Last Updated on November 1, 2019 by Admin
Implementing Network Security ( Version 2.0) – CCNAS Chapter 5 Exam Online
CCNAS – Chapter 5 Exam
Quiz-summary
0 of 23 questions completed
Questions:
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
Information
CCNAS – Chapter 5 Exam
You have already completed the quiz before. Hence you can not start it again.
Quiz is loading...
You must sign in or sign up to start the quiz.
You have to finish following quiz, to start this quiz:
Results
0 of 23 questions answered correctly
Your time:
Time has elapsed
You have reached 0 of 0 points, (0)
| Average score |
|
| Your score |
|
Categories
- Not categorized 0%
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- Answered
- Review
-
Question 1 of 23
1. Question
1 pointsWhat information must an IPS track in order to detect attacks matching a composite signature?
Correct
Incorrect
A composite signature is called a stateful signature. It identifies a sequence of operations distributed across multiple hosts over an arbitrary period of time. Because this type of attack involves multiple packets, an IPS sensor must maintain the state information. However, an IPS sensor cannot maintain the state information indefinitely. A composite signature is configured with a time period to maintain the state for the specific attack when it is first detected. Thus, an IPS may not be able to maintain all the information related to an attack such as total number of packets, total length of attack time, and the amount of bandwidth consumed by the attack.
Hint
A composite signature is called a stateful signature. It identifies a sequence of operations distributed across multiple hosts over an arbitrary period of time. Because this type of attack involves multiple packets, an IPS sensor must maintain the state information. However, an IPS sensor cannot maintain the state information indefinitely. A composite signature is configured with a time period to maintain the state for the specific attack when it is first detected. Thus, an IPS may not be able to maintain all the information related to an attack such as total number of packets, total length of attack time, and the amount of bandwidth consumed by the attack.
-
Question 2 of 23
2. Question
1 pointsWhat is a disadvantage of a pattern-based detection mechanism?
Correct
Incorrect
An IDS/IPS with pattern-based detection, also known as signature-based detection, compares the network traffic to a database of known attacks (signature files) and triggers an alarm or prevents communication if a match is found. The signatures must be created first. Hence this type of intrusion detection cannot detect unknown attacks. It is easy to configure and to deploy. Its operation does not depend on the information of normal network behavior (or baseline).
Hint
An IDS/IPS with pattern-based detection, also known as signature-based detection, compares the network traffic to a database of known attacks (signature files) and triggers an alarm or prevents communication if a match is found. The signatures must be created first. Hence this type of intrusion detection cannot detect unknown attacks. It is easy to configure and to deploy. Its operation does not depend on the information of normal network behavior (or baseline).
-
Question 3 of 23
3. Question
1 pointsWhat is the purpose in configuring an IOS IPS crypto key when enabling IOS IPS on a Cisco router?
Correct
Incorrect
The crypto key verifies the digital signature for the master signature file (sigdef-default.xml). The content of the file is signed by a Cisco private key to guarantee its authenticity and integrity.
Hint
The crypto key verifies the digital signature for the master signature file (sigdef-default.xml). The content of the file is signed by a Cisco private key to guarantee its authenticity and integrity.
-
Question 4 of 23
4. Question
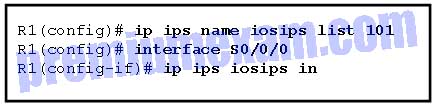
1 pointsRefer to the exhibit. What is the result of issuing the Cisco IOS IPS commands on router R1?
Correct
Incorrect
In configuring IOS IPS with the command ip ips, an optional extended or standard ACL can be used to filter the scanned traffic. All traffic that is permitted by the ACL is subject to inspection by the IPS. Traffic that is denied by the ACL is not inspected by the IPS.Hint
In configuring IOS IPS with the command ip ips, an optional extended or standard ACL can be used to filter the scanned traffic. All traffic that is permitted by the ACL is subject to inspection by the IPS. Traffic that is denied by the ACL is not inspected by the IPS. -
Question 5 of 23
5. Question
2 pointsWhich two benefits does the IPS version 5.x signature format provide over the version 4.x signature format? (Choose two.)
Correct
Incorrect
Since IOS 12.4(11)T, Cisco introduced version 5.x IPS signature format. The new version supports encrypted signature parameters and other features such as signature risk rating, which rates the signature on security risk.
Hint
Since IOS 12.4(11)T, Cisco introduced version 5.x IPS signature format. The new version supports encrypted signature parameters and other features such as signature risk rating, which rates the signature on security risk.
-
Question 6 of 23
6. Question
1 pointsWhich type of IPS signature detection is used to distract and confuse attackers?
Correct
Incorrect
The honeypot-based detection method uses dummy servers to attract attacks. The purpose of the honey pot approach is to distract attacks away from real network devices. After capturing the attack activities on honeypot servers, network administrators can analyze incoming types of attacks and malicious traffic patterns.
Hint
The honeypot-based detection method uses dummy servers to attract attacks. The purpose of the honey pot approach is to distract attacks away from real network devices. After capturing the attack activities on honeypot servers, network administrators can analyze incoming types of attacks and malicious traffic patterns. -
Question 7 of 23
7. Question
1 pointsWhich statement is true about an atomic alert that is generated by an IPS?
Correct
Incorrect
The two main alert generation mechanisms for IDS/IPS devices are atomic and summary alerts. Atomic alerts are generated every time a signature triggers. With a summary alert, a single atomic alert is generated for the first detection of an attack. Then the duplicate alarms are counted, but not sent, for a specific time period. When it reaches the specified time period, an alert is sent that indicates the number of alarms that occurred during the time interval.
Hint
The two main alert generation mechanisms for IDS/IPS devices are atomic and summary alerts. Atomic alerts are generated every time a signature triggers. With a summary alert, a single atomic alert is generated for the first detection of an attack. Then the duplicate alarms are counted, but not sent, for a specific time period. When it reaches the specified time period, an alert is sent that indicates the number of alarms that occurred during the time interval.
-
Question 8 of 23
8. Question
1 pointsA system analyst is configuring and tuning a recently deployed IPS appliance. By examining the IPS alarm log, the analyst notices that the IPS does not generate alarms for a few known attack packets. Which term describes the lack of alarms by the IPS?
Correct
Incorrect
The alarms generated by an IPS can be classified into 4 types:
- A false positive occurs when an IPS generates an alarm on normal user traffic that should not have triggered an alarm.
- A false negative occurs when an IPS fails to generate an alarm after processing attack traffic the IPS is configured to detect.
- A true positive occurs when an IPS generates an alarm in response to known attack traffic.
- A true negative occurs when normal network traffic does not generate an alarm.
Hint
The alarms generated by an IPS can be classified into 4 types:
- A false positive occurs when an IPS generates an alarm on normal user traffic that should not have triggered an alarm.
- A false negative occurs when an IPS fails to generate an alarm after processing attack traffic the IPS is configured to detect.
- A true positive occurs when an IPS generates an alarm in response to known attack traffic.
- A true negative occurs when normal network traffic does not generate an alarm.
-
Question 9 of 23
9. Question
1 pointsA security specialist configures an IPS so that it will generate an alert when an attack is first detected. Alerts for the subsequent detection of the same attack are suppressed for a pre-defined period of time. Another alert will be generated at the end of the period indicating the number of the attack detected. Which IPS alert monitoring mechanism is configured?
Correct
Incorrect
Alerts generated by an IPS should be monitored closely to ensure proper actions are taken against malicious attacks. IPS solutions incorporate two types of alerts, atomic alerts and summary alerts. Atomic alerts are generated every time a signature triggers. A summary alert is a single alert that indicates multiple occurrences of the same signature from the same source address or port. With a summary alter, the first detection of the attack triggers a normal alert. Subsequent detection of the same attack is counted until the end of the signature summary interval. When the length of time specified by the summary interval has elapsed, a summary alarm is sent, indicating the number of alarms that occurred during the time interval.
Hint
Alerts generated by an IPS should be monitored closely to ensure proper actions are taken against malicious attacks. IPS solutions incorporate two types of alerts, atomic alerts and summary alerts. Atomic alerts are generated every time a signature triggers. A summary alert is a single alert that indicates multiple occurrences of the same signature from the same source address or port. With a summary alter, the first detection of the attack triggers a normal alert. Subsequent detection of the same attack is counted until the end of the signature summary interval. When the length of time specified by the summary interval has elapsed, a summary alarm is sent, indicating the number of alarms that occurred during the time interval.
-
Question 10 of 23
10. Question
1 pointsIn configuring a Cisco router to prepare for IPS and VPN features, a network administrator opens the file realm-cisco.pub.key.txt, and copies and pastes the contents to the router at the global configuration prompt. What is the result after this configuration step?
Correct
Incorrect
The third step in implementing IOS IPS is to configure the Cisco IOS IPS public key that is located in the realm-cisco.pub.key.txt file. This public key is used to verify digital signature for the master signature file, and can be downloaded from cisco.com. To configure the IOS IPS crypto key, open the text file, and copy and paste the contents to the router at the global configuration prompt. Public/private key pairs for IPsec VPN and SSH server are generated using different methods.
Hint
The third step in implementing IOS IPS is to configure the Cisco IOS IPS public key that is located in the realm-cisco.pub.key.txt file. This public key is used to verify digital signature for the master signature file, and can be downloaded from cisco.com. To configure the IOS IPS crypto key, open the text file, and copy and paste the contents to the router at the global configuration prompt. Public/private key pairs for IPsec VPN and SSH server are generated using different methods.
-
Question 11 of 23
11. Question
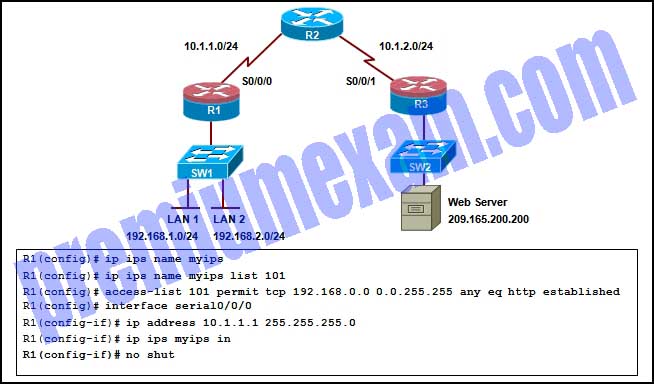
1 pointsRefer to the exhibit. Based on the configuration, which traffic will be examined by the IPS that is configured on router R1?
Correct
Incorrect
Because the IPS inspection is configured on the S0/0/0 interface with inbound direction, but the ACL source address range is 192.168.0.0/16 and the traffic type is http established, there will be no traffic to match these criteria (note, there is no web server on LAN 1 or LAN 2). Hence no traffic inspection will take place.
Hint
Because the IPS inspection is configured on the S0/0/0 interface with inbound direction, but the ACL source address range is 192.168.0.0/16 and the traffic type is http established, there will be no traffic to match these criteria (note, there is no web server on LAN 1 or LAN 2). Hence no traffic inspection will take place.
-
Question 12 of 23
12. Question
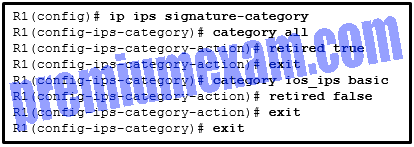
1 pointsRefer to the exhibit. Based on the IPS configuration provided, which conclusion can be drawn?
Correct
Incorrect
The IPS signature in the all category is retired, which means no signatures are compiled into memory. The IPS signature ios_ips basic category is unretired (by the command retired false), resulting in the signatures in the ios_ips basic being compiled into RAM for traffic inspection.
Hint
The IPS signature in the all category is retired, which means no signatures are compiled into memory. The IPS signature ios_ips basic category is unretired (by the command retired false), resulting in the signatures in the ios_ips basic being compiled into RAM for traffic inspection.
-
Question 13 of 23
13. Question
1 pointsA network administrator is configuring an IOS IPS with the command
R1(config)# ip ips signature-definition
Which configuration task can be achieved with this command?
Correct
Incorrect
The IOS command ip ips signature-definition is used to configure a specific signature, including retire/unretire and event action. To configure a signature category, the command ip ips signature-category is used.Hint
The IOS command ip ips signature-definition is used to configure a specific signature, including retire/unretire and event action. To configure a signature category, the command ip ips signature-category is used. -
Question 14 of 23
14. Question
2 pointsWhat are two disadvantages of using an IDS? (Choose two.)
Correct
Incorrect
The disadvantage of operating with mirrored traffic is that the IDS cannot stop malicious single-packet attacks from reaching the target before responding to the attack. Also, an IDS often requires assistance from other networking devices, such as routers and firewalls, to respond to an attack. An advantage of an IDS is that by working offline using mirrored traffic, it has no impact on traffic flow.
Hint
The disadvantage of operating with mirrored traffic is that the IDS cannot stop malicious single-packet attacks from reaching the target before responding to the attack. Also, an IDS often requires assistance from other networking devices, such as routers and firewalls, to respond to an attack. An advantage of an IDS is that by working offline using mirrored traffic, it has no impact on traffic flow.
-
Question 15 of 23
15. Question
2 pointsWhat are two shared characteristics of the IDS and the IPS? (Choose two.)
Correct
Incorrect
Both the IDS and the IPS are deployed as sensors and use signatures to detect malicious traffic. The IDS analyzes copies of network traffic, which results in minimal impact on network performance. The IDS also relies on an IPS to stop malicious traffic. Hint
Both the IDS and the IPS are deployed as sensors and use signatures to detect malicious traffic. The IDS analyzes copies of network traffic, which results in minimal impact on network performance. The IDS also relies on an IPS to stop malicious traffic.
-
Question 16 of 23
16. Question
1 pointsRefer to the exhibit. A network administrator enters the command on a Cisco IOS IPS router. What is the effect?
Correct
Incorrect
The ip ips notify command is used to set the IPS event notification. This command has two options, log and sdee. The log option is to specify that notifications are sent in syslog format. The sdee option is to specify that notifications are sent in SDEE format. If no option is specified, by default, notifications are sent in syslog format.Hint
The ip ips notify command is used to set the IPS event notification. This command has two options, log and sdee. The log option is to specify that notifications are sent in syslog format. The sdee option is to specify that notifications are sent in SDEE format. If no option is specified, by default, notifications are sent in syslog format. -
Question 17 of 23
17. Question
1 pointsA network administrator suspects the default setting of the ip ips notify sdee command has caused performance degradation on the Cisco IOS IPS router. The network administrator enters the ip sdee events 50 command in an attempt to remedy the performance issues. What is the immediate effect of this command?
Correct
Incorrect
When sending IPS notification with SDEE format, the buffer on the router stores up to 200 events by default. If a smaller buffer is requested, all stored events are lost. If a larger buffer is requested, all stored events are saved. The default buffer can be altered with the ip sdee events command. All stored events are lost when Cisco SDEE notification is disabled. A new buffer is allocated when the notifications are re-enabled.
Hint
When sending IPS notification with SDEE format, the buffer on the router stores up to 200 events by default. If a smaller buffer is requested, all stored events are lost. If a larger buffer is requested, all stored events are saved. The default buffer can be altered with the ip sdee events command. All stored events are lost when Cisco SDEE notification is disabled. A new buffer is allocated when the notifications are re-enabled. -
Question 18 of 23
18. Question
1 pointsTrue or False?
A Cisco IDS does not affect the flow of traffic when it operates in promiscuous mode.Correct
Incorrect
In promiscuous mode, also known as passive mode, the flow of traffic is unaffected because the IDS sensor analyzes copies of traffic instead of actual forwarded packets.
Hint
In promiscuous mode, also known as passive mode, the flow of traffic is unaffected because the IDS sensor analyzes copies of traffic instead of actual forwarded packets.
-
Question 19 of 23
19. Question
1 pointsWhat is a required condition to enable IPS activity reporting using the SDEE format?
Correct
Incorrect
To enable IPS activity reporting format using SDEE, the HTTP or HTTPS server must first be enabled on the router. If the HTTP server is not enabled, the router cannot respond to the SDEE clients because it cannot see the requests. The ip ips notify log command will send notification using syslog. The tasks of configuring the signature category and creating an IOS IPS configuration directory in flash are necessary to implement IOS IPS, but they are not directly associated with SDEE feature.Hint
To enable IPS activity reporting format using SDEE, the HTTP or HTTPS server must first be enabled on the router. If the HTTP server is not enabled, the router cannot respond to the SDEE clients because it cannot see the requests. The ip ips notify log command will send notification using syslog. The tasks of configuring the signature category and creating an IOS IPS configuration directory in flash are necessary to implement IOS IPS, but they are not directly associated with SDEE feature. -
Question 20 of 23
20. Question
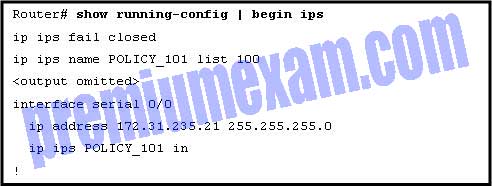
1 pointsRefer to the exhibit. Which statement best describes how incoming traffic on serial 0/0 is handled?
Correct
Incorrect
From the configuration, ACL 100 is used to identify matching packets to be inspected. However, since the ACL 100 configuration is unknown (not displayed), the only conclusion we can draw for sure is that “Traffic matching ACL 100 will be scanned and reported.”
Hint
From the configuration, ACL 100 is used to identify matching packets to be inspected. However, since the ACL 100 configuration is unknown (not displayed), the only conclusion we can draw for sure is that “Traffic matching ACL 100 will be scanned and reported.”
-
Question 21 of 23
21. Question
1 pointsWhat is a disadvantage of network-based IPS as compared to host-based IPS?
Correct
Incorrect
Network-based IPS devices are implemented as inline mode to actively monitor the traffic on networks. They can take immediate actions when security criteria match. One limitation of them is that they cannot monitor/inspect encrypted packets.
Hint
Network-based IPS devices are implemented as inline mode to actively monitor the traffic on networks. They can take immediate actions when security criteria match. One limitation of them is that they cannot monitor/inspect encrypted packets.
-
Question 22 of 23
22. Question
1 pointsAn IPS sensor has detected the string confidential across multiple packets in a TCP session. Which type of signature trigger and signature type does this describe?
Correct
Incorrect
Pattern-based detection (also called signature-based detection) searches for a specific pattern that can be textual, binary, or a series of function calls. It can be detected in a single packet (atomic) or in a packet sequence (composite).
Hint
Pattern-based detection (also called signature-based detection) searches for a specific pattern that can be textual, binary, or a series of function calls. It can be detected in a single packet (atomic) or in a packet sequence (composite).
-
Question 23 of 23
23. Question
2 pointsWhat are two drawbacks to using HIPS? (Choose two.)
Correct
Incorrect
Two disadvantages of deploying HIPS are (1) that it cannot create a complete view of the network or have knowledge of events that might be occurring beyond an individual host and (2) every host operating system within the organization must be supported. However, an advantage of using HIPS is that it can monitor and protect the operating system as well as critical system processes on each network host.
Hint
Two disadvantages of deploying HIPS are (1) that it cannot create a complete view of the network or have knowledge of events that might be occurring beyond an individual host and (2) every host operating system within the organization must be supported. However, an advantage of using HIPS is that it can monitor and protect the operating system as well as critical system processes on each network host.