Last Updated on November 1, 2019 by Admin
Implementing Network Security ( Version 2.0) – CCNAS Chapter 9 Exam Online
CCNAS – Chapter 9 Exam
Quiz-summary
0 of 28 questions completed
Questions:
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
Information
CCNAS – Chapter 9 Exam
You have already completed the quiz before. Hence you can not start it again.
Quiz is loading...
You must sign in or sign up to start the quiz.
You have to finish following quiz, to start this quiz:
Results
0 of 28 questions answered correctly
Your time:
Time has elapsed
You have reached 0 of 0 points, (0)
| Average score |
|
| Your score |
|
Categories
- Not categorized 0%
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- Answered
- Review
-
Question 1 of 28
1. Question
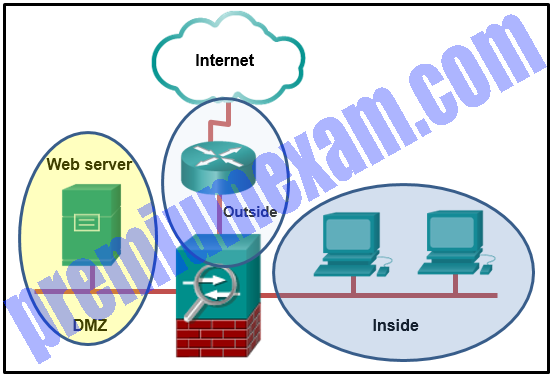
1 pointsRefer to the exhibit. An administrator creates three zones (A, B, and C) in an ASA that filters traffic. Traffic originating from Zone A going to Zone C is denied, and traffic originating from Zone B going to Zone C is denied. What is a possible scenario for Zones A, B, and C?
Correct
Incorrect
ASA protects Network/Zone C (Inside) from unauthorized access by users on a Network/Zone B (Outside). It also denies traffic from Network/Zone A (DMZ) to access the Network/Zone C (Inside).
Hint
ASA protects Network/Zone C (Inside) from unauthorized access by users on a Network/Zone B (Outside). It also denies traffic from Network/Zone A (DMZ) to access the Network/Zone C (Inside).
-
Question 2 of 28
2. Question
1 pointsWhat is one of the drawbacks to using transparent mode operation on an ASA device?
Correct
Incorrect
In transparent mode the ASA functions like a Layer 2 device. An ASA device can have an IP address assigned on the local network for management purposes. The drawbacks to using transparent mode include no support for dynamic routing protocols, VPNs, QoS, or DHCP Relay.
Hint
In transparent mode the ASA functions like a Layer 2 device. An ASA device can have an IP address assigned on the local network for management purposes. The drawbacks to using transparent mode include no support for dynamic routing protocols, VPNs, QoS, or DHCP Relay.
-
Question 3 of 28
3. Question
1 pointsWhat is a characteristic of ASA security levels?
Correct
Incorrect
The ASA assigns security levels to distinguish between inside and outside networks. The higher the level, the more trusted the interface. The security level numbers range between 0 to 100. When traffic moves from an interface with a higher security level to an interface with a lower security level, it is considered outbound traffic.
Hint
The ASA assigns security levels to distinguish between inside and outside networks. The higher the level, the more trusted the interface. The security level numbers range between 0 to 100. When traffic moves from an interface with a higher security level to an interface with a lower security level, it is considered outbound traffic.
-
Question 4 of 28
4. Question
1 pointsRefer to the exhibit. Two types of VLAN interfaces were configured on an ASA 5505 with a Base license. The administrator wants to configure a third VLAN interface with limited functionality. Which action should be taken by the administrator to configure the third interface?
Correct
Incorrect
An ASA 5505 with a Base license does not allow three fully functioning VLAN interfaces to be created, but a third “limited” VLAN interface can be created if it is first configured with the no forward interface vlan command. When the inside and outside VLAN interfaces are configured, the no forward interface vlan number command must be entered before the nameif command is entered on the third interface. The Security Plus license is required to achieve full functionality.
Hint
An ASA 5505 with a Base license does not allow three fully functioning VLAN interfaces to be created, but a third “limited” VLAN interface can be created if it is first configured with the no forward interface vlan command. When the inside and outside VLAN interfaces are configured, the no forward interface vlan number command must be entered before the nameif command is entered on the third interface. The Security Plus license is required to achieve full functionality.
-
Question 5 of 28
5. Question
1 pointsWhat command defines a DHCP pool that uses the maximum number of DHCP client addresses available on an ASA 5505 that is using the Base license?
Correct
Incorrect
The ASA 5505 Base license is a 10-user license and therefore the maximum number of DHCP clients supported is 32. The only pool that contains 32 addresses is the pool with range 192.168.1.25-192.168.1.56
Hint
The ASA 5505 Base license is a 10-user license and therefore the maximum number of DHCP clients supported is 32. The only pool that contains 32 addresses is the pool with range 192.168.1.25-192.168.1.56
-
Question 6 of 28
6. Question
2 pointsWhich two statements are true about ASA standard ACLs? (Choose two.)
Correct
Incorrect
ASA standard ACLs are used to identify the destination IP addresses, unlike IOS ACLs where a standard ACL identifies the source host/network. They are typically only used for OSPF routes and can be used in a route map for OSPF redistribution. Standard access lists cannot be applied to interfaces to control traffic.
Hint
ASA standard ACLs are used to identify the destination IP addresses, unlike IOS ACLs where a standard ACL identifies the source host/network. They are typically only used for OSPF routes and can be used in a route map for OSPF redistribution. Standard access lists cannot be applied to interfaces to control traffic.
-
Question 7 of 28
7. Question
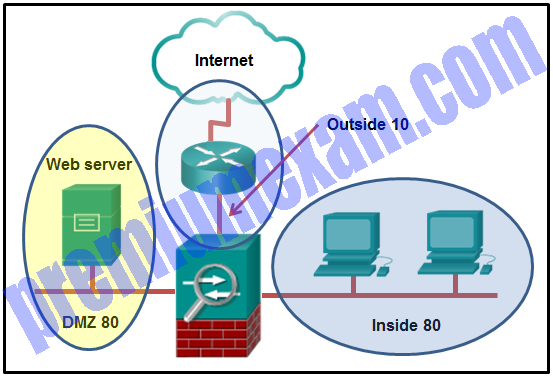
1 pointsRefer to the exhibit. A network administrator is configuring the security level for the ASA. What is a best practice for assigning the security level on the three interfaces?
Correct
Incorrect
The Cisco ASA assigns security levels to distinguish among different networks it connects. Security levels define the level of trustworthiness of an interface. The higher the level, the more trusted the interface. The security level numbers range between 0 (untrustworthy) to 100 (very trustworthy). Therefore, the interface connecting to the Internet should be assigned the lowest level. The interface connecting to the internal network should be assigned the highest level. The interface connecting to the DMZ network should be assigned a level between them.
Hint
The Cisco ASA assigns security levels to distinguish among different networks it connects. Security levels define the level of trustworthiness of an interface. The higher the level, the more trusted the interface. The security level numbers range between 0 (untrustworthy) to 100 (very trustworthy). Therefore, the interface connecting to the Internet should be assigned the lowest level. The interface connecting to the internal network should be assigned the highest level. The interface connecting to the DMZ network should be assigned a level between them.
-
Question 8 of 28
8. Question
1 pointsRefer to the exhibit. A network administrator is configuring the security level for the ASA. Which statement describes the default result if the administrator tries to assign the Inside interface with the same security level as the DMZ interface?
Correct
Incorrect
Multiple interfaces in an ASA can be assigned the same security level. To allow connectivity between interfaces with the same security levels, the same-security-traffic permit inter-interface global configuration command is required. Traffic from the higher level network to the lower level network is allowed by default. However, traffic initiated on the lower level network is denied access to the higher level network by default.Hint
Multiple interfaces in an ASA can be assigned the same security level. To allow connectivity between interfaces with the same security levels, the same-security-traffic permit inter-interface global configuration command is required. Traffic from the higher level network to the lower level network is allowed by default. However, traffic initiated on the lower level network is denied access to the higher level network by default. -
Question 9 of 28
9. Question
1 pointsWhat is a difference between ASA IPv4 ACLs and IOS IPv4 ACLs?
Correct
Incorrect
There are many similarities between ASA ACLs and IOS ACLs, including:
- In both, there is an implicit deny any
- Only one ACL per interface, per protocol, per direction still applies.
- Both use deny and permit ACEs.
- ACLs can be either named or numbered.
ASA ACLs differ from IOS ACLs in that they use a network mask (e.g., 255.255.255.0) instead of a wildcard mask (e.g. 0.0.0.255). Although most ASA ACLs are named, they can also be numbered.
Hint
There are many similarities between ASA ACLs and IOS ACLs, including:
- In both, there is an implicit deny any
- Only one ACL per interface, per protocol, per direction still applies.
- Both use deny and permit ACEs.
- ACLs can be either named or numbered.
ASA ACLs differ from IOS ACLs in that they use a network mask (e.g., 255.255.255.0) instead of a wildcard mask (e.g. 0.0.0.255). Although most ASA ACLs are named, they can also be numbered.
-
Question 10 of 28
10. Question
1 pointsWhat is the purpose of the webtype ACLs in an ASA?
Correct
Incorrect
The webtype ACLs are used in a configuration that supports filtering for clientless SSL VPN users.
Hint
The webtype ACLs are used in a configuration that supports filtering for clientless SSL VPN users.
-
Question 11 of 28
11. Question
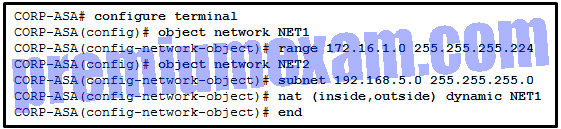
1 pointsRefer to the exhibit. A network administrator has configured NAT on an ASA device. What type of NAT is used?
Correct
Incorrect
NAT can be deployed on an ASA using one of these methods:
- inside NAT – when a host from a higher-security interface has traffic destined for a lower-security interface and the ASA translates the internal host address to a global address
- outside NAT – when traffic from a lower-security interface destined for a host on the higher-security interface is translated
- bidirectional NAT – when both inside NAT and outside NAT are used together
Because the nat command is applied so that the inside interface is mapped to the outside interface, the NAT type is inside. Also, the dynamic keyword in the nat command indicates that it is a dynamic mapping.
Hint
NAT can be deployed on an ASA using one of these methods:
- inside NAT – when a host from a higher-security interface has traffic destined for a lower-security interface and the ASA translates the internal host address to a global address
- outside NAT – when traffic from a lower-security interface destined for a host on the higher-security interface is translated
- bidirectional NAT – when both inside NAT and outside NAT are used together
Because the nat command is applied so that the inside interface is mapped to the outside interface, the NAT type is inside. Also, the dynamic keyword in the nat command indicates that it is a dynamic mapping.
-
Question 12 of 28
12. Question
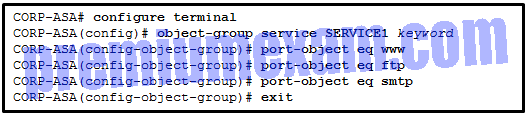
1 pointsRefer to the exhibit. A network administrator is configuring an object group on an ASA device. Which configuration keyword should be used after the object group name SERVICE1?
Correct
Incorrect
Because this is a service object group, the keyword should indicate which protocol is used. The options are tcp, udp, tcp-udp, icmp, and icmpv6. The subsequent commands indicate that the services in the group are WWW, FTP, and SMTP. Because all of these protocols use TCP, the keyword in the service object group should be tcp.Hint
Because this is a service object group, the keyword should indicate which protocol is used. The options are tcp, udp, tcp-udp, icmp, and icmpv6. The subsequent commands indicate that the services in the group are WWW, FTP, and SMTP. Because all of these protocols use TCP, the keyword in the service object group should be tcp. -
Question 13 of 28
13. Question
2 pointsWhen dynamic NAT on an ASA is being configured, what two parameters must be specified by network objects? (Choose two.)
Correct
Incorrect
On an ASA, both the pool of addresses that will be used as inside global address and the range of internal private addresses that should be translated are configured through network objects.
Hint
On an ASA, both the pool of addresses that will be used as inside global address and the range of internal private addresses that should be translated are configured through network objects.
-
Question 14 of 28
14. Question
1 pointsWhat function is performed by the class maps configuration object in the Cisco modular policy framework?
Correct
Incorrect
There are three configuration objects in the MPF; class maps, policy maps, and service policy. The class maps configuration object uses match criteria to identify interesting traffic.
Hint
There are three configuration objects in the MPF; class maps, policy maps, and service policy. The class maps configuration object uses match criteria to identify interesting traffic.
-
Question 15 of 28
15. Question
1 pointsRefer to the exhibit. Based on the security levels of the interfaces on ASA1, what traffic will be allowed on the interfaces?
Correct
Incorrect
ASA devices have security levels assigned to each interface that are not part of a configured ACL. These security levels allow traffic from more secure interfaces, such as security level 100, to access less secure interfaces, such as level 0. By default, they allow traffic from more secure interfaces (higher security level) to access less secure interfaces (lower security level). Traffic from the less secure interfaces is blocked from accessing more secure interfaces.
Hint
ASA devices have security levels assigned to each interface that are not part of a configured ACL. These security levels allow traffic from more secure interfaces, such as security level 100, to access less secure interfaces, such as level 0. By default, they allow traffic from more secure interfaces (higher security level) to access less secure interfaces (lower security level). Traffic from the less secure interfaces is blocked from accessing more secure interfaces.
-
Question 16 of 28
16. Question
3 pointsWhat are three characteristics of the ASA routed mode? (Choose three.)
Correct
Incorrect
Routed mode is the traditional mode for deploying a firewall where there are two or more interfaces that separate Layer 3 networks. The ASA is considered to be a router hop in the network and can perform NAT between connected networks. Routed mode supports multiple interfaces. Each interface is on a different subnet and requires an IP address on that subnet.
Hint
Routed mode is the traditional mode for deploying a firewall where there are two or more interfaces that separate Layer 3 networks. The ASA is considered to be a router hop in the network and can perform NAT between connected networks. Routed mode supports multiple interfaces. Each interface is on a different subnet and requires an IP address on that subnet.
-
Question 17 of 28
17. Question
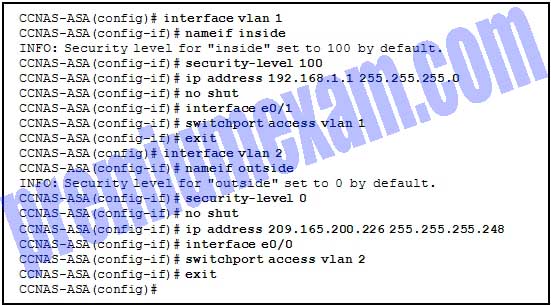
1 pointsRefer to the exhibit. An administrator has configured an ASA 5505 as indicated but is still unable to ping the inside interface from an inside host. What is the cause of this problem?
Correct
Incorrect
VLAN 1 and VLAN 2 have been configured correctly. Neither e0/0 nor e0/1 have been activated. For an inside host to ping the inside interface would require activating the e0/1 interface.
Hint
VLAN 1 and VLAN 2 have been configured correctly. Neither e0/0 nor e0/1 have been activated. For an inside host to ping the inside interface would require activating the e0/1 interface.
-
Question 18 of 28
18. Question
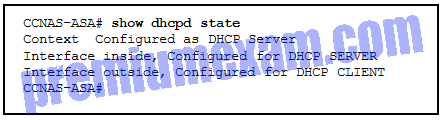
3 pointsRefer to the exhibit. According to the command output, which three statements are true about the DHCP options entered on the ASA 5505? (Choose three.)
Correct
Incorrect
-
Question 19 of 28
19. Question
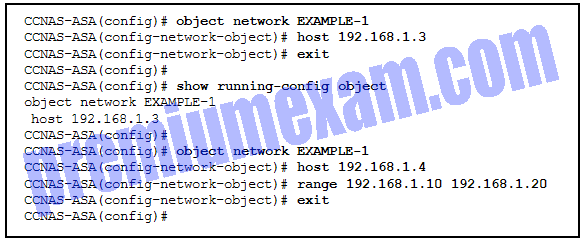
1 pointsRefer to the exhibit. What will be displayed in the output of the show running-config object command after the exhibited configuration commands are entered on an ASA 5505?
Correct
Incorrect
The show running-config object command is used to display or verify the IP address/mask pair within the object. There can only be one statement in the network object. Entering a second IP address/mask pair will replace the existing configuration.Hint
The show running-config object command is used to display or verify the IP address/mask pair within the object. There can only be one statement in the network object. Entering a second IP address/mask pair will replace the existing configuration. -
Question 20 of 28
20. Question
1 pointsWhat must be configured on a Cisco ASA device to support local authentication?
Correct
Incorrect
An ASA can be configured to authenticate by using a local user database or an external server, or both. Local authentication on a Cisco ASA requires the configuration of AAA on the ASA.
Hint
An ASA can be configured to authenticate by using a local user database or an external server, or both. Local authentication on a Cisco ASA requires the configuration of AAA on the ASA.
-
Question 21 of 28
21. Question
1 pointsWhich statement describes a difference between the Cisco ASA IOS CLI feature and the router IOS CLI feature?
Correct
Incorrect
The ASA CLI is a proprietary OS which has a similar look and feel to the Cisco router IOS. Although it shares some common features with the router IOS, it has its unique features. For example, an ASA CLI command can be executed regardless of the current configuration mode prompt. The IOS do command is not required or recognized. Both the ASA CLI and the router CLI use the # symbol to indicate the EXEC mode. Both CLIs use the Tab key to complete a partially typed command. Different from the router IOS, the ASA provides a help command that provides a brief command description and syntax for certain commands.
Hint
The ASA CLI is a proprietary OS which has a similar look and feel to the Cisco router IOS. Although it shares some common features with the router IOS, it has its unique features. For example, an ASA CLI command can be executed regardless of the current configuration mode prompt. The IOS do command is not required or recognized. Both the ASA CLI and the router CLI use the # symbol to indicate the EXEC mode. Both CLIs use the Tab key to complete a partially typed command. Different from the router IOS, the ASA provides a help command that provides a brief command description and syntax for certain commands.
-
Question 22 of 28
22. Question
2 pointsWhat are two factory default configurations on an ASA 5505? (Choose two.)
Correct
Incorrect
The ASA 5505 ships with a default configuration that includes the following:
- VLAN 1 – for the inside network with security level 100.
- VLAN 2 – for the outside network with security level 0 and it should acquire its IP address and default route from an upstream device.
- PAT is configured so that inside host addresses are translated using the outside interface IP address.
- HTTP access for ASDM is enabled.
- DHCP services are provided to the inside hosts.
Hint
The ASA 5505 ships with a default configuration that includes the following:
- VLAN 1 – for the inside network with security level 100.
- VLAN 2 – for the outside network with security level 0 and it should acquire its IP address and default route from an upstream device.
- PAT is configured so that inside host addresses are translated using the outside interface IP address.
- HTTP access for ASDM is enabled.
- DHCP services are provided to the inside hosts.
-
Question 23 of 28
23. Question
1 pointsWhich type of NAT would be used on an ASA where 10.0.1.0/24 inside addresses are to be translated only if traffic from these addresses is destined for the 198.133.219.0/24 network?
Correct
Incorrect
Policy NAT is based on rules that determine when specific source addresses will get translated. Those source addresses are intended for specific destination addresses or for specific ports or for both a destination address and a specific port.
Hint
Policy NAT is based on rules that determine when specific source addresses will get translated. Those source addresses are intended for specific destination addresses or for specific ports or for both a destination address and a specific port.
-
Question 24 of 28
24. Question
1 pointsWhich statement describes a feature of AAA in an ASA device?
Correct
Incorrect
AAA services (authentication, authorization, and accounting) are disabled by default. Authentication can be used alone or with authorization and accounting. Authorization always requires a user to be authenticated first. Accounting can be used alone, or with authentication and authorization. Authorization controls the services and commands that are available to each authenticated user. If authorization is not enabled, authentication would provide the same access to services for all authenticated users.
Hint
AAA services (authentication, authorization, and accounting) are disabled by default. Authentication can be used alone or with authorization and accounting. Authorization always requires a user to be authenticated first. Accounting can be used alone, or with authentication and authorization. Authorization controls the services and commands that are available to each authenticated user. If authorization is not enabled, authentication would provide the same access to services for all authenticated users.
-
Question 25 of 28
25. Question
1 pointsA network administrator is working on the implementation of the Cisco Modular Policy Framework on an ASA device. The administrator issues a clear service-policy command. What is the effect after this command is entered?
Correct
Incorrect
In an MPF implementation, the clear service-policy command clears the service policy statistics. The clear configure service-policy command in global configuration mode removes all service policies.Hint
In an MPF implementation, the clear service-policy command clears the service policy statistics. The clear configure service-policy command in global configuration mode removes all service policies. -
Question 26 of 28
26. Question
1 pointsWhat is needed to allow specific traffic that is sourced on the outside network of an ASA firewall to reach an internal network?
Correct
Incorrect
In order to explicitly permit traffic from an interface with a lower security level to an interface with a higher security level, an ACL must be configured. By default, traffic will only flow from a higher security level to a lower.
Hint
In order to explicitly permit traffic from an interface with a lower security level to an interface with a higher security level, an ACL must be configured. By default, traffic will only flow from a higher security level to a lower.
-
Question 27 of 28
27. Question
2 pointsWhat are two differences between an ASA 5505 and an ASA 5506-X with FirePOWER device? (Choose two.)
Correct
Incorrect
The default DRAM memory is 4 GB in a Cisco ASA 5506-X device. The default DRAM memory in a Cisco ASA 5505 device is 256 MB. Both devices have 8 Ethernet ports in the backplane.However, Ethernet ports in ASA 5505 are switch ports and Ethernet ports in ASA 5506-X are routed ports. Both devices support remote access VPN functions, security level settings, and SSL VPN.
Hint
The default DRAM memory is 4 GB in a Cisco ASA 5506-X device. The default DRAM memory in a Cisco ASA 5505 device is 256 MB. Both devices have 8 Ethernet ports in the backplane.However, Ethernet ports in ASA 5505 are switch ports and Ethernet ports in ASA 5506-X are routed ports. Both devices support remote access VPN functions, security level settings, and SSL VPN.
-
Question 28 of 28
28. Question
1 pointsA network analyst needs to reset an ASA 5506-X device to its default as-shipped state after the next reboot. What is the minimum length of time the RESET pin should be pressed to take the this effect?
Correct
Incorrect
On the backplane of an ASA 5506-X device, there is a RESET pin at the lower right side. If pressed for longer than three seconds, it resets the ASA to its default “as-shipped” state following the next reboot.
Hint
On the backplane of an ASA 5506-X device, there is a RESET pin at the lower right side. If pressed for longer than three seconds, it resets the ASA to its default “as-shipped” state following the next reboot.