Last Updated on November 1, 2019 by Admin
Implementing Network Security (Version 2.0) – CCNA Security 2.0 Practice Final Online
CCNAS – Practice Final
Quiz-summary
0 of 58 questions completed
Questions:
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
- 41
- 42
- 43
- 44
- 45
- 46
- 47
- 48
- 49
- 50
- 51
- 52
- 53
- 54
- 55
- 56
- 57
- 58
Information
CCNAS – Practice Final
You have already completed the quiz before. Hence you can not start it again.
Quiz is loading...
You must sign in or sign up to start the quiz.
You have to finish following quiz, to start this quiz:
Results
0 of 58 questions answered correctly
Your time:
Time has elapsed
You have reached 0 of 0 points, (0)
| Average score |
|
| Your score |
|
Categories
- Not categorized 0%
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
- 41
- 42
- 43
- 44
- 45
- 46
- 47
- 48
- 49
- 50
- 51
- 52
- 53
- 54
- 55
- 56
- 57
- 58
- Answered
- Review
-
Question 1 of 58
1. Question
2 pointsWhich two types of hackers are typically classified as grey hat hackers? (Choose two.)
Correct
Incorrect
Grey hat hackers may do unethical or illegal things, but not for personal gain or to cause damage. Hacktivists use their hacking as a form of political or social protest, and vulnerability brokers hack to uncover weaknesses and report them to vendors. Depending on the perspective one possesses, state-sponsored hackers are either white hat or black hat operators. Script kiddies create hacking scripts to cause damage or disruption. Cyber criminals use hacking to obtain financial gain by illegal means.
Hint
Grey hat hackers may do unethical or illegal things, but not for personal gain or to cause damage. Hacktivists use their hacking as a form of political or social protest, and vulnerability brokers hack to uncover weaknesses and report them to vendors. Depending on the perspective one possesses, state-sponsored hackers are either white hat or black hat operators. Script kiddies create hacking scripts to cause damage or disruption. Cyber criminals use hacking to obtain financial gain by illegal means.
-
Question 2 of 58
2. Question
1 pointsWhich security implementation will provide management plane protection for a network device?
Correct
Incorrect
Management plane processes typically use protocols such as Telnet and SSH. Role-based access control ensures that only authorized users have management privileges. ACLs perform packet filtering and antispoofing functions on the data plane to secure packets generated by users. Routing protocol authentication on the control plane ensures that a router does not accept false routing updates from neighbor routers.
Hint
Management plane processes typically use protocols such as Telnet and SSH. Role-based access control ensures that only authorized users have management privileges. ACLs perform packet filtering and antispoofing functions on the data plane to secure packets generated by users. Routing protocol authentication on the control plane ensures that a router does not accept false routing updates from neighbor routers.
-
Question 3 of 58
3. Question
1 pointsWhich feature of the Cisco Network Foundation Protection framework prevents a route processor from being overwhelmed by unnecessary traffic?
Correct
Incorrect
Control Plane Policing provides a method for an administrator to control the amount of traffic that is being handled by the route processor. This security measure prevents a route processor from being overwhelmed by unnecessary traffic. IP Source Guard and access control lists are used to secure the data plane of network devices.
Hint
Control Plane Policing provides a method for an administrator to control the amount of traffic that is being handled by the route processor. This security measure prevents a route processor from being overwhelmed by unnecessary traffic. IP Source Guard and access control lists are used to secure the data plane of network devices.
-
Question 4 of 58
4. Question
3 pointsWhich three areas of router security must be maintained to secure an edge router at the network perimeter? (Choose three.)
Correct
Incorrect
There are three areas of router security to maintain:
1) physical security
2) router hardening
3) operating system securityHint
There are three areas of router security to maintain:
1) physical security
2) router hardening
3) operating system security -
Question 5 of 58
5. Question
3 pointsWhen configuring SSH on a router to implement secure network management, a network engineer has issued the login local and transport input ssh line vty commands. What three additional configuration actions have to be performed to complete the SSH configuration? (Choose three.)
Correct
Incorrect
SSH is automatically enabled after the RSA keys are generated. Setting user privilege levels and configuring role-based CLI access are good security practices but are not a requirement of implementing SSH.
Hint
SSH is automatically enabled after the RSA keys are generated. Setting user privilege levels and configuring role-based CLI access are good security practices but are not a requirement of implementing SSH.
-
Question 6 of 58
6. Question
2 pointsWhat are two drawbacks in assigning user privilege levels on a Cisco router? (Choose two.)
Correct
Incorrect
Privilege levels may not provide desired flexibility and specificity because higher levels always inherit commands from lower levels, and commands with multiple keywords give the user access to all commands available for each keyword. Privilege levels cannot specify access control to interfaces, ports, or slots. AAA is not required to set privilege levels, but is required in order to create role-based views. The role of root user does not exist in privilege levels.
Hint
Privilege levels may not provide desired flexibility and specificity because higher levels always inherit commands from lower levels, and commands with multiple keywords give the user access to all commands available for each keyword. Privilege levels cannot specify access control to interfaces, ports, or slots. AAA is not required to set privilege levels, but is required in order to create role-based views. The role of root user does not exist in privilege levels.
-
Question 7 of 58
7. Question
1 pointsWhat is a result of enabling the Cisco IOS image resilience feature?
Correct
Incorrect
The Cisco IOS image resilience feature creates a copy of the IOS image and running configuration (primary bootset) and stores them locally in a hidden file. Once the feature is enabled, it can only be disabled through a console session. Images that are loaded from a remote location, such as a TFTP server, cannot be secured. The Cisco IOS file system prevents secured files from being listed in command output.
Hint
The Cisco IOS image resilience feature creates a copy of the IOS image and running configuration (primary bootset) and stores them locally in a hidden file. Once the feature is enabled, it can only be disabled through a console session. Images that are loaded from a remote location, such as a TFTP server, cannot be secured. The Cisco IOS file system prevents secured files from being listed in command output.
-
Question 8 of 58
8. Question
1 pointsWhat service or protocol does the Secure Copy Protocol rely on to ensure that secure copy transfers are from authorized users?
Correct
Incorrect
Secure Copy Protocol (SCP) is used to securely copy IOS images and configuration files to a SCP server. To perform this, SCP will use SSH connections from users authenticated through AAA.
Hint
Secure Copy Protocol (SCP) is used to securely copy IOS images and configuration files to a SCP server. To perform this, SCP will use SSH connections from users authenticated through AAA.
-
Question 9 of 58
9. Question
1 pointsWhat is a limitation to using OOB management on a large enterprise network?
Correct
Incorrect
OOB management provides a dedicated management network without production traffic. Devices within that network, such as terminal servers, have direct console access for management purposes. Because in-band management runs over the production network, secure tunnels or VPNs may be needed. Failures on the production network may not be communicated to the OOB network administrator because the OOB management network may not be affected.
Hint
OOB management provides a dedicated management network without production traffic. Devices within that network, such as terminal servers, have direct console access for management purposes. Because in-band management runs over the production network, secure tunnels or VPNs may be needed. Failures on the production network may not be communicated to the OOB network administrator because the OOB management network may not be affected.
-
Question 10 of 58
10. Question
1 pointsA syslog server has received the message shown.
*Mar 1 00:07:18.783: %SYS-5-CONFIG_I: Configured from console by vty0 (172.16.45.1)
What can be determined from the syslog message?
Correct
Incorrect
The message shown is a level 5 Log_Notice and displays that a user with an IP address of 172.16.45.1 has configured this device remotely.
Hint
The message shown is a level 5 Log_Notice and displays that a user with an IP address of 172.16.45.1 has configured this device remotely.
-
Question 11 of 58
11. Question
1 pointsWhich service should be disabled on a router to prevent a malicious host from falsely responding to ARP requests with the intent to redirect the Ethernet frames?
Correct
Incorrect
Proxy ARP is a technique used on a device on a network to answer ARP queries for a device on another network. This service should be disabled on a router and the correct default gateway address should be configured (manually or by DHCP) for the normal process of remote network access. CDP and LLDP are device discovery protocols. Reverse ARP is used to resolve IP addresses.
Hint
Proxy ARP is a technique used on a device on a network to answer ARP queries for a device on another network. This service should be disabled on a router and the correct default gateway address should be configured (manually or by DHCP) for the normal process of remote network access. CDP and LLDP are device discovery protocols. Reverse ARP is used to resolve IP addresses.
-
Question 12 of 58
12. Question
3 pointsWhich three forwarding plane services and functions are enabled by the Cisco AutoSecure feature? (Choose three.)
Correct
Incorrect
Cisco Express Forwarding, traffic filtering using ACLs, and Cisco IOS firewall inspection are forwarding plane services and functions. Secure SSH, secure password and login functions, and legal notification using a banner are management plane services and functions.
Hint
Cisco Express Forwarding, traffic filtering using ACLs, and Cisco IOS firewall inspection are forwarding plane services and functions. Secure SSH, secure password and login functions, and legal notification using a banner are management plane services and functions.
-
Question 13 of 58
13. Question
1 pointsWhat is the purpose of AAA accounting?
Correct
Incorrect
AAA accounting collects and reports usage data. This data can be used for such purposes as auditing or billing. AAA authentication is the process of verifying users are who they say they are. AAA authorization is what the users can and cannot do on the network after they are authenticated.
Hint
AAA accounting collects and reports usage data. This data can be used for such purposes as auditing or billing. AAA authentication is the process of verifying users are who they say they are. AAA authorization is what the users can and cannot do on the network after they are authenticated.
-
Question 14 of 58
14. Question
2 pointsWhat are two protocols that are used by AAA to authenticate users against a central database of usernames and password? (Choose two.)
Correct
Incorrect
By using TACACS+ or RADIUS, AAA can authenticate users from a database of usernames and passwords stored centrally on a server such as a Cisco ACS server.
Hint
By using TACACS+ or RADIUS, AAA can authenticate users from a database of usernames and passwords stored centrally on a server such as a Cisco ACS server.
-
Question 15 of 58
15. Question
1 pointsWhat does the keyword default specify when used with the aaa authentication login command?
Correct
Incorrect
The default keyword applies AAA authentication to all console, aux, and vty lines. AAA authentication can be configured to use a AAA server or local usernames/passwords to authenticate users.Hint
The default keyword applies AAA authentication to all console, aux, and vty lines. AAA authentication can be configured to use a AAA server or local usernames/passwords to authenticate users. -
Question 16 of 58
16. Question
1 pointsA user complains about not being able to gain access to the network. What command would be used by the network administrator to determine which AAA method list is being used for this particular user as the user logs on?
Correct
Incorrect
In the debug aaa authenticationcommand output, to quickly identify which method list is being used, look for the GETUSER and GETPASS status messages.Hint
In the debug aaa authenticationcommand output, to quickly identify which method list is being used, look for the GETUSER and GETPASS status messages. -
Question 17 of 58
17. Question
3 pointsWhat are three characteristics of the RADIUS protocol? (Choose three.)
Correct
Incorrect
RADIUS is an open-standard AAA protocol using UDP port 1645 or 1812 for authentication and UDP port 1646 or 1813 for accounting. It combines authentication and authorization into one process; thus, a password is encrypted for transmission while the rest of the packet will be sent in plain text. RADIUS offers the expedited service and more comprehensive accounting desired by remote-access providers but provides lower security and less potential for customization than TACACS+.Hint
RADIUS is an open-standard AAA protocol using UDP port 1645 or 1812 for authentication and UDP port 1646 or 1813 for accounting. It combines authentication and authorization into one process; thus, a password is encrypted for transmission while the rest of the packet will be sent in plain text. RADIUS offers the expedited service and more comprehensive accounting desired by remote-access providers but provides lower security and less potential for customization than TACACS+. -
Question 18 of 58
18. Question
2 pointsA network administrator is configuring an AAA server to manage RADIUS authentication. Which two features are included in RADIUS authentication? (Choose two.)
Correct
Incorrect
RADIUS authentication supports the following features:RADIUS authentication and authorization as one process
Encrypts only the password
Utilizes UDP
Supports remote-access technologies, 802.1X, and Session Initiation Protocol (SIP)Hint
RADIUS authentication supports the following features:RADIUS authentication and authorization as one process
Encrypts only the password
Utilizes UDP
Supports remote-access technologies, 802.1X, and Session Initiation Protocol (SIP) -
Question 19 of 58
19. Question
2 pointsA network administrator is configuring an AAA server to manage TACACS+ authentication. What are two attributes of TACACS+ authentication? (Choose two.)
Correct
Incorrect
TACACS+ authentication includes the following attributes:
Separates authentication and authorization processes
Encrypts all communication, not just passwords
Utilizes TCP port 49Hint
TACACS+ authentication includes the following attributes:
Separates authentication and authorization processes
Encrypts all communication, not just passwords
Utilizes TCP port 49 -
Question 20 of 58
20. Question
1 pointsWhat type of ACL offers greater flexibility and control over network access?
Correct
Incorrect
The two types of ACLs are standard and extended. Both types can be named or numbered, but extended ACLs offer greater flexibility.
Hint
The two types of ACLs are standard and extended. Both types can be named or numbered, but extended ACLs offer greater flexibility.
-
Question 21 of 58
21. Question
1 pointsWhich statement accurately describes Cisco IOS Zone-Based Policy Firewall operation?
Correct
Incorrect
The pass action allows traffic only in one direction. Interfaces automatically become members of the self zone. Interfaces are assigned to zones in interface configuration mode, but most configuration takes place in global configuration mode and associated submodes. Interfaces can belong to only one zone at any time.
Hint
The pass action allows traffic only in one direction. Interfaces automatically become members of the self zone. Interfaces are assigned to zones in interface configuration mode, but most configuration takes place in global configuration mode and associated submodes. Interfaces can belong to only one zone at any time.
-
Question 22 of 58
22. Question
1 pointsHow are Intrusion Prevention System (IPS) and Intrusion Detection System (IDS) components used conjunctively?
Correct
Incorrect
IDS sensors are typically deployed in offline mode. Although they do not stop the triggered packets immediately, they have no impact on network performance and hence can be configured to identify a broader scope of activities. IPS sensors can be configured to perform a packet drop to stop the trigger packet. However, because they are deployed inline, inspection of heavy traffic flow could have a negative impact on network performance. IDS and IPS technologies can complement each other. For example, an IDS can be implemented to validate IPS operation because the IDS can be configured for deeper packet inspection offline. This allows the IPS to focus on fewer but more critical traffic patterns inline.
Hint
IDS sensors are typically deployed in offline mode. Although they do not stop the triggered packets immediately, they have no impact on network performance and hence can be configured to identify a broader scope of activities. IPS sensors can be configured to perform a packet drop to stop the trigger packet. However, because they are deployed inline, inspection of heavy traffic flow could have a negative impact on network performance. IDS and IPS technologies can complement each other. For example, an IDS can be implemented to validate IPS operation because the IDS can be configured for deeper packet inspection offline. This allows the IPS to focus on fewer but more critical traffic patterns inline.
-
Question 23 of 58
23. Question
1 pointsWhat is an advantage of HIPS that is not provided by IDS?
Correct
Incorrect
Network-based IDS (NIDS) sensors are typically deployed in offline mode. They do not protect individual hosts. Host-based IPS (HIPS) is software installed on a single host to monitor and analyze suspicious activity. It can monitor and protect operating system and critical system processes that are specific to that host. HIPS can be thought of as a combination of antivirus software, antimalware software, and a firewall.
Hint
Network-based IDS (NIDS) sensors are typically deployed in offline mode. They do not protect individual hosts. Host-based IPS (HIPS) is software installed on a single host to monitor and analyze suspicious activity. It can monitor and protect operating system and critical system processes that are specific to that host. HIPS can be thought of as a combination of antivirus software, antimalware software, and a firewall.
-
Question 24 of 58
24. Question
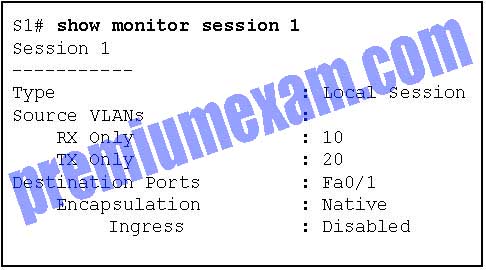
1 pointsRefer to the exhibit. Based on the output generated by the show monitor session 1 command, how will SPAN operate on the switch?
Correct
Incorrect
The show monitor session command is used to verify how SPAN is configured (what ports are involved in the traffic mirroring).Hint
The show monitor session command is used to verify how SPAN is configured (what ports are involved in the traffic mirroring). -
Question 25 of 58
25. Question
1 pointsWhat term describes a set of rules used by an IDS or IPS to detect typical intrusion activity?
Correct
Incorrect
A signature is a set of rules that an IDS and an IPS use to detect typical intrusion activity, such as DoS attacks. These signatures uniquely identify specific worms, viruses, protocol anomalies, and malicious traffic.
Hint
A signature is a set of rules that an IDS and an IPS use to detect typical intrusion activity, such as DoS attacks. These signatures uniquely identify specific worms, viruses, protocol anomalies, and malicious traffic.
-
Question 26 of 58
26. Question
1 pointsWhich router component determines the number of signatures and engines that can be supported in an IPS implementation?
Correct
Incorrect
The number of signatures and engines that can be adequately supported depends on the amount of available memory .
Hint
The number of signatures and engines that can be adequately supported depends on the amount of available memory .
-
Question 27 of 58
27. Question
1 pointsA company deploys a network-based IPS. Which statement describes a false negative alarm that is issued by the IPS sensor?
Correct
Incorrect
The four IDS/IPS alarm types are:
False Positive – A normal user packet passes and an alarm is generated.
False Negative – An attack packet passes and no alarm is generated.
True Positive – An attack packet passes and an alarm is generated.
True Negative – A normal user packet passes and no alarm is generated.Hint
The four IDS/IPS alarm types are:
False Positive – A normal user packet passes and an alarm is generated.
False Negative – An attack packet passes and no alarm is generated.
True Positive – An attack packet passes and an alarm is generated.
True Negative – A normal user packet passes and no alarm is generated. -
Question 28 of 58
28. Question
1 pointsWhich statement describes the Cisco Cloud Web Security?
Correct
Incorrect
The Cisco Cloud Web Security (CWS) is a cloud-based security service that uses web proxies in the Cisco cloud environment to scan traffic for malware and policy enforcement. It is not a firewall or web server solution. The Cisco Web Security Appliance (WSA) combines multiple security solutions to provide an all-in-one solution on a single platform to address the challenges of securing and controlling web traffic.
Hint
The Cisco Cloud Web Security (CWS) is a cloud-based security service that uses web proxies in the Cisco cloud environment to scan traffic for malware and policy enforcement. It is not a firewall or web server solution. The Cisco Web Security Appliance (WSA) combines multiple security solutions to provide an all-in-one solution on a single platform to address the challenges of securing and controlling web traffic.
-
Question 29 of 58
29. Question
1 pointsWhat ports can receive forwarded traffic from an isolated port that is part of a PVLAN?
Correct
Incorrect
PVLANs are used to provide Layer 2 isolation between ports within the same broadcast domain. The level of isolation can be specified
with three types of PVLAN ports:- Promiscuous ports that can forward traffic to all other ports
- Isolated ports that can only forward traffic to promiscuous ports
- Community ports that can forward traffic to other community ports and promiscuous ports
Hint
PVLANs are used to provide Layer 2 isolation between ports within the same broadcast domain. The level of isolation can be specified
with three types of PVLAN ports:- Promiscuous ports that can forward traffic to all other ports
- Isolated ports that can only forward traffic to promiscuous ports
- Community ports that can forward traffic to other community ports and promiscuous ports
-
Question 30 of 58
30. Question
1 pointsWhich type of VLAN-hopping attack may be prevented by designating an unused VLAN as the native VLAN?
Correct
Incorrect
Spoofing DTP messages forces a switch into trunking mode as part of a VLAN-hopping attack, but VLAN double tagging works even if trunk ports are disabled. Changing the native VLAN from the default to an unused VLAN reduces the possibility of this type of attack. DHCP spoofing and DHCP starvation exploit vulnerabilities in the DHCP message exchange.
Hint
Spoofing DTP messages forces a switch into trunking mode as part of a VLAN-hopping attack, but VLAN double tagging works even if trunk ports are disabled. Changing the native VLAN from the default to an unused VLAN reduces the possibility of this type of attack. DHCP spoofing and DHCP starvation exploit vulnerabilities in the DHCP message exchange.
-
Question 31 of 58
31. Question
1 pointsHow can DHCP spoofing attacks be mitigated?
Correct
Incorrect
One of the procedures to prevent a VLAN hopping attack is to disable DTP (auto trunking) negotiations on nontrunking ports. DHCP spoofing attacks can be mitigated by using DHCP snooping on trusted ports. The ip verify source interface configuration command is used to enable IP Source Guard on untrusted ports to protect against MAC and IP address spoofing.
Hint
One of the procedures to prevent a VLAN hopping attack is to disable DTP (auto trunking) negotiations on nontrunking ports. DHCP spoofing attacks can be mitigated by using DHCP snooping on trusted ports. The ip verify source interface configuration command is used to enable IP Source Guard on untrusted ports to protect against MAC and IP address spoofing.
-
Question 32 of 58
32. Question
1 pointsWhat is the result of a DHCP starvation attack?
Correct
Incorrect
DCHP starvation attacks are launched by an attacker with the intent to create a DoS for DHCP clients. To accomplish this goal, the attacker uses a tool that sends many DHCPDISCOVER messages to lease the entire pool of available IP addresses, thus denying them to legitimate hosts.
Hint
DCHP starvation attacks are launched by an attacker with the intent to create a DoS for DHCP clients. To accomplish this goal, the attacker uses a tool that sends many DHCPDISCOVER messages to lease the entire pool of available IP addresses, thus denying them to legitimate hosts.
-
Question 33 of 58
33. Question
1 pointsOn what switch ports should PortFast be enabled to enhance STP stability?
Correct
Incorrect
PortFast will immediately bring an interface configured as an access or trunk port to the forwarding state from a blocking state, bypassing the listening and learning states. If configured on a trunk link, immediately transitioning to the forwarding state could lead to the formation of Layer 2 loops.
Hint
PortFast will immediately bring an interface configured as an access or trunk port to the forwarding state from a blocking state, bypassing the listening and learning states. If configured on a trunk link, immediately transitioning to the forwarding state could lead to the formation of Layer 2 loops.
-
Question 34 of 58
34. Question
1 pointsWhat can be used as an alternative to HMAC?
Correct
Incorrect
Both HMAC and digital signatures are used to guarantee that messages are authentic. MD5 and SHA are considered legacy algorithms that should be avoided because they have security flaws. Encryption algorithms ensure data confidentiality rather than authentication.
Hint
Both HMAC and digital signatures are used to guarantee that messages are authentic. MD5 and SHA are considered legacy algorithms that should be avoided because they have security flaws. Encryption algorithms ensure data confidentiality rather than authentication.
-
Question 35 of 58
35. Question
1 pointsWhat is a characteristic of asymmetric algorithms?
Correct
Incorrect
Asymmetric algorithms do not require a preshared key, which makes key management simpler. The longer key lengths that are used by asymmetric algorithms result in slower execution by devices.
Hint
Asymmetric algorithms do not require a preshared key, which makes key management simpler. The longer key lengths that are used by asymmetric algorithms result in slower execution by devices.
-
Question 36 of 58
36. Question
1 pointsWhy is Diffie-Hellman algorithm typically avoided for encrypting data?
Correct
Incorrect
Diffie-Hellman (DH) is an asymmetric mathematical algorithm that is too slow for encrypting large amounts of data. The longer key length and complexity of DH make it ideal for generating the keys used by symmetric algorithms. Symmetric algorithms typically encrypt the data, whereas DH creates the keys they use.
Hint
Diffie-Hellman (DH) is an asymmetric mathematical algorithm that is too slow for encrypting large amounts of data. The longer key length and complexity of DH make it ideal for generating the keys used by symmetric algorithms. Symmetric algorithms typically encrypt the data, whereas DH creates the keys they use.
-
Question 37 of 58
37. Question
2 pointsWhich two statements describe the use of asymmetric algorithms? (Choose two.)
Correct
Incorrect
Asymmetric algorithms use two keys: a public key and a private key. Both keys are capable of the encryption process, but the complementary matched key is required for decryption. If a public key encrypts the data, the matching private key decrypts the data. The opposite is also true. If a private key encrypts the data, the corresponding public key decrypts the data.
Hint
Asymmetric algorithms use two keys: a public key and a private key. Both keys are capable of the encryption process, but the complementary matched key is required for decryption. If a public key encrypts the data, the matching private key decrypts the data. The opposite is also true. If a private key encrypts the data, the corresponding public key decrypts the data.
-
Question 38 of 58
38. Question
1 pointsA security technician uses an asymmetric algorithm to encrypt messages with a private key and then forwards that data to another technician. What key must be used to decrypt this data?
Correct
Incorrect
Asymmetric algorithms use two keys. if a public key encrypts the data, the matching private key decrypts the data. The opposite is also true. If a private key encrypts the data, the corresponding public key decrypts the data.
Hint
Asymmetric algorithms use two keys. if a public key encrypts the data, the matching private key decrypts the data. The opposite is also true. If a private key encrypts the data, the corresponding public key decrypts the data.
-
Question 39 of 58
39. Question
1 pointsA company deploys a hub-and-spoke VPN topology where the security appliance is the hub and the remote VPN networks are the spokes. Which VPN method should be used in order for one spoke to communicate with another spoke through the single public interface of the security appliance?
Correct
Incorrect
Hairpinning allows VPN traffic received on a single interface to be routed back out that same interface. Split tunneling allows traffic that originates from a remote-access client to be split according to whether the traffic must cross a VPN or the traffic is destined for the public Internet. MPLS and GRE are two types of Layer 3 VPNs.
Hint
Hairpinning allows VPN traffic received on a single interface to be routed back out that same interface. Split tunneling allows traffic that originates from a remote-access client to be split according to whether the traffic must cross a VPN or the traffic is destined for the public Internet. MPLS and GRE are two types of Layer 3 VPNs.
-
Question 40 of 58
40. Question
1 pointsWhat algorithm is used with IPsec to provide data confidentiality?
Correct
Incorrect
The IPsec framework uses various protocols and algorithms to provide data confidentiality, data integrity, authentication, and secure key exchange. Two popular algorithms that are used to ensure that data is not intercepted and modified (data integrity) are MD5 and SHA. AES is an encryption protocol and provides data confidentiality. DH (Diffie-Hellman) is an algorithm that is used for key exchange. RSA is an algorithm that is used for authentication.
Hint
The IPsec framework uses various protocols and algorithms to provide data confidentiality, data integrity, authentication, and secure key exchange. Two popular algorithms that are used to ensure that data is not intercepted and modified (data integrity) are MD5 and SHA. AES is an encryption protocol and provides data confidentiality. DH (Diffie-Hellman) is an algorithm that is used for key exchange. RSA is an algorithm that is used for authentication.
-
Question 41 of 58
41. Question
1 pointsWhat is the function of the Hashed Message Authentication Code (HMAC) algorithm in setting up an IPsec VPN?
Correct
Incorrect
The IPsec framework uses various protocols and algorithms to provide data confidentiality, data integrity, authentication, and secure key exchange. The Hashed Message Authentication Code (HMAC) is a data integrity algorithm that uses a hash value to guarantee the integrity of a message.
Hint
The IPsec framework uses various protocols and algorithms to provide data confidentiality, data integrity, authentication, and secure key exchange. The Hashed Message Authentication Code (HMAC) is a data integrity algorithm that uses a hash value to guarantee the integrity of a message.
-
Question 42 of 58
42. Question
1 pointsWhat is the next step in the establishment of an IPsec VPN after IKE Phase 1 is complete?
Correct
Incorrect
Establishing an IPsec tunnel involves five steps:
detection of interesting traffic defined by an ACL
IKE Phase 1 in which peers negotiate ISAKMP SA policy
IKE Phase 2 in which peers negotiate IPsec SA policy
Creation of the IPsec tunnel
Termination of the IPsec tunnelHint
Establishing an IPsec tunnel involves five steps:
detection of interesting traffic defined by an ACL
IKE Phase 1 in which peers negotiate ISAKMP SA policy
IKE Phase 2 in which peers negotiate IPsec SA policy
Creation of the IPsec tunnel
Termination of the IPsec tunnel -
Question 43 of 58
43. Question
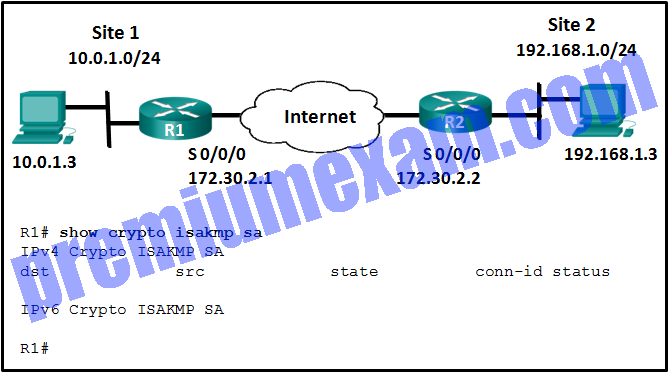
1 pointsRefer to the exhibit. The ISAKMP policy for the IKE Phase 1 tunnel was configured, but the tunnel does not yet exist. Which action should be taken next before IKE Phase 1 negotiations can begin?
Correct
Incorrect
Although the ISAKMP policy for the IKE Phase 1 tunnel is configured, the tunnel does not yet exist as verified with the show crypto isakmp sa command. Interesting traffic must be detected before IKE Phase 1 negotiations can begin. To define interesting traffic, each router has to be configured with an ACL to permit traffic from the local LAN to the remote LAN.Hint
Although the ISAKMP policy for the IKE Phase 1 tunnel is configured, the tunnel does not yet exist as verified with the show crypto isakmp sa command. Interesting traffic must be detected before IKE Phase 1 negotiations can begin. To define interesting traffic, each router has to be configured with an ACL to permit traffic from the local LAN to the remote LAN. -
Question 44 of 58
44. Question
1 pointsWhich feature is specific to the Security Plus upgrade license of an ASA 5505 and provides increased availability?
Correct
Incorrect
The Security Plus upgrade license enables the ASA 5505 to support redundant ISP connections and stateless active/standby high-availability services.
Hint
The Security Plus upgrade license enables the ASA 5505 to support redundant ISP connections and stateless active/standby high-availability services.
-
Question 45 of 58
45. Question
1 pointsWhat is a characteristic of a DMZ zone?
Correct
Incorrect
The characteristics of a DMZ zone are as follows:Traffic originating from the inside network going to the DMZ network is permitted.
Traffic originating from the outside network going to the DMZ network is selectively permitted.
Traffic originating from the DMZ network going to the inside network is denied.Hint
The characteristics of a DMZ zone are as follows:Traffic originating from the inside network going to the DMZ network is permitted.
Traffic originating from the outside network going to the DMZ network is selectively permitted.
Traffic originating from the DMZ network going to the inside network is denied. -
Question 46 of 58
46. Question
1 pointsWhat technology is used to separate physical interfaces on the ASA 5505 device into different security zones?
Correct
Incorrect
For an ASA 5505, common deployments use a specific VLAN with a higher security level for an inside network and a separate VLAN with a lower security level for the outside network.
Hint
For an ASA 5505, common deployments use a specific VLAN with a higher security level for an inside network and a separate VLAN with a lower security level for the outside network.
-
Question 47 of 58
47. Question
1 pointsWhat is the default preconfigured security level for the outside network interface on a Cisco ASA 5505?
Correct
Incorrect
By default the Cisco ASA ships with two interfaces preconfigured: interface VLAN 1 for the inside network with a security level of 100 and VLAN 2 for outside network with a security level of 0.
Hint
By default the Cisco ASA ships with two interfaces preconfigured: interface VLAN 1 for the inside network with a security level of 100 and VLAN 2 for outside network with a security level of 0.
-
Question 48 of 58
48. Question
1 pointsWhat can be configured as part of a network object?
Correct
Incorrect
There are two types of objects that can be configured on the Cisco ASA 5505: network objects and service objects. Network objects can be configured with an IP address and mask. Service objects can be configured with a protocol or port ranges.
Hint
There are two types of objects that can be configured on the Cisco ASA 5505: network objects and service objects. Network objects can be configured with an IP address and mask. Service objects can be configured with a protocol or port ranges.
-
Question 49 of 58
49. Question
1 pointsWhich interface setting can be configured in ASDM through the Device Setup tab?
Correct
Incorrect
In the Device Setup tab, the ASA Layer 3 interfaces can be created, edited, or deleted. Name, security level, and IP address are some of the settings that can be configured on an interface. There is no NAT, port security, or EtherChannel configuration in this tab.
Hint
In the Device Setup tab, the ASA Layer 3 interfaces can be created, edited, or deleted. Name, security level, and IP address are some of the settings that can be configured on an interface. There is no NAT, port security, or EtherChannel configuration in this tab.
-
Question 50 of 58
50. Question
1 pointsWhat is a characteristic of an ASA site-to-site VPN?
Correct
Incorrect
An ASA site-to-site VPN creates a secure LAN-to-LAN connection. The VPN can be established with another ASA or ISR router. Pings can be issued to test the tunnel established between devices. The first echo request packet sent to the remote host fails, but then the others succeed because the devices must negotiate the tunnel parameters.
Hint
An ASA site-to-site VPN creates a secure LAN-to-LAN connection. The VPN can be established with another ASA or ISR router. Pings can be issued to test the tunnel established between devices. The first echo request packet sent to the remote host fails, but then the others succeed because the devices must negotiate the tunnel parameters.
-
Question 51 of 58
51. Question
2 pointsWhich two end points can be on the other side of an ASA site-to-site VPN configured using ASDM? (Choose two.)
Correct
Incorrect
ASDM supports creating an ASA site-to-site VPN between two ASAs or between an ASA and an ISR router.
Hint
ASDM supports creating an ASA site-to-site VPN between two ASAs or between an ASA and an ISR router.
-
Question 52 of 58
52. Question
1 pointsWhich type of ASDM connection would provide secure remote access for remote users into corporate networks?
Correct
Incorrect
The ASDM Launcher is an option used to run Cisco ASDM as a local application instead of through a browser. The other option is to run ASDM as a Java Web Start application through a browser. The site-to-site VPN option is used to connect an ASA to a remote ASA or ISR router. Cisco AnyConnect SSL VPN provides remote users with secure access to corporate networks.
Hint
The ASDM Launcher is an option used to run Cisco ASDM as a local application instead of through a browser. The other option is to run ASDM as a Java Web Start application through a browser. The site-to-site VPN option is used to connect an ASA to a remote ASA or ISR router. Cisco AnyConnect SSL VPN provides remote users with secure access to corporate networks.
-
Question 53 of 58
53. Question
1 pointsA security technician is evaluating a new operations security proposal designed to limit access to all servers. What is an advantage of using network security testing to evaluate the new proposal?
Correct
Incorrect
Network security testing can evaluate the effectiveness of an operations security solution without having to wait for a real threat to take place. However, this type of testing should be conducted periodically, versus just once. It is effective to evaluate many different tasks when it is conducted during both the implementation and operational stages.
Hint
Network security testing can evaluate the effectiveness of an operations security solution without having to wait for a real threat to take place. However, this type of testing should be conducted periodically, versus just once. It is effective to evaluate many different tasks when it is conducted during both the implementation and operational stages.
-
Question 54 of 58
54. Question
1 pointsWhat information does the SIEM network security management tool provide to network administrators?
Correct
Incorrect
SIEM, which is a combination of Security Information Management and Security Event Management products, is used for forensic analysis and provides real-time reporting of security events.
Hint
SIEM, which is a combination of Security Information Management and Security Event Management products, is used for forensic analysis and provides real-time reporting of security events.
-
Question 55 of 58
55. Question
3 pointsWhat three tasks can a network administrator accomplish with the Nmap and Zenmap security testing tools? (Choose three.)
Correct
Incorrect
Nmap is a low-level network scanner that is available to the public and that has the ability to perform port scanning, to identify open TCP and UDP ports, and which can also perform system identification. It can also be used to identify Layer 3 protocols that are running on a system. Zenmap is the GUI version of Nmap.
Hint
Nmap is a low-level network scanner that is available to the public and that has the ability to perform port scanning, to identify open TCP and UDP ports, and which can also perform system identification. It can also be used to identify Layer 3 protocols that are running on a system. Zenmap is the GUI version of Nmap.
-
Question 56 of 58
56. Question
1 pointsWhich security document includes implementation details, usually with step-by-step instructions and graphics?
Correct
Incorrect
Of the three types of security policy documents (standards, guidelines, and procedures), it is the procedure document that includes details such as step-by-step instructions and graphics.
Hint
Of the three types of security policy documents (standards, guidelines, and procedures), it is the procedure document that includes details such as step-by-step instructions and graphics.
-
Question 57 of 58
57. Question
1 pointsWhich service is added to the Cisco ASA 5500 by the ASA 5500-X?
Correct
Incorrect
The Cisco ASA 5500-X series with FirePOWER service merges the ASA 5500 series devices with some new features such as advanced malware protection as well as application control and URL filtering. The services of ASA virtualization, high availability with failover, and threat control and containment services are already provided by ASA 5500 devices.
Hint
The Cisco ASA 5500-X series with FirePOWER service merges the ASA 5500 series devices with some new features such as advanced malware protection as well as application control and URL filtering. The services of ASA virtualization, high availability with failover, and threat control and containment services are already provided by ASA 5500 devices.
-
Question 58 of 58
58. Question
1 pointsA network analyst inserts a USB drive into an ASA 5506-X device. How is the external storage treated by the IOS?
Correct
Incorrect
On the backplane of an ASA 5506-X device, there is a USB Type A port. If a USB drive is inserted into the port, the external storage device will be mounted as disk1.
Hint
On the backplane of an ASA 5506-X device, there is a USB Type A port. If a USB drive is inserted into the port, the external storage device will be mounted as disk1.