Last Updated on October 28, 2019 by Admin
ITN Final Exam Form B Online
ITN -- Final Exam Form B
Quiz-summary
0 of 54 questions completed
Questions:
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
- 41
- 42
- 43
- 44
- 45
- 46
- 47
- 48
- 49
- 50
- 51
- 52
- 53
- 54
Information
ITN — Final Exam Form B
You have already completed the quiz before. Hence you can not start it again.
Quiz is loading...
You must sign in or sign up to start the quiz.
You have to finish following quiz, to start this quiz:
Results
0 of 54 questions answered correctly
Your time:
Time has elapsed
You have reached 0 of 0 points, (0)
| Average score |
|
| Your score |
|
Categories
- Not categorized 0%
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
- 41
- 42
- 43
- 44
- 45
- 46
- 47
- 48
- 49
- 50
- 51
- 52
- 53
- 54
- Answered
- Review
-
Question 1 of 54
1. Question
1 pointsA medium-sized business is researching available options for connecting to the Internet. The company is looking for a high speed option with dedicated, symmetric access. Which connection type should the company choose?Correct
Incorrect
-
Question 2 of 54
2. Question
1 pointsWhat is the purpose of having a converged network?Correct
Incorrect
With the development of technology, companies can now consolidate disparate networks onto one platform called a converged network. In a converged network, voice, video, and data travel over the same network, thus eliminating the need to create and maintain separate networks. This also reduces the costs associated with providing and maintaining the communication network infrastructure.Hint
With the development of technology, companies can now consolidate disparate networks onto one platform called a converged network. In a converged network, voice, video, and data travel over the same network, thus eliminating the need to create and maintain separate networks. This also reduces the costs associated with providing and maintaining the communication network infrastructure. -
Question 3 of 54
3. Question
1 pointsWhat characteristic of a network enables it to quickly grow to support new users and applications without impacting the performance of the service being delivered to existing users?Correct
Incorrect
Networks must be able to quickly grow to support new users and services, without impacting existing users and services. This ability to grow is known as scalability.Hint
Networks must be able to quickly grow to support new users and services, without impacting existing users and services. This ability to grow is known as scalability. -
Question 4 of 54
4. Question
1 pointsWhich connection provides a secure CLI session with encryption to a Cisco switch?Correct
Incorrect
A CLI session using Secure Shell (SSH) provides enhanced security because SSH supports strong passwords and encryption during the transport of session data. The other methods support authentication but not encryption.Hint
A CLI session using Secure Shell (SSH) provides enhanced security because SSH supports strong passwords and encryption during the transport of session data. The other methods support authentication but not encryption. -
Question 5 of 54
5. Question
1 pointsA network technician is attempting to configure an interface by entering the following command: SanJose(config)# ip address 192.168.2.1 255.255.255.0. The command is rejected by the device. What is the reason for this?Correct
Incorrect
The wrong mode of operation is being used. The CLI prompt indicates that the mode of operation is global configuration. IP addresses must be configured from interface configuration mode, as indicated by the SanJose(config-if)# prompt.Hint
The wrong mode of operation is being used. The CLI prompt indicates that the mode of operation is global configuration. IP addresses must be configured from interface configuration mode, as indicated by the SanJose(config-if)# prompt. -
Question 6 of 54
6. Question
1 pointsAfter several configuration changes are made to a router, the copy running-configuration startup-configuration command is issued. Where will the changes be stored?Correct
Incorrect
-
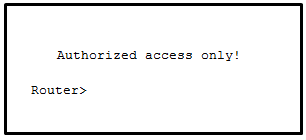
Question 7 of 54
7. Question
1 pointsRefer to the exhibit. From global configuration mode, an administrator is attempting to create a message-of-the-day banner by using the command banner motd V Authorized access only! Violators will be prosecuted! V When users log in using Telnet, the banner does not appear correctly. What is the problem?
Correct
Incorrect
-
Question 8 of 54
8. Question
3 pointsWhat are three characteristics of an SVI? (Choose three.)Correct
Incorrect
Switches have one or more switch virtual interfaces (SVIs). SVIs are created in software since there is no physical hardware associated with them. Virtual interfaces provide a means to remotely manage a switch over a network that is using IP. Each switch comes with one SVI appearing in the default configuration “out-of-the-box.” The default SVI interface is VLAN1.Hint
Switches have one or more switch virtual interfaces (SVIs). SVIs are created in software since there is no physical hardware associated with them. Virtual interfaces provide a means to remotely manage a switch over a network that is using IP. Each switch comes with one SVI appearing in the default configuration “out-of-the-box.” The default SVI interface is VLAN1. -
Question 9 of 54
9. Question
1 pointsA technician configures a switch with these commands:
SwitchA(config)# interface vlan 1
SwitchA(config-if)# ip address 192.168.1.1 255.255.255.0
SwitchA(config-if)# no shutdownWhat is the technician configuring?
Correct
Incorrect
For a switch to have an IP address, a switch virtual interface must be configured. This allows the switch to be managed remotely over the network.Hint
For a switch to have an IP address, a switch virtual interface must be configured. This allows the switch to be managed remotely over the network. -
Question 10 of 54
10. Question
1 pointsIn computer communication, what is the purpose of message encoding?Correct
Incorrect
Before a message is sent across a network it must first be encoded. Encoding is the process of converting the data message into another format suitable for transmission across the physical medium. Each bit of the message is encoded into a pattern of sounds, light waves, or electrical impulses depending on the network media over which the bits are transmitted. The destination host receives and decodes the signals in order to interpret the message.Hint
Before a message is sent across a network it must first be encoded. Encoding is the process of converting the data message into another format suitable for transmission across the physical medium. Each bit of the message is encoded into a pattern of sounds, light waves, or electrical impulses depending on the network media over which the bits are transmitted. The destination host receives and decodes the signals in order to interpret the message. -
Question 11 of 54
11. Question
1 pointsWhat protocol is responsible for controlling the size of segments and the rate at which segments are exchanged between a web client and a web server?Correct
Incorrect
TCP is a Layer 4 protocol of the OSI model. TCP has several responsibilities in the network communication process. It divides large messages into smaller segments which are more efficient to send across the network. It also controls the size and rate of segments exchanged between clients and servers.Hint
TCP is a Layer 4 protocol of the OSI model. TCP has several responsibilities in the network communication process. It divides large messages into smaller segments which are more efficient to send across the network. It also controls the size and rate of segments exchanged between clients and servers. -
Question 12 of 54
12. Question
2 pointsWhat are two benefits of using a layered network model? (Choose two.)Correct
Incorrect
Some vendors have developed their own reference models and protocols. Today, if a device is to communicate on the Internet, the device must use the TCP/IP model. The benefits of using a layered model are as follows:
- assists in protocol design
- fosters competition between vendors
- prevents a technology that functions at one layer from affecting any other layer
- provides a common language for describing network functionality
- helps in visualizing the interaction between each layer and protocols between each layer
Hint
Some vendors have developed their own reference models and protocols. Today, if a device is to communicate on the Internet, the device must use the TCP/IP model. The benefits of using a layered model are as follows:
- assists in protocol design
- fosters competition between vendors
- prevents a technology that functions at one layer from affecting any other layer
- provides a common language for describing network functionality
- helps in visualizing the interaction between each layer and protocols between each layer
-
Question 13 of 54
13. Question
1 pointsWhat is the process of dividing a data stream into smaller pieces before transmission?Correct
Incorrect
Data streams would cause significant network congestion if they were transmitted as a single large stream of bits. To increase efficiency, data streams are segmented into smaller more manageable pieces which are then transmitted over the network. -
Question 14 of 54
14. Question
1 pointsWhen IPv4 addressing is manually configured on a web server, which property of the IPv4 configuration identifies the network and host portion for an IPv4 address?Correct
Incorrect
There are several components that need to be entered when configuring IPv4 for an end device:
- IPv4 address – uniquely identifies an end device on the network
- Subnet mask – determines the network address portion and host portion for an IPv4 address
- Default gateway – the IP address of the router interface used for communicating with hosts in another network
- DNS server address – the IP address of the Domain Name System (DNS) server
DHCP server address (if DHCP is used) is not configured manually on end devices. It will be provided by a DHCP server when an end device requests an IP address.
Hint
There are several components that need to be entered when configuring IPv4 for an end device:
- IPv4 address – uniquely identifies an end device on the network
- Subnet mask – determines the network address portion and host portion for an IPv4 address
- Default gateway – the IP address of the router interface used for communicating with hosts in another network
- DNS server address – the IP address of the Domain Name System (DNS) server
DHCP server address (if DHCP is used) is not configured manually on end devices. It will be provided by a DHCP server when an end device requests an IP address.
-
Question 15 of 54
15. Question
1 pointsA network administrator is troubleshooting connectivity issues on a server. Using a tester, the administrator notices that the signals generated by the server NIC are distorted and not usable. In which layer of the OSI model is the error categorized?Correct
Incorrect
The NIC has responsibilities in both Layer 1 and Layer 2. The NIC encodes the frame as a series of signals that are transmitted onto the local media. This is the responsibility of the physical layer of the OSI model. The signal could be in the form of electrical, optical, or radio waves.Hint
The NIC has responsibilities in both Layer 1 and Layer 2. The NIC encodes the frame as a series of signals that are transmitted onto the local media. This is the responsibility of the physical layer of the OSI model. The signal could be in the form of electrical, optical, or radio waves. -
Question 16 of 54
16. Question
3 pointsA network engineer is measuring the transfer of bits across the company backbone for a mission critical database application. The engineer notices that the network throughput appears lower than the bandwidth expected. Which three factors could influence the differences in throughput? (Choose three.)Correct
Incorrect
Throughput usually does not match the specified bandwidth of physical links due to multiple factors. These factors include, the amount of traffic, type of traffic, and latency created by the network devices the data has to cross.Hint
Throughput usually does not match the specified bandwidth of physical links due to multiple factors. These factors include, the amount of traffic, type of traffic, and latency created by the network devices the data has to cross. -
Question 17 of 54
17. Question
1 pointsWhich type of UTP cable is used to connect a PC to a switch port?Correct
Incorrect
A rollover cable is a Cisco proprietary cable used to connect to a router or switch console port. A straight-through (also called patch) cable is usually used to interconnect a host to a switch and a switch to a router. A crossover cable is used to interconnect similar devices together, for example, between two switches, two routers, and two hosts.Hint
A rollover cable is a Cisco proprietary cable used to connect to a router or switch console port. A straight-through (also called patch) cable is usually used to interconnect a host to a switch and a switch to a router. A crossover cable is used to interconnect similar devices together, for example, between two switches, two routers, and two hosts. -
Question 18 of 54
18. Question
1 pointsWhat is a characteristic of the LLC sublayer?Correct
Incorrect
The Logical Link Control (LLC) defines the software processes that provide services to the network layer protocols. The information is placed by LLC in the frame and identifies which network layer protocol is being used for the frame. This information allows multiple Layer 3 protocols, such as IPv4 and IPv6, to utilize the same network interface and media.Hint
The Logical Link Control (LLC) defines the software processes that provide services to the network layer protocols. The information is placed by LLC in the frame and identifies which network layer protocol is being used for the frame. This information allows multiple Layer 3 protocols, such as IPv4 and IPv6, to utilize the same network interface and media. -
Question 19 of 54
19. Question
3 pointsWhat are the three primary functions provided by Layer 2 data encapsulation? (Choose three.)Correct
Incorrect
Through the framing process, delimiters are used to identify the start and end of the sequence of bits that make up a frame. Data link layer addressing is added to enable a frame to be delivered to a destination node. A cyclic redundancy check (CRC) field is calculated on every bit and added to the frame. If the CRC value contained in the arriving frame is the same as the one the receiving node creates, the frame will be processed.Hint
Through the framing process, delimiters are used to identify the start and end of the sequence of bits that make up a frame. Data link layer addressing is added to enable a frame to be delivered to a destination node. A cyclic redundancy check (CRC) field is calculated on every bit and added to the frame. If the CRC value contained in the arriving frame is the same as the one the receiving node creates, the frame will be processed. -
Question 20 of 54
20. Question
1 pointsWhat will a host on an Ethernet network do if it receives a frame with a destination MAC address that does not match its own MAC address?Correct
Incorrect
In an Ethernet network, each NIC in the network checks every arriving frame to see if the destination MAC address in the frame matches its own MAC address. If there is no match, the device discards the frame. If there is a match, the NIC passes the frame up to the next OSI layer.
Hint
In an Ethernet network, each NIC in the network checks every arriving frame to see if the destination MAC address in the frame matches its own MAC address. If there is no match, the device discards the frame. If there is a match, the NIC passes the frame up to the next OSI layer.
-
Question 21 of 54
21. Question
2 pointsWhat are two actions performed by a Cisco switch? (Choose two.)Correct
Incorrect
Important actions that a switch performs are as follows:
- When a frame comes in, the switch examines the Layer 2 source address to build and maintain the Layer 2 MAC address table.
- It examines the Layer 2 destination address to determine how to forward the frame. When the destination address is in the MAC address table, then the frame is sent out a particular port. When the address is unknown, the frame is sent to all ports that have devices connected to that network.
Hint
Important actions that a switch performs are as follows:
- When a frame comes in, the switch examines the Layer 2 source address to build and maintain the Layer 2 MAC address table.
- It examines the Layer 2 destination address to determine how to forward the frame. When the destination address is in the MAC address table, then the frame is sent out a particular port. When the address is unknown, the frame is sent to all ports that have devices connected to that network.
-
Question 22 of 54
22. Question
2 pointsWhat are two examples of the cut-through switching method? (Choose two.)Correct
Incorrect
Store-and forward switching accepts the entire frame and performs error checking using CRC before forwarding the frame. Store-and-forward is often required for QOS analysis. Fast-forward and fragment-free are both variations of the cut-through switching method where only part of the frame is received before the switch begins to forward it.Hint
Store-and forward switching accepts the entire frame and performs error checking using CRC before forwarding the frame. Store-and-forward is often required for QOS analysis. Fast-forward and fragment-free are both variations of the cut-through switching method where only part of the frame is received before the switch begins to forward it. -
Question 23 of 54
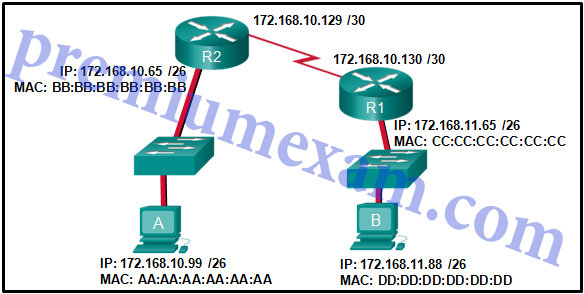
23. Question
1 pointsRefer to the exhibit. If host A sends an IP packet to host B, what will the destination address be in the frame when it leaves host A?
Correct
Incorrect
When a host sends information to a distant network, the Layer 2 frame header will contain a source and destination MAC address. The source address will be the originating host device. The destination address will be the router interface that connects to the same network. In the case of host A sending information to host B, the source address is AA:AA:AA:AA:AA:AA and the destination address is the MAC address assigned to the R2 Ethernet interface, BB:BB:BB:BB:BB:BB.Hint
When a host sends information to a distant network, the Layer 2 frame header will contain a source and destination MAC address. The source address will be the originating host device. The destination address will be the router interface that connects to the same network. In the case of host A sending information to host B, the source address is AA:AA:AA:AA:AA:AA and the destination address is the MAC address assigned to the R2 Ethernet interface, BB:BB:BB:BB:BB:BB. -
Question 24 of 54
24. Question
2 pointsWhat are two services provided by the OSI network layer? (Choose two.)Correct
Incorrect
The OSI network layer provides several services to allow communication between devices:
- addressing
- encapsulation
- routing
- de-encapsulation
Error detection, placing frames on the media, and collision detection are all functions of the data ink layer.
Hint
The OSI network layer provides several services to allow communication between devices:
- addressing
- encapsulation
- routing
- de-encapsulation
Error detection, placing frames on the media, and collision detection are all functions of the data ink layer.
-
Question 25 of 54
25. Question
1 pointsWhat information is added during encapsulation at OSI Layer 3?Correct
Incorrect
IP is a Layer 3 protocol. Layer 3 devices can open the Layer 3 header to inspect the Layer 3 header which contains IP-related information including the source and destination IP addresses.Hint
IP is a Layer 3 protocol. Layer 3 devices can open the Layer 3 header to inspect the Layer 3 header which contains IP-related information including the source and destination IP addresses. -
Question 26 of 54
26. Question
2 pointsWhat are two functions of NVRAM? (Choose two.)Correct
Incorrect
NVRAM is permanent memory storage, so the startup configuration file is preserved even if the router loses power.Hint
NVRAM is permanent memory storage, so the startup configuration file is preserved even if the router loses power. -
Question 27 of 54
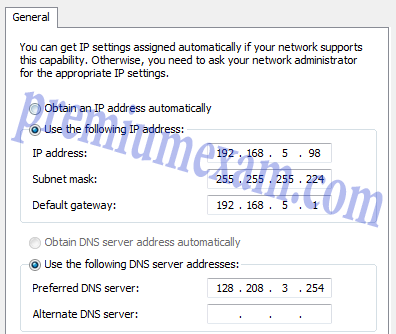
27. Question
1 pointsRefer to the exhibit. The network administrator for a small advertising company has chosen to use the 192.168.5.96/27 network for internal LAN addressing. As shown in the exhibit, a static IP address is assigned to the company web server. However, the web server cannot access the Internet. The administrator verifies that local workstations with IP addresses that are assigned by a DHCP server can access the Internet, and the web server is able to ping local workstations. Which component is incorrectly configured?
Correct
Incorrect
When a 255.255.255.224 subnet mask is used, the first three bits of the last octet are part of the network portion for an IPv4 address in the subnet. For the 192.168.5.96/27 network, valid host addresses are 192.168.5.97 through 192.168.5.126. The default gateway address is for the Layer 3 device on the same network and it must contain an IP address within the valid IP address range.Hint
When a 255.255.255.224 subnet mask is used, the first three bits of the last octet are part of the network portion for an IPv4 address in the subnet. For the 192.168.5.96/27 network, valid host addresses are 192.168.5.97 through 192.168.5.126. The default gateway address is for the Layer 3 device on the same network and it must contain an IP address within the valid IP address range. -
Question 28 of 54
28. Question
1 pointsWhy does a Layer 3 device perform the ANDing process on a destination IP address and subnet mask?Correct
Incorrect
ANDing allows us to identify the network address from the IP address and the network mask.Hint
ANDing allows us to identify the network address from the IP address and the network mask. -
Question 29 of 54
29. Question
3 pointsWhat are the three ranges of IP addresses that are reserved for internal private use? (Choose three.)Correct
Incorrect
The private IP address blocks that are used inside companies are as follows:
- 10.0.0.0 /8 (any address that starts with 10 in the first octet)
- 172.16.0.0 /12 (any address that starts with 172.16 in the first two octets through 172.31.255.255)
- 192.168.0.0 /16 (any address that starts with 192.168 in the first two octets)
Hint
The private IP address blocks that are used inside companies are as follows:
- 10.0.0.0 /8 (any address that starts with 10 in the first octet)
- 172.16.0.0 /12 (any address that starts with 172.16 in the first two octets through 172.31.255.255)
- 192.168.0.0 /16 (any address that starts with 192.168 in the first two octets)
-
Question 30 of 54
30. Question
3 pointsWhich three addresses are valid public addresses? (Choose three.)Correct
Incorrect
-
Question 31 of 54
31. Question
1 pointsWhat type of IPv6 address is FE80::1?Correct
Incorrect
Link-local IPv6 addresses start with FE80::/10, which is any address from FE80:: to FEBF::. Link-local addresses are used extensively in IPv6 and allow directly connected devices to communicate with each other on the link they share.Hint
Link-local IPv6 addresses start with FE80::/10, which is any address from FE80:: to FEBF::. Link-local addresses are used extensively in IPv6 and allow directly connected devices to communicate with each other on the link they share. -
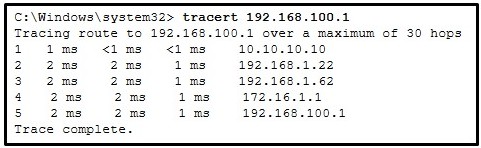
Question 32 of 54
32. Question
2 pointsRefer to the exhibit. On the basis of the output, which two statements about network connectivity are correct? (Choose two.)
Correct
Incorrect
The output displays a successful Layer 3 connection between a host computer and a host at 19.168.100.1. It can be determined that 4 hops exist between them and the average transmission time is 1 milliseconds. Layer 3 connectivity does not necessarily mean that an application can run between the hosts.Hint
The output displays a successful Layer 3 connection between a host computer and a host at 19.168.100.1. It can be determined that 4 hops exist between them and the average transmission time is 1 milliseconds. Layer 3 connectivity does not necessarily mean that an application can run between the hosts. -
Question 33 of 54
33. Question
1 pointsWhich subnet would include the address 192.168.1.96 as a usable host address?Correct
Incorrect
For the subnet of 192.168.1.64/26, there are 6 bits for host addresses, yielding 64 possible addresses. However, the first and last subnets are the network and broadcast addresses for this subnet. Therefore, the range of host addresses for this subnet is 192.168.1.65 to 192.168.1.126. The other subnets do not contain the address 192.168.1.96 as a valid host address.Hint
For the subnet of 192.168.1.64/26, there are 6 bits for host addresses, yielding 64 possible addresses. However, the first and last subnets are the network and broadcast addresses for this subnet. Therefore, the range of host addresses for this subnet is 192.168.1.65 to 192.168.1.126. The other subnets do not contain the address 192.168.1.96 as a valid host address. -
Question 34 of 54
34. Question
1 pointsHow many hosts are addressable on a network that has a mask of 255.255.255.248?Correct
Incorrect
The subnet mask of 255.255.255.248 is the same as /29. This means the network portion of the address is 29 of the 32 bits in the address. Only 3 bits remain for host bits. 2^3 = 8, but one of these addresses has to be used for the network number and one address must be used as the broadcast address to reach all of the hosts on this network. That leaves only 6 usable IP addresses that can be assigned to hosts in this network. Don’t forget that the default gateway must be one of these devices if this network is to communicate with other networks.Hint
The subnet mask of 255.255.255.248 is the same as /29. This means the network portion of the address is 29 of the 32 bits in the address. Only 3 bits remain for host bits. 2^3 = 8, but one of these addresses has to be used for the network number and one address must be used as the broadcast address to reach all of the hosts on this network. That leaves only 6 usable IP addresses that can be assigned to hosts in this network. Don’t forget that the default gateway must be one of these devices if this network is to communicate with other networks. -
Question 35 of 54
35. Question
1 pointsWhich statement is true about variable-length subnet masking?Correct
Incorrect
In variable-length subnet masking, bits are borrowed to create subnets. Additional bits may be borrowed to create additional subnets within the original subnets. This may continue until there are no bits available to borrow.Hint
In variable-length subnet masking, bits are borrowed to create subnets. Additional bits may be borrowed to create additional subnets within the original subnets. This may continue until there are no bits available to borrow. -
Question 36 of 54
36. Question
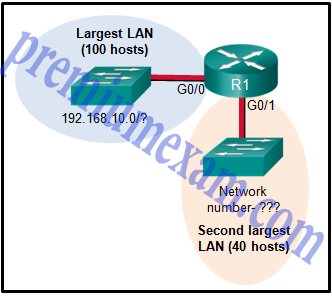
1 pointsRefer to the exhibit. Consider the IP address of 192.168.10.0/24 that has been assigned to a high school building. The largest network in this building has 100 devices. If 192.168.10.0 is the network number for the largest network, what would be the network number for the next largest network, which has 40 devices?
Correct
Incorrect
The first thing to calculate is what IP addresses are used by the largest LAN. Because the LAN has 100 hosts, 7 bits must be left for host bits. This would be a subnet mask of 255.255.255.128 for the largest LAN (192.168.10.0/25). The IP addresses range from 192.168.10.0 through 192.168.10.127. 192.168.10.0 is the network number (all 0s in the host bits) and 192.168.10.127 is the broadcast for this Ethernet LAN (all 1s in the host bits). The next available IP address is the next network number – 192.168.10.128.Hint
The first thing to calculate is what IP addresses are used by the largest LAN. Because the LAN has 100 hosts, 7 bits must be left for host bits. This would be a subnet mask of 255.255.255.128 for the largest LAN (192.168.10.0/25). The IP addresses range from 192.168.10.0 through 192.168.10.127. 192.168.10.0 is the network number (all 0s in the host bits) and 192.168.10.127 is the broadcast for this Ethernet LAN (all 1s in the host bits). The next available IP address is the next network number – 192.168.10.128. -
Question 37 of 54
37. Question
2 pointsIn what two situations would UDP be the preferred transport protocol over TCP? (Choose two.)Correct
Incorrect
UDP is a stateless protocol, which means that neither device on either end of the conversation must keep track of the conversation. As a stateless protocol, UDP is used as the Layer 4 protocol for applications that need speedy (best-effort) delivery. An example of such traffic is the transport of digitized voice or video.Hint
UDP is a stateless protocol, which means that neither device on either end of the conversation must keep track of the conversation. As a stateless protocol, UDP is used as the Layer 4 protocol for applications that need speedy (best-effort) delivery. An example of such traffic is the transport of digitized voice or video. -
Question 38 of 54
38. Question
1 pointsWhat important information is added to the TCP/IP transport layer header to ensure communication and connectivity with a remote network device?Correct
Incorrect
The destination and source port numbers are used to identify exactly which protocol and process is requesting or responding to a request.Hint
The destination and source port numbers are used to identify exactly which protocol and process is requesting or responding to a request. -
Question 39 of 54
39. Question
1 pointsWhat is the TCP mechanism used in congestion avoidance?Correct
Incorrect
TCP uses windows to attempt to manage the rate of transmission to the maximum flow that the network and destination device can support while minimizing loss and retransmissions. When overwhelmed with data, the destination can send a request to reduce the of the window. This congestion avoidance is called sliding windows.Hint
TCP uses windows to attempt to manage the rate of transmission to the maximum flow that the network and destination device can support while minimizing loss and retransmissions. When overwhelmed with data, the destination can send a request to reduce the of the window. This congestion avoidance is called sliding windows. -
Question 40 of 54
40. Question
3 pointsWhich three statements characterize UDP? (Choose three.)Correct
Incorrect
UDP is a simple protocol that provides the basic transport layer functions. It has much lower overhead than TCP because it is not connection-oriented and does not offer the sophisticated retransmission, sequencing, and flow control mechanisms that provide reliability.Hint
UDP is a simple protocol that provides the basic transport layer functions. It has much lower overhead than TCP because it is not connection-oriented and does not offer the sophisticated retransmission, sequencing, and flow control mechanisms that provide reliability. -
Question 41 of 54
41. Question
2 pointsWhich two tasks are functions of the presentation layer? (Choose two.)Correct
Incorrect
The presentation layer deals with common data format. Encryption, formatting, and compression are some of the functions of the layer. Addressing occurs in the network layer, session control occurs in the session layer, and authentication takes place in the application or session layer.Hint
The presentation layer deals with common data format. Encryption, formatting, and compression are some of the functions of the layer. Addressing occurs in the network layer, session control occurs in the session layer, and authentication takes place in the application or session layer. -
Question 42 of 54
42. Question
2 pointsWhich two protocols operate at the highest layer of the TCP/IP protocol stack? (Choose two.)Correct
Incorrect
The application layer is the top layer of the TCP/IP protocol stack. Application layer protocols include HTTP, DNS, HTML, TFTP, POP, IMAP, FTP, and SMTP.Hint
The application layer is the top layer of the TCP/IP protocol stack. Application layer protocols include HTTP, DNS, HTML, TFTP, POP, IMAP, FTP, and SMTP. -
Question 43 of 54
43. Question
2 pointsWhich two roles can a computer assume in a peer-to-peer network where a file is being shared between two computers? (Choose two.)Correct
Incorrect
In a peer-to-peer (P2P) network, two or more computers are connected and can share resources without the use of a dedicated server. The computer that has the file acts as a server for the device (the client) that requests the file.Hint
In a peer-to-peer (P2P) network, two or more computers are connected and can share resources without the use of a dedicated server. The computer that has the file acts as a server for the device (the client) that requests the file. -
Question 44 of 54
44. Question
1 pointsWhat is the function of the HTTP GET message?Correct
Incorrect
There are three common HTTP message types:
- GET – used by clients to request data from the web server
- POST – used by clients to upload data to a web server
- PUT – used by clients to upload data to a web server
Hint
There are three common HTTP message types:
- GET – used by clients to request data from the web server
- POST – used by clients to upload data to a web server
- PUT – used by clients to upload data to a web server
-
Question 45 of 54
45. Question
1 pointsA wireless host needs to request an IP address. What protocol would be used to process the request?Correct
Incorrect
The DHCP protocol is used to request, issue, and manage IP addressing information. CSMA/CD is the access method used with wired Ethernet. ICMP is used to test connectivity. SNMP is used with network management and FTP is used for file transfer.Hint
The DHCP protocol is used to request, issue, and manage IP addressing information. CSMA/CD is the access method used with wired Ethernet. ICMP is used to test connectivity. SNMP is used with network management and FTP is used for file transfer. -
Question 46 of 54
46. Question
1 pointsWhen planning for network growth, where in the network should packet captures take place to assess network traffic?Correct
Incorrect
Because some types of traffic will be only on specific network segments, packet captures for analysis should be performed on as many segments as possible.Hint
Because some types of traffic will be only on specific network segments, packet captures for analysis should be performed on as many segments as possible. -
Question 47 of 54
47. Question
1 pointsWhen applied to a router, which command would help mitigate brute-force password attacks against the router?Correct
Incorrect
The login block-for command sets a limit on the maximum number of failed login attempts allowed within a defined period of time. If this limit is exceeded, no further logins are allowed for the specified period of time. This helps to mitigate brute-force password cracking since it will significantly increase the amount of time required to crack a password. The exec-timeout command specifies how long the session can be idle before the user is disconnected. The service password-encryption command encrypts the passwords in the running configuration. The banner motd command displays a message to users who are logging in to the device.Hint
The login block-for command sets a limit on the maximum number of failed login attempts allowed within a defined period of time. If this limit is exceeded, no further logins are allowed for the specified period of time. This helps to mitigate brute-force password cracking since it will significantly increase the amount of time required to crack a password. The exec-timeout command specifies how long the session can be idle before the user is disconnected. The service password-encryption command encrypts the passwords in the running configuration. The banner motd command displays a message to users who are logging in to the device. -
Question 48 of 54
48. Question
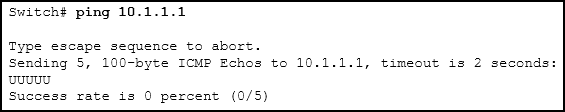
1 pointsRefer to the exhibit. An administrator is testing connectivity to a remote device with the IP address 10.1.1.1. What does the output of this command indicate?
Correct
Incorrect
In the output of the ping command, an exclamation mark (!) indicates a response was successfully received, a period (.) indicates that the connection timed out while waiting for a reply, and the letter “U” indicates that a router along the path did not have a route to the destination and sent an ICMP destination unreachable message back to the source.Hint
In the output of the ping command, an exclamation mark (!) indicates a response was successfully received, a period (.) indicates that the connection timed out while waiting for a reply, and the letter “U” indicates that a router along the path did not have a route to the destination and sent an ICMP destination unreachable message back to the source. -
Question 49 of 54
49. Question
1 pointsA user is unable to reach the web site when typing http://www.cisco.com in a web browser, but can reach the same site by typing http://72.163.4.161. What is the issue?Correct
Incorrect
Domain Name Service (DNS) is used to translate a web address to an IP address. The address of the DNS server is provided via DHCP to host computers.Hint
Domain Name Service (DNS) is used to translate a web address to an IP address. The address of the DNS server is provided via DHCP to host computers. -
Question 50 of 54
50. Question
1 pointsWhat source IP address does a router use by default when the traceroute command is issued?Correct
Incorrect
When sending an echo request message, a router will use the IP address of the exit interface as the source IP address. This default behavior can be changed by using an extended ping and specifying a specific source IP address.Hint
When sending an echo request message, a router will use the IP address of the exit interface as the source IP address. This default behavior can be changed by using an extended ping and specifying a specific source IP address. -
Question 51 of 54
51. Question
3 pointsMatch each item to the type of topology diagram on which it is typically identified. (Not all options are used.)
Sort elements
- location of a desktop PC in a classroom
- path of cables that connect rooms to wiring closets
- IP address of a server
- USB port on a desktop PC in a classroom
-
physical topology diagram
-
physical topology diagram
-
logical topology diagram
Correct
Incorrect
A logical topology diagram typically depicts the IP addressing scheme and groupings of devices and ports. A physical topology diagram shows how those devices are connected to each other and the network, focusing on the physical locations of intermediary devices, configured ports, and cabling.Hint
A logical topology diagram typically depicts the IP addressing scheme and groupings of devices and ports. A physical topology diagram shows how those devices are connected to each other and the network, focusing on the physical locations of intermediary devices, configured ports, and cabling. -
Question 52 of 54
52. Question
6 pointsMatch the description with the associated IOS mode. (Not all options are used.)
Sort elements
- limited number of basic monitoring commands
- the first entrance into the CLI of an IOS device
- accessed by entering the enable command
- identified by a prompt ending with the # character
- changes made affect the operation of the device as a whole
- accessed by entering the configure terminal command
- used to enable the password for vty lines
-
user EXEC mode
-
user EXEC mode
-
privileged EXEC mode
-
privileged EXEC mode
-
global configuration mode
-
global configuration mode
Correct
Incorrect
-
Question 53 of 54
53. Question
6 pointsMatch the situation with the appropriate use of network media.
Sort elements
- Copper Cables
- Copper Cables
- Fiber Optic
- Fiber Optic
- Wireless
- Wireless
-
horizontal cabling structure
-
desktop PCs in an enterprise office
-
backbone cabling in an enterprise
-
bong-haul networks
-
guest access in a coffee shop
-
waiting rooms in a hospital
Correct
Incorrect
Copper Cables – horizontal cabling structure and desktop PCs in offices in an enterprise
Fiber optic – backbone cabling in an enterprise and long-haul networks
Wireless – coffee shops and waiting rooms in a hospitalHint
Copper Cables – horizontal cabling structure and desktop PCs in offices in an enterprise
Fiber optic – backbone cabling in an enterprise and long-haul networks
Wireless – coffee shops and waiting rooms in a hospital -
Question 54 of 54
54. Question
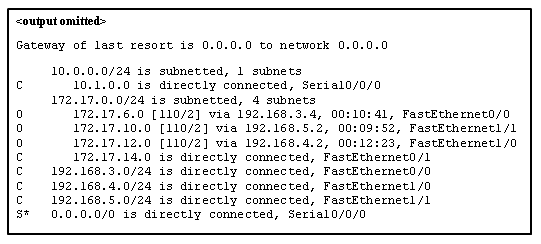
5 pointsRefer to the exhibit. Match the packets with their destination IP address to the exiting interfaces on the router. (Not all targets are used.)
Sort elements
- FastEthernet0/0
- FastEthernet0/1
- FastEthernet1/0
- FastEthernet1/1
- Serial0/0/0
- The packet is dropped.
-
packets with destination of 172.17.6.15
-
packets with destination of 172.17.14.8
-
packets with destination of 172.17.12.10
-
packets with destination of 172.17.10.5
-
packets with destination of 172.17.8.20
Correct
Incorrect
Packets with a destination of 172.17.6.15 are forwarded through Fa0/0. Packets with a destination of 172.17.10.5 are forwarded through Fa1/1. Packets with a destination of 172.17.12.10 are forwarded through Fa1/0. Packets with a destination of 172.17.14.8 are forwarded through Fa0/1. Because network 172.17.8.0 has no entry in the routing table, it will take the gateway of last resort, which means that packets with a destination of 172.17.8.20 are forwarded through Serial0/0/0. Because a gateway of last resort exists, no packets will be dropped.Hint
Packets with a destination of 172.17.6.15 are forwarded through Fa0/0. Packets with a destination of 172.17.10.5 are forwarded through Fa1/1. Packets with a destination of 172.17.12.10 are forwarded through Fa1/0. Packets with a destination of 172.17.14.8 are forwarded through Fa0/1. Because network 172.17.8.0 has no entry in the routing table, it will take the gateway of last resort, which means that packets with a destination of 172.17.8.20 are forwarded through Serial0/0/0. Because a gateway of last resort exists, no packets will be dropped.