configured on the local router. This is evidenced by the application of the aaa authentication login telnet local-case command. The administrator must use a capital C in Cisco123 to match the applied configuration.Hint
To authenticate and log in using a Telnet vty line, the network administrator is required to use the local username and password that has been configured on the local router. This is evidenced by the application of the aaa authentication login telnet local-case command. The administrator must use a capital C in Cisco123 to match the applied configuration. -
Question 12 of 60
12. Question
1 pointsWhat is a feature of the TACACS+ protocol?
Correct
Incorrect
TACACS+ has the following features:separates authentication and authorization
encrypts all communication
uses TCP port 49Hint
TACACS+ has the following features:separates authentication and authorization
encrypts all communication
uses TCP port 49 -
Question 13 of 60
13. Question
1 pointsIn an AAA-enabled network, a user issues the configure terminal command from the privileged executive mode of operation. What AAA function is at work if this command is rejected?
Correct
Incorrect
Authentication must ensure that devices or end users are legitimate. Authorization is concerned with allowing and disallowing authenticated users access to certain areas and programs on the network. The configure terminal command is rejected because the user is not authorized to execute the command.
Hint
Authentication must ensure that devices or end users are legitimate. Authorization is concerned with allowing and disallowing authenticated users access to certain areas and programs on the network. The configure terminal command is rejected because the user is not authorized to execute the command.
-
Question 14 of 60
14. Question
1 pointsA network administrator enters the single-connection command. What effect does this command have on AAA operation?
Correct
Incorrect
By default, TACACS+ establishes a new TCP session for every authorization request. This can lead to delays.To improve performance, Cisco Secure ACS supports persistent TCP sessions configured with the single-connection command.
Hint
By default, TACACS+ establishes a new TCP session for every authorization request. This can lead to delays.To improve performance, Cisco Secure ACS supports persistent TCP sessions configured with the single-connection command.
-
Question 15 of 60
15. Question
1 pointsRefer to the exhibit. In the network that is shown, which AAA command logs the use of EXEC session commands?
Correct
Incorrect
The aaa accounting exec start-stop group tacacs+ command is used to configure the router to log the use of EXEC commands.Hint
The aaa accounting exec start-stop group tacacs+ command is used to configure the router to log the use of EXEC commands. -
Question 16 of 60
16. Question
1 pointsWhat is an advantage in using a packet filtering firewall versus a high-end firewall appliance?
Correct
Incorrect
There are several advantages of using a packet filtering firewall:
– allows for implementing simple permit or deny rule sets.
– has a low impact on network performance
– is easy to implement, and is supported by most routers
– provides an initial degree of security at the network layer
– performs almost all the tasks of a high-end firewall at a much lower costHint
There are several advantages of using a packet filtering firewall:
– allows for implementing simple permit or deny rule sets.
– has a low impact on network performance
– is easy to implement, and is supported by most routers
– provides an initial degree of security at the network layer
– performs almost all the tasks of a high-end firewall at a much lower cost -
Question 17 of 60
17. Question
1 pointsWhat is a benefit of using a next-generation firewall rather than a stateful firewall?
Correct
Incorrect
Stateful and next-generation firewalls provide better log information than packet filtering firewalls. Both stateful and next-generation firewalls defend against spoofing by filtering unwanted traffic. However, next-generation firewalls provide the following benefits over stateful firewalls:
- Granularity control within applications
- Website and application traffic filtering based on site reputation
- Proactive rather than reactive protection from Internet threat
- Enforcement of security policies based on multiple criteria
- Improved performance with NAT, VPN, and stateful inspections
- Integrated IPS
Hint
Stateful and next-generation firewalls provide better log information than packet filtering firewalls. Both stateful and next-generation firewalls defend against spoofing by filtering unwanted traffic. However, next-generation firewalls provide the following benefits over stateful firewalls:
- Granularity control within applications
- Website and application traffic filtering based on site reputation
- Proactive rather than reactive protection from Internet threat
- Enforcement of security policies based on multiple criteria
- Improved performance with NAT, VPN, and stateful inspections
- Integrated IPS
-
Question 18 of 60
18. Question
2 pointsWhat are two characteristics of a stateful firewall? (Choose two.)
Correct
Incorrect
Stateful firewalls are the most versatile and the most common firewall technologies in use. Stateful firewalls provide stateful packet filtering by using connection information maintained in a state table. Stateful filtering is a firewall architecture that is classified at the network layer. It also analyzes traffic at OSI Layers 4 and 5. Stateful firewalls cannot prevent application layer attacks because they do not examine the actual contents of an HTTP connection.
Hint
Stateful firewalls are the most versatile and the most common firewall technologies in use. Stateful firewalls provide stateful packet filtering by using connection information maintained in a state table. Stateful filtering is a firewall architecture that is classified at the network layer. It also analyzes traffic at OSI Layers 4 and 5. Stateful firewalls cannot prevent application layer attacks because they do not examine the actual contents of an HTTP connection.
-
Question 19 of 60
19. Question
2 pointsWhat are two benefits of using a ZPF rather than a Classic Firewall? (Choose two.)
Correct
Incorrect
There are several benefits of a ZPF:
· It is not dependent on ACLs.
· The router security posture is to block unless explicitly allowed.
· Policies are easy to read and troubleshoot with C3PL.
· One policy affects any given traffic, instead of needing multiple ACLs and inspection actions.In addition, an interface cannot be simultaneously configured as a security zone member and for IP inspection.
Hint
There are several benefits of a ZPF:
· It is not dependent on ACLs.
· The router security posture is to block unless explicitly allowed.
· Policies are easy to read and troubleshoot with C3PL.
· One policy affects any given traffic, instead of needing multiple ACLs and inspection actions.In addition, an interface cannot be simultaneously configured as a security zone member and for IP inspection.
-
Question 20 of 60
20. Question
1 pointsWhat is a feature of a Cisco IOS Zone-Based Policy Firewall?
Correct
Incorrect
The pass action allows traffic in only one direction. Interfaces automatically become members of the self zone. Interfaces are assigned to a zone in interface configuration mode, but most configuration takes place in global configuration mode and associated submodes. An interface can belong to only one zone at a time.
Hint
The pass action allows traffic in only one direction. Interfaces automatically become members of the self zone. Interfaces are assigned to a zone in interface configuration mode, but most configuration takes place in global configuration mode and associated submodes. An interface can belong to only one zone at a time.
-
Question 21 of 60
21. Question
1 pointsWhich IDS/IPS signature alarm will look for packets that are destined to or from a particular port?
Correct
Incorrect
Cisco IDS and IPS sensors can use four types of signature alarms or triggers:
- Pattern-based detection – also known as signature-based detection, searches for a specific and pre-defined pattern. In most cases, the pattern is matched to the signature only if the suspect packet is associated with a particular service or destined to or from particular ports.
- Anomaly-based detection – also known as profile-based detection, involves first defining a profile of what is considered normal for the network or host. After defining normal activity, the signature triggers an action if excessive activity occurs beyond a specified threshold that is not included in the normal profile.
- Policy-based detection – also known as behavior-based detection, is similar to pattern-based detection, but instead of trying to define specific patterns, the administrator defines behaviors that are suspicious based on historical analysis.
- Honey pot-based detection – uses a dummy server to attract attacks.
Hint
Cisco IDS and IPS sensors can use four types of signature alarms or triggers:
- Pattern-based detection – also known as signature-based detection, searches for a specific and pre-defined pattern. In most cases, the pattern is matched to the signature only if the suspect packet is associated with a particular service or destined to or from particular ports.
- Anomaly-based detection – also known as profile-based detection, involves first defining a profile of what is considered normal for the network or host. After defining normal activity, the signature triggers an action if excessive activity occurs beyond a specified threshold that is not included in the normal profile.
- Policy-based detection – also known as behavior-based detection, is similar to pattern-based detection, but instead of trying to define specific patterns, the administrator defines behaviors that are suspicious based on historical analysis.
- Honey pot-based detection – uses a dummy server to attract attacks.
-
Question 22 of 60
22. Question
3 pointsWhich three actions can the Cisco IOS Firewall IPS feature be configured to take when an intrusion activity is detected? (Choose three.)
Correct
Incorrect
In IPS implementation, when a signature detects a matching activity, the signature triggers one or more of these actions:Generates an alert
Logs the activity
Drops or prevent the activity
Resets a TCP connection
Blocks future activity
Allows the activityHint
In IPS implementation, when a signature detects a matching activity, the signature triggers one or more of these actions:Generates an alert
Logs the activity
Drops or prevent the activity
Resets a TCP connection
Blocks future activity
Allows the activity -
Question 23 of 60
23. Question
1 pointsAn organization has configured an IPS solution to use atomic alerts. What type of response will occur when a signature is detected?
Correct
Incorrect
Atomic alerts are generated every time a signature triggers. A summary alert is a single alert that indicates multiple occurrences of the same signature from the same source address or port. Deny packet and deny flow actions do not automatically cause TCP reset actions to occur. Atomic alerts do not shut down interfaces.
Hint
Atomic alerts are generated every time a signature triggers. A summary alert is a single alert that indicates multiple occurrences of the same signature from the same source address or port. Deny packet and deny flow actions do not automatically cause TCP reset actions to occur. Atomic alerts do not shut down interfaces.
-
Question 24 of 60
24. Question
1 pointsWhich Cisco IOS subcommand is used to compile an IPS signature into memory?
Correct
Incorrect
The Cisco IOS subcommand retired can be used to retire (not to compile into memory) or unretire (compile into memory) individual signatures or a group of signatures that belong to a signature category. The command retired false instructs IOS to compile an IPS signature into memory. The command retired true instructs IOS not to compile an IPS signature into memory. The commands event-action produce-alert and event-action deny-attacker-inline define the action when an enabled signature is matched.Hint
The Cisco IOS subcommand retired can be used to retire (not to compile into memory) or unretire (compile into memory) individual signatures or a group of signatures that belong to a signature category. The command retired false instructs IOS to compile an IPS signature into memory. The command retired true instructs IOS not to compile an IPS signature into memory. The commands event-action produce-alert and event-action deny-attacker-inline define the action when an enabled signature is matched. -
Question 25 of 60
25. Question
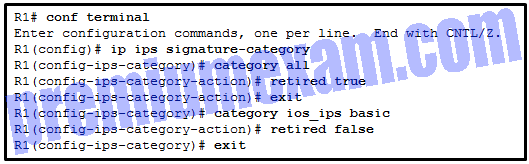
1 pointsRefer to the exhibit. Based on the configuration that is shown, which statement is true about the IPS signature category?
Correct
Incorrect
When a signature category is marked as retired by using the command retired true, then the IPS does not compile signatures that are part of that category into memory for inspection (scanning). The retired false command does the opposite. This command instructs the IPS to include those signatures that are part of that category into memory for scanning.Hint
When a signature category is marked as retired by using the command retired true, then the IPS does not compile signatures that are part of that category into memory for inspection (scanning). The retired false command does the opposite. This command instructs the IPS to include those signatures that are part of that category into memory for scanning. -
Question 26 of 60
26. Question
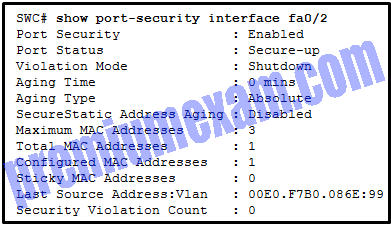
3 pointsRefer to the exhibit. The network administrator is configuring the port security feature on switch SWC. The administrator issued the command show port-security interface fa 0/2 to verify the configuration. What can be concluded from the output that is shown? (Choose three.)
Correct
Incorrect
Because the security violation count is at 0, no violation has occurred. The system shows that 3 MAC addresses are allowed on port fa0/2, but only one has been configured and no sticky MAC addresses have been learned. The port is up because of the port status of secure-up. The violation mode is what happens when an unauthorized device is attached to the port. A port must be in access mode in order to activate and use port security.
Hint
Because the security violation count is at 0, no violation has occurred. The system shows that 3 MAC addresses are allowed on port fa0/2, but only one has been configured and no sticky MAC addresses have been learned. The port is up because of the port status of secure-up. The violation mode is what happens when an unauthorized device is attached to the port. A port must be in access mode in order to activate and use port security.
-
Question 27 of 60
27. Question
2 pointsWhich two ports can send and receive Layer 2 traffic from a community port on a PVLAN? (Choose two.)
Correct
Incorrect
Community ports can send and receive information with ports within the same community, or with a promiscuous port. Isolated ports can only communicate with promiscuous ports. Promiscuous ports can talk to all interfaces. PVLAN edge protected ports only forward traffic through a Layer 3 device to other protected ports.
Hint
Community ports can send and receive information with ports within the same community, or with a promiscuous port. Isolated ports can only communicate with promiscuous ports. Promiscuous ports can talk to all interfaces. PVLAN edge protected ports only forward traffic through a Layer 3 device to other protected ports.
-
Question 28 of 60
28. Question
1 pointsWhat Layer 2 attack is mitigated by disabling Dynamic Trunking Protocol?
Correct
Incorrect
Mitigating a VLAN hopping attack can be done by disabling Dynamic Trunking Protocol (DTP) and by setting the native VLAN of trunk links to VLANs not in use.
Hint
Mitigating a VLAN hopping attack can be done by disabling Dynamic Trunking Protocol (DTP) and by setting the native VLAN of trunk links to VLANs not in use.
-
Question 29 of 60
29. Question
1 pointsOn which port should Dynamic ARP Inspection (DAI) be configured on a switch?
Correct
Incorrect
DHCP snooping must be enabled on a port where DAI is configured, because DAI requires the DHCP snooping table to operate. Only a trusted interface, such as an uplink port between switches, is configured to implement DAI. All access ports are untrusted.
Hint
DHCP snooping must be enabled on a port where DAI is configured, because DAI requires the DHCP snooping table to operate. Only a trusted interface, such as an uplink port between switches, is configured to implement DAI. All access ports are untrusted.
-
Question 30 of 60
30. Question
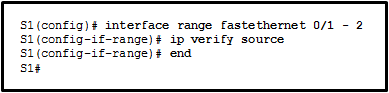
1 pointsRefer to the exhibit. The ip verify source command is applied on untrusted interfaces. Which type of attack is mitigated by using this configuration?
Correct
Incorrect
To protect against MAC and IP address spoofing, apply the IP Source Guard security feature, using the ip verify source command, on untrusted ports.
Hint
To protect against MAC and IP address spoofing, apply the IP Source Guard security feature, using the ip verify source command, on untrusted ports.
-
Question 31 of 60
31. Question
1 pointsWhy is hashing cryptographically stronger compared to a cyclical redundancy check (CRC)?
Correct
Incorrect
When assuring integrity with CRC values, it is easy to generate data with the same CRC. With hash functions, it is computationally infeasible for two different sets of data to come up with the same hash output. Hashing can use many bit values depending on the algorithm. These characteristics make hashing much stronger cryptographically.
Hint
When assuring integrity with CRC values, it is easy to generate data with the same CRC. With hash functions, it is computationally infeasible for two different sets of data to come up with the same hash output. Hashing can use many bit values depending on the algorithm. These characteristics make hashing much stronger cryptographically.
-
Question 32 of 60
32. Question
1 pointsWhy are DES keys considered weak keys?
Correct
Incorrect
Weak keys, whether part of an existing encryption algorithm or manually generated, reveal regularities in encryption. This creates a shortcut by which a hacker can break the encryption. DES has four keys for which encryption is identical to decryption.
Hint
Weak keys, whether part of an existing encryption algorithm or manually generated, reveal regularities in encryption. This creates a shortcut by which a hacker can break the encryption. DES has four keys for which encryption is identical to decryption.
-
Question 33 of 60
33. Question
1 pointsWhat type of algorithms require sender and receiver to exchange a secret key that is used to ensure the confidentiality of messages?
Correct
Incorrect
Symmetric algorithms use the same key, a secret key, to encrypt and decrypt data. This key must be pre-shared before communication can occur. Asymmetric algorithms require more processing power and overhead on the communicating devices because these keys can be long in order to avoid being hacked.
Hint
Symmetric algorithms use the same key, a secret key, to encrypt and decrypt data. This key must be pre-shared before communication can occur. Asymmetric algorithms require more processing power and overhead on the communicating devices because these keys can be long in order to avoid being hacked.
-
Question 34 of 60
34. Question
2 pointsWhat two assurances does digital signing provide about code that is downloaded from the Internet? (Choose two.)
Correct
Incorrect
Digitally signing code provides several assurances about the code:
The code is authentic and is actually sourced by the publisher.
The code has not been modified since it left the software publisher.
The publisher undeniably published the code. This provides nonrepudiation of the act of publishing.Hint
Digitally signing code provides several assurances about the code:
The code is authentic and is actually sourced by the publisher.
The code has not been modified since it left the software publisher.
The publisher undeniably published the code. This provides nonrepudiation of the act of publishing. -
Question 35 of 60
35. Question
1 pointsWhich statement describes the use of certificate classes in the PKI?
Correct
Incorrect
The higher the certificate number, the more trustworthy the certificate. Class 1 certificates are for individuals, with a focus on email verification. An enterprise can act as its own CA and implement PKI for internal use. In that situation, the vendor can issue certificates as needed for various purposes.
Hint
The higher the certificate number, the more trustworthy the certificate. Class 1 certificates are for individuals, with a focus on email verification. An enterprise can act as its own CA and implement PKI for internal use. In that situation, the vendor can issue certificates as needed for various purposes.
-
Question 36 of 60
36. Question
2 pointsWhat two algorithms can be part of an IPsec policy to provide encryption and hashing to protect interesting traffic? (Choose two.)
Correct
Incorrect
The IPsec framework uses various protocols and algorithms to provide data confidentiality, data integrity, authentication, and secure key exchange. Two algorithms that can be used within an IPsec policy to protect interesting traffic are AES, which is an encryption protocol, and SHA, which is a hashing algorithm.
Hint
The IPsec framework uses various protocols and algorithms to provide data confidentiality, data integrity, authentication, and secure key exchange. Two algorithms that can be used within an IPsec policy to protect interesting traffic are AES, which is an encryption protocol, and SHA, which is a hashing algorithm.
-
Question 37 of 60
37. Question
1 pointsWhat algorithm is used to provide data integrity of a message through the use of a calculated hash value?
Correct
Incorrect
The IPsec framework uses various protocols and algorithms to provide data confidentiality, data integrity, authentication, and secure key exchange. To ensure that data is not intercepted and modified (data integrity), Hashed Message Authentication Code (HMAC) is used. AES is an encryption protocol and provides data confidentiality. DH (Diffie-Hellman) is an algorithm that is used for key exchange. RSA is an algorithm that is used for authentication.
Hint
The IPsec framework uses various protocols and algorithms to provide data confidentiality, data integrity, authentication, and secure key exchange. To ensure that data is not intercepted and modified (data integrity), Hashed Message Authentication Code (HMAC) is used. AES is an encryption protocol and provides data confidentiality. DH (Diffie-Hellman) is an algorithm that is used for key exchange. RSA is an algorithm that is used for authentication.
-
Question 38 of 60
38. Question
1 pointsWhat is negotiated in the establishment of an IPsec tunnel between two IPsec hosts during IKE Phase 1?
Correct
Incorrect
Establishing an IPsec tunnel involves five steps:Detection of interesting traffic defined by an ACL
IKE Phase 1 in which peers negotiate ISAKMP SA policy
IKE Phase 2 in which peers negotiate IPsec SA policy
Creation of the IPsec tunnel
Termination of the IPsec tunnelHint
Establishing an IPsec tunnel involves five steps:Detection of interesting traffic defined by an ACL
IKE Phase 1 in which peers negotiate ISAKMP SA policy
IKE Phase 2 in which peers negotiate IPsec SA policy
Creation of the IPsec tunnel
Termination of the IPsec tunnel -
Question 39 of 60
39. Question
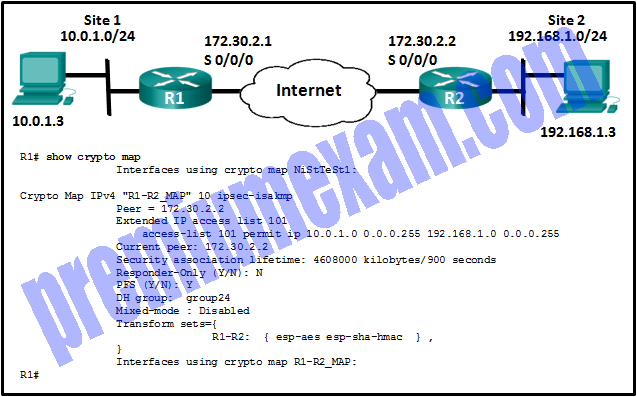
1 pointsRefer to the exhibit. Which conclusion can be made from the show crypto map command output that is shown on R1?
Correct
Incorrect
According to the show crypto map command output, all required SAs are in place, but no interface is currently using the crypto map. To complete the tunnel configuration, the crypto map has to be applied to the outbound interface of each router.Hint
According to the show crypto map command output, all required SAs are in place, but no interface is currently using the crypto map. To complete the tunnel configuration, the crypto map has to be applied to the outbound interface of each router. -
Question 40 of 60
40. Question
2 pointsIn which two instances will traffic be denied as it crosses the ASA 5505 device? (Choose two.)
Correct
Incorrect
When an ASA 5505 device is being utilized, traffic is denied as it travels from a lower security zone to a higher security zone. The highest security zone is the internal network, the DMZ is usually the next highest, and the outside network is the lowest. Traffic is only allowed to move from a lower security level to a higher if it is in response to originating traffic within the higher security zone.
Hint
When an ASA 5505 device is being utilized, traffic is denied as it travels from a lower security zone to a higher security zone. The highest security zone is the internal network, the DMZ is usually the next highest, and the outside network is the lowest. Traffic is only allowed to move from a lower security level to a higher if it is in response to originating traffic within the higher security zone.
-
Question 41 of 60
41. Question
1 pointsWhat mechanism is used by an ASA 5505 device to allow inspected outbound traffic to return to the originating sender who is on an inside network?
Correct
Incorrect
Stateful packet inspection allows return traffic that is sourced on the outside network to be received by the originating sender on the internal network.
Hint
Stateful packet inspection allows return traffic that is sourced on the outside network to be received by the originating sender on the internal network.
-
Question 42 of 60
42. Question
1 pointsWhich type of traffic is subject to filtering on an ASA 5505 device?
Correct
Incorrect
Filtering only applies to traffic traveling in the direction from a higher security level to a lower security level.
Hint
Filtering only applies to traffic traveling in the direction from a higher security level to a lower security level.
-
Question 43 of 60
43. Question
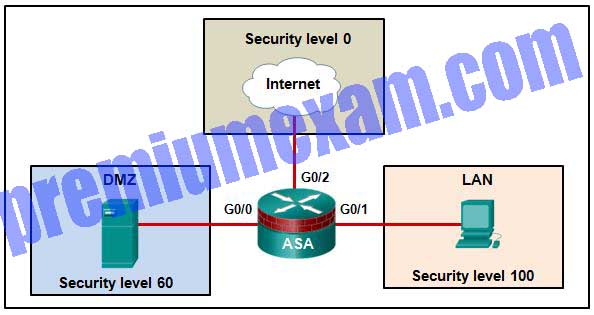
1 pointsRefer to the exhibit. Based on the security levels of the interfaces on the ASA, what statement correctly describes the flow of traffic allowed on the interfaces?
Correct
Incorrect
When traffic moves from an interface with a higher security level to an interface with a lower security level, it is considered outbound traffic. Conversely, traffic that moves from an interface with a lower security level to an interface with a higher security level is considered inbound traffic.
Hint
When traffic moves from an interface with a higher security level to an interface with a lower security level, it is considered outbound traffic. Conversely, traffic that moves from an interface with a lower security level to an interface with a higher security level is considered inbound traffic.
-
Question 44 of 60
44. Question
2 pointsWhich two conditions must be met in order for a network administrator to be able to remotely manage multiple ASAs with Cisco ASDM? (Choose two.)
Correct
Incorrect
Cisco ASDM is a Java-based GUI tool that makes ASA configuration easier. In order to remotely manage multiple ASAs with Cisco ASDM, each ASA must have the same ASDM version. When ASDM is run as a local application, no browser is required and several ASA devices can be managed.
Hint
Cisco ASDM is a Java-based GUI tool that makes ASA configuration easier. In order to remotely manage multiple ASAs with Cisco ASDM, each ASA must have the same ASDM version. When ASDM is run as a local application, no browser is required and several ASA devices can be managed.
-
Question 45 of 60
45. Question
1 pointsWhich interface option could be set through ASDM for a Cisco ASA?
Correct
Incorrect
To assign a VLAN number to an interface, choose Configuration > Device Setup > Interfaces and add or select an interface. Choose the Advanced tab to assign a VLAN. Other options that can be assigned to an interface include an IP address, mask, and security level.Hint
To assign a VLAN number to an interface, choose Configuration > Device Setup > Interfaces and add or select an interface. Choose the Advanced tab to assign a VLAN. Other options that can be assigned to an interface include an IP address, mask, and security level. -
Question 46 of 60
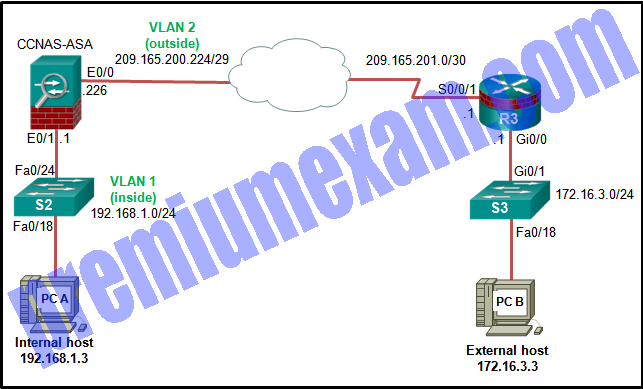
46. Question
1 pointsRefer to the exhibit. If a network administrator is using ASDM to configure a site-to-site VPN between the CCNAS-ASA and R3, which IP address would the administrator use for the peer IP address textbox on the ASA if data traffic is to be encrypted between the two remote LANs?
Correct
Incorrect
When ASDM is used to configure an ASA, the peer address is the IP address of the other site for the VPN. In this instance R3 has the outside IP address of 209.165.201.1, so that must be the peer IP address for the ASA. Conversely, R3 will have to be configured with a peer IP address of 209.165.200.226.
Hint
When ASDM is used to configure an ASA, the peer address is the IP address of the other site for the VPN. In this instance R3 has the outside IP address of 209.165.201.1, so that must be the peer IP address for the ASA. Conversely, R3 will have to be configured with a peer IP address of 209.165.200.226.
-
Question 47 of 60
47. Question
2 pointsWhich two end points can be on the other side of an ASA site-to-site VPN configured using ASDM? (Choose two.)
Correct
Incorrect
ASDM supports creating an ASA site-to-site VPN between two ASAs or between an ASA and an ISR router.
Hint
ASDM supports creating an ASA site-to-site VPN between two ASAs or between an ASA and an ISR router.
-
Question 48 of 60
48. Question
2 pointsAn administrator assigned a level of router access to the user ADMIN using the commands below.
Router(config)# privilege exec level 14 show ip route
Router(config)# enable algorithm-type scrypt secret level 14 cisco-level-10
Router(config)# username ADMIN privilege 14 algorithm-type scrypt secret cisco-level-10Which two actions are permitted to the user ADMIN? (Choose two.)
Correct
Incorrect
Assigning a command such as show ip route to a specific privilege level automatically assigns all commands associated with the first few keywords to the specified privilege level. So, the show and the show ip commands are automatically set to the privilege level where show ip route is set, which is necessary because the show ip route command cannot be executed without access to the show and show ip commands. Assigning the show ip route command allows the user to issue all show commands, such as show version.Hint
Assigning a command such as show ip route to a specific privilege level automatically assigns all commands associated with the first few keywords to the specified privilege level. So, the show and the show ip commands are automatically set to the privilege level where show ip route is set, which is necessary because the show ip route command cannot be executed without access to the show and show ip commands. Assigning the show ip route command allows the user to issue all show commands, such as show version. -
Question 49 of 60
49. Question
2 pointsWhich two protocols can be selected using the Cisco AnyConnect VPN Wizard to protect the traffic inside a VPN tunnel? (Choose two.)
Correct
Incorrect
When a full tunnel is creating using the Cisco AnyConnect VPN Wizard, the VPN protocols should be selected to protect the traffic inside the tunnel. The VPN protocol choices are SSL and/or IPsec. Otherwise, a third-party certificate can be configured. Initially SSL and IPsec are selected.
Hint
When a full tunnel is creating using the Cisco AnyConnect VPN Wizard, the VPN protocols should be selected to protect the traffic inside the tunnel. The VPN protocol choices are SSL and/or IPsec. Otherwise, a third-party certificate can be configured. Initially SSL and IPsec are selected.
-
Question 50 of 60
50. Question
1 pointsA network analyst wants to monitor the activity of all new interns. Which type of security testing would track when the interns sign on and sign off the network?
Correct
Incorrect
An integrity checking system can report login and logout activities. Network scanning can detect user names, groups, and shared resources by scanning listening TCP ports. Password cracking is used to test and detect weak passwords. Vulnerability scanning can detect potential weaknesses in a system, such as misconfigurations, default passwords, or DoS attack targets.
Hint
An integrity checking system can report login and logout activities. Network scanning can detect user names, groups, and shared resources by scanning listening TCP ports. Password cracking is used to test and detect weak passwords. Vulnerability scanning can detect potential weaknesses in a system, such as misconfigurations, default passwords, or DoS attack targets.
-
Question 51 of 60
51. Question
3 pointsWhat are three characteristics of SIEM? (Choose three.)
Correct
Incorrect
Security Information Event Management (SIEM) is a technology that provides real-time reporting and long-term analysis of security events. SIEM provides the ability to search logs and events from disparate systems or applications to detect threats. SIEM aggregates duplicate events to reduce the volume of event data. SIEM can be implemented as software or as a managed.service. SuperScan is a Microsoft Windows port scanning tool that runs on most versions of Windows.Tools, such as Nmap and SuperScan, can provide effective penetration testing on a network and determine network vulnerabilities while helping to anticipate possible attack mechanisms.
Hint
Security Information Event Management (SIEM) is a technology that provides real-time reporting and long-term analysis of security events. SIEM provides the ability to search logs and events from disparate systems or applications to detect threats. SIEM aggregates duplicate events to reduce the volume of event data. SIEM can be implemented as software or as a managed.service. SuperScan is a Microsoft Windows port scanning tool that runs on most versions of Windows.Tools, such as Nmap and SuperScan, can provide effective penetration testing on a network and determine network vulnerabilities while helping to anticipate possible attack mechanisms.
-
Question 52 of 60
52. Question
2 pointsWhat are two tasks that can be accomplished with the Nmap and Zenmap network tools? (Choose two.)
Correct
Incorrect
Nmap is a low-level network scanner that is available to the public and which has the ability to perform port scanning, to identify open TCP and UDP ports, and perform system identification. It can also be used to identify Layer 3 protocols that are running on a system.
Hint
Nmap is a low-level network scanner that is available to the public and which has the ability to perform port scanning, to identify open TCP and UDP ports, and perform system identification. It can also be used to identify Layer 3 protocols that are running on a system.
-
Question 53 of 60
53. Question
1 pointsA company deploys a Cisco ASA with the Cisco CWS connector enabled as the firewall on the border of corporate network. An employee on the internal network is accessing a public website. What should the employee do in order to make sure the web traffic is protected by the Cisco CWS?
Correct
Incorrect
Once the connector is enabled on the Cisco ASA device, users on the internal network can connect to the Cisco CWS transparently when they access external websites. The Cisco CWS serves as a proxy for the web access to scan traffic for malware and policy enforcement. Users visit external websites by accessing the URLs directly on the web browsers.
Hint
Once the connector is enabled on the Cisco ASA device, users on the internal network can connect to the Cisco CWS transparently when they access external websites. The Cisco CWS serves as a proxy for the web access to scan traffic for malware and policy enforcement. Users visit external websites by accessing the URLs directly on the web browsers.
-
Question 54 of 60
54. Question
1 pointsThe corporate security policy dictates that the traffic from the remote-access VPN clients must be separated between trusted traffic that is destined for the corporate subnets and untrusted traffic destined for the public Internet. Which VPN solution should be implemented to ensure compliance with the corporate policy?
Correct
Incorrect
Hairpinning allows VPN traffic that is received on a single interface to be routed back out that same interface. Split tunneling allows traffic that originates from a remote-access client to be split according to whether the traffic must cross a VPN or the traffic is destined for the public Internet. MPLS and GRE are two types of Layer 3 VPNs.
Hint
Hairpinning allows VPN traffic that is received on a single interface to be routed back out that same interface. Split tunneling allows traffic that originates from a remote-access client to be split according to whether the traffic must cross a VPN or the traffic is destined for the public Internet. MPLS and GRE are two types of Layer 3 VPNs.
-
Question 55 of 60
55. Question
1 pointsWhat is required for auto detection and negotiation of NAT when establishing a VPN link?
Correct
Incorrect
Establishing a VPN between two sites has been a challenge when NAT is involved at either end of the tunnel. The enhanced version of original IKE, IKE version 2, now supports NAT Traversal (NAT-T). NAT-T has the ability to encapsulate ESP packets inside UDP. During IKE version 2 Phase 1, the VPN end devices can detect whether the other device is NAT-T capable and whether either device is connecting through a NAT-enabled device in order to establish the tunnel.
Hint
Establishing a VPN between two sites has been a challenge when NAT is involved at either end of the tunnel. The enhanced version of original IKE, IKE version 2, now supports NAT Traversal (NAT-T). NAT-T has the ability to encapsulate ESP packets inside UDP. During IKE version 2 Phase 1, the VPN end devices can detect whether the other device is NAT-T capable and whether either device is connecting through a NAT-enabled device in order to establish the tunnel. -
Question 56 of 60
56. Question
1 pointsWhat is the benefit of the network-based IPS (NIPS) over host-based IPS (HIPS) deployment models?
Correct
Incorrect
The network-based IPS (NIPS) is deployed in a network to monitor traffic in the network. Different from the host-based IPS (HIPS), NIPS does not provides protection to specific individual hosts. The operation of NIPS does not rely on the operating system of individual hosts nor centrally managed software agents.
Hint
The network-based IPS (NIPS) is deployed in a network to monitor traffic in the network. Different from the host-based IPS (HIPS), NIPS does not provides protection to specific individual hosts. The operation of NIPS does not rely on the operating system of individual hosts nor centrally managed software agents.
-
Question 57 of 60
57. Question
1 pointsWhich security policy characteristic defines the purpose of standards?
Correct
Incorrect
Standards help IT staff maintain consistency in the operations of the network. Guidelines are a list of suggestions on how to do things more efficiently and securely. They are similar to standards, but are more flexible and are not usually mandatory. Procedure documents are longer and more detailed than standards and guidelines. Procedure documents include implementation details that usually contain step-by-step instructions and graphics.
Hint
Standards help IT staff maintain consistency in the operations of the network. Guidelines are a list of suggestions on how to do things more efficiently and securely. They are similar to standards, but are more flexible and are not usually mandatory. Procedure documents are longer and more detailed than standards and guidelines. Procedure documents include implementation details that usually contain step-by-step instructions and graphics.
-
Question 58 of 60
58. Question
2 pointsWhat two new features are offered by Cisco ASA 5500-X with FirePOWER service when compared with the original ASA 5500 series? (Choose two.)
Correct
Incorrect
The Cisco ASA 5500-X series with FirePOWER service merges the ASA 5500 series appliances with some new features such as advanced malware protection as well as application control and URL filtering. The stateful firewall, IPsec VPN, and security level settings are functions common to both ASA 5500 and ASA 5500-X series devices.
Hint
The Cisco ASA 5500-X series with FirePOWER service merges the ASA 5500 series appliances with some new features such as advanced malware protection as well as application control and URL filtering. The stateful firewall, IPsec VPN, and security level settings are functions common to both ASA 5500 and ASA 5500-X series devices.
-
Question 59 of 60
59. Question
2 pointsWhich two statements describe the 8 Ethernet ports in the backplane of a Cisco ASA 5506-X device? (Choose two.)
Correct
Incorrect
Unlike the ASA 5505, the ASA 5506-X does not use switch ports. All Ethernet ports in the backplane are routed and require IP addresses.
Hint
Unlike the ASA 5505, the ASA 5506-X does not use switch ports. All Ethernet ports in the backplane are routed and require IP addresses.
-
Question 60 of 60
60. Question
3 pointsMatch the network security testing technique with how it is used to test network security. (Not all options are used.)
Sort elements
- used to determine the possible consequences of successful attacks on the network
- used to discover available resources on the network
- used to find weaknesses and misconfigurations on network systems
- used to detect and report changes made to systems
-
penetration testing
-
network scanning
-
vulnerability scanning
Correct
Incorrect
Network scanning tools are used to probe network devices, servers and hosts for open TCP or UDP ports. Vulnerability scanning tools are used to discover security weaknesses in a network or computer system. Penetration testing tools are used to determine the possible outcome of a successful attack on a network or computer system.
Hint
Network scanning tools are used to probe network devices, servers and hosts for open TCP or UDP ports. Vulnerability scanning tools are used to discover security weaknesses in a network or computer system. Penetration testing tools are used to determine the possible outcome of a successful attack on a network or computer system.